Vulnerability Description
F5 Networks disclosed a major supply-chain breach in which a suspected nation-state threat actor gained persistent access to internal engineering and development environments.
The intrusion resulted in the theft of BIG-IP source code, internal vulnerability research, and limited customer configuration data. While F5 reports no impact to core operations or software integrity, the potential exposure of undisclosed vulnerabilities poses elevated risk to all BIG-IP customers.
Within hours of disclosure, CISA issued Emergency Directive ED-26-01, ordering federal agencies to mitigate or disconnect affected F5 devices due to potential downstream compromise. The directive instructs agencies to prioritize updates for F5OS, BIG‑IP TMOS, BIG‑IQ, and BNK/CNF.
F5 has released updated software to address CVEs in several of its products in response. While F5 has stated that there is no current evidence of undisclosed critical or remote code execution vulnerabilities being leveraged in attacks, customers are strongly encouraged to install these updates as a precaution.
| Field | Description |
| Vendor | F5 Networks |
| Products Affected | BIG-IP product family (including TMUI, iControl REST, APM, API, and management interfaces)Note that NGINX, Distributed Cloud, and Silverline are not affected. |
| Date of Disclosure | October 15, 2025 |
| Threat Actor | Suspected nation-state group (undisclosed attribution) |
| Incident Type | Supply-chain intrusion / source-code and vulnerability data exfiltration |
| Impact | Exposure of BIG-IP source code and internal flaw data; potential for future zero-day exploitation; limited customer configuration leakage |
| Initial Access | Compromise of internal development and knowledge-management systems (exact vector under investigation) first detected on August 9, 2025 |
| Exploitation Status | No confirmed customer exploitation as of publication, but CISA warns of high likelihood of weaponization |
Censys Perspective
Censys has identified 681,308 internet-facing F5 BIG-IP devices across the globe, including load balancers, application gateways, and management interfaces. While we cannot confirm which instances are vulnerable, this scan data provides a clear picture of the widespread global exposure of F5 BIG-IP infrastructure.
