Executive Summary
In March 2023, various media outlets published details from documents received in February of 2022 from a former NTC Vulkan employee who opposed Russia’s invasion of Ukraine. Moscow-based NTC Vulkan, the outlets reported, was contracted by Russian intelligence to create the following offensive cyber tools:
- Scan or Scan-V – an internet-wide scanning tool designed to discover vulnerabilities for use in potential cyber operations
- Amesit or Amezit – “A framework used to control the online information environment and manipulate public opinion, enhance psychological operations, and…support IO and OT-related operations”
- Krystal-2B – a training platform for cyber attacks on critical infrastructure.
In this investigation, Censys researchers discovered six hosts belonging to NTC Vulkan and were able to currently and historically profile the tools and software they hosted, providing a baseline profile of the company. Most interestingly, Censys uncovered a connection to a group called Raccoon Security via a NTC Vulkan certificate. This discovery was significant in that no other media mentioned this connected group, despite the fact that Raccoon Security’s stated capabilities show close matches with the tools Russian intelligence sought from NTC Vulkan.
Given Russia’s history of using offensive cyber tools in conjunction with military or geopolitical aims and that the intent of NTC Vulkan’s contracts for the Russian GRU’s Sandworm seemed to include enabling offensive Russian cyber operations potentially targeting elections and critical infrastructure, Censys researchers assessed that NTC Vulkan’s capabilities could pose a threat to democratic institutions. And since NTC Vulkan was founded by two former Russian intelligence officers, Censys researchers chose to profile the dispositions of hosts linked to NTC Vulkan, in an effort to spread awareness of the group and its capabilities.
Findings
NTC Vulkan Hosts
Censys researchers first focused on the publicly available assets belonging to NTC Vulkan to establish attribution between the company and any domains, hosts, or certificates within the Censys scan dataset. During this search, Censys uncovered six NTC Vulkan hosts that illustrated the company has either used or is currently using BigBlueButton and Jitsi Meet virtual collaboration software; Nextcloud data storage and virtual collaboration; Cisco and pfSense firewalls; an Nginx server; and a GitLab server, among other tools.
Considering the leaked NTC Vulkan information indicated tool development for the GRU, Censys’ historical discovery of the GitLab server may match this assertion. The presence of BigBlueButton and Jitsi Meet video conferencing tools may indicate internal remote collaboration or possibly collaboration with an external entity such as a client. The Nextcloud servers may serve in a similar collaboration capacity and/or for internal NTC Vulkan use. Additionally, NTC Vulkan’s external posture includes the consistent use of Cisco and pfSense network appliances.
Raccoon Security Hosts
After discovering these NTC Vulkan hosts, Censys researchers enumerated all NTC Vulkan certificates, both current and expired. To do this, Censys pivoted off the organization field in one of the certificates on a confirmed NTC Vulkan host, as well as searching for the ntc-vulkan[.]ru domain and variations on “NTC Vulkan” (e.g. “NTCVulkan,” “NTC Vulcan,” etc.) within Censys’ certificates database. While reviewing these certificates, Censys researchers looked for any additional indicators of attribution, including other domains in the Subject Alternate Names (SANs) and Common Name (CN) fields to identify further links to the group or any other organization with which it might be affiliated.
Censys found raccoonsecurity[.]ru within the CN of the certificate subject and the SANs. This initial indicator lead to a search of Censys’ certificate data for “raccoonsecurity” leading to the discovery of not only other certificates, but a virtual host on a shared hosting provider with the domains raccoonsecurity[.]org, raccoonsecurity[.]net and raccoonsecurity[.]org, all of which redirect to raccoonsecurity[.]ru.
A look at the Raccoon Security website (via Russian to English translation using Google Translate), shows the following services:
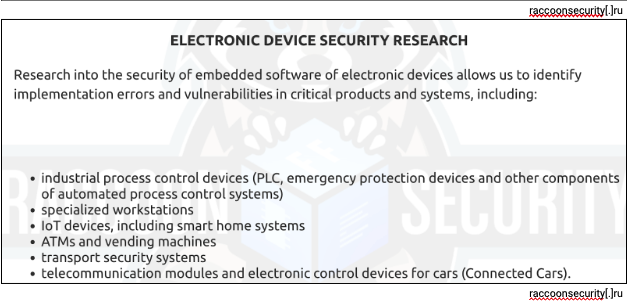
While these services are branded in a defensive manner on the website, their utility matches leaked NTC Vulkan contract initiatives. This includes Krystal-2B, a training environment for attacking operational technology, which could be enabled by conducting and learning from the services offered above. This also includes Scan-V which aimed to identify vulnerabilities on devices identified globally, coinciding with the verbiage above of “identify implementation errors and vulnerabilities in critical products and systems.” Additionally, the Raccoon Security website offers secure design and development consultation and planning, which matches the developmental nature of the projects GRU contracted NTC Vulkan to execute.

Furthermore, a Google search of raccoonsecurity[.]ru shows mention of Raccoon Security as an internal brand and team of NTC Vulkan on ntc-vulkan[.]ru/about/news/racoon-security/.
Censys therefore concludes that Racoon Security is a brand of NTC Vulkan and that it is possible that Raccoon Security’s activities include either previous or current participation in the previously-mentioned leaked initiatives contracted by the GRU. Censys recommends monitoring Raccoon Security, its domains, website, IP address, and any certificates in which it is mentioned to uncover any temporal changes in the organization’s posture or infrastructure.
Assessment
Censys assesses with high confidence that the NTC Vulkan hosts, certificates, and domains identified in this report do indeed belong to the same NTC Vulkan identified in sources cited in this report. The NTC Vulkan certificate naming conventions and domains identified in Censys’ dataset correspond to the publicly facing NTC Vulkan website. Even though Censys researchers identified software changes on NTC Vulkan hosts and the creation of new certificates as old ones expired, naming conventions remained consistent on the certificates and Censys observed no changes in IP addresses over time. These indicators therefore allow Censys to conclude the assets identified in this report belong to NTC Vulkan. This assertion is not shocking, as NTC Vulkan is a public business, but it is useful for those looking to reliably monitor the organization for changes in its posture or capabilities.
Censys also assesses with high confidence that Raccoon Security, and its related domains, host, and certificates belong to the Moscow-based cybersecurity development brand of the same name. This is due to the fact that the associated domains of Raccoon Security all redirect to the Raccoon Security main website. Censys also is confident that Raccoon Security is a group within NTC Vulkan, not only because Censys researchers discovered Raccoon Security’s domain within a certificate that listed NTC Vulkan in the organization field, but because the corresponding Racoon Security website explicitly states that it is “…an internal corporate association of specialists from the Vulcan research and development center….” NTC Vulkan’s site confirms this relationship.
While Censys cannot confirm that Raccoon Security is developing the offensive tools mentioned in the aforementioned NTC Vulkan leaks, it seems that the services and capabilities listed on its website lend itself to this ability.
In conclusion, identifying NTC Vulkan’s and Raccoon Security’s public digital footprint indicated to Censys researchers that:
- Leveraging even one domain confirmed to belong to an organization can be enough to understand the common tools that organization leverages to sustain business operations, such as virtual training, cloud collaboration, and network defense.
- Investigating the history of those hosts can be useful in guiding analysts as to the core functions of those hosts and even the organization itself.
- Examining certificates of a certain organization can be a useful way to uncover related organizations and their domains, which can lead to useful pivots revealing new hosts.
Contact
If you would like details about hosts, IPs, software, or certificates mentioned in this report, or for any questions, feedback, or requests, please email us at federal@censys.io.






