Product Release: Web Entities – The Censys Internet Intelligence Platform™ now detects and helps organizations protect Web Entities!
What Are Web Entities?
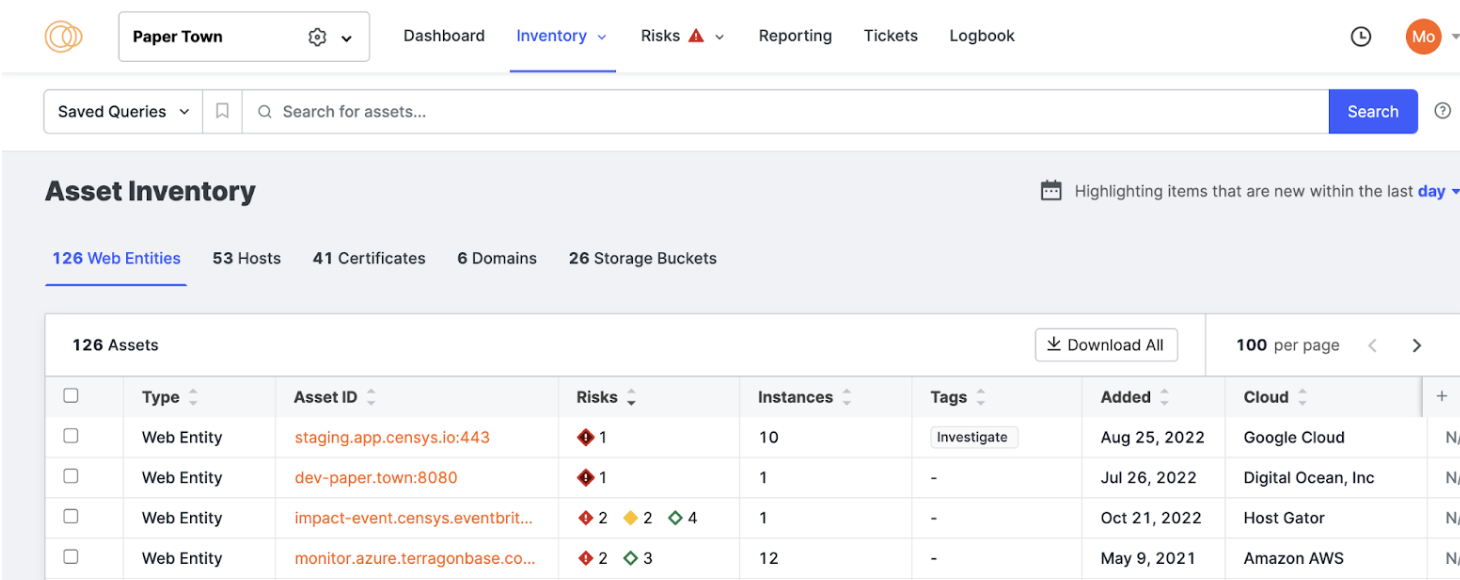
We define Web Entities as all of your named HTTP(S) services such as websites, elasticsearch instances, kubernetes clusters, and prometheus endpoints. Your organization may have thousands of web entities across your digital environment. These assets can be difficult to protect because they are hosted on dynamic cloud environments that use a name as a primary asset identifier, rather than an IP. Your security and IT teams need a holistic view of all exposed entities across their attack surface to have actionable insights into exposures and risks.
Providing Visibility into the Assets that Your Organization Is Responsible for Defending
Censys’ Internet Intelligence Platform™ is designed to help organizations have the most comprehensive inventory of an organization’s internet-facing assets. In addition to owning and managing IPs, Domains, Certificates, and Storage Buckets, organizations are also responsible for protecting the web inventory. With Web Entities, we’re providing a new asset type that gives organizations visibility into their website and other name-based HTTP content. These assets can be discovered, monitored, assessed for risks, and triaged so that teams can better defend against places where attacks happen.
Built on the most accurate and up-to-date internet map, IT security teams will now have access to a more complete inventory of all internet facing exposures to protect the business from what hackers look to exploit. Web Entities enables organizations to easily categorize, identify and assemble web inventory and risks. This empowers security teams by eliminating resources spent on mapping identifiers to business systems, and instead prioritize and respond to exposures as quickly as possible.
Saving Security and IT Teams Time and Resources
We’ve modeled web entities in a way that better reflects the cloud infrastructure that most teams use to deploy their websites and name-based HTTP services. Some of the main improvements in our in model include:
Assets can be reliably identified and monitored using a name (and port)
Web Entities reflect name-based identification of an asset, allowing teams to effectively identify, track, and remediate risks even when the underlying IP addresses that serve instances of the entity change.
Risks are associated with a web entity, not an IP
Risks detected on Web Entities are affiliated to them, not the underlying host, so teams are presented with a single risk rather than with separate risks for each instance.
Attack Surfaces are isolated from digital neighbor’s data
Web Entities are the product of scanning with names belonging to an organization, so even if you use large web-hosting infrastructure, the data and risks returned are relevant to your security operations.
Using Censys’ Internet Intelligence Platform™ with the power of Web Entities, your security organization is empowered to:
- Continuously discover and monitor external web inventory for a holistic view into all internet facing exposures
- Have visibility into the relationships between all exposed web entities, giving security teams the ability to understand and map paths between assets
- Cut down on the noise by replacing risk duplication and false positives with meaningful alerts and insights
- Consistently track assets by name rather than by changing, dynamic, or hosted IP addresses that come and go
Want To Learn More?
If you’re new to Censys, you can see your attack surface in real time by requesting a live demo.