Executive Summary
- 330+ Ubiquiti devices currently display a defacement banner suggesting they’ve used default credentials, reused a password, were infected by a worm, or compromised in some other way, with first reports of these banners dating back to 2016.
- Though these several hundred defaced hosts linger, we observe a 75% decrease in the number of hosts displaying the defaced banners from January 2022 through August 2025.
- Affected devices are primarily found on consumer and residential ISPs, suggesting that these may belong to smaller organizations. Over a third of the defaced hosts are found in the U.S., with a strong presence across Eastern Europe as well.
- Scanning the Internet for signs of compromised devices is a well-established technique, yet it continues to bring visibility to breached infrastructure that may have been forgotten but remains on the Internet–sometimes up to a decade after initial compromise.
Introduction
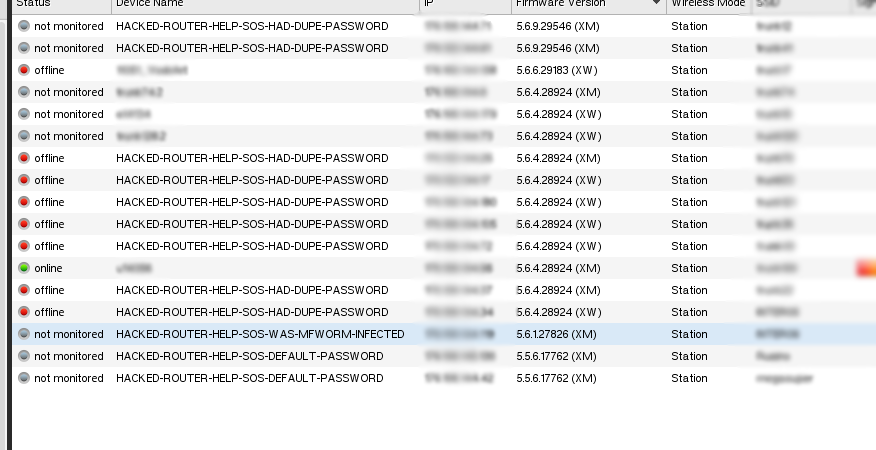
They say nothing gold can stay, but defaced router device names certainly can stick around. Recently while exploring data in the Censys Platform, we identified roughly 330 hosts with banners prefixed with “HACKED-ROUTER-HELP-.” While this is a relatively small number of hosts, a quick web search for this phrase took us down an unexpected rabbit hole. We identified multiple variants of this banner in our data, including “HACKED-ROUTER-HELP-SOS-HAD-DUPE-PASSWORD,” “HACKED-ROUTER-HELP-SOS-DEFAULT-PASSWORD,” and “HACKED-ROUTER-HELP-SOS-WAS-MFWORM-INFECTED,” along with other variants whose existence stretch back nearly a decade.
All affected hosts appear to be Ubiquiti devices and the banner primarily appears on the Ubiquiti service on 10001/UDP, though there are several instances of the defacement string on telnet 23/TCP or 10123/TCP.
