Executive Summary
- On September 29, Mandiant and Google Threat Intelligence Group began tracking an extortion campaign targeting Oracle’s E-Business Suite, reminiscent in many ways of the MOVEit Transfer campaign of 2023
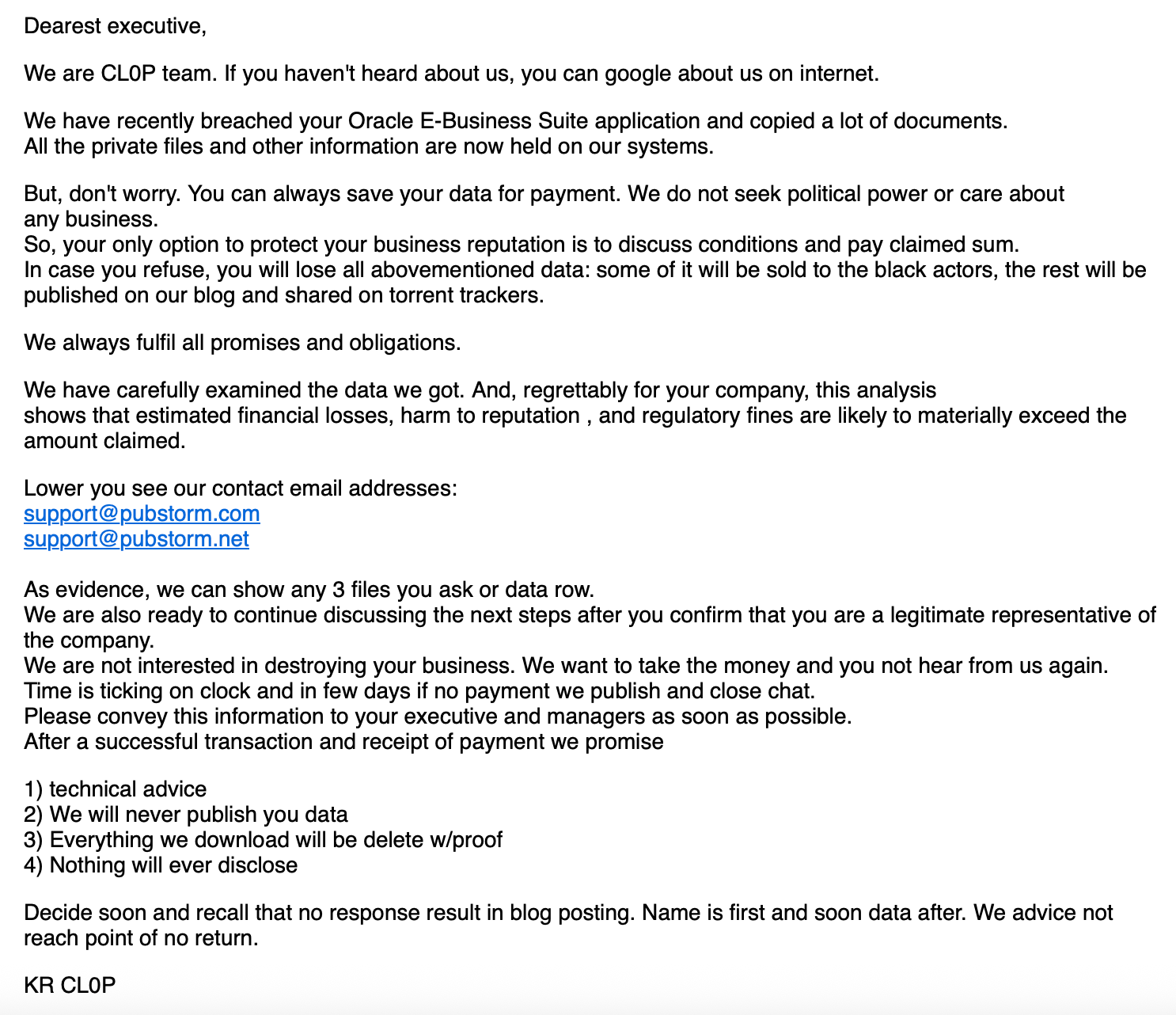
- Extortion actor Cl0p claimed credit for the attack in emails sent to executives of affected companies, and as of October 2025, organizations are slowly being listed on Cl0p’s data leak site
- We studied exposed instances of Oracle EBS in early October to understand potential impacts across industries and geography
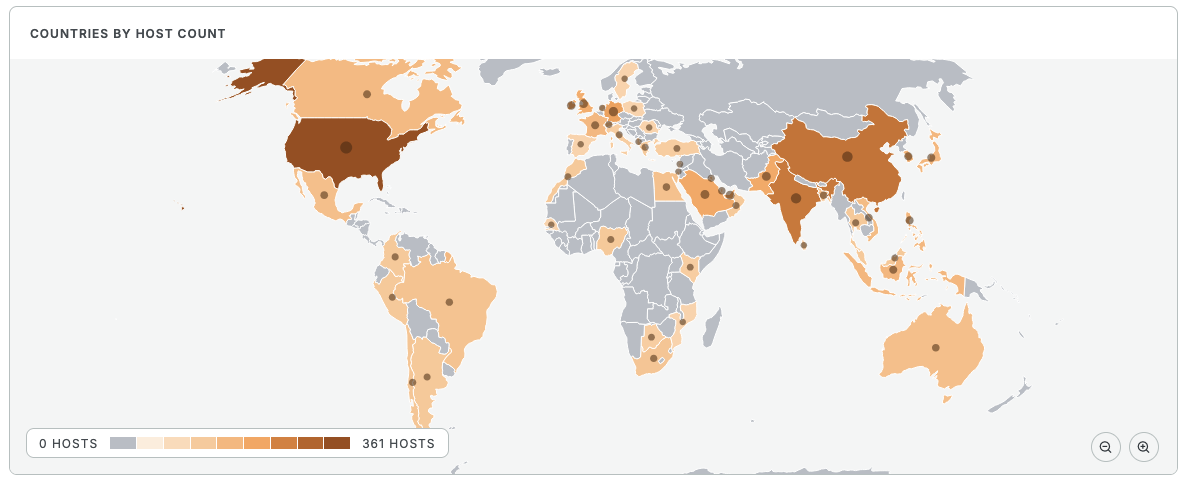
- As of this post, the U.S., China, and India have the most exposed instances, just as we saw earlier in October
- Of instances we could confidently categorize by industry, just under 14% appear to belong to Manufacturing/Industrial organizations, 12% are Government/Public Sector, and 10% are Conglomerate/Holding Companies
- Though smaller in percentage, Energy, Utilities, and Oil & Gas represent 6% of categorized instances we observe
- Contrasting the 2023 MOVEit campaign with this campaign against EBS, there are notable similarities (threat actor involvement, TTPs) and differences (geographic spread of instances, types of vulnerabilities exploited, and potentially affected industries)
Introduction
Over the summer months of 2025, extortion actor Cl0p pulled a page out of their old playbook when it came to a vulnerability in Oracle’s E-Business Suite: targeting enterprise business software with zero-day exploits, quietly exfiltrating data, and leaking said data if extortion fees remain unpaid.
Oracle’s EBS offers a range of functionality for key business operations, including order management and logistics, project management, and financial management. The categories of EBS products on the product homepage suggest these instances likely house some very sensitive business data.
The Recent Campaign
On September 29, 2025, Mandiant and Google Threat Intelligence Group (GTIG) began tracking an extortion campaign against organizations running EBS. Cl0p reportedly began sending emails to executives at organizations from which they’d stolen data, threatening to sell and leak the data if an extortion fee went unpaid.
