Executive Summary
- CVE-2026-41940, a critical pre-auth bypass in cPanel/WHM, was recently disclosed, coinciding with a sharp spike in hosts classified as malicious across Censys data.
- Analysis shows the May 1 surge was highly concentrated: ~80% of newly malicious hosts were running cPanel/WHM, marking a clear break from baseline activity.
- At least two distinct attack paths are active: one deploying Mirai variants post-compromise, and another involving ransomware that encrypts files and appends a “.sorry” extension.
- Early ransomware indicators are already widespread, with thousands of cPanel hosts exposing encrypted files via open directories, suggesting large-scale automated exploitation is underway.
Introduction
On April 29, 2026, CVE-2026-41940 was disclosed as a critical pre-authentication bypass affecting cPanel and WHM. The issue impacts the login flow and may allow a remote, unauthenticated attacker to bypass authentication controls and gain elevated access to affected systems.
Within 24 hours of disclosure, consistent with timelines tracked by organizations such as Zero Day Clock, the vulnerability appears to have been weaponized by multiple third parties.
Investigating the Spike
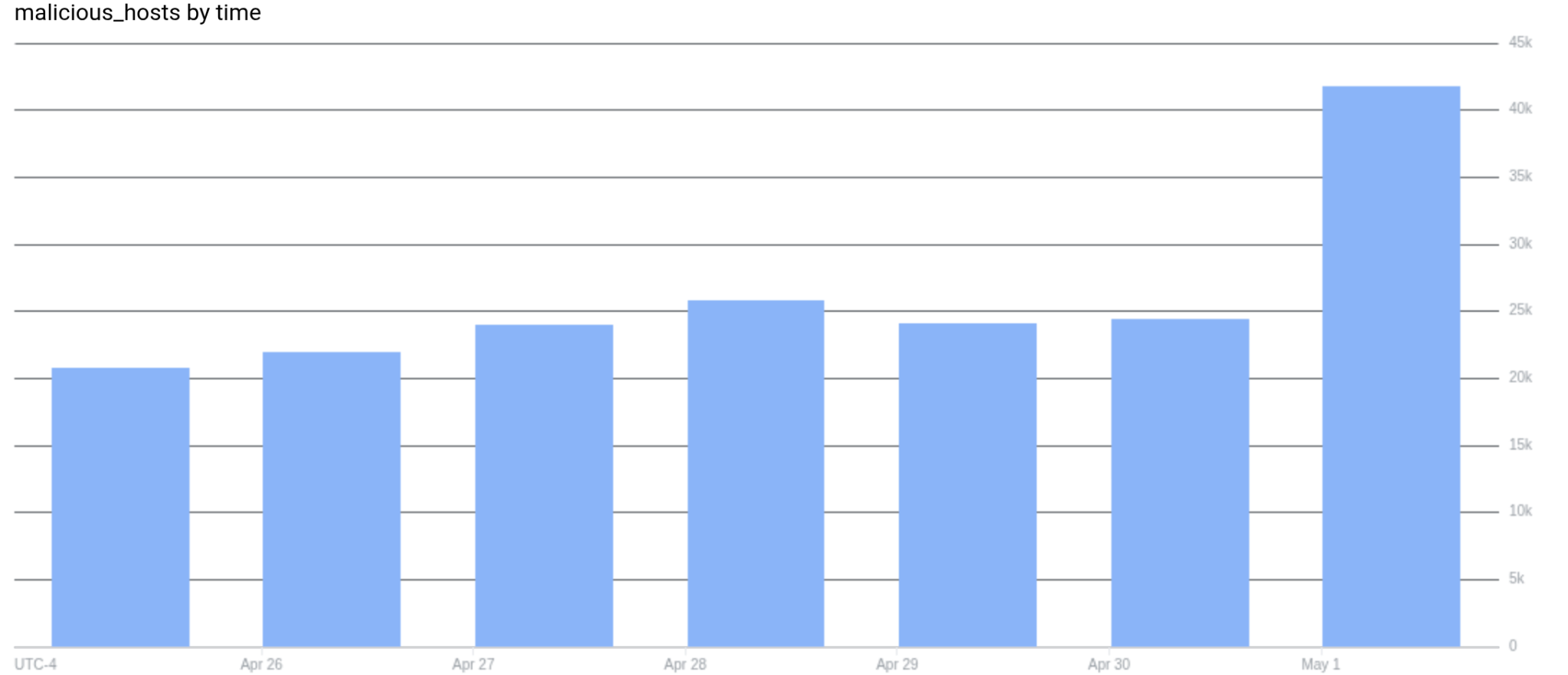
Overnight, Censys observed a sharp increase in the number of hosts newly classified as “malicious” across our dataset, with counts roughly doubling from the previous day. This anomaly triggered an investigation. At the time, the cause of the spike was unclear, and the connection to CVE-2026-41940 was not yet established.