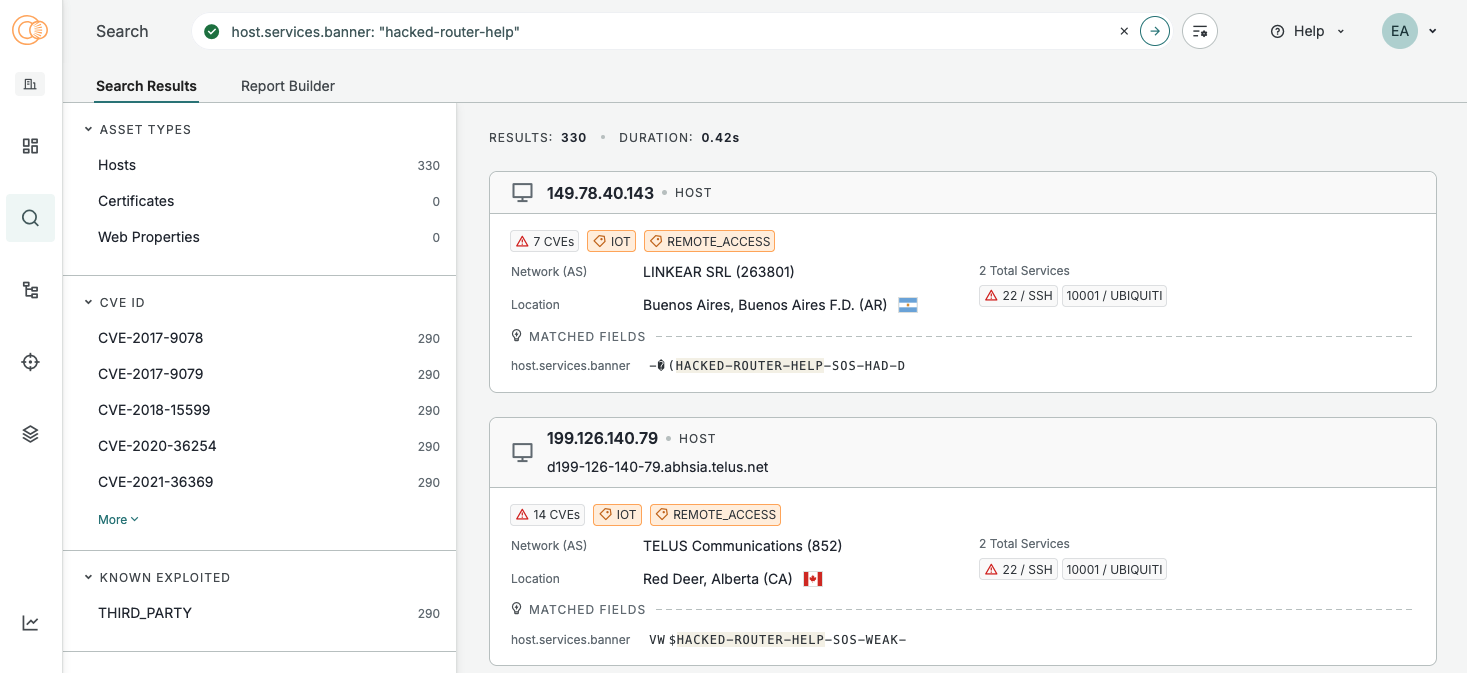
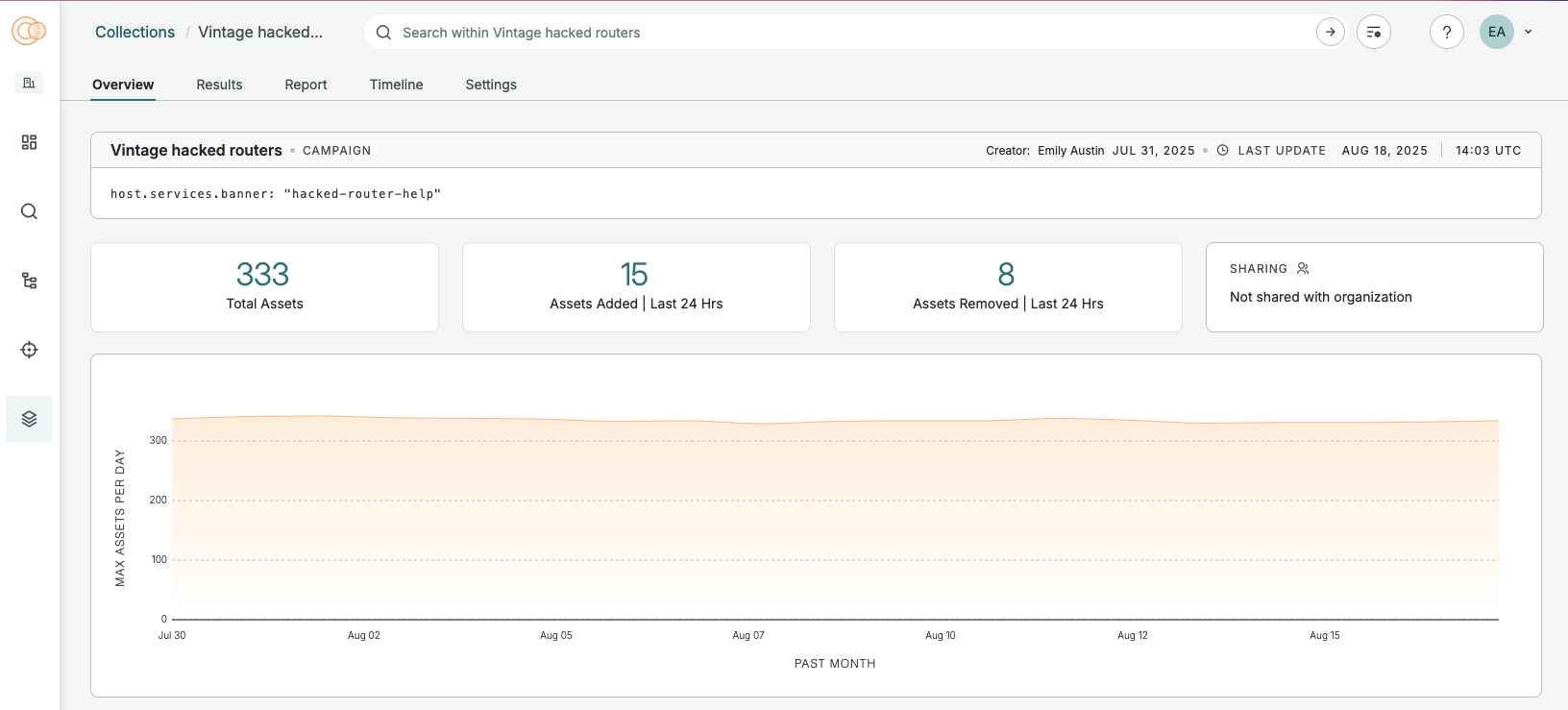
After a bit of manual investigation of these hosts, we set up a Collection to better track these devices. In Censys Platform, a Collection is a saved set of query results that update automatically as our underlying data changes, allowing for better tracking over time.
We note that searching for “hacked” or other notable strings in service banners is hardly a new or novel technique, but it can occasionally surface interesting findings. In this case, the interesting finding is that this is extremely not new or novel–rather, this is about defacement artifacts that have likely lingered for years.
Campaign History
August 2016 marks the earliest mention of these “HACKED-ROUTER” device names we could find. Ubiquiti forum user “LifeBoat” turned to the community for help after noticing that multiple airMAX devices on their network suddenly had names like “HACKED-ROUTER-HELP-SOS-DEFAULT-PASSWORD.”
The post mentions the MF worm which hit Ubiquiti devices in May 2016 as a possible culprit, though the user claims that credentials associated with the worm didn’t work on their devices as they tried to login post-compromise. Notably, “HACKED-ROUTER-HELP-SOS-WAS-MFWORM-INFECTED” shows up as a device name in the inventory screenshot they provided.
According to Symantec research from May 2016, the MF worm leveraged an arbitrary file upload vulnerability to load and copy itself to devices. It then went on to create a backdoor account with credentials mother:f*cker (censorship ours), blocked admins from access, and began to look for other devices on the same network to which it could spread.
There is no mention of defaced device names in Symantec’s research, other reporting, or Ubiquiti forum posts about the MF worm at the time, suggesting that the defaced hostnames are likely unrelated to the initial MF worm campaign.
Roughly a year later in 2017, a researcher noted thousands of Ubiquiti devices with the “DUPE-PASSWORD” variant online.

In 2018, though there don’t appear to have been new findings regarding these devices, Bleeping Computer reported on both Ubiquiti device defacements and a newer, similar campaign against MikroTik routers.
