Vulnerability Description
CVE-2025-61882 is a critical vulnerability in the Oracle Concurrent Processing component (BI Publisher Integration) of Oracle E-Business Suite. It involves a pre-authentication remote code execution chain that can be exploited by an unauthenticated attacker with network access via HTTP to completely compromise the Oracle Concurrent Processing subsystem. The vulnerability combines multiple weaknesses including HTTP Request Smuggling, Server-Side Request Forgery (SSRF), Path Traversal, and XML External Entity (XXE) injection.
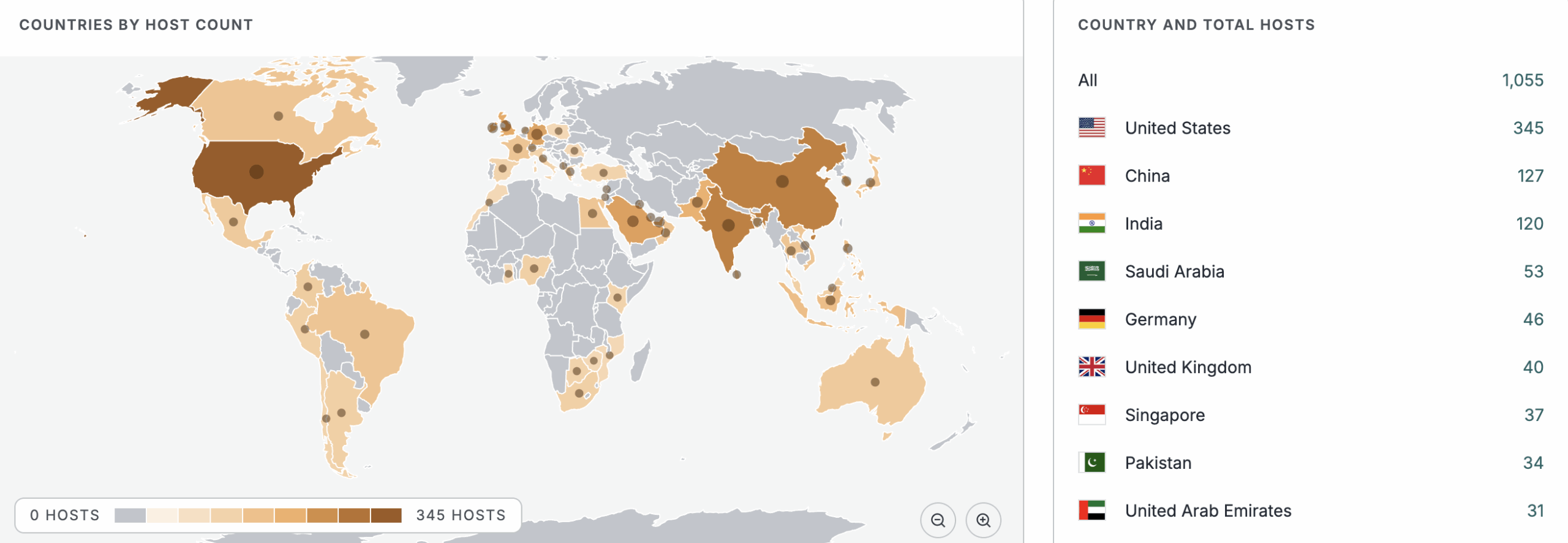
See the full breakdown by country in Censys Platform –>
| Field | Description |
| CVE-ID | CVE-2025-61882 — CVSS 9.8 (critical) — assigned by Oracle |
| Vulnerability Description | Oracle E-Business Suite contains a vulnerability in the Oracle Concurrent Processing product (BI Publisher Integration component) that allows an unauthenticated attacker with network access via HTTP to achieve remote code execution. The vulnerability is a pre-authentication exploit chain combining HTTP Request Smuggling (CWE-444), Server-Side Request Forgery (CWE-918), Path Traversal (CWE-22), and XML External Entity injection (CWE-611). The vulnerability is easily exploitable and requires no user interaction. |
| Date of Disclosure | October 5, 2025 |
| Affected Assets | Oracle E-Business Suite, specifically the Oracle Concurrent Processing component with BI Publisher Integration. |
| Vulnerable Software Versions | Oracle E-Business Suite versions 12.2.3 through 12.2.14. |
| PoC Available? | Yes. A fully functional proof-of-concept exploit chain exists in the wild. WatchTowr Labs obtained and analyzed the PoC, publishing a detailed technical breakdown on October 6, 2025. |
| Exploitation Status | CISA has confirmed active exploitation in the wild and added CVE-2025-61882 to the Known Exploited Vulnerabilities catalog on October 6, 2025, with a remediation deadline of October 27, 2025 for federal agencies. |
| Patch Status | Oracle released fixes in the July 2025 Critical Patch Update. Organizations should upgrade immediately. There are no workarounds. Administrators should restrict network access to Oracle EBS and remove Internet accessibility where possible. |
Censys Perspective
Censys has observed 2,043 internet-accessible Oracle E-Business Suite instances exposed to the internet. Due to the critical nature of this pre-authentication RCE vulnerability, active exploitation confirmed by CISA, public PoC availability, and the sensitive nature of ERP systems, organizations should treat this with extreme urgency.
We recommend immediately identifying Oracle E-Business Suite instances in your environment and verifying they have been patched with the July 2025 CPU. Note that while Censys can identify Oracle E-Business Suite software, version detection is inconsistent across different scanning methods, making it difficult to definitively identify vulnerable instances. Organizations should assume all exposed Oracle EBS instances are vulnerable until patched.
The queries below can help identify Oracle E-Business Suite instances, but they cannot determine if systems are vulnerable. Organizations must verify patch status independently.
web.software: (vendor: “oracle” and product: “e-business_suite”) or web.endpoints.path: “/OA_HTML/” or web.endpoints.http.html_title=”E-Business Suite Home Page Redirect” or web.endpoints.http.headers: (key=”Set-Cookie” and value: “EBS-Cookie=”) or (web.cert.parsed.issuer.organization=”ORACLE” and web.cert.parsed.subject.common_name=”Self-Signed Certificate for EBS_web “)
host.services.software: (vendor=”Oracle” and product=”E-Business Suite”)
services.software: (vendor: “Oracle” and product: “E-Business Suite”)
References
- https://www.oracle.com/security-alerts/alert-cve-2025-61882.html
- https://labs.watchtowr.com/well-well-well-its-another-day-oracle-e-business-suite-pre-auth-rce-chain-cve-2025-61882well-well-well-its-another-day-oracle-e-business-suite-pre-auth-rce-chain-cve-2025-61882/
- https://nvd.nist.gov/vuln/detail/CVE-2025-61882
- https://www.crowdstrike.com/en-us/blog/crowdstrike-identifies-campaign-targeting-oracle-e-business-suite-zero-day-CVE-2025-61882/





