Thank you for joining us for the third installment of our 2025 State of the Internet Report. Previously, we looked at the intersection of our Rapid Response vulnerability reports and threat actor activity. This report will look closely at two investigations from the Censys Research team over the past year.
At Censys, our broad scanning of the Internet enables us to uniquely identify threat actor infrastructure. Malware control servers, phishing pages, and other malicious infrastructure often rely on Internet-exposed services to allow for access by both operators and targets. Sometimes, the identifiable parts of this attack surface take the form of an admin web panel or an exposed service that only responds to a custom protocol.
Throughout the past year, we mapped out spikes of botnet activity consisting of smart entertainment systems, DDoS control infrastructure and malware targeting ASUS routers. For the third part of our SOTIR25 report, we took a more in-depth look at two long-running malware investigations.
Wainscot (aka Waiscot)
In December 2024, Black Lotus Labs published a report titled Snowblind: The Invisible Hand of Secret Blizzard about a series of intrusions conducted by the Russia-linked APT group Secret Blizzard (known commonly as Turla) against Storm-0156, a Pakistan-linked threat cluster that shares overlaps with the threat actors SideCopy and Transparent Tribe (aka APT36). Beginning in December 2022, Secret Blizzard allegedly targeted various malware command and control platforms used by Storm-0156. This access would have provided Secret Blizzard with a range of capabilities, from leveraging existing Storm-0156 access to conducting counter attribution activities.
Our analysis of this campaign led to a successful sinkhole operation in which we identified an additional Indian military target of Storm-0156 through domain sinkholing. This infection leveraged a suspected variant of the Wainscot malware to automatically exfiltrate data from a system believed to be in a rural conflict zone with intermittent Internet connectivity.
Secret Blizzard is a threat actor tracked by Microsoft that significantly overlaps with the activity commonly referred to as Waterburg, Turla, SIG23, Venomous Bear, Snake and G0010. With over two decades of activity and a reputation for sophistication, Secret Blizzard remains a persistent threat. This report focuses on a specific subset of its operations tracked from December 2022 through November 2024 that targeted Storm-0156, a threat actor believed to be associated with the Pakistani government.