In this 2019 post about analyzing Internet scan data with R, we noticed an additional variant of the banner in the dataset used for analysis, shown below:
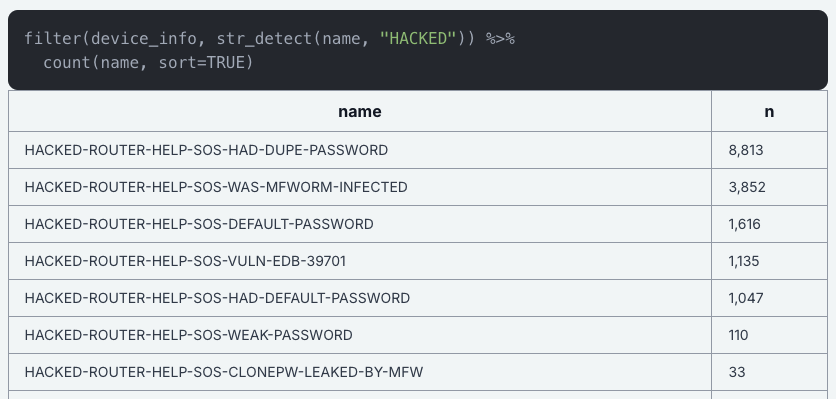
As of our current analysis, we observe at least one of all variants shown above except “CLONEPW-LEAKED-BY-MFW.”
In following years, researchers studying router compromises and Ubiquiti vulnerabilities have noted instances of these banners still present among the greater Ubiquiti device population.
Current Host Profiles
As of this analysis, 82% of hosts with a “HACKED-ROUTER-HELP” banner are running Ubiquiti/10001/UDP and SSH/22/TCP; 9% have only the Ubiquiti service running. We also find multiple one-off instances of hosts with some combination of HTTP, telnet, SSH, and/or the Ubiquiti service running.
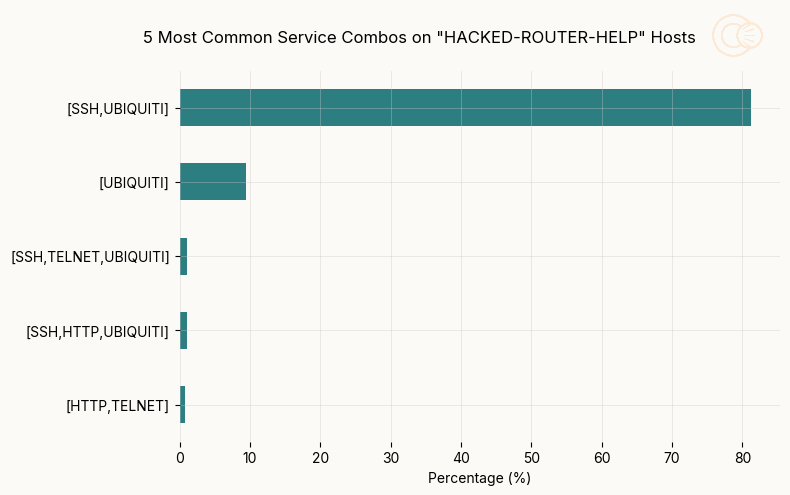
In the few cases where there is not a Ubiquiti service running, the defaced banner appears on TELNET/23 while a certificate with Ubiquiti in the subject and issuer DN appears on HTTP/443.
| Defaced Banner | Percent of Current Total |
| HACKED-ROUTER-HELP-SOS-WAS-MFWORM-INFECTED | 40.8 |
| HACKED-ROUTER-HELP-SOS-HAD-DUPE-PASSWORD | 27.5 |
| HACKED-ROUTER-HELP-SOS-HAD-DEFAULT-PASSWORD | 14.4 |
| HACKED-ROUTER-HELP-SOS-DEFAULT-PASSWORD | 10.8 |
| HACKED-ROUTER-HELP-SOS-VULN-EDB-39701 | 6.1 |
| HACKED-ROUTER-HELP-SOS-WEAK-PASSWORD | 0.2 |
We puzzled earlier over the relationship between the MF worm and these banners, and given the other banners that appear on these devices, we believe these are indications of how the devices were compromised to accomplish the defacements.
