Introduction
This week marks the conclusion of our 2025 State of the Internet Report series, where we examined various aspects of malicious infrastructure on the Internet. Using our comprehensive map of the Internet, we explored coordinated C2 takedowns, malware linked to the Democratic People’s Republic of Korea (DPRK)’s fraudulent employment operations, lifespans of C2 servers and open web directories, and the use of residential network devices as proxies for malicious activity.
If you’d like to explore the series in detail, you can find the posts here:
- Introduction
- Notable Incidents
- Malware Investigations
- C2 Time to Live
- Digging Into Residential Proxy Infrastructure
- Open Directories Time to Live
We present a summary of each section below, though we highly recommend reading the original posts linked above.
Notable Incidents
In our first installment of this series, we provided deeper analysis of several major security events from 2024, the first two of which we covered previously as a part of Rapid Response.
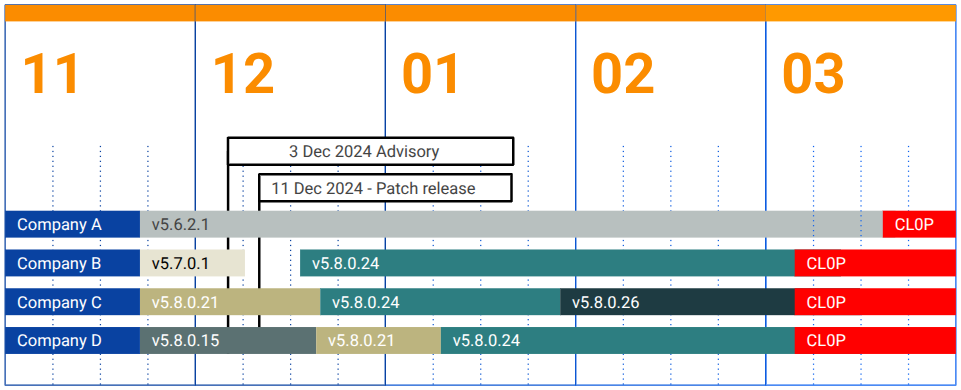
- We began by examining a combination of unauthenticated remote code execution and unrestricted file upload / download vulnerabilities in Cleo file transfer software. These vulnerabilities were exploited by CL0P and Termite ransomware groups starting in December 2024, with varying degrees of success–CL0P claimed 378 victim organizations, while Termite claimed 12. We also explored timelines of several victim organizations–from the Cleo advisory and patch releases, to organizational patching behavior, to finally appearing on CL0P’s data leak site.
- Next, we studied a zero day vulnerability in FortiOS andFortiProxy that was linked to DragonForce ransomware attacks through artifacts discovered in an open directory. The ransomware operation may have tested over 250,000 IP addresses and ultimately appeared to have compromised 31 devices.
- Finally, we revisited Operation Morpheus, a global disruption of pirated Cobalt Strike instances. spearheaded by the UK’s National Crime Agency. The effort achieved an 85% success rate, taking down 593 out of 690 targeted pirated Cobalt Strike instances in June 2024.
Malware Investigations
In our second post of the series, we walked through two malware investigations our team recently conducted.
- Our first investigation involved Wainscot malware, in which the Russia-linked APT group Secret Blizzard (Turla) targeted Storm-0156, a Pakistan-linked threat cluster. Through a successful sinkhole operation, we discovered an infected Indian military system along the Pakistan border that was automatically exfiltrating data using a modified version of Wainscot designed to work with intermittent Internet connectivity. The team reported this incident to India’s CERT-IN and the infection appears to have been remediated.
- The second investigation focused on BeaverTail malware, part of an ongoing campaign by North Korean operators using fake identities to target software developers and job seekers through fraudulent recruitment opportunities. This Python-based information stealer subsequently deploys InvisibleFerret, a backdoor with keylogging and remote control capabilities. Despite multiple industry reports, BeaverTail continues to operate effectively through July 2025, primarily hosted on Cloudzy VPS infrastructure across Europe and the United States.