On October 4, Oracle released a security alert for newly issued CVE-2025-61882, a critical (9.8) pre-authentication remote code execution (RCE) vulnerability. Analysis of this vulnerability is beyond the scope of this post, but WatchTowr Labs published a detailed breakdown of the exploit chain. Investigation from GTIG and Mandiant suggests that the initial exploitation of this vulnerability may have begun on August 9, 2025, with “additional suspicious activity” identified as early as July 10, 2025.
Shortly after the initial Oracle security alert, Oracle released another alert on October 11. This vulnerability, CVE-2025-61884, is a high severity (7.5) server side request forgery (SSRF) that is remotely exploitable without authentication.
Censys Perspective
As this campaign unfolded, we were curious about where the majority of fallout might be observed, both in regards to affected industries as well as geography. Similar to how we studied the 2023 MOVEit Transfer extortion campaign, we set out to understand more about the potential long term impacts of the attack against EBS.
On October 7, 2025, we observed 2,043 EBS instances online globally, with the highest concentrations found in the U.S., China, and India.
As of this post, we observe 2,777 EBS instances online globally–over 700 more than we saw earlier in October. News of this campaign was gaining traction in early October, and it’s possible that administrators had blocked access or taken down EBS instances for patching at the time of our initial measurement. These instances may now be patched and back online.
Industry Impact
Using the Censys Platform, we examined exposed EBS systems as of October 9, 2025, extracted URLs found in HTTP response bodies associated with EBS systems, and categorized the root domain by industry. In total, we identified just over 700 unique domains but were unable to categorize roughly 300 of them due to a variety of factors (e.g., site unavailable, web searches inconclusive as to what the organization is or does).
For the remaining near 400 unique domains, there are a variety of industries represented: Manufacturing and Industrial organizations top the list at just under 14% of total domains we were able to classify, followed closely by organizations in Government (12%), Holding Companies (11%), and the Tech sector (9%).
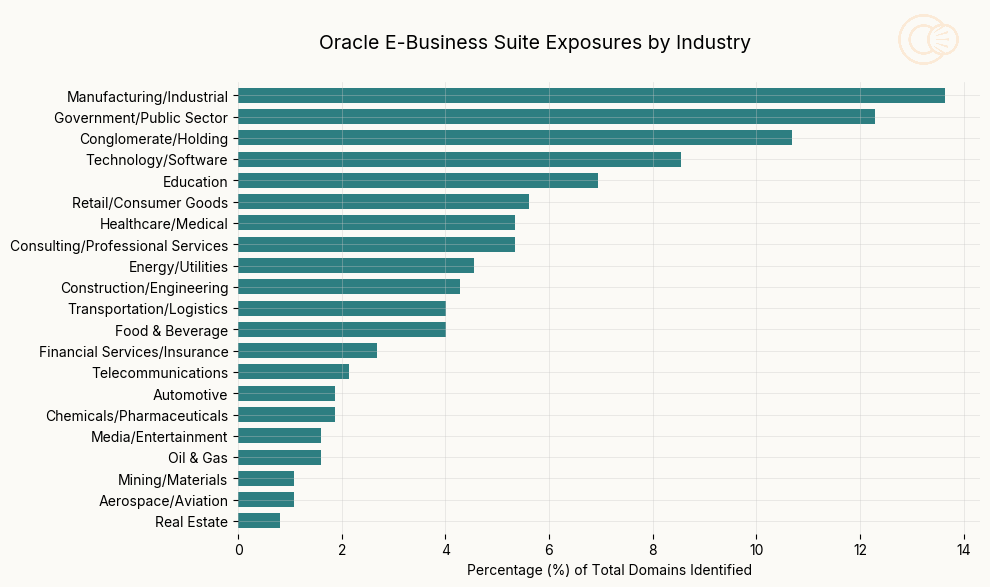
Though not as prominent, collectively representing 6% of observed instances, the presence of Energy/Utilities and Oil & Gas organizations among those with public-facing EBS instances is noteworthy. Much of our prior research into industrial control systems (ICS) and utilities has focused on exposure of sensitive operational technology (OT) devices and systems like human-machine interfaces (HMIs) and programmable logic controllers (PLCs).
