Note: An updated version of this blog has been published on March 30, 2026.
Executive Summary
- On June 22, 2025, the U.S. Department of Homeland Security (DHS) issued an advisory warning against a “heightened threat environment” in the United States following U.S. airstrikes over Iranian nuclear sites. Further, on June 30, CISA and partners released an alert urging critical infrastructure operators to remain vigilant for targeted activity by Iranian threat actors.
- We studied recent Internet exposure of four device types previously targeted or known to be of interest to Iranian threat actors. Devices we studied include Unitronics Vision PLCs, Orpak SiteOmat, Red Lion equipment, and the Tridium Niagara framework. Apart from Unitronics devices which are slightly more common in Australia, these devices are most commonly observed in the United States.
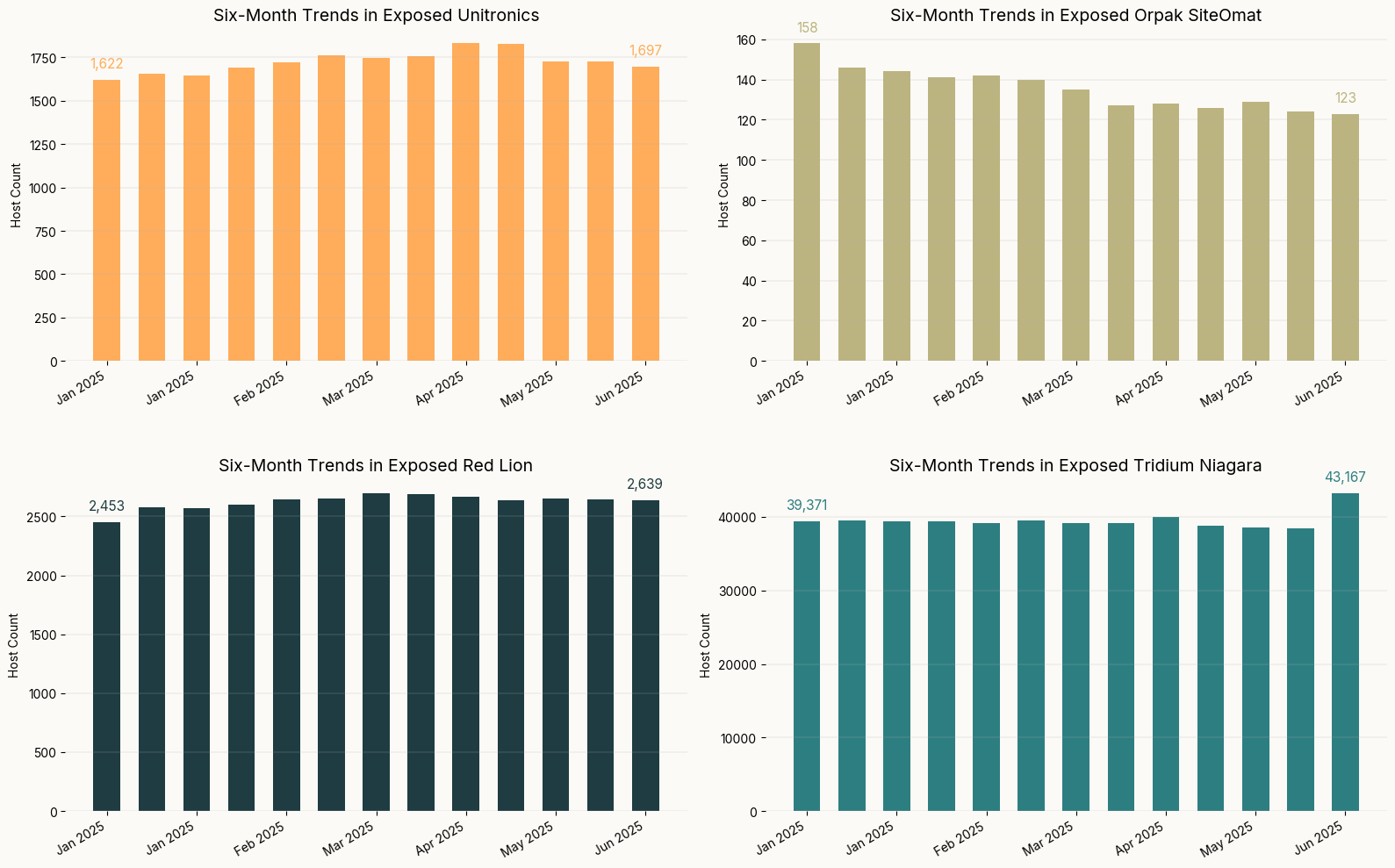
- During the six month timeframe from January to June 2025, we observed increases of 4.5%-9.2% in exposure for all devices studied except Orpak SiteOmat, which decreased by nearly 25%, or about 35 systems. SiteOmat is the least commonly observed system of the devices and software studied.
