Executive Summary
DDoSia (DDoSia project) is a participatory distributed denial of service (DDoS) capability created by Russian hacktivists in 2022, early in the Russo-Ukrainian war. DDoSia is designed for volunteers to contribute network resources towards conducting denial of service attacks. Operated by the pro-Russian hacktivist group NoName057(16), attacks have focused heavily on Ukraine and other NATO targets.
Censys has actively monitored DDoSia since mid 2025, following reconstitution after disruption by law enforcement. During this time, we have observed an average of 6 control servers active at any given time; however, servers typically have a relatively short lifespan — averaging 2.53 days. Some servers we have observed are active for over a week, but most instances we only see for less than a few hours.
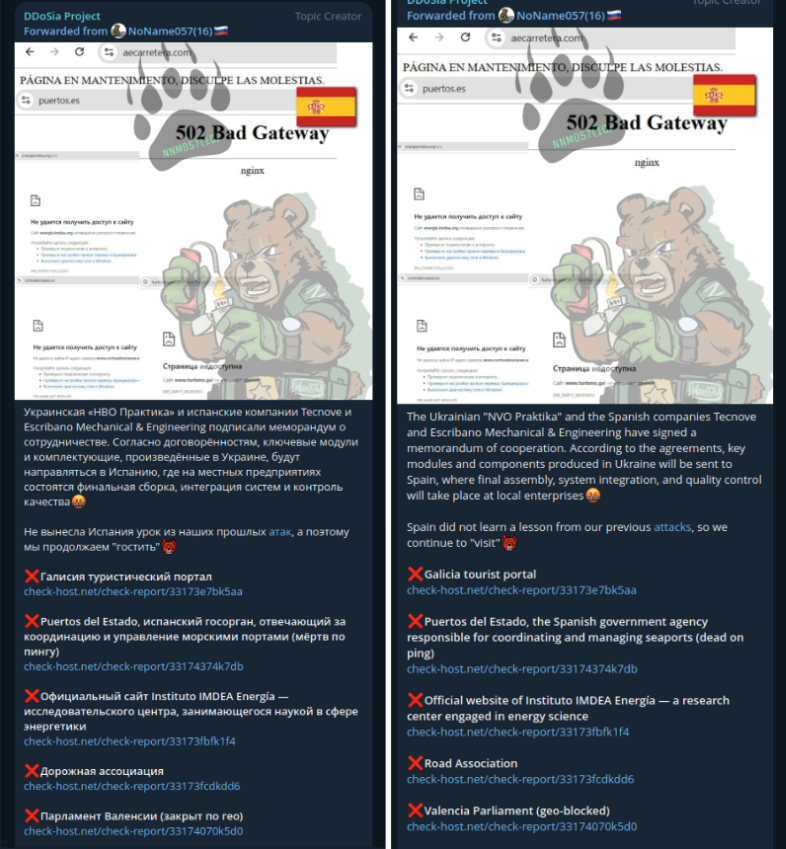
Targeting of DDoSia is heavily focused on Ukraine, European allies, and NATO states in government, military, transportation, public utilities, financial, and tourism sectors.
Introduction
First released in March 2022 on Telegram, DDoSia is a distributed denial of service (DDoS) tool operated by the pro Russian hacktivist group NoName057(16). DDoSia is deployed by volunteers and tasked through a central infrastructure; it follows a similar design to other participatory DDoS tools, such as versions of Low Orbit Ion Cannon (LOIC) with HiveMind mode or DDoS tooling distributed by CyberBerkut in 2015.
A key component of any participatory DDoS system is a mechanism for distributing attack tools and instructions to supporters; for this, NoName057(16) relies heavily on Telegram — having built a following of over 45k prior to law enforcement disruption in July 2025. DDoS capabilities built on traditional malware — such as Mirai — often rely upon self-propagation to reach a volume of infected systems capable of generating a sufficient traffic volume to impact a remote target. Instead, DDoSia relies upon volunteers running DDoSia, presumably on a variety of systems ranging from personal equipment to rented servers and compromised hosts.