Censys recently partnered with GreyNoise to enrich our dataset with external classification signals. GreyNoise identifies Internet-wide scanning and exploitation activity and labels source IPs based on observed behavior.
By incorporating these labels, Censys can correlate known malicious scanning infrastructure with exposed services, enabling us to link observed attacker activity to the servers they use. This is an incredibly powerful combination.
Note that this feature is not yet generally available to the public, so consider this our announcement teaser.
We then built an aggregate report in Censys grouping on GreyNoise tags (host.greynoise.tags.name) and ordering results by distinct host count to identify the most prevalent malicious classifications.
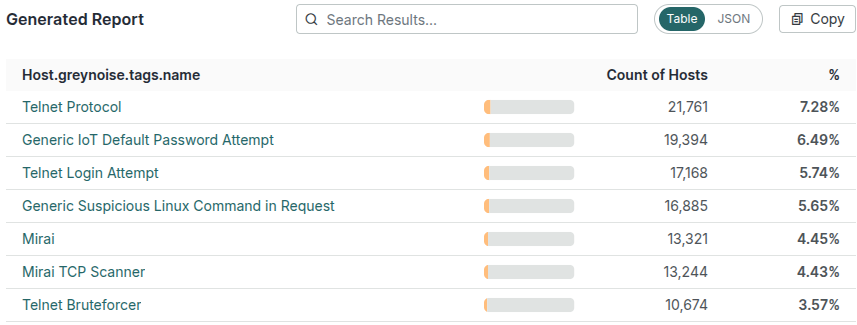
The results largely consist of Telnet brute force activity, with patterns consistent with Mirai; in fact, Mirai is explicitly identified in the classification tags.
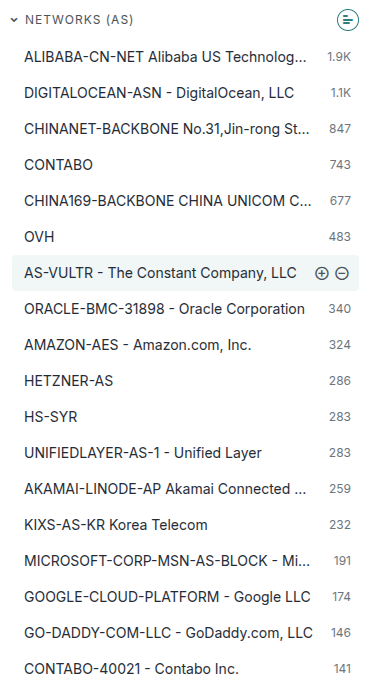
Drilling into the top tag (“Telnet Protocol”) revealed two very clear pictures. The activity was concentrated in autonomous systems tied to VPS and hosting providers (Figure 1), and, more importantly, nearly all hosts associated with these malicious tags were running cPanel.
 |  |
| Figure 1 | Figure 2 |
So this was an ah-ha moment; from the initial search results, it looks like some sort of association with cPanel, and most likely related to CVE-2026-41940.
