Introduction
On September 27, Progress Software published an advisory for 8 newly discovered vulnerabilities in their WS_FTP tool. This advisory comes on the heels of an interesting summer for Progress, whose MOVEit Transfer tool has seen widespread exploitation after a series of SQL injection vulnerabilities were discovered in the tool’s web interface.
Judging by the product name: “WS_FTP,” one would think these are vulnerabilities in their FTP server, but this is untrue. The reality is that there seem to be multiple services associated with the actual FTP server itself that are running over HTTP.
WS_FTP and the Ad Hoc Transfer Module
Similar to MOVEit, WS_FTP is a file transfer solution, and while it’s specifically FTP server software, it has a server manager web interface and an optional Ad Hoc Transfer UI module.
This module provides a web interface and a Microsoft Outlook plugin that rely on the underlying WS_FTP server. The advisory includes 2 critical, 3 high, and 3 medium vulnerabilities, some of which affect only instances of WS_FTP that have enabled the Ad Hoc Transfer module, but others that affect the server manager interface (standard on all installations). The highest criticality vulnerability from this disclosure, CVE-2023-40044, explicitly affects instances of WS_FTP with the Ad Hoc Transfer module enabled.
While there is currently no known exploitation of any of the vulnerabilities in the Progress advisory, it’s highly recommended for WS_FTP administrators to apply patches linked in the advisory–and if patching somehow isn’t an option, to at least disable the Ad Hoc Transfer module in the meantime.
Censys View of the Ad Hoc Transfer Module
NOTE: we do not have direct access to test any WS_FTP product; all this information has been gleaned from our scan data.
One method we’ve devised to determine whether these hosts are running the WS_FTP HTTP service is by using the Censys search query:
services.http.request.uri=”*/ThinClient/WTM/public/index.html”
Unfortunately, this only shows us servers with the WS_FTP HTTP server installed, but not whether the “Ad Hoc Transfer Module” is enabled. However, using Censys and other tools (jq , censys-cli, and httpx), one can determine if the module is enabled:
$ censys search 'services.http.request.uri="*/ThinClient/WTM/public/index.html"' | \
jq '.[]|.ip' -cr | \
httpx -path '/AHT/AHT_UI/public/index.html#/login' -sc -title -mc 200
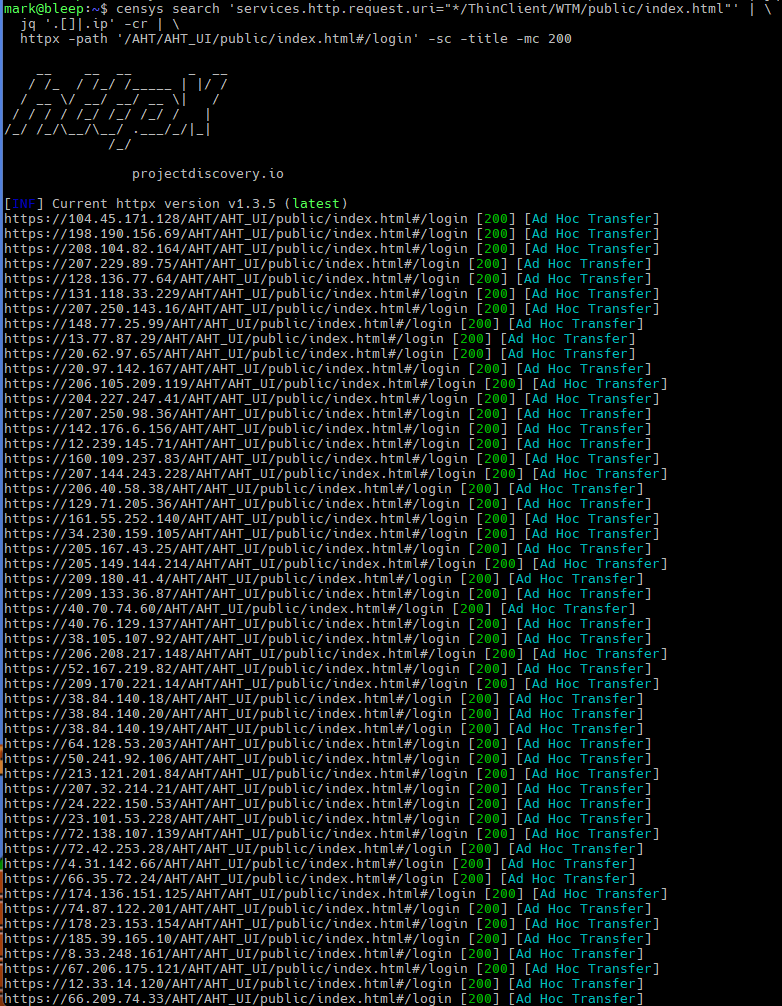
Using a similar technique, we discovered that out of the 325 WS_FTP servers with this HTTP service running, we only found that 91 hosts (28%) have disabled the Ad Hoc Transfer module (at least from what we gathered by trying to fetch /AHT/AHT_UI/public/index.html#/login).
Compared to the total number of WS_FTP servers running the FTP and SCP interface, which total over 4,000 hosts, the number of potentially vulnerable servers is much lower than expected, which is not the worst news.
Conclusion
Compared to MOVEit, of which we still see several thousand instances online, there are relatively few hosts running WS_FTP with the Ad Hoc Transfer module installed, and nearly a third of those have been disabled as of the publication of this post.
Of the vulnerabilities listed in the Progress advisory, at least 5 were discovered by researchers at other companies, including Assetnote and Deloitte. This isn’t the first time Assetnote researchers have uncovered vulnerabilities in a file transfer tool. Last October, a researcher there discovered a remote code execution vulnerability in IBM’s Aspera Faspex, which was publicly disclosed and patched in January of this year.
Rapid7 has also conducted security assessments of popular file transfer tools following the campaigns against GoAnywhere and MOVEit. The heightened interest in these tools from threat actors and security researchers alike raises questions about the security posture of these “secure” tools built for transferring sensitive data.