Volunteers do not have the ability to select attack targets; however, NoName057(16) motivates supporters to contribute by offering financial rewards for top contributors and, in pro-Russia ideology, by maintaining an active social media campaign highlighting their anti-Ukrane, anti-NATO views.
Technical Characteristics
DDoSia is distributed as a compiled Golang binary through the DDoSia Project Telegram group and available for most modern operating systems and architectures. Open source research has also identified links to the Bobik malware from 2020 that may have been a predecessor to DDoSia.
Based on the banner printed when run, the authors likely refer to this tool as “Go-Stresser”. Early versions of DDoSia were historically hosted on Github and included a version written in Python. A list of available binaries from the Telegram chat in December 2025 is included in the Appendix.
Previous reporting from Sekoia from June 2023 presented an outstanding overview of how volunteers deploy DDoSia and the communication flow between infected systems and control infrastructure.
Operational Context
In July 2025, Europol and Eurojust launched a joint international operation known as Eastwood that sought to dismantle DDoSia and the capability established by NoName057(16). The reported results of this operation include and are summarized in the information card following:
- 2 arrests / 7 arrest warrants issued
- 24 house searches
- 13 individual questions
- +1000 supporters notified of legal liability
- +100 servers disrupted worldwide.

A key data point from this card is the +1000 supporters notified for their legal liability, because it provides one of the few estimates of how many active volunteers are running DDoSia bots. While the total number of active bots is highly volatile due to the nature of DDoS attacks, we can estimate at low-confidence the total number of DDoS bots controlled by DDoSia is under 10k. This estimate is based on each active supporter running at least one bot, with a potential subset running multiple (but under 10) bots.
Despite law enforcement action, DDoSia was able to reestablish itself within several days and resumed launching DDoS attacks. Critically, this disruption significantly interrupted communication between operators and volunteers. After losing their main telegram group with 45k subscribers, the reformed group has since reached 14k as of December 2025. The following section summarizes Censys visibility into infrastructure and prevalence trends associated with DDoSia, following this disruption.
Censys Perspective
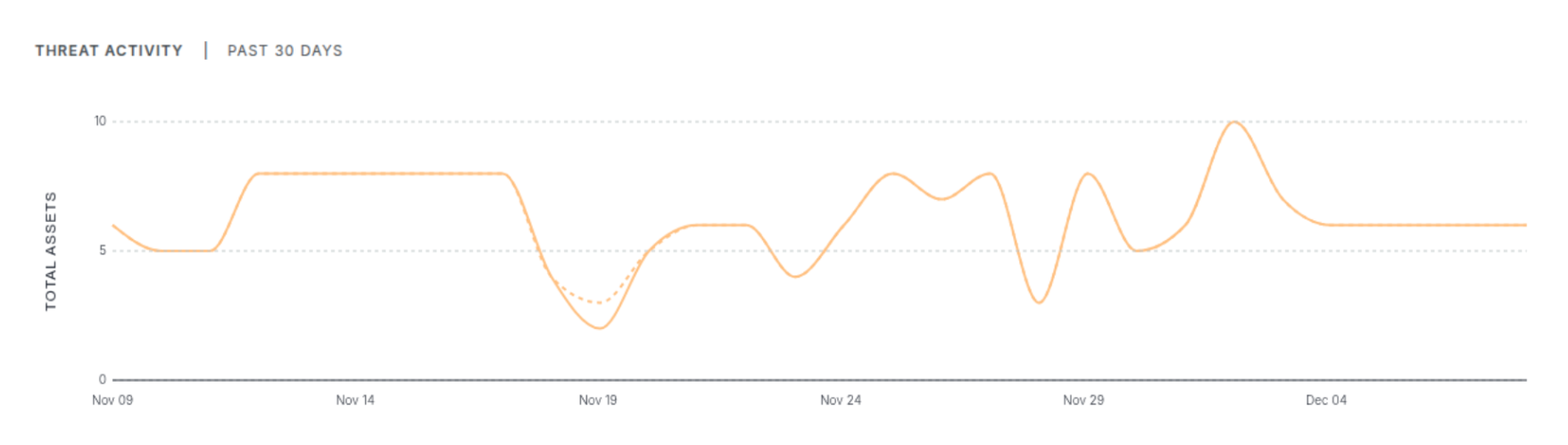
Censys has actively tracked DDoSia in our Threat Hunting Module since June 2025. Since we started tracking control infrastructure of DDoSia, we have observed a rapidly changing infrastructure with hosts often staying online for less than a day. The following screenshot shows the number of systems online for DDoSia for November 2025.
