Welcome back to Part III of our “Unleash the Power of Censys Search” series! In this series, we take a closer look at different ways Censys Search users can make the most of their engagement with the tool. In Part I, we provided tips for how to get started running queries in Censys Search. In Part II, we shared real examples of how Censys Search has been used to support threat hunting investigations and research efforts. In today’s blog, we’re focusing on the value of accessing historical data through Censys Search. All Censys Search users have the ability to look at historical data to observe how assets like hosts have changed over time. The depth of historical data varies across Censys Search packages.
Let’s delve into why a historical perspective can be valuable, and how to achieve it in Censys Search.
Traveling Back in Time: Why Historical Data Matters
In the realm of cybersecurity, the ability to look back at how internet-exposed assets have changed over time can be incredibly useful. By assessing activity on assets like hosts over time, security teams can trace the footprints of potential threats and gain unparalleled context that can empower them to make more informed decisions about how to mitigate and prevent future threats.
Benefits of this kind of historical view include:
1.Advancing Threat Hunting Efforts: One key advantage of gaining a historical perspective is the ability it provides to uncover stealthy and persistent threats that may have flown under the radar during real-time monitoring. Threats often operate in the shadows, leaving subtle traces that might be easily missed in the chaos of live monitoring. With the ability to rewind the clock, threat hunters can shine a spotlight on dormant threats, understanding their dormant phases and potential resurgence. This proactive stance is invaluable in nipping potential risks in the bud before they blossom into full-fledged attacks. Keep reading for an example of how historical views aided a real Censys-led threat hunting investigation.
2. Improving Incident Response: Historical views also serve as a forensic tool, aiding in the investigation and attribution of cyber incidents. In the aftermath of an attack, the ability to review historical data can help teams reconstruct the sequence of events, identify the initial point of compromise, and trace the lateral movement of adversaries within a network. This forensic capability is not just about post-incident analysis; it also plays a pivotal role in strengthening the security posture by helping teams learn from past incidents, so that they can prevent similar occurrences in the future.
3. Understanding Trends: Historical views help security teams and researchers learn more about what changes to internet-exposed devices might mean for security posture and the state of internet security as a whole. Our own research team recently explored if and how open directories, a longstanding exposure type, were still prevalent across the internet. (Spoiler alert: they are.) Historical views also support our research team’s work on projects like the annual State of the Internet Report, which helps analyze how the internet is, or is not, getting more secure over time.
Using Censys Search to Gain a Historical View
As the leading provider of internet intelligence, Censys maintains the most comprehensive, accurate, and up-to-date view of global internet infrastructure available. This view has allowed us to track activity on the global internet infrastructure over time and observe how it’s changed. Users of our Censys Search tool have access to this temporal view, too, through the historical data available via our web UI and API.
What does this mean in practice? On any host page in Censys Search, a user can select “Host History” in the top navigation bar to see a chronology of events related to host activity. For example, a user can see when services are added to hosts, locations are updated, and fields are changed, among other activities.
You can find an example of a host history view below.
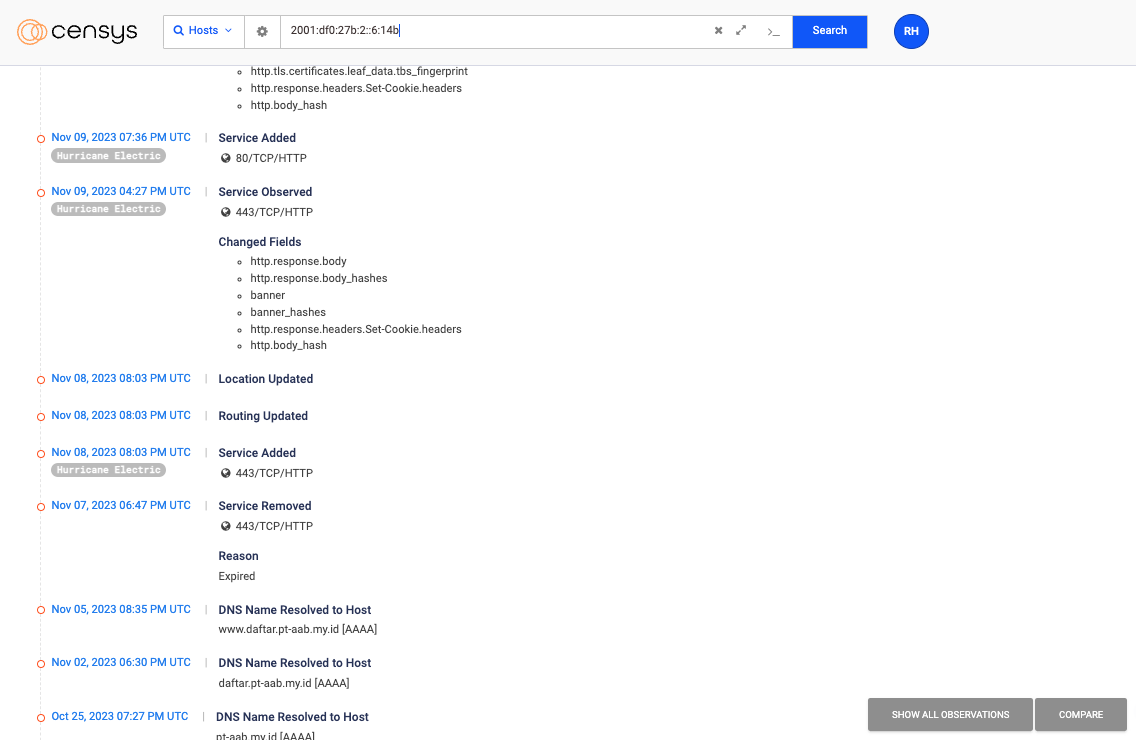