To validate whether cPanel was actually driving the spike, we compared daily counts of GreyNoise-classified hosts to the subset running cPanel or WHM. In the days leading up to May 1, cPanel systems made up a negligible fraction of maliciously classified hosts, typically ranging from a few dozen to just over 100 out of more than 80,000 total GreyNoise-tagged systems. During this period, day-over-day changes in overall malicious activity were largely independent of cPanel infrastructure, reflecting normal background scanning noise.
That pattern shattered abruptly on May 1. While the total number of GreyNoise-classified hosts increased by roughly 19,000, the number of cPanel systems increased by over 15,000 in the same window. This represents nearly 80% of the net new maliciously classified hosts. This is a clear deviation from prior behavior and indicates that the surge was not broad-based, but overwhelmingly driven by activity targeting cPanel systems.
| Date | GreyNoise Hosts | Δ GreyNoise | cPanel/WHM Hosts | Δ cPanel/WHM | % of Δ from cPanel |
|---|---|---|---|---|---|
| 2026-04-26 | 116,655 | — | 117 | — | — |
| 2026-04-27 | 81,306 | -35,349 | 47 | -70 | 0.20% |
| 2026-04-28 | 81,053 | -253 | 106 | +59 | — |
| 2026-04-29 | 80,979 | -74 | 70 | -36 | 48.65% |
| 2026-04-30 | 87,383 | +6,404 | 146 | +76 | 1.19% |
| 2026-05-01 | 106,514 | +19,131 | 15,448 | +15,302 | 79.99% |
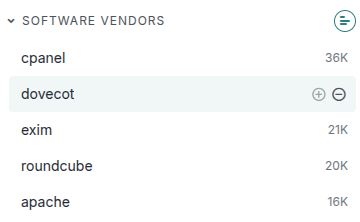
We then identified an unverified post on X (Twitter) from a user (@social5h3ll) claiming that the cPanel vulnerability was being used to deploy a Mirai variant named nuclear.x86.
We wanted to dig further into this claim, so we obtained a sample of the referenced binary (SHA256: 95bcc0a2bb0fff25a2770010406cd0964fd4b3033ed8bae181518f7c8b69d324) and analyzed it to determine whether cPanel exploitation was built directly into the malware, or whether compromised servers were being used to deploy the payload post-exploitation. We found no evidence that cPanel was implemented as an attack module within the binary. This suggests the malware is being deployed after initial compromise, rather than exploiting cPanel directly.
There are currently 1,052,657 hosts in Censys running cPanel/WHM, and at the time of writing, only 9,595 of those have been observed participating in malicious activity. That may not seem like much compared to the whole, but this number is likely to keep growing.
To better understand where this activity is taking place, we can look at these hosts grouped by autonomous system. As stated earlier, the results are heavily skewed toward VPS and cloud hosting providers, and the top 10 providers account for the majority of the total.