Most of the banners are straightforward, but we explore them here:
- HACKED-ROUTER-HELP-SOS-WAS-MFWORM-INFECTED
- We never found evidence of banner defacement reported as an indicator of compromise (IOC) for the MF worm. Part of the MF worm’s process was to create a backdoor account with widely known credentials, so it’s possible the actor behind the defacements tried “mother:f*cker” as credentials. When successful, this banner would be displayed.
- HACKED-ROUTER-HELP-SOS-HAD-DUPE-PASSWORD
- This banner likely indicates that multiple devices on the same network reused credentials–once a valid set of credentials was identified, it would be trivial to try those credentials against other devices.
- HACKED-ROUTER-HELP-SOS-HAD-DEFAULT-PASSWORD / HACKED-ROUTER-HELP-SOS-DEFAULT-PASSWORD
- It’s unclear why there is a slight semantic difference in these banners, but they functionally represent the same weakness. Devices with this banner likely used the default Ubiquiti credentials of ubnt:ubnt.
- HACKED-ROUTER-HELP-SOS-VULN-EDB-39701
- This banner likely refers to this Metasploit module for the arbitrary file upload vulnerability leveraged by the MF worm for initial access to these devices.
- HACKED-ROUTER-HELP-SOS-WEAK-PASSWORD
- This message likely points to easily crackable credentials–those with low entropy and complexity, such as a short string of all lowercase letters, a single word, or short phrase.
Global Presence
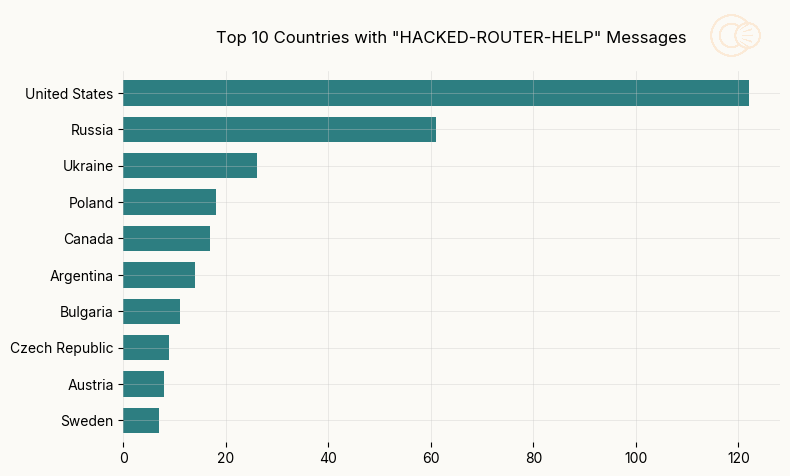
As of this analysis, over a third (122) of the defaced hosts are concentrated in the U.S., with a strong presence across Eastern Europe as well. It’s unsurprising to see the U.S. top the list based on the number of hosts we find in the U.S. generally, but this could speak more broadly to equipment maintenance patterns in these regions.