However, exposures of IT and business tooling associated with industrial organizations should serve as a reminder that while OT systems are an appealing target for threat actors, sometimes the simplest way in is via the IT network. This is why many OT/IT hardening guides encourage operators and administrators to ensure their IT and OT networks are properly segmented, reducing means of lateral movement.
Geographic Impact
Similar to patterns noted in our earlier observations, we currently find most instances of Oracle EBS in the U.S., China, and India, though there is broad global adoption of the software.
Comparisons to 2023 MOVEit Campaign
Comparisons between this campaign and the 2023 activity against MOVEit have been drawn in a number of publications, and upon closer consideration it’s easy to understand why, despite the different types of software affected.
Perhaps the most obvious parallel between the EBS and MOVEit campaigns is Cl0p’s involvement. In both campaigns, Cl0p leveraged zero-day vulnerabilities to target enterprise software exposed directly to the Internet, enabling them to exfiltrate organizations’ sensitive data. Moreover, in each case, what began as identification of a single vulnerability (MOVEit: CVE-2023-34362, EBS: CVE-2025-61882) and CVE designation cascaded into at least one additional vulnerability rapidly being discovered in each product (two for MOVEit, but who’s counting?). At the time of each of our analyses, there were similar numbers of each product observed online–nearly 3,000 MOVEit instances, and 2,700 EBS instances.
However, there are also interesting differences to note. The geographic spread of Oracle EBS instances is far more global in nature than that of MOVEit in 2023. While the U.S. has the single greatest percentage of exposed EBS systems (36% of total), that’s far less than the percentage of MOVEit systems found in the U.S. in 2023 (69%).
We also note differences in industries potentially affected by these attacks: we found MOVEit primarily in the Financial Services (31%), Healthcare (16%), and Technology (9%) sectors, but EBS appears more prominently in the Manufacturing/Industrial (13%), Government (12%), and Conglomerate/Holding Company (11%) sectors.
Finally, it’s worth discussing the difference in complexity of vulnerabilities that led to each of these tools being exploited. The initial MOVEit vulnerability, CVE-2023-34362, was a SQL injection vulnerability. It feels apropos to mention here that web app injection vulnerabilities (e.g. SQLi) have been a part of the OWASP Top 10 list since its inception in 2003.
In sharp contrast to the MOVEit SQLi, there’s the initial EBS vulnerability, CVE-2025-61882. In the words of WatchTowr Labs researchers:
…CVE-2025-61882 (as it is now memorably called) is not “just” one vulnerability. It is a poetic flow of numerous small/medium weaknesses.
This is noteworthy because (if others can speculate, we are going to as well) whoever first discovered these vulnerabilities and chained them clearly knows Oracle EBS incredibly well at this point.
Ultimately, while Cl0p may rely on a familiar playbook of zero-days and extortion, the downstream effects can differ, depending on the software in their crosshairs.
Conclusions
Similar to observations we made following the 2023 MOVEit campaign, enterprise back office software is a prime target for financially motivated threat actors. It’s often deployed by large, data-rich organizations that are highly motivated to avoid data leaks, making it particularly enticing for these organizations to pay extortion fees.
While there are many similarities between Cl0p’s exploitation of MOVEit and EBS, there are differences in affected industries and geography simply based on adoption of the targeted tool. It’s also interesting to note the range of complexity of the vulnerabilities at play in each of these cases. Regardless, the history of campaigns against such tooling and software makes it clear that threat actors will continue to exploit these systems as long as they are connected directly to the Internet with no additional safeguards.
Not sure if you have sensitive business software exposed to the Internet? Censys can help.