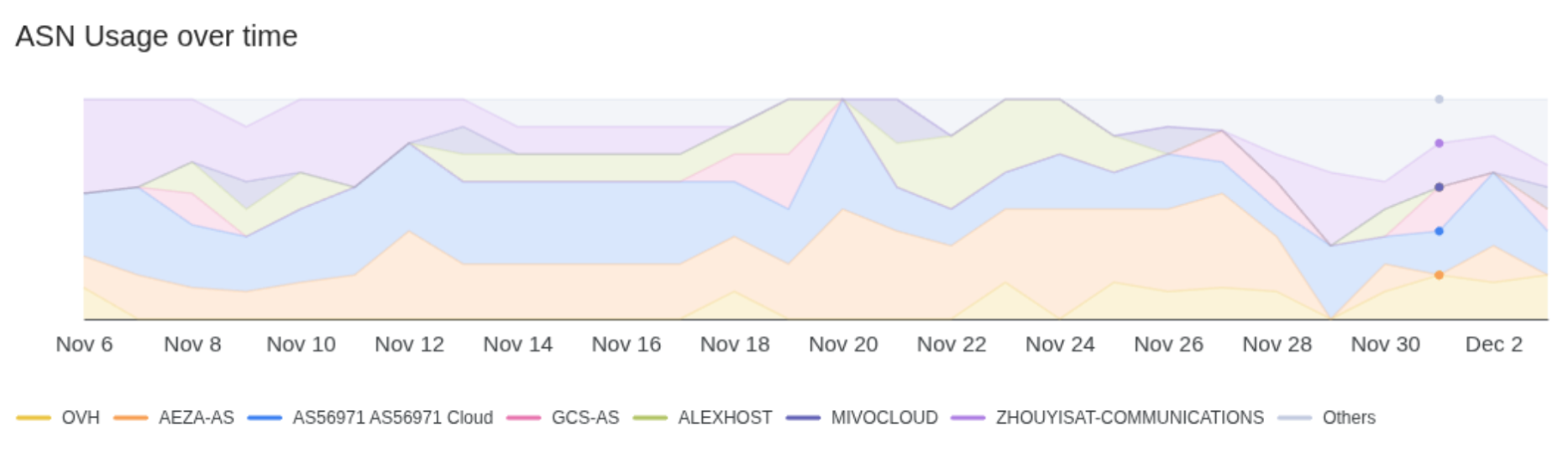
Identified control infrastructure is consistently hosted on Virtual Private Servers (VPS) – typically at Azea, which was sanctioned by the US Treasury Department in 2025, and AS56971 (HostVDS). The following chart shows ASN networks DDoSia infrastructure has been observed throughout November 2025.
When looking at the rate at which DDoSia infrastructure changes, we found the mean lifespan of each control server in November was 2.5 days. This was unexpectedly high, given just over half of the identified instances were active for less than 24 hours; however, 10% were online for 10-15 days.
Systems operated by DDoSia typically have minimal public service exposure — often, only exposing 22/TCP for SSH and 80/TCP for HTTP check-ins. This minimal footprint often leaves limited artifacts for researchers to fingerprint.