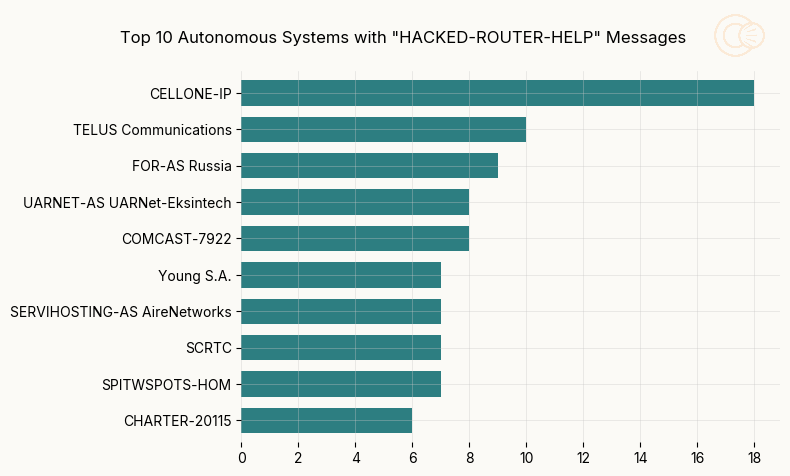
While these instances are littered across various autonomous systems, they’re primarily found on consumer and residential ISP networks. Beyond being the top AS where we observe these hosts, CELLONE-IP (AS1410), associated with provider “CellularOne” in Arizona, U.S., stands out for another reason.
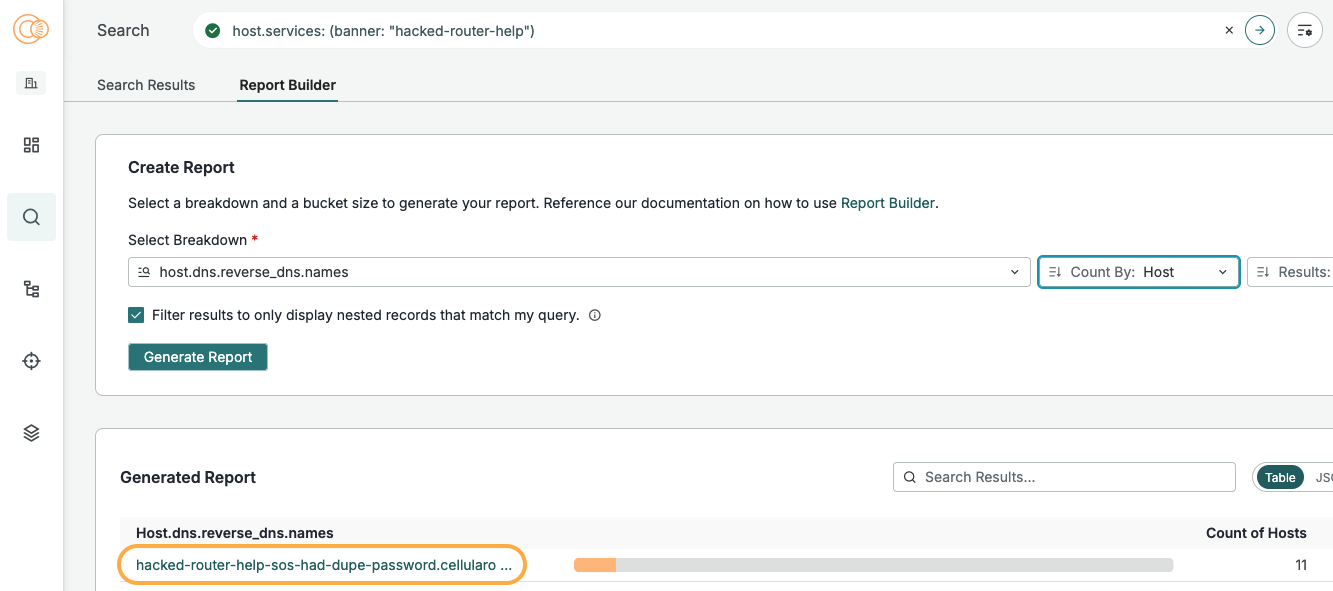
The majority of hosts we examined have unremarkable reverse DNS values in the format of “ip.isp-hostname.tld,” but each of the hosts on CELLONE-IP with a reverse DNS value and a defaced banner have a reverse DNS of “hacked-router-help-sos-had-dupe-password[.]cellularoneonline[.]com.” This is likely a result of the reverse DNS value being set based on the device’s hostname which is somewhat unusual.
Compromise Longevity
To be as thorough as possible, we must at least consider that these banners are newer and not part of the initial campaign in 2016. Copycat attacks aren’t uncommon, and it’s possible someone has defaced these hosts in the years since. However, two findings support the hypothesis that these devices have likely been compromised for an extended period of time.
