Automation and quality data are key ingredients to any successful security program. Quality data in, means quality data out. Automation wherever possible means saving precious time for your security team. This is no different when it comes to External Attack Surface Management products.
Today, Censys is excited to launch even more automation and visibility into your presence on the Internet with our new Automated Onboarding. The new feature allows under-resourced teams to punch above their weight class by finding more of your assets on the Internet in less time.
Use cases: M&A and enterprise operations
Going through a merger or acquisition? Or maybe your company is large and distributed around the world? Automated Onboarding can be especially useful for your security team.
Mergers and acquisitions
With more mergers and acquisitions every year, this means more and more assets are inherited as they change hands between companies. Knowing where all of your Internet facing assets are and ensuring you address the most critical issues quickly is crucial in managing your company’s risk. With Automated Onboarding, we give you visibility into even the most nested acquisitions of a target company with the click of a button. Save time and know what you need to address as quickly as possible so you can speed up the diligence and integration processes while confidently managing risk.
Enterprise operations
A sprawling and distributed presence on the Internet can be unruly and near impossible to manage without automation and effective tools. Enterprise attack surfaces change constantly, whether you’re buying up domains, companies, moving your assets to the cloud, or maintaining a very distributed workforce. Automated Onboarding helps these teams by automating the discovery of those new assets on the Internet with a very easy and intuitive onboarding flow. This means saving your team time and effort so they can focus on remediation and other security implementation activities.
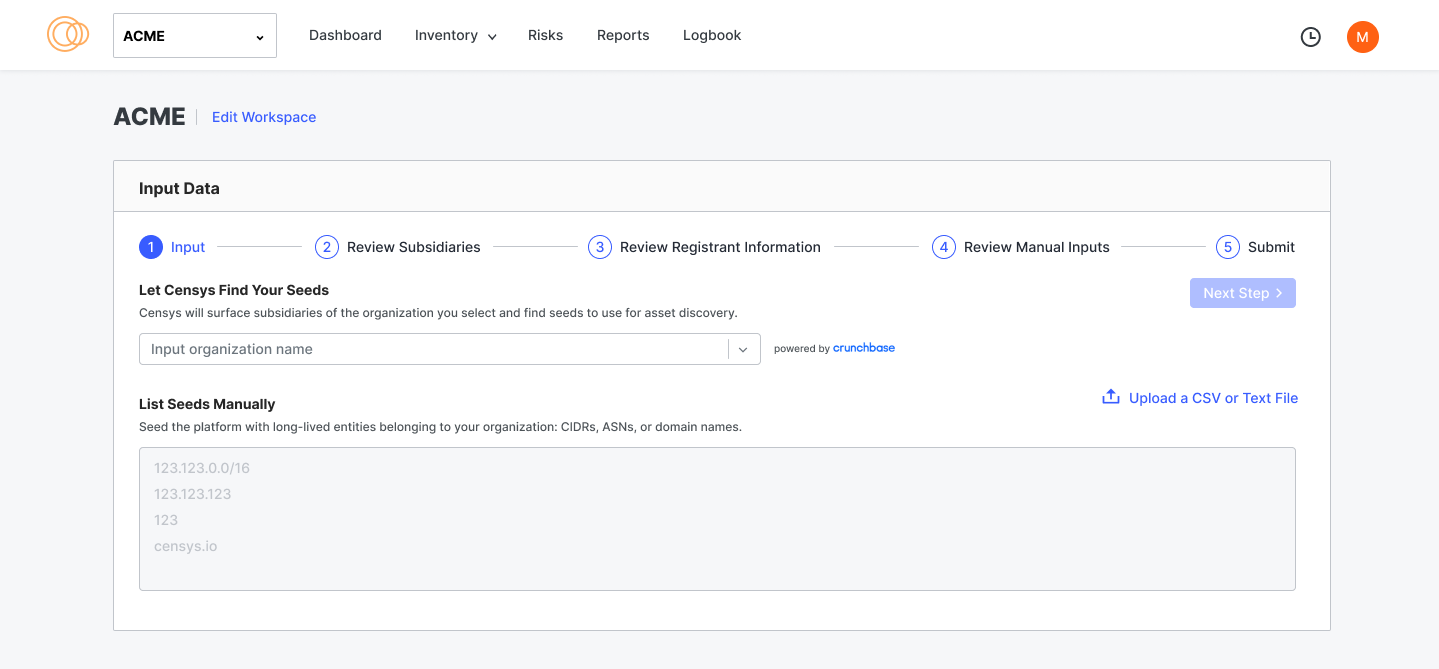
A quick start with Automated Onboarding
The good news is it doesn’t take long at all to get started with Censys. Easy to use and highly customizable, to begin uncovering your external attack surface with Censys ASM, it really only takes a few simple steps.
1. Input a company name.
2. Review subsidiaries part of the company.
3. Review registrant information.
4. Review your manual data entered.
5. Submit!
Your attack surface is now being generated and will be monitored with fresh insights daily.
With Automated Onboarding, Censys ASM discovers even more of your attack surface. You can get started today.