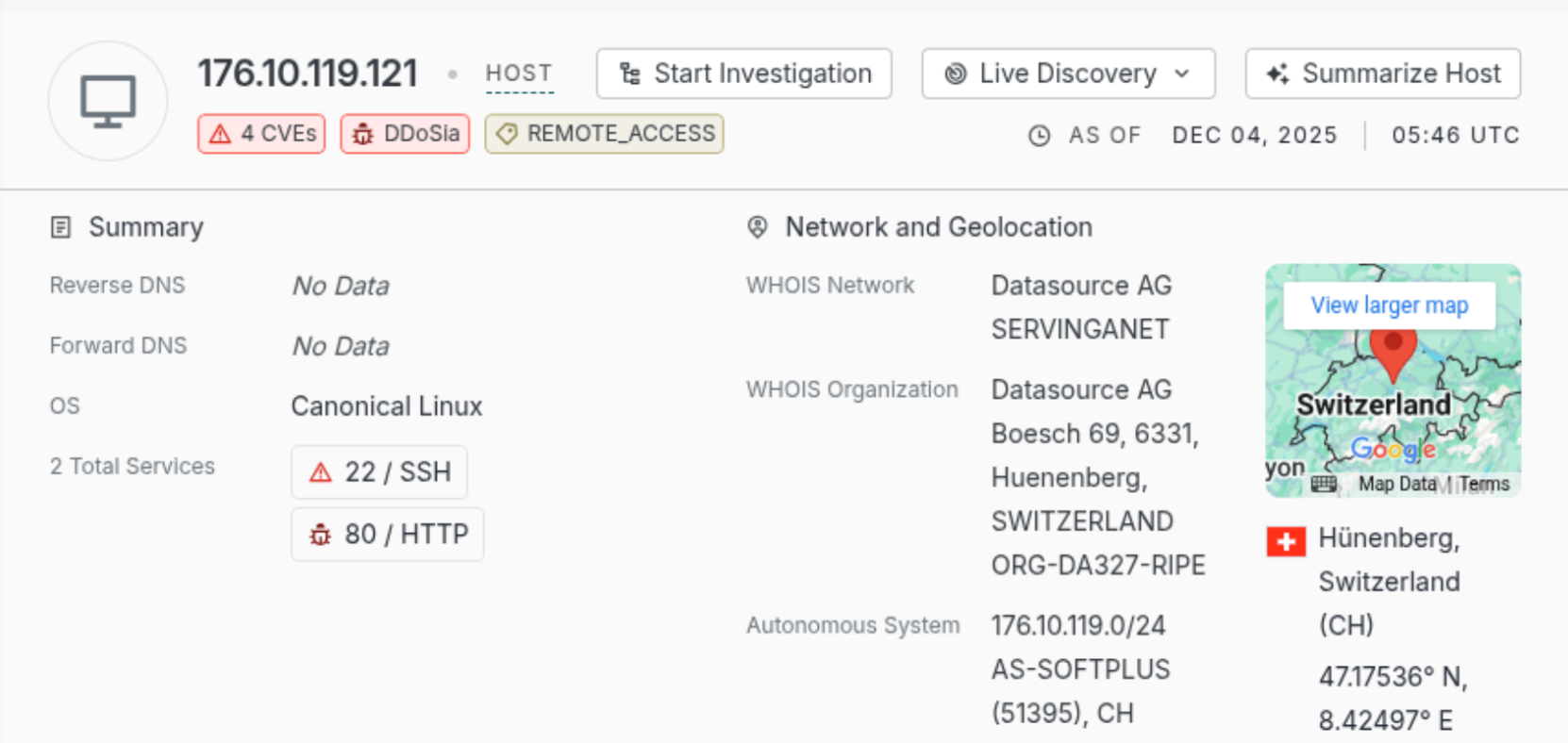
Based on the services and content exposed, it is likely operators are hosting DDoSia on dedicated virtual servers and not on compromised infrastructure.