While targeting of other threat actors may be more prevalent with criminally motivated actors, attacks between nation-state affiliated threat groups are rare. Within this rare space, Turla has been a historically active player, leveraging vulnerabilities within the publicly facing attack surface of other threat actors’ tooling. In 2017, Symantec tracked a campaign under the name Waterbug in which the Russian threat actor Turla reportedly compromised the Iranian group APT34 (aka OilRig) and leveraged their infrastructure and access to deploy Turla-linked malware against Middle Eastern government networks.
From Lumen’s reporting, we focused on the infrastructure of Storm-0156, believed to have been targeted by Secret Blizzard. When evaluating 154.53.42[.]194 in Censys data, we noticed the domain secdesk[.]xyz was available, so we registered it and redirected all subdomains to a sinkhole, a.k.a. a server we set up to intercept malicious traffic.
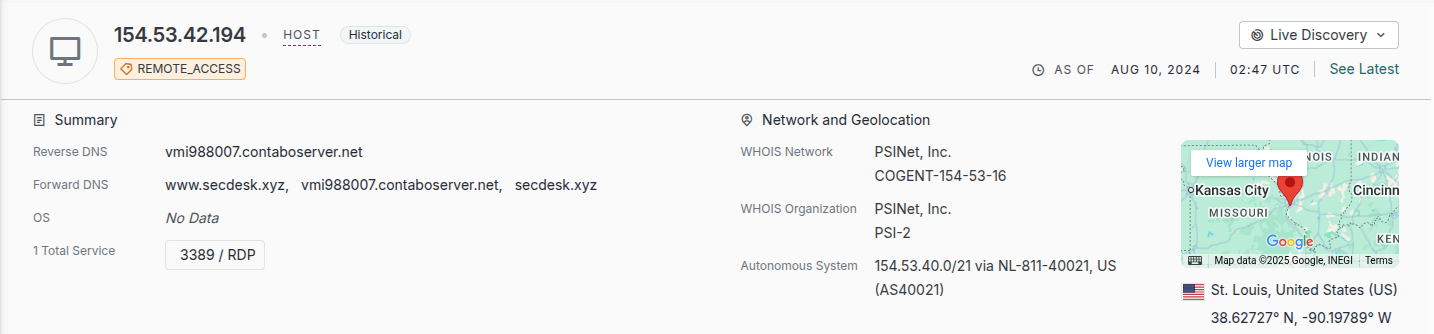
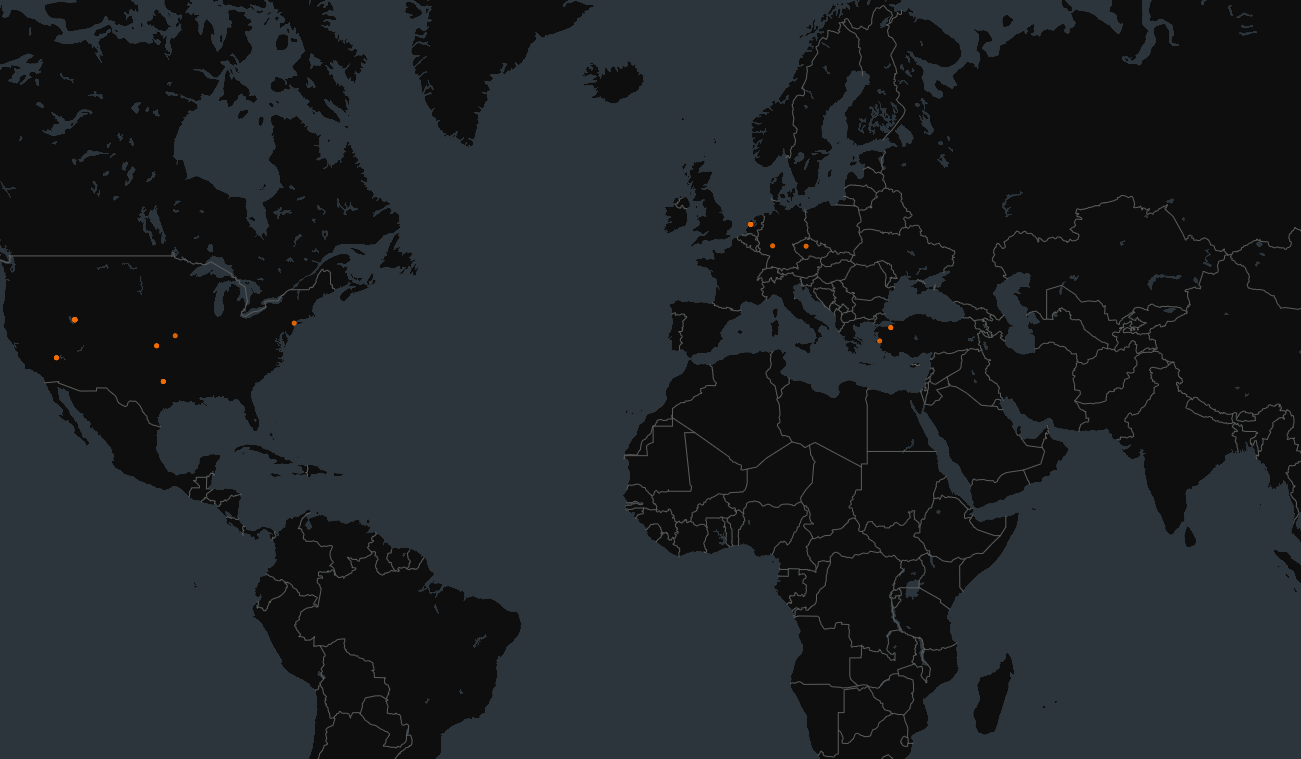
This sinkhole collected traffic destined for this domain. Reports on VirusTotal linked this domain to copies of the Wainscot malware, configured with secdesk[.]xyz:8062/one for command and control. Analysis of inbound sinkhole traffic matched observed sandbox activity, with a distinctive modification not present in previously reported behavior. Results over the next two months showed a single host infected with Wainscot attempting to exfiltrate data to the sinkhole at unpredictable intervals from a different IPv4 address. The following map shows mapped locations for each observed address:
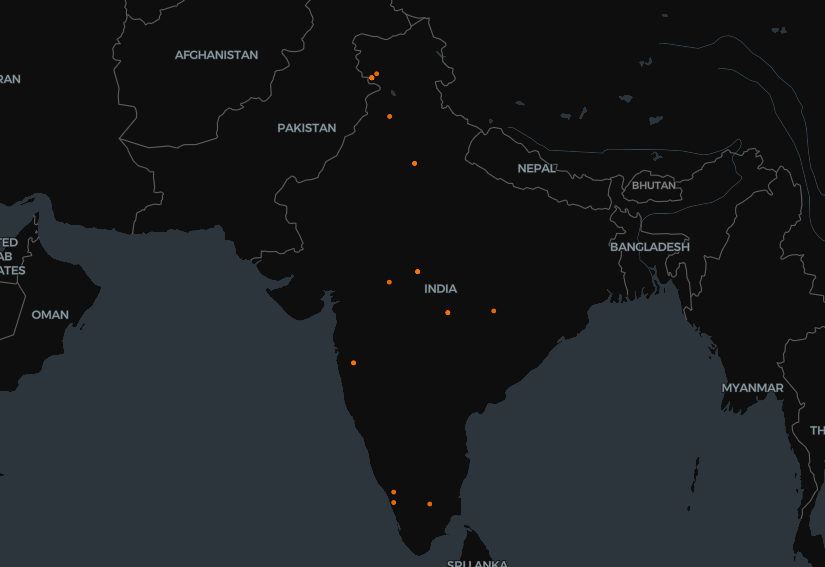
When a host is seen routinely checking into a sinkhole from different IP addresses, it is commonly associated with an infected system using a dial-up, satellite or mobile connection in which Internet traffic may not always be assumed. If the threat actor knew in advance this system may have non-continuous Internet access, Wainscot may have been intentionally modified to track files and exfiltrate them whenever Internet connectivity to support this target. This theory is supported by observations of the infected host attempting to upload identical files across various check-in periods.