- At least two of the four systems (Unitronics and Orpak SiteOmat) ship or previously shipped with default credentials. These are easily searchable online and render access to these systems trivial for a threat actor.
- Even if these devices were not known targets of a specific threat actor or nation state in the news, operators should always change default passwords and take measures to remove these interfaces from the Internet.
Introduction
On June 22, 2025, DHS issued an advisory warning against a “heightened threat environment” in the United States following U.S. airstrikes over Iranian nuclear sites. Increased risk of cyber attacks by “pro-Iranian hacktivists” is explicitly mentioned in the advisory and some have speculated that this may include attacks on power and water systems.
On June 30, 2025, CISA and the Federal Bureau of Investigation (FBI), the Department of Defense Cyber Crime Center (DC3), and the National Security Agency (NSA) released an alert warning critical infrastructure operators and other network administrators in the U.S. to remain vigilant for potential targeted activity by Iranian threat actors. Specifically, they mention that Defense Industrial Base organizations who have relationships with Israeli research and defense firms may be at an increased risk.
Devices of Interest
Given these warnings, we wanted to better understand the Internet exposure of systems previously targeted or known to be of interest to Iranian actors. While targets have ranged from IoT and networking equipment to industrial control systems (ICS), we chose to specifically focus on ICS devices given the criticality of many of these systems and increased concern for their safety. Thus, this is not a comprehensive list of known-targeted devices, but a subset:
- Unitronics Vision PLC/HMIs
- Unitronics is an Israel-based manufacturer of PLCs, HMIs, and other tooling often used in industrial environments. Their devices are used across a variety of industries, but those in the water and wastewater (WWS) sector have been commonly targeted by threat actors. Until late 2023, these systems shipped with a default password of “1111”. Unitronics systems use PCOM, a proprietary protocol, for communications between their devices.
- Orpak SiteOmat
- Orpak, now a subsidiary of Gilbarco Veeder-Root, is an Israel-based provider of fuel station automation, fleet management, and other solutions for oil companies and commercial vehicle fleets. SiteOmat is their fuel station automation software, which ships with a default username and password of “Admin/Admin”.
- Red Lion
- Red Lion is a U.S.-based company that specializes in HMIs, meters, and controllers for automated or industrial environments. Their products are used across a variety of sectors, including factory and process automation, WWS, oil & gas, and building automation. Crimson is the configuration software for Red Lion’s controllers, HMIs, and meters, which includes a drag-and-drop interface for easier programming.
- Tridium Niagara
- Tridium is a U.S.-based company whose Niagara framework is used to integrate various building automation and control tools into a single interface. This tooling allows building administrators to control lighting, HVAC, and security systems locally or remotely. Tridium systems use FOX, a proprietary protocol, for communications between Niagara devices.
We studied the Internet presence of these devices at biweekly intervals from January through June 2025. We note that all data referenced in this report reflects device exposure numbers, not vulnerable device numbers. However, exposing systems connected to critical infrastructure directly to the Internet is risky and should be avoided.
| Device Type | January 2025 Total | June 2025 Total | Delta |
| Unitronics | 1,622 | 1,697 | +4.5% |
| Orpak SiteOmat | 158 | 123 | -24.9% |
| Red Lion | 2,453 | 2,639 | +7.3% |
| Tridium Niagara | 39,371 | 43,167 | +9.2% |
Services on the Internet are often ephemeral by nature, and some fluctuation of exposure over time is not unusual. Unitronics and Red Lion devices each saw exposure increases of less than 10% from January through June 2025.
Tridium Niagara, the device type with highest exposure counts overall, increased 9.2% from January through June. Most of the increased exposures appear to be in Germany, Sweden, and Japan.
Orpak SiteOmat is the only system we studied that decreased in exposure during the study timeframe, and somewhat dramatically, if we consider the percentage drop of nearly 25%. However, there were relatively few of these systems online in January (158), making the drop to 123 in June. Chile, Turkey, and the U.S. saw the largest decreases, but that’s also where the majority of these systems are observed, even today.
We explore these exposures further in the sections below.