| ASN / Provider | Malicious Hosts running cPanel |
|---|---|
| DIGITALOCEAN-ASN – DigitalOcean, LLC | 1,043 |
| CONTABO | 716 |
| OVH | 501 |
| AS-VULTR – The Constant Company, LLC | 391 |
| ORACLE-BMC-31898 – Oracle Corporation | 321 |
| UNIFIEDLAYER-AS-1 – Unified Layer | 280 |
| HETZNER-AS | 277 |
| AKAMAI-LINODE-AP – Akamai Connected Cloud | 275 |
| GO-DADDY-COM-LLC – GoDaddy.com, LLC | 209 |
| MICROSOFT-CORP-MSN-AS-BLOCK – Microsoft Corporation | 169 |
Potential cPanel Ransomware Campaign
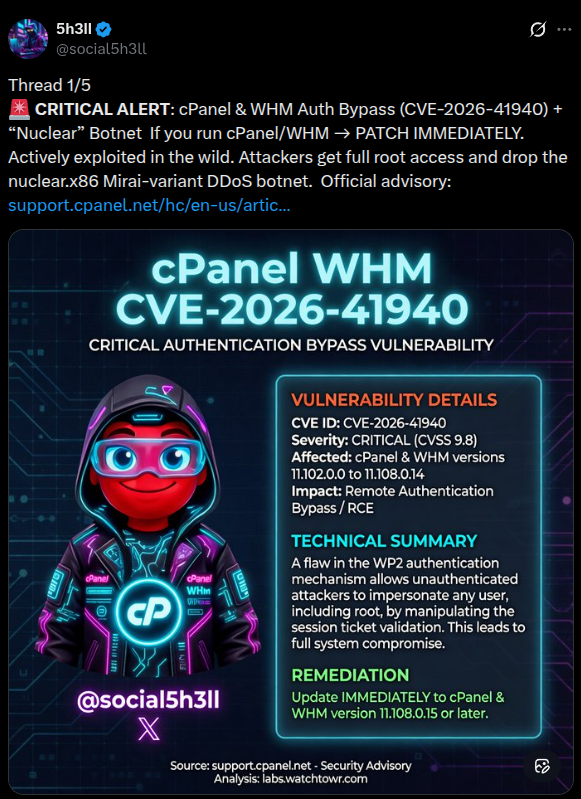
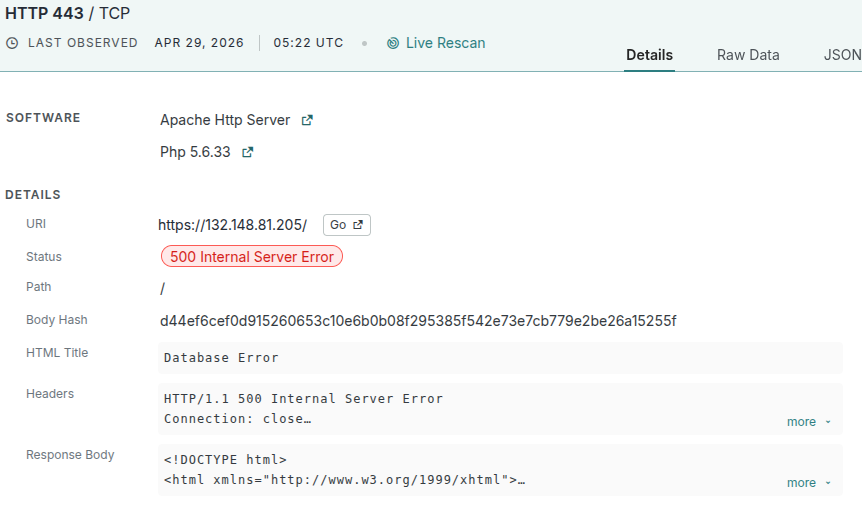
While we were writing this report, we noticed a distinct pattern across a subset of cPanel hosts. Roughly 7,000 servers were exposing open directories, with every file in the listing suffixed with “.sorry”. And those open directories did not exist yesterday. This immediately stood out, as uniform file renaming like this is a common indicator of ransomware activity, where files are encrypted and renamed during the process.