- Port 10001 hosts the Ubiquiti Device Discovery Protocol which historically ran over UDP and, as its name implies, enables discovery of Ubiquiti devices on a network. This protocol has previously garnered attention for its use in DDoS amplification attacks. Ubiquiti’s documentation notes that TCP support for Device Discovery was added in v1.10.7, which was released in 2018. As of this analysis, none of the Ubiquiti services with the defaced banner are served over TCP, suggesting that these banners could predate the release of TCP support.
- Using Censys historical data to examine uptime of the Ubiquiti service on these hosts, we determined the average uptime was 193 days, while the median was 285 days. This does not mean the banners didn’t change during that time, but it does imply a very long-lived service.
193 days and 285 days are hardly comparable to a decade, though. In this analysis, we used IPv4 addresses as the primary key for these hosts, which introduces another layer of complexity: DHCP churn. DHCP, or dynamic host configuration protocol, is used to assign IP addresses to devices when they join a network.
If the assigned IP address isn’t static–an unchanging IP address associated with a specific device–it can change periodically due to circumstances such as DHCP lease expiration or power loss. As a result, the same physical device may be represented by different IP addresses over time.
One way to broadly account for this is to examine the presence of defaced banners over time. If they are not the result of a new campaign, we’d expect to see a relatively flat or decreasing number of affected hosts over time.
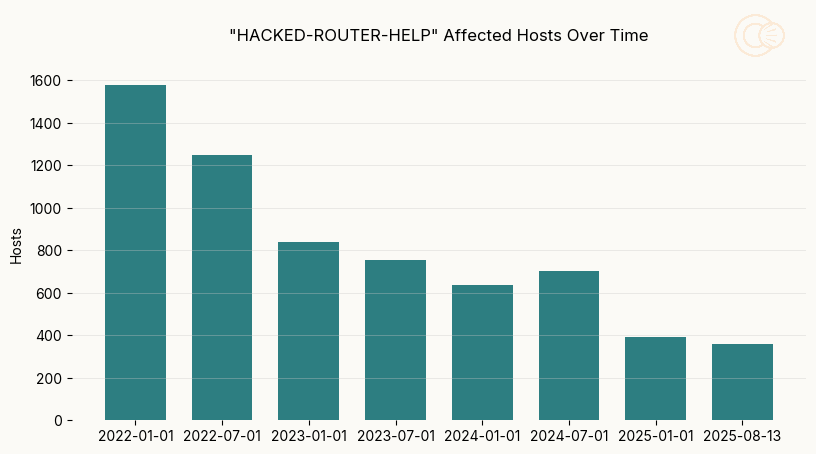
Generally, this is the pattern that emerges and we observe a 75% drop in defaced hosts from January 2022 through August 2025. However, there’s a minor increase in these hosts observed in July 2024. Further investigation reveals that this is largely driven by an increase in hosts in Russia displaying a version of the banner, along with (but not limited to) hosts in several other Eastern European countries. Notably, the U.S. does not contribute to this increase, with a 17% drop in affected hosts from January to July 2024.
It’s unclear what exactly this signifies, but in the following snapshots from January and August 2025, we observe a return to the steady decrease in hosts displaying the defaced banners.
Conclusions
Trawling through Internet scan data for obvious signs of compromised infrastructure is as old as Internet scanning itself, but there are still insights to be gained from this relatively simple technique. We can’t say for certain that all of these devices have been compromised for nearly a decade, but they’ve likely been compromised long enough that ideally, someone responsible for them should have noticed.
Our data shows there has been a substantial drop in devices displaying these banners since 2022, but the fact that several hundred remain hints at the continued challenges of device maintenance and protection.
You can investigate these and other Internet oddities with Censys, the leader in Internet intelligence and insights. Learn more about what makes our data the most accurate, timely source for understanding everything on the Internet.