C2 Time to Live
This week, we explored the concept of Time to Live (TTL) for command and control (C2) infrastructure.
- We analyzed the lifespans of Cobalt Strike and Viper C2 services from both network availability and content-based perspectives. The study revealed substantial differences between the two families: Cobalt Strike services are much shorter-lived with average/median TTLs of 11.2/5.0 days, while Viper services exhibit longer lifespans at 17.4/18.5 days. We hypothesized this difference stems from Cobalt Strike’s higher prevalence and recognition, leading to more varied operational behaviors.
| Average | Median | 25th percentile | 75th percentile | Max | |
| Cobalt Strike | 11.2 | 5.0 | 3.0 | 19.0 | 30 |
| Viper | 17.4 | 18.5 | 4.0 | 30.0 | 30.0 |
- Our analysis also revealed substantial variation within C2 families based on specific ports used, and discussed a content-based tracking method using Cobalt Strike watermarks embedded in beacons. This content-based approach showed slightly longer service lifespans (11.1/6.0 days average/median) compared to network-only tracking, highlighting that service availability and content persistence don’t always align. Breadth AND depth is key to investigations.
Residential Proxy Infrastructure
In this installment, we took an in-depth look at PolarEdge, a large-scale IoT botnet with suspected Operational Relay Box (ORB) characteristics.
- According to research from Sekoia, the botnet compromises a mix of enterprise-grade devices (Cisco APIC controllers, ASA firewalls) and consumer-grade equipment (ASUS routers, Synology NAS devices, IP cameras, VoIP phones) using a custom TLS backdoor derived from Mbed TLS.
- The campaign began in June 2023 and has grown from approximately 150 infections to nearly 40,000 active devices by August 2025, with infections heavily concentrated in South Korea (51.6%) and the United States (21.1%). Most compromised hosts present the backdoor on high, nonstandard ports between TCP/40000–50000 to evade detection.

- What makes PolarEdge particularly concerning is its role in creating residential proxy networks that route malicious traffic through trusted consumer IP addresses, making attacks much harder to detect and block than those originating from data centers.
- PolarEdge demonstrates exceptional persistence with very low infrastructure churn, maintaining long-lived access to compromised devices. This stealthy approach, combined with the use of legitimate encryption and randomized high ports, allows the botnet to hide in plain sight while potentially supporting multiple purposes including automated scanning, credential harvesting, and serving as proxy infrastructure for malicious operations.
Open Directory Time to Live
In our final piece of research in this series, we investigated the lifespans of open web directories–publicly accessible filesystems that often contain malicious payloads and files.
- Unlike previous analyses of C2 infrastructure that could rely on distinctive watermarks for tracking, open directories required a different approach. We used rolling hash algorithm TLSH to compare the similarity of directory contents over time, examining both network availability and content persistence during April 2025.

- We discovered substantial discrepancies between network and content lifespans: open directories have a median network lifespan of 1 day, meaning they frequently disappear and reappear from a network perspective, but the median content lifespan is 3 days. This reveals that content doesn’t necessarily change even when network visibility fluctuates.
- The ability to monitor content persistence allows defenders to understand how open directories evolve and change over time, regardless of their intermittent network availability.
Conclusions
With this series, we illustrated Censys’s visibility into malicious and adversary-controlled infrastructure, highlighting interesting findings from our research over the previous year. These analyses emphasized how Internet-wide scan data can provide insights into threat actor capabilities and behaviors, patching cadences, proxy infrastructure proliferation, lifespans of malicious services, and the measurable impact of disruption operations on the cybercrime ecosystem.
Though we studied malicious infrastructure through various lenses throughout this series, a common theme emerges: access to the most accurate, up-to-date data on Internet infrastructure is key to understanding and tracking threat actor operations and behavior.