Unitronics
Unitronics HMIs were the target of a November 2023 campaign claimed by the CyberAv3ngers, an Iranian hacktivist group with ties to the Iranian Revolutionary Guard Corps (IRGC). According to CISA’s advisory, “The threat actors compromised Unitronics Vision Series PLCs with human machine interfaces (HMI). These compromised devices were publicly exposed to the internet with default passwords and by default are on TCP port 20256.”
Multiple changes were made to disrupt operations, prevent operators from connecting to affected systems, and an anti-Israel defacement message was left on system splash pages.
Unitronics Exposure by Country
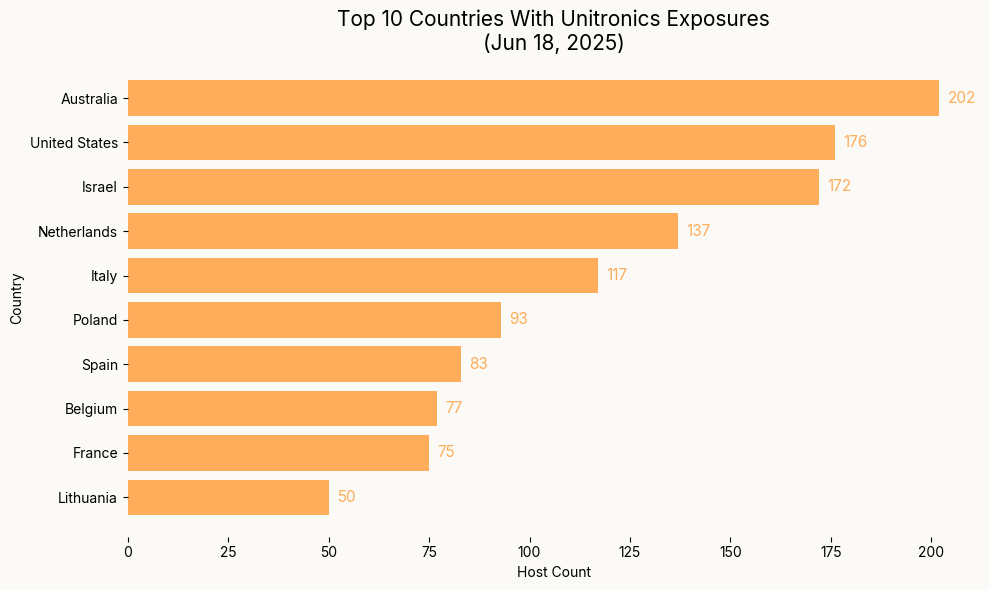
Unlike the other devices we’ll examine, Australia hosts the highest number of Unitronics devices, followed somewhat closely by the U.S. and Israel. We also observe Unitronics devices across multiple countries in Europe.
Unitronics Exposure by Network
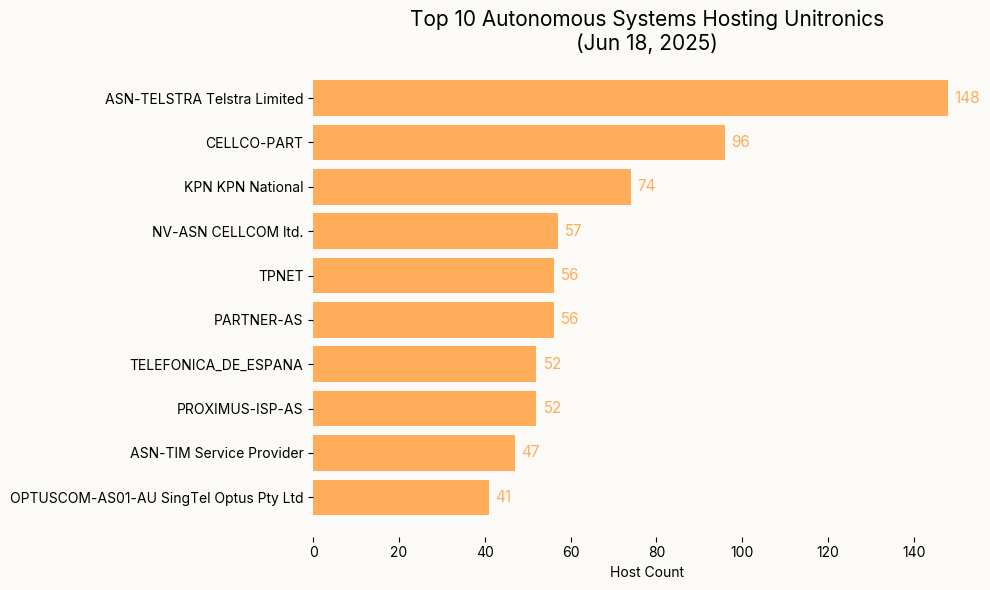
Given the Unitronics footprint in Australia, it is not surprising to see an Australian telco (ASN-TELSTRA) top the list of networks where we most commonly observe Unitronics. CELLCO-PART, the second-most common network where we observe Unitronics, is an AS owned by Verizon in the U.S. We have observed large numbers of ICS devices and systems on CELLCO-PART in previous research.