In a 2023 blog post, Gen was one of the first to publicly identify that DDoSia control servers consistently returned matching target information and publicly present initial findings that DDoSia was operating a multi-layed control infrastructure. From our scanning and existing open-source intelligence reporting, we suspect DDoSia’s is operating a multi-layered control infrastructure, that may follow the following structure:
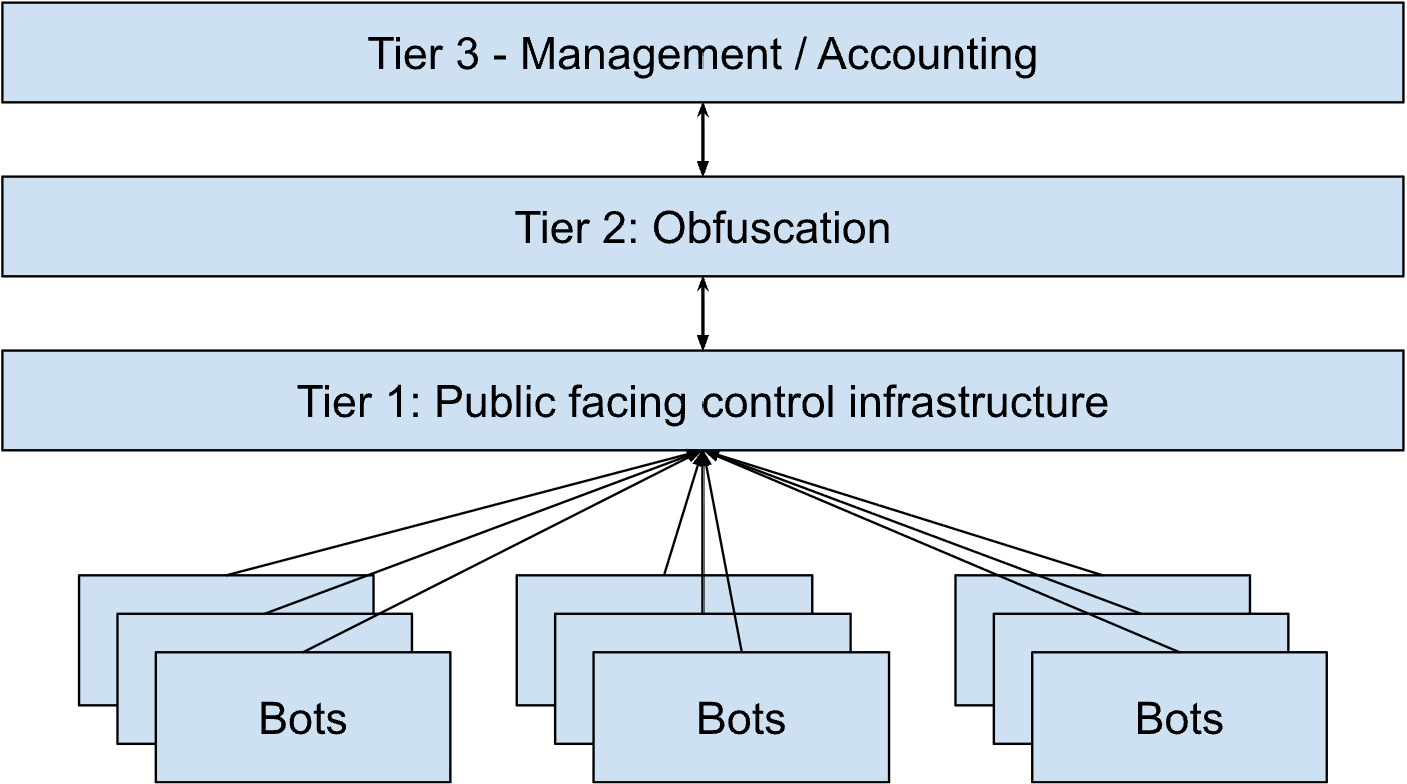
Within this structure, systems running DDoSia likely only communicate with a subset of systems we will refer to as Tier 1. IP addresses of these systems are provided by the DDoSia projects Telegram bots to members operating attacking systems.
The second layer of this we suspect is for obfuscating traffic between systems interacting with bots and core management infrastructure. These systems are short lived (under 24 hours), respond to check in requests, and may be running simple proxy tools to relay traffic from Tier 1.