Wainscot typically takes action based on actor tasking, such as listing files, running system commands, and uploading or downloading files. When operating a sinkhole, inbound requests are almost always check-in requests, in which an infected host is requesting tasking from a threat actor. Inbound requests to our sinkhole did not follow this process. Instead, upon connection the observed infected system would instead automatically begin sending documents and images.
Analysis of recovered data indicated the infected system was likely operated by a battalion in the Territorial Army of India along the border of Pakistan. Upon identification, the Censys Research contacted the Indian Computer Emergency Response Team (CERT-IN) to report the incident. While it may be inappropriate for a CERT to confirm the outcome of an incident report, we have not observed requests from this infection since February 2025 and we now believe this infection to be remediated.
BeaverTail
Throughout 2024, reports of individuals from the Democratic People’s Republic of Korea (DPRK) leveraging fake identities to gain employment at companies in the technology sector became more frequent. Also seen targeting freelance developers, this activity has been financially motivated, resulting in outcomes such as extortion, theft of sensitive information and technology, and leveraging of access for additional attacks.
Starting in the late 2010s, technology companies and cryptocurrency exchanges began facing a new insider threat from DPRK remote workers. Using stolen or artificial identities to hide their identity, DPRK is believed to have thousands of individuals working in satellite locations in China, Russia, Vietnam and other nearby countries, all collectively working to raise funding for the North Korean government. Since the COVID pandemic and supported by AI tooling, reported activity has significantly increased in scale and reach of targeting.
In October 2024, Palo Alto’s Unit 42 published Contagious Interview which detailed an ongoing campaign involving DPRK operators targeting job seekers through fake recruitment opportunities. Described in this report are two closely related python-based malware families, BeaverTail and InvisibleFerret. Often shared under the masquerade of a video conferencing application, BeaverTail acts as an initial information stealer and subsequently deploys InvisibleFerret, a backdoor written in Python with keylogging and remote control functionality.
Starting in March 2025, we began closely tracking the BeaverTail malware using the Censys Platform. Results can be seen labeled in the Platform:
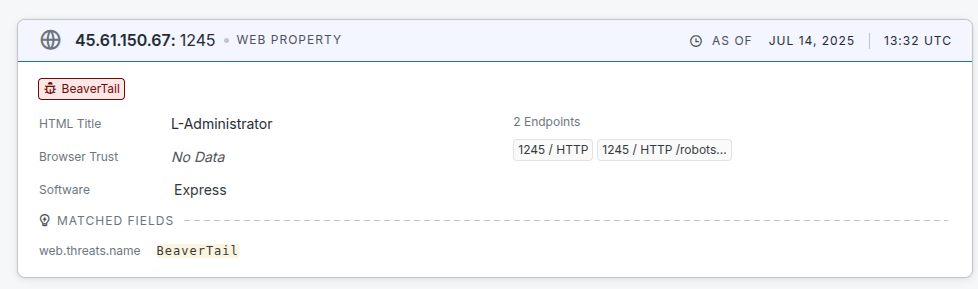
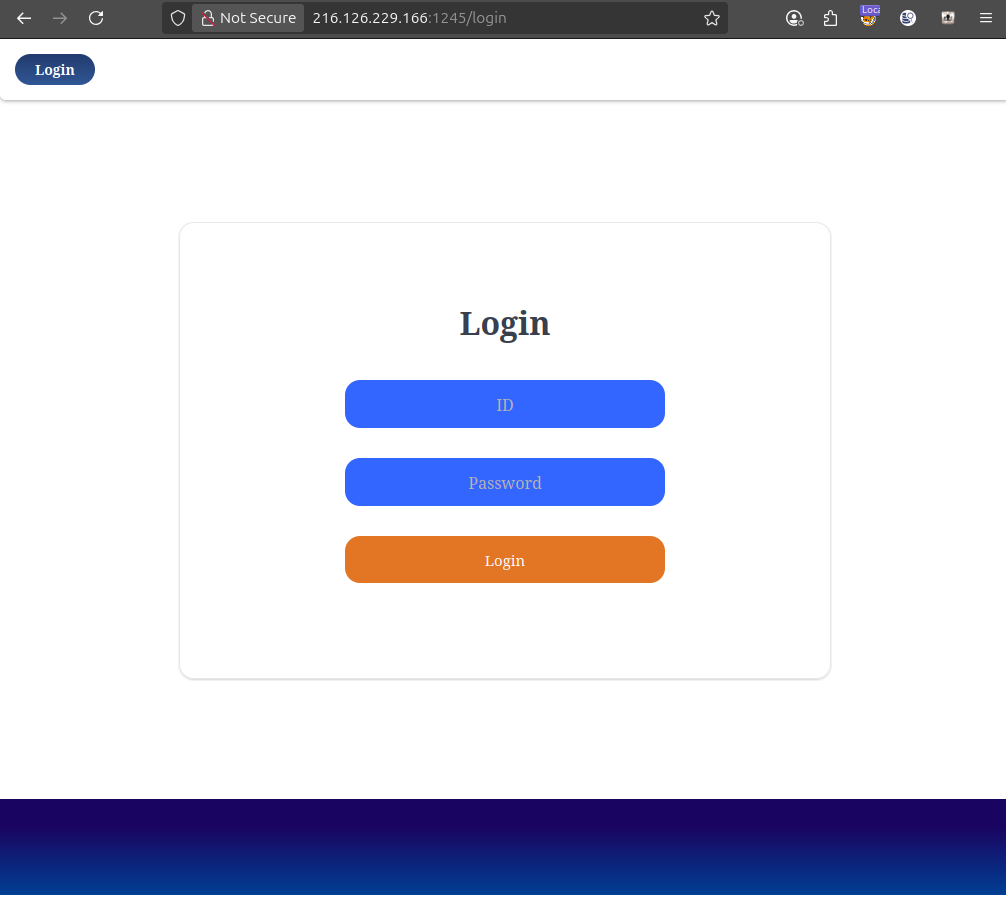
As we identified BeaverTail control servers, TCP ports 1224,1225 and 3000 were consistently observed open on these hosts for receiving callbacks from infected systems. Notably, varied services were observed between control servers, with some hosts exposing only a service for communicating with infected hosts and some others exposing a login panel, likely a control panel for actor control of infected systems. A screenshot of this login panel is shown below:
Typically, we see 4 control servers online at any given time. However, based on overlapping payloads, this may be a reflection of the actor operating a layer of proxies before action control server instances. Notably, operators of BeaverTail have heavily favored the VPS provider Cloudzy (commonly seen as RouterHosting in ASN details) as part of this infrastructure. Previous public reporting has raised concerns about Cloudzy’s ownership and limited response to abuse reporting.
When mapped, we can see a concentration of control servers hosted in Europe and the United States.
Despite reporting on BeaverTail by multiple industry and government entities, BeaverTail continues to see operational use through July 2025. Its use as part of typosquatting attacks against package repositories and broad targeting of developers is likely to continue until detection capabilities significantly reduce this malware’s overall effectiveness. While additional tools have been observed, such as OtterCookie – a rudimentary Javascript based backdoor, it has yet to replace BeaverTail.
Conclusion
Our investigations offer several distinct views into modern threat actor behavior. Storm-0156’s suspected modifications to Wainscot were likely a resourceful way to support exfiltration from a targeted system with unreliable Internet connectivity. The strategic exploitation by SilentBlizzard against other threat actors allows them to both mirror collected information of intelligence targets and opportunistically leverage existing access for enablement.
With BeaverTail, we see persistent targeting of software developers leveraging techniques and services consistent with other freelance developers. Sharing backdoored code projects on Github and using package repositories to stage loaders are ways this actor tailors their lures to improve their odds of success. These campaigns remain effective not because of technical sophistication, but because of adaptability and persistence.
The 2025 State of the Internet Report continues with Part 4 that examines C2 Time-to-Live lifespan.