Orpak SiteOmat
In October 2023, the CyberAv3ngers claimed to have attacked multiple Orpak SiteOmat web interfaces, likely gaining access by leveraging the software’s default credentials.
# Exploit Title: SiteOmat Fueling System - Default Password
# Date: 2024-03-15
# Exploit Author: Parsa rezaie khiabanloo
# Vendor Homepage: https://www.orpak.com/
# Tested on: Windows,Linux
# Google Dork : intitle:"SiteOmat Loader"
# Shodan Dork : Server: Orpak
# Attacker with this google dork can find the login panel
and put the default username and password.
Username : Admin
password : Admin
(https://cxsecurity.com/issue/WLB-2024030031)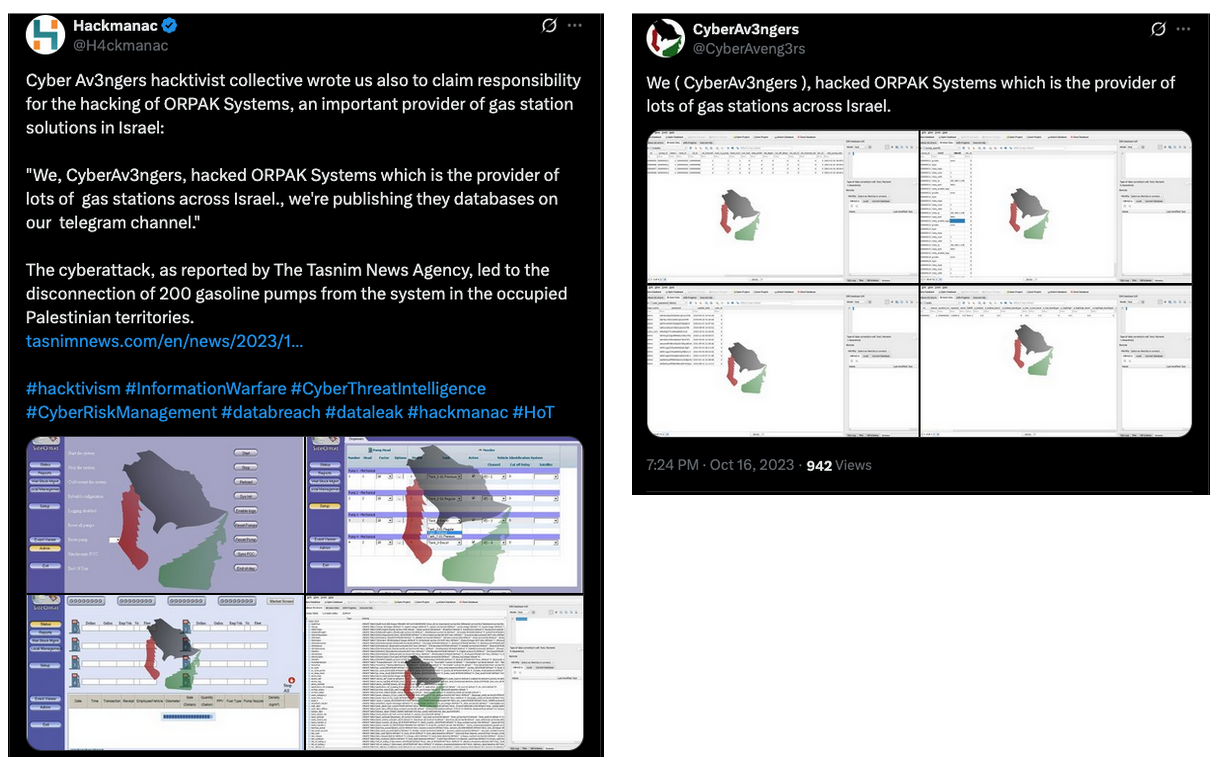
Orpak SiteOmat Exposure by Country
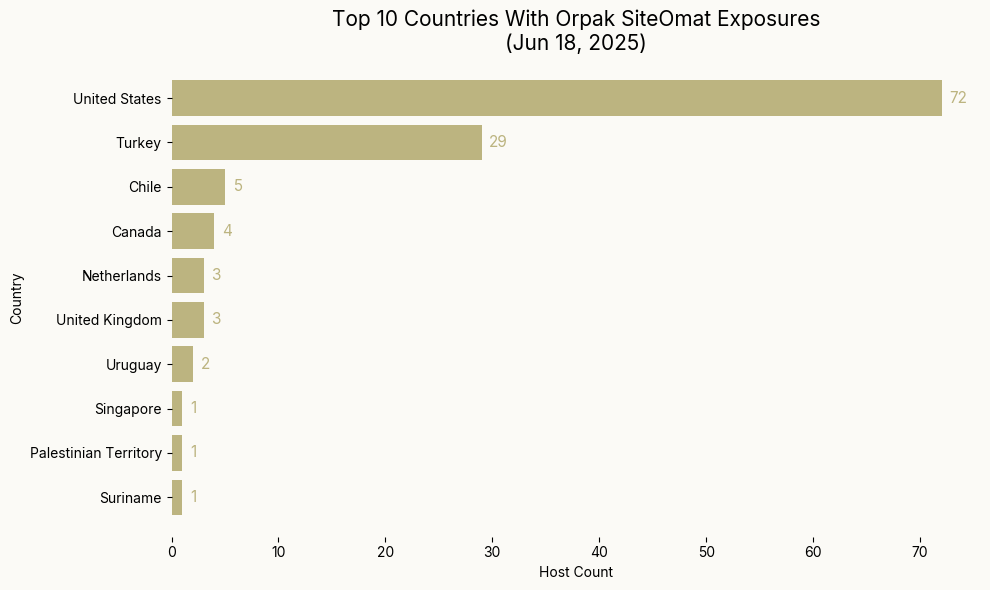