 | 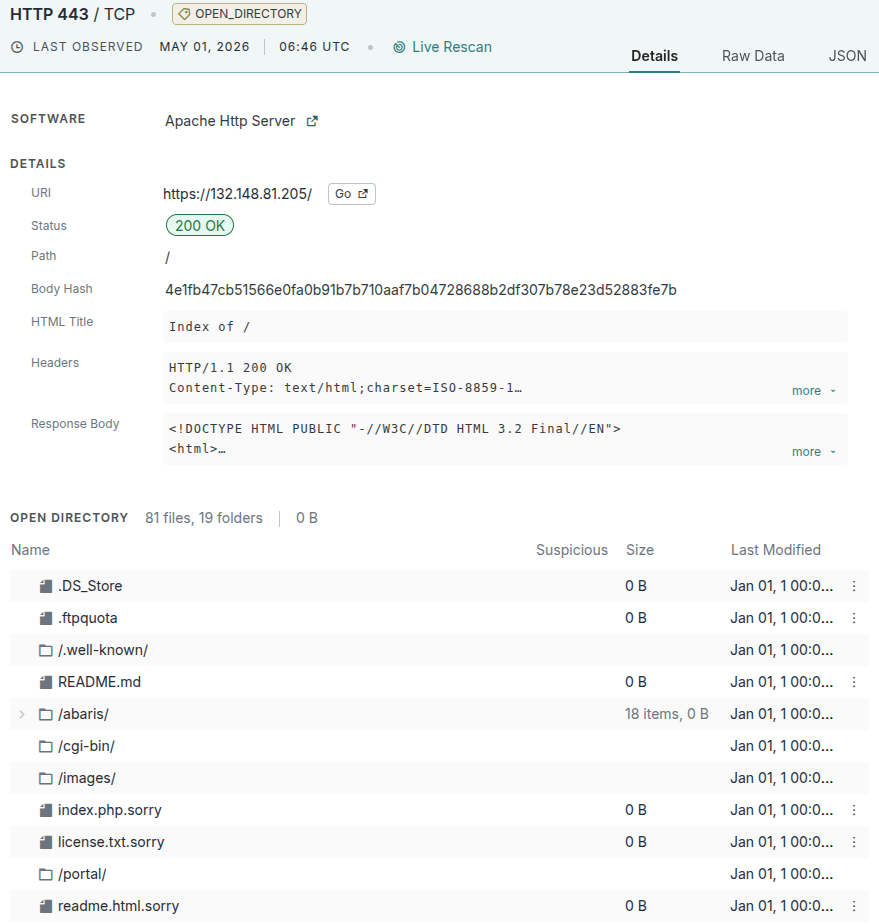 |
| Example host on April 29th, 2026 | Example host on May 1, 2026 |
The “.sorry” file extension has previously been associated with the Hidden-Tear variant of the Sorry Ransomware. In some of these open directories, we found the following ransom note:
Please contact us through the qtox tool
Download qtox https://github.com/qTox/qTox/blob/master/README.md#qtox
If you can't contact us, please contact some data recovery company(suggest taobao.com), may they can contact to us.
Add our TOX ID and send an encrypted file and 'Sorry-ID' for testing decryption.
Our TOX ID: 3D7889AEC00F2325E1A3FBC0ACA4E521670497F11E47FDE13EADE8FED3144B5EB56D6B198724Conclusion
This event is still developing, so the full scope is unclear, but the pattern suggests a coordinated ransomware campaign targeting exposed cPanel/WHM systems.
There are currently 8,859 hosts on the Internet exposing open directories where filenames end in “.sorry”. Of those,7,135 hosts are identified as running cPanel or WHM, indicating that the majority of affected systems fall into this category.
We can break this down further by examining the specific filenames exposed in these open directories. The pattern is consistent across hosts: the same set of common web application files are being renamed with a “.sorry” suffix.
| Filename | Hosts |
|---|---|
| index.html.sorry | 6,465 |
| index.php.sorry | 1,637 |
| license.txt.sorry | 855 |
| wp-activate.php.sorry | 798 |
| wp-config.php.sorry | 795 |
| wp-cron.php.sorry | 793 |
| wp-load.php.sorry | 793 |
| wp-links-opml.php.sorry | 792 |
| wp-mail.php.sorry | 792 |
| wp-settings.php.sorry | 791 |
At this point, there appear to be at least two separate campaigns targeting cPanel: one deploying Mirai variants, and another consistent with ransomware activity. There are likely additional campaigns underway, but these are the two we were able to clearly identify from scan data.