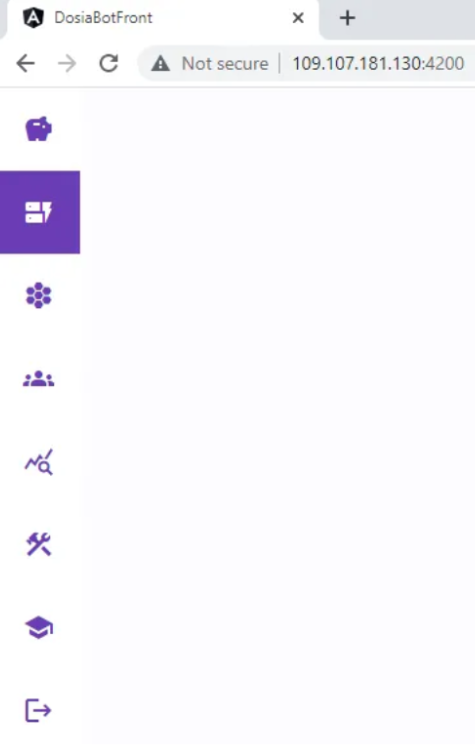
The final layer of this architecture is likely for core management and accounting systems. Further evidence for this was presented by Team Cymru in 2023, in which they identified netflow links to several systems suspected of acting as database, metric tracking, and service queues for control infrastructure. Around the same time as Team Cymru’s post, Gen also published additional information that included a suspected (partial) screenshot of NoName(057)16’s web control panel for DDoSia – shown below:
This type of multi-layer infrastructure is typical for mature botnet operators as it provides both redundancy and technical separation between bots and operators.
Conclusion
DDoSia’s ability to conduct DDoS attacks is an active threat to Ukraine and supporting countries and organizations. Since 2022, it has been used almost continuously for conducting DDoS attacks against Ukraine, European allies and NATO states. These attacks have heavily sought to push back against those supporting Ukraine and included efforts to disrupt transportation of aid and tourism. For defenders, DDoS mitigation tools and services are critical for limiting the impact of DDoSia attacks.
Appendix
Identified Control Servers
A list of observed control servers based on Censys scanning and publicly available botnet logs is available at this GitHub Gist link.
DDoSia Clients
| SHA256 Hash | File Name |
| 8ba11c9e3d3f38a2473620579f61119be9ada9bc0e4dc37fc045017f56248473 | d_freebsd_arm |
| 0e19deac3d64a33495d237ed4cdb3581813b88b6ed2afe84b8c2908201feaf91 | d_freebsd_x32 |
| 95375dac86bf8daf101cb8120d78f0340e6b1cdbea16b859d96d7aef946be983 | d_freebsd_x64 |
| e3f229dc71ce65c1f2de05e2cfbd7ae848d330661d9b9b3fa00d594bf84f4d93 | d_lin_arm |
| 48e9d5b0f8a2d56d31b4e845597789a81e3733c03751139a22f55ceebd15b75a | d_lin_arm_wr |
| 307e3ea1cb140f375443ef3c9b62028dd5c6449c1bf242b83d6db5d730bd2121 | d_lin_x32 |
| 2aaf3c08da86d5d0f6f9c00d4011991fd2cd50fa0777d51d5552b98365b15774 | d_lin_x64 |
| 7ee3574b0693e78060d863a5794437960aec0614af6c1909dd075daec0bcaf92 | d_mac_arm64 |
| 87cd40fbf9f363c212a8402cc8350f624fd6760799c013a0cdd301707a5bd083 | d_mac_x64 |
| 0eae66824c65efe6b69937bf8427b7f28df591f2788b8088fbe9a05e8c26e077 | d_win_arm64.exe |
| b81734717f36d3cea59e5690b984333c5a6908a15883a0463d77cb20dadcec0c | d_win_x32.exe |
| 532edcad0f1637b4cb6fe2638c84c9cee2a52786b89f8d155c910bf60f43da9c | d_win_x64.exe |