As of June 2025, the U.S. hosts more than double of any other country’s SiteOmat instances, but it’s also somewhat commonly observed in Turkey. Chile, Canada, the Netherlands, and other locations worldwide.
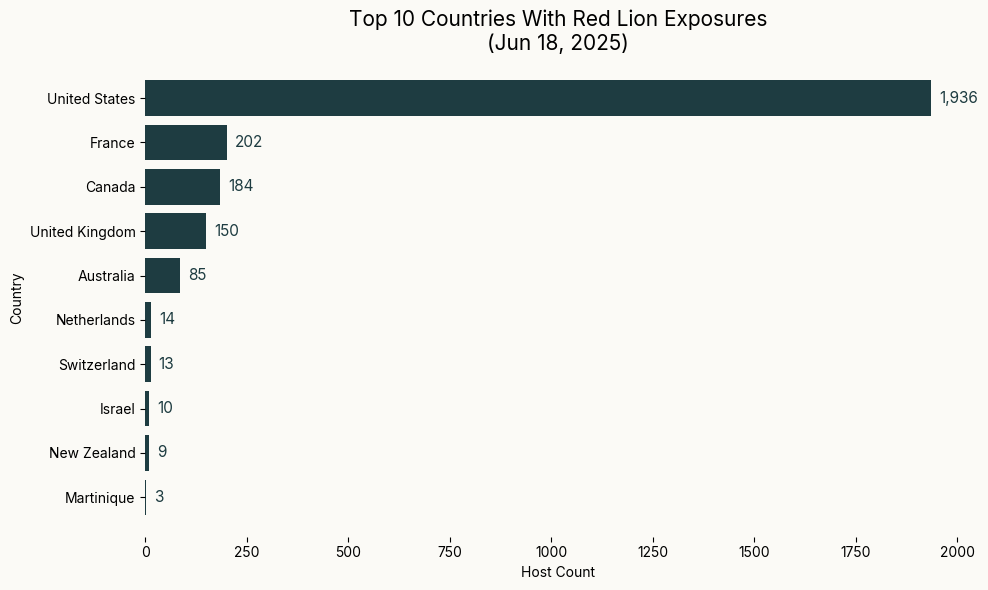
Orpak SiteOmat Exposure by Network
The U.S. hosts the majority of Orpak SiteOmat interfaces, but the network with the highest concentration of these systems is Turkish mobile network TURKCELL-AS. Rather than U.S. instances being concentrated on one network, they are spread across networks like ATT-INTERNET4, COMCAST-7922, and others in the long tail of networks where SiteOmat is observed. Note that the graph above reflects the top 10 networks where we observe SiteOmat, but we see SiteOmat on over 60 distinct ASes on June 18, 2025.
