We are celebrating the launch of Certs 2.0 – the largest X.509 certificate repository in existence! ???? Our new Certs 2.0 index provides enhanced access to our extensive billion certificate repository, with more efficient and granular searching capabilities. Additional benefits include:
- Upgraded schema
- Daily revocation checks & processing of certificates
- Enhanced search performance
- Fast integration with new CT logs
- Deduplication of pre-certificates
- Advanced Censys Search Language
With all these new goodies available, we wanted to take a moment and review why they’re critical for a secure Internet, provide a few pointers on how to interpret our parsed certs data, and share some examples of how you can leverage this data in your threat hunting activities.
Introduction to X.509 certificates
While using the modern Internet, we interact with certificates on a daily basis. They’re now such an integral part of secure Internet infrastructure that we rarely think about them, unless they’re expired or missing from a website. X.509 certificates are often also known as SSL certificates–X.509 refers to the standard that defines public key certificates. Regardless of how you reference them, these certificates help mitigate risk on the Internet in several ways:
- Certificates enable encryption for web traffic. This means threat actors can’t easily intercept and read the data being passed between a client and server. There was a time when one could connect to a public WiFi network, fire up Wireshark, and see some interesting things floating around because most connections were served over HTTP. The ubiquity of certificates has made this an increasingly rare and largely unsuccessful practice.
- Certificates act as identity verification. When an entity obtains a certificate from a trusted certificate authority (CA), they must provide evidence of their identity. In some cases this means providing proof of ownership of a domain (DV), or a meeting with an employee from the organization requesting the cert (EV). When a site presents a certificate from a CA, it’s evidence that they have successfully verified their identity and are who they say they are.
Words of warning ⚠️
Certs and legitimacy
While important, the presence of a certificate on a site shouldn’t be conflated with the site’s legitimacy. For years, many browsers have displayed a padlock or other icon when visiting sites served over HTTPS. Users were often told that if they observed the icon in the URL bar of their browser, the site they were visiting was secure. Well, sure–it could be a secure connection to a phishing page.
While potentially a useful signal if interpreted in the correct context, threat actors noticed the framing of “the padlock means it’s secure so it’s safe to enter my credit card information here” and it’s now common to see phishing sites with certificates. Services offering free certificates, while helping democratize certificates for all, have provided threat actors with additional avenues to obtain certificates for malicious sites. Suggesting that a site is “secure” in a general sense simply because an icon in the browser indicates that traffic is being served over HTTPS is misleading and harmful.
Self-signed certs
Self-signed certificates are just that: self-signed. They aren’t issued by a CA, but by the entity requesting the certificate, and have not been subject to the verification requirements necessary to obtain a cert through a CA. While they can be useful for testing environments or experimentation, they should not be used for employee- or public-facing assets.

Live look at a self-signed certificate being “verified”
Anatomy of an X.509 certificate
Below are some fields you’ll commonly find in Censys Certificates data:
- Subject Distinguished Name (DN): Information about the entity to whom the certificate was issued
- Issuer Distinguished Name (DN): Information about the certificate authority that issued the certificate
- Serial: Unique identifier for the certificate, assigned by the certificate authority
- Validity: Date range for which the certificate is valid
The Subject DN and Issuer DN can contain fields such as:
- C = Country
- ST = State
- L = Locality or city
- O = Organization Name
- OU = Organizational Unit
- CN = Common Name
Values for the Subject DN will reflect values for the Subject, or entity requesting the cert, while the Issuer DN values will reflect those of the CA. You can read more about parsed certificate values in Censys data here.
Threat hunting with certificates
Because certificates are useful for verifying an entity’s identity, they can provide helpful pivots in threat hunts and other investigations. Here are a few examples to help you get started.
Searching for C2s
Many popular C2 frameworks now come with certificates to ensure their communications are encrypted. While some generate certificates with random or user-supplied values, others use the same values across every installation, which can be useful for hunting.
PoshC2 is one such C2. The default values for their cert are as follows, for both Subject and Issuer DN:
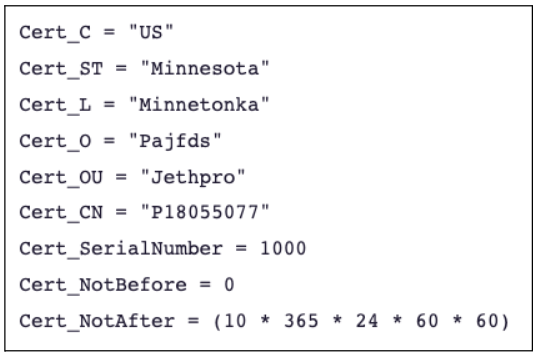
This Certificates search will show the all matching certs Censys has observed:
parsed.subject.organization=Pajfds and parsed.subject.organizational_unit=Jethpro
We can also search for those values on hosts:
services.tls.certificates.leaf_data.subject.organization:Pajfds and services.tls.certificates.leaf_data.subject.organizational_unit:Jethpro
Certs as part of a larger investigation
In 2021, Citizen Lab leveraged Censys cert data as part of an investigation into Candiru, a mercenary spyware vendor whose products have been used to target activists around the world. By matching an email address in a self-signed cert to documents known to be affiliated with Candiru, researchers were able to pivot and find additional related infrastructure, enabling them to continue tracking the group.
Conclusion
Certificates play an important role in making the Internet a safer and more secure place for all. They can also be a valuable tool in a threat hunter’s toolkit.
Want To Learn More?
If you’re new to Censys, you can see your attack surface in real time by requesting a live demo. For current Censys customers, please reach out to your CSM to learn more about leveraging Certs 2.0.