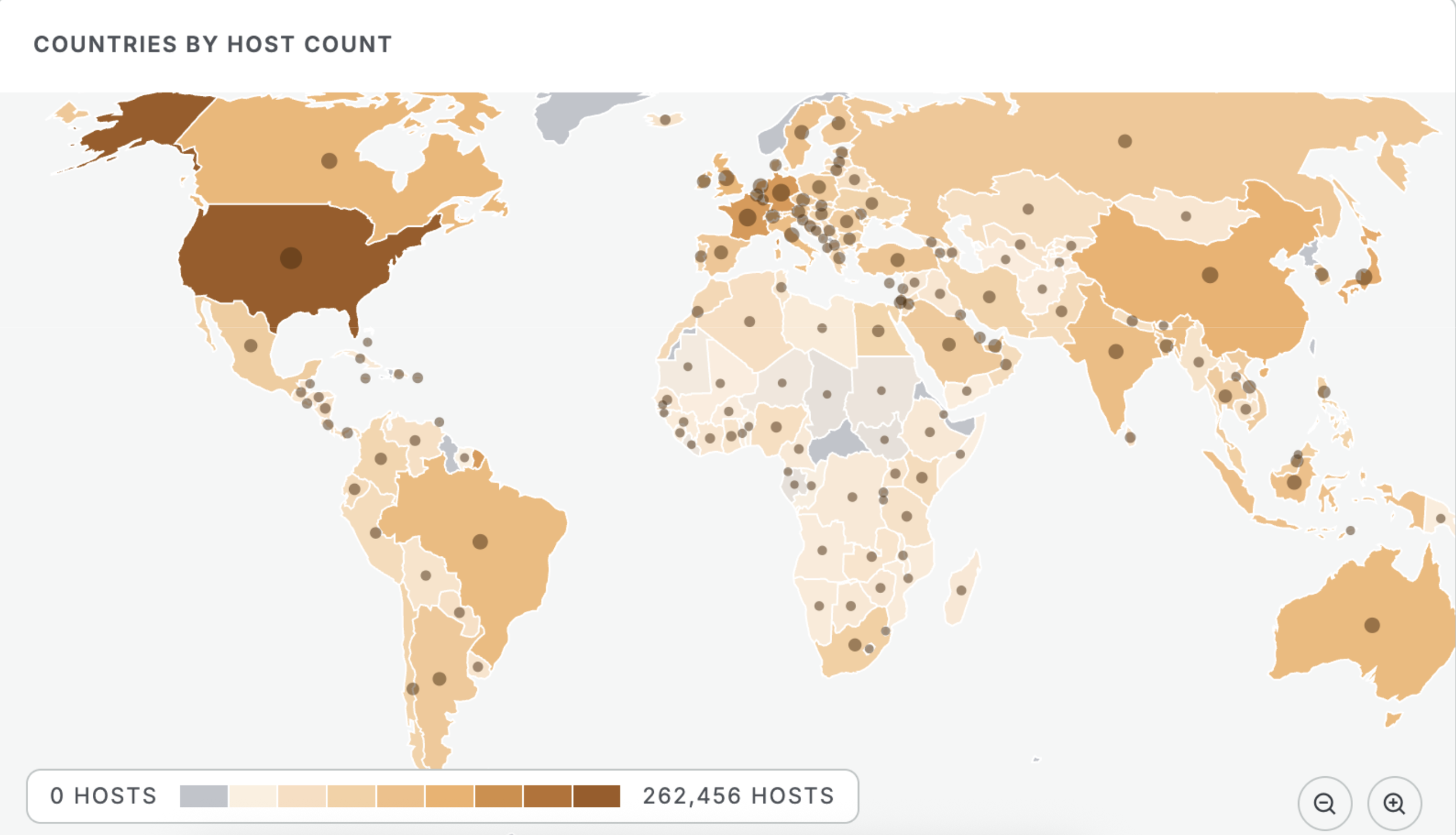
See the full breakdown by country in Censys Platform –>
Over 90% of the observed systems appear to be running BIG-IP Local Traffic Manager (LTM) or Access Policy Manager (APM). A smaller portion includes Application Security Manager (ASM), Advanced WAF, and the BIG-IP Configuration Utility.
BIG-IP Configuration Utility is the web-based admin interface used to manage and configure BIG-IP systems, including access to TMUI and other core components. The other products—LTM, APM, ASM, and Advanced WAF—are functional modules that provide traffic management, access control, and security features but are not admin interfaces themselves.
Although details about the exposed vulnerabilities remain limited, F5 reports no evidence that the stolen information has been used in active attacks or that any private data has been publicly disclosed. The company is continuing its investigation and will notify customers whose configuration or implementation data may have been accessed.
Still as a precautionary measure, it’s recommended that defenders inventory all F5 / BIG-IP assets (hardware, virtual, and cloud) and restrict management interfaces (TMUI, iControl REST, APM, API) from untrusted networks.
The queries below can help identify F5 BIG-IP instances, but they cannot determine if systems are vulnerable. Organizations must verify patch status independently.
host.services.software: (vendor: “f5″ and (product:”big-ip” or product=”ip_configuration_utility” )) and not host.services.labels.value = “HONEYPOT” and not host.services.representative_info: *
services.software: (vendor:”f5″ and (product:”big-ip” or product=”IP Configuration Utility”)) and not labels:{`honeypot`, `tarpit`}
host.services.software: (vendor:”f5″ and (product:”big-ip” or product=”IP Configuration Utility”)) and not host.labels:{`honeypot`, `tarpit`}
References
- https://my.f5.com/manage/s/article/K000156572
- https://www.bleepingcomputer.com/news/security/hackers-breach-f5-to-steal-undisclosed-big-ip-flaws-source-code/
- https://www.cisa.gov/news-events/directives/ed-26-01-mitigate-vulnerabilities-f5-devices
- https://techcrunch.com/2025/10/15/cyber-giant-f5-networks-says-government-hackers-had-long-term-access-to-its-systems-stole-code-and-customer-data/