Red Lion
In 2024, Claroty published research on IOCONTROL, malware designed for targeting IoT and ICS devices. IOCONTROL is believed to have been leveraged by Iran-affiliated actors to target industrial routers, firewalls, IP cameras, and more. Red Lion is among the list of vendors reportedly affected by this malware.
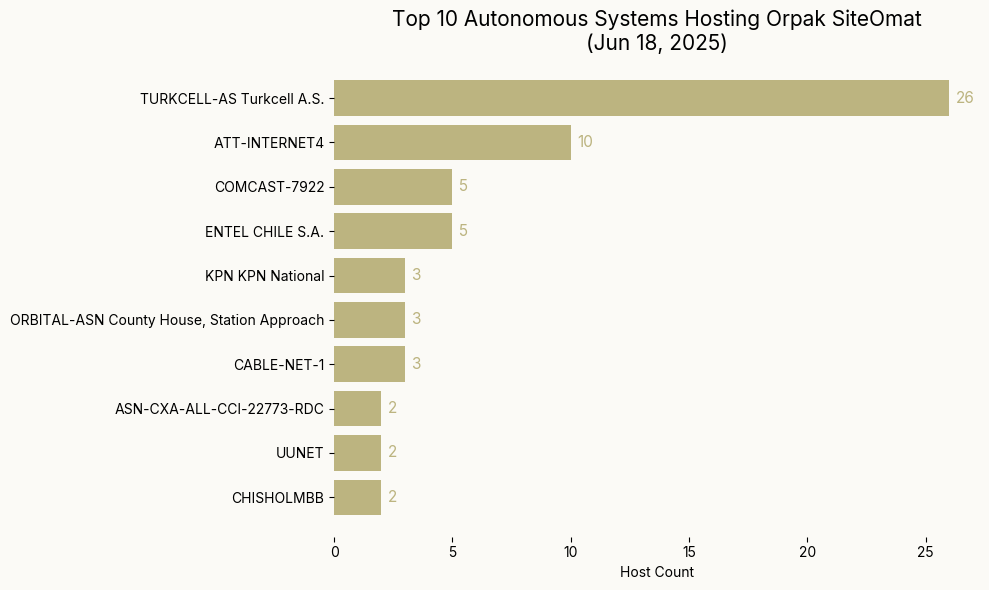
Red Lion Exposure by Country
Red Lion systems have a heavy footprint in the U.S., with 73% of all Red Lion systems observed there. Beyond the U.S., France, Canada, the U.K., and Australia also host multiple instances of Red Lion that are exposed to the Internet.
Red Lion Exposure by Network
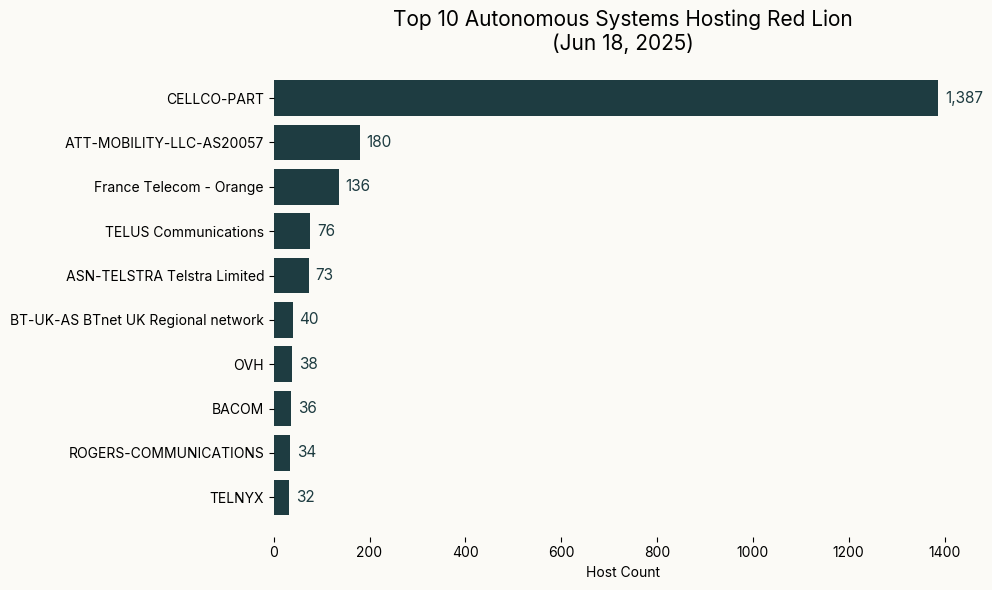
Given Red Lion’s prevalence in the U.S., the heavy representation on CELLCO-PART is unsurprising. France Telecom, TELUS, and ASN-TELSTRA are also represented, which corresponds to Red Lion’s presence in France, Canada, and Australia.