When observing the history of a host, you can either look at a list of all temporal activity (what’s shown above), or, you can compare activity from two points in time. To see all of the observations Censys made of a host’s services, even ones that resulted in no change to its representation, open the History tab and toggle the “See All Observations” button to blue. To compare activity from two points in time, tick the boxes on the left-hand side of the activity you want to compare and click the “Compare” button. A comparison could be useful when trying to determine if and how a host may have been impacted by a zero-day.
A few words on access: As mentioned, all Censys Search users have access to historical data! Free community users have access to up to a week’s worth of historical data, while users with advanced packages have access to more robust historical data, going back three years. Researchers and users interested in our data downloads can access up to seven years of historical data.
Leveraging Historical Data in Practice
The Censys Research Team recently used the host history function in Censys Search to facilitate an investigation into NTC Vulkan infrastructure. NTC Vulkan is a Moscow-based group, founded by two former Russian intelligence officials. Reporting indicates that the group has been contracted by Russian intelligence to create offensive cyber tools, including those that could be used to target elections and attack critical infrastructure.
In their investigation, Censys researchers discovered six hosts belonging to NTC Vulkan and were able to currently and historically profile the tools and software they hosted, providing a baseline profile of the company. For example, using historical analysis, Censys was able to identify a GitLab server that NTC Vulkan may have been using to develop tools for Russia’s GRU Sandworm (a cyber unit of Russia’s military intelligence service). Investigating the history of NTC Vulkan’s hosts helped the team learn more about the core functions of the hosts and even the organization itself.
Check out our Discovery of NTC Vulkan Infrastructure article for a full analysis of what our research team uncovered.
If you’ve been following along with Censys, you’ve probably also heard us talk about our investigation into Russian ransomware. There are a lot of details to share about this investigation, which you can read about in full here. As the team’s work related to host history, however, they used a historical perspective in Censys Search to help confirm that what they were observing was indeed nefarious activity.
The team had identified a suspicious host with a PoshC2 certificate that also presented a HTTP response with a malware kit. Through historical analysis of the malware kit, the team could see that months earlier the malware kit had “restoreassistance_net@decorous[.]cyou” appended to each of its files. A Google search revealed “@decorous[.]cyou” as a domain used by the MedusaLocker group, confirmed by a CISA Alert.
Censys assessed that this constituted a “smoking gun” and implicated this host as part of a ransomware C2 network, likely as an attacker or a proxy (as a victim is possible; however, Censys’ historical analysis indicates the presence, removal, and reemergence of the PoshC2 certificate and a persistence of the malware kit modified over time, which would be more in line with an attacker modifying their attack methods).
In other words, without this historical view, Censys researchers would have only been able to observe activity on Host F from a present-day perspective, and would have missed changes related to the PoshC2 certificate and malware kit.
Learning from the Past to Secure the Future
Internet-exposed assets and the threats that target them are continuously evolving. The ability to look back at how activity associated with these assets has changed provides a critical lens through which security practitioners, threat hunters, and researchers can identify threats and manage risk, as well as gain insights that can be used to make more informed decisions moving forward.
Check out historical data in Censys Search today! Head over to search.censys.io to start exploring or to sign up for a free Community account.
Interested in upgrading from a free account? Reach out to our team!





