The Censys–ThreatQ integration enriches threat indicators on demand and at scale by pulling deep, real-time Internet intelligence directly into the ThreatQ platform. Customers gain immediate visibility into additional IP, domain, FQDN, and certificate context, allowing teams to quickly prioritize, score, and act on the most relevant threats and exposures. This integration reduces investigation time, improves confidence in decision making, and keeps defensive actions continuously up to date.
Integration Highlights
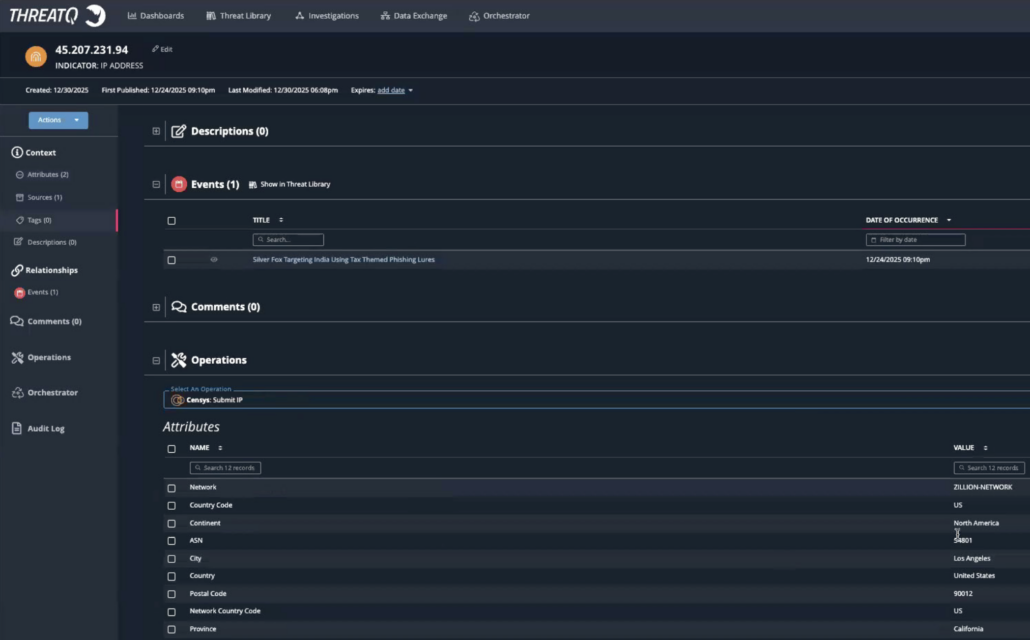
- On-demand enrichment: Analysts can query Censys directly from individual indicators in ThreatQuotient to instantly retrieve expanded attribution and context.
- Automated bulk enrichment: Scheduled workflows enrich filtered indicator collections, scaling investigations from single IOCs to hundreds at once.
- Flexible data controls: Customers choose which Censys attributes to ingest into ThreatQuotient, tailoring enrichment to their operational needs.
- Improved prioritization: Enriched attributes feed ThreatQ scoring and filtering to reduce large indicator sets into actionable, high-priority lists.
- Continuous intelligence refresh: Scheduled reprocessing ensures indicators stay current as Censys discovers new infrastructure and relationships.
- Downstream action enablement: Prioritized intelligence can trigger additional automations, such as blocking indicators across security controls.
ThreatQuotient Platform
The ThreatQuotient solutions make security operations more efficient and effective. The ThreatQ data-driven threat intelligence platform is both open and extensible, supporting the integration of disparate security technologies into a single security infrastructure, automating actions and workflows so that tools and people can work in unison. Empowered with continuous prioritization based on their organization’s unique risk profile, security teams can focus resources on the most relevant threats, and collaboratively investigate and respond with the aim of taking the right actions faster.
Censys Internet Intelligence
The Censys Platform and Censys Attack Surface Management (ASM) are powered by the Censys Internet Map that scans every asset on the Internet to deliver visibility, accuracy, and timeliness unmatched by any other solutions in the market.
The Censys Platform tracks adversary infrastructure in real time, surfacing malicious domains, phishing infrastructure, and command-and-control (C2) servers to help detect threats before they impact your organization. Censys ASM continuously maps internet-facing assets, including cloud environments and unmanaged services, enabling identification of risks, elimination of blind spots, and proactive protection against sophisticated attacks.