Tridium Niagara
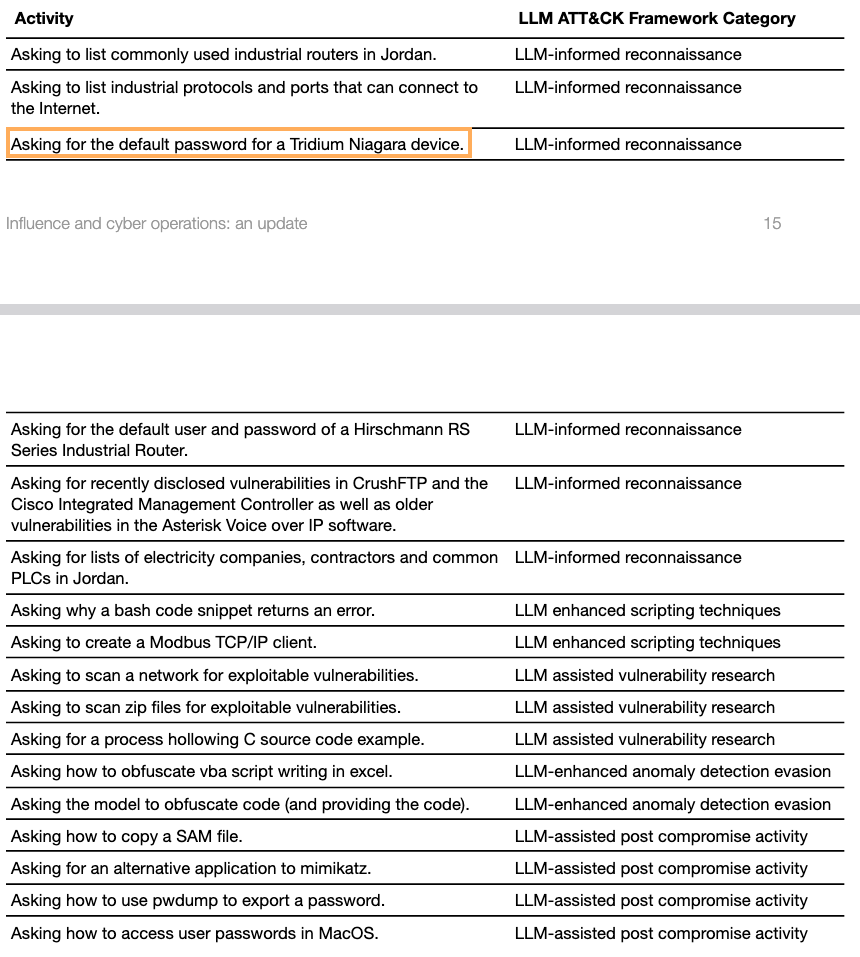
While the devices above are known and reported to have been targeted by Iranian actors, we are currently unaware of any Iranian attacks against Tridium Niagara. However, these systems do appear to have at least been a fleeting interest of one Iranian threat actor.
In October 2024, OpenAI released an updated report on influence and cyber operations across their platform. In the report, they address activity attributed to the CyberAv3ngers, who appear to have used OpenAI models to conduct research on ICS devices. This reconnaissance includes inquiring about common industrial routers, PLCs, and electric companies in particular regions, as well as default passwords for various devices, including Tridium Niagara devices.
Tridium Niagara Exposure by Country
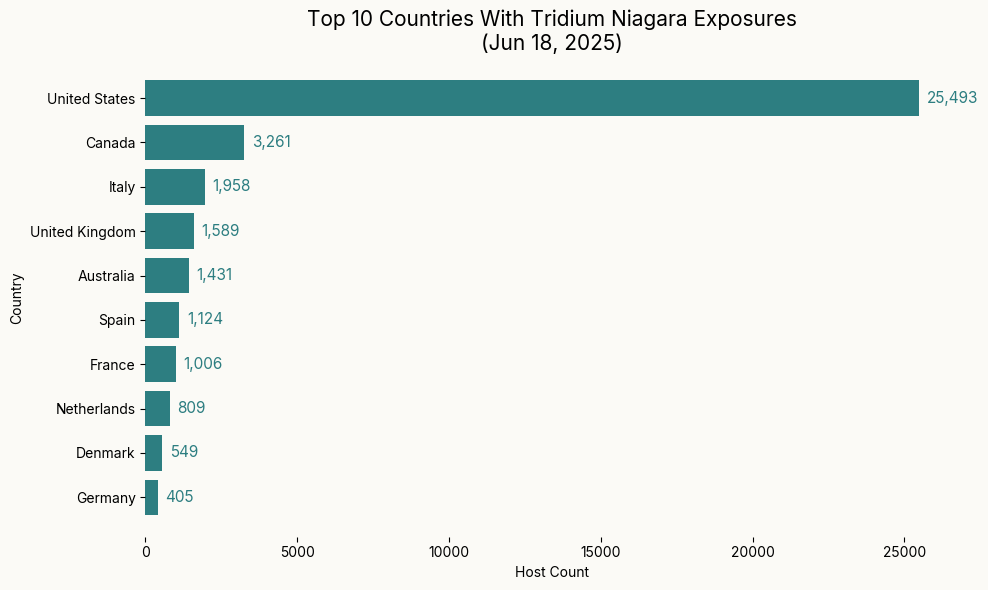
Tridium Niagara is by far most commonly observed in the U.S., with strong representation in Canada and Europe as well.
Tridium Niagara Exposure by Network
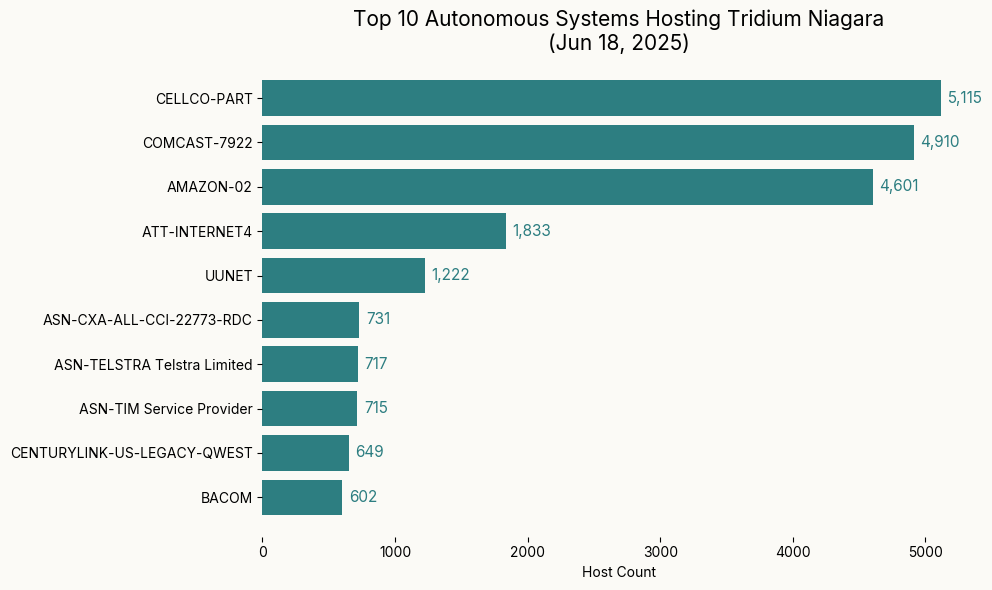
Given Tridium Niagara’s heavy presence in the U.S., it’s unsurprising that over 10,000 of these systems are on CELLCO-PART or COMCAST-7922, both of which commonly host industrial devices. Interestingly, AMAZON-02 is the third-most common AS where Tridium is observed. Typically, we do not observe large numbers of industrial infrastructure in cloud providers.
Conclusions
- Apart from Unitronics, which is most commonly observed in Australia, the highest numbers of these devices are observed in the U.S. Our previous research has found that the U.S. has the highest numbers of exposed ICS devices in general, which is further supported by these recent trends.
- Though Tridium Niagara boasts the highest exposure numbers, it’s building automation software. Depending on a threat actor’s objective, these systems, though plentiful, may not be the most valuable targets.
- As we’ve observed in previous research, most of these systems appear on mobile or consumer ISPs, not in cloud networks.
- Use of default passwords continues to provide threat actors with simple ways to access critical systems. Manufacturers should avoid shipping devices or software with default credentials, and instead require strong, unique passwords and provide guidance to help operators avoid exposing these systems directly to the Internet.