Vulnerability Description
CVE-2026-0300 is an unauthenticated buffer overflow in the User-ID Authentication Portal (Captive Portal) service of PAN-OS. The vendor advisory states that exploitation yields arbitrary code execution with root privileges on PA-Series and VM-Series firewalls, and that risk is “greatly reduced” when access to the Authentication Portal is restricted to trusted internal IP addresses. Vendor-rated exploit maturity is “ATTACKED” with limited in-the-wild exploitation reported, primarily against Authentication Portals exposed to untrusted IP addresses or the public Internet. In observed campaigns, attackers have pivoted from the compromised firewall into the customer’s directory infrastructure, using firewall-extracted credentials to enumerate Active Directory.
| Field | Description |
| CVE-ID | CVE-2026-4670 — CVSS v3 9.3 (critical) — assigned by Palo Alto Networks |
| Vulnerability Description | CVE-2026-0300 is an unauthenticated buffer overflow in the User-ID Authentication Portal (Captive Portal) service of PAN-OS. The vendor advisory states that exploitation yields arbitrary code execution with root privileges on PA-Series and VM-Series firewalls, and that risk is “greatly reduced” when access to the Authentication Portal is restricted to trusted internal IP addresses. |
| Date of Disclosure | May 6, 2026 |
| Affected Assets | Palo Alto PA-Series and VM-Series firewalls running affected versions of PAN-OS (see below). Note that Prisma Access, Cloud NGFW, and Panorama appliances are not impacted by this vulnerability. Exploitation requires the User-ID Authentication Portal feature to be enabled. Devices running affected versions with the Authentication Portal disabled are not exploitable but should still be updated. |
| Vulnerable Software Versions | Palo Alto PA-Series and VM-Series firewalls running the following versions of PAN-OS: PAN-OS 12.1: < 12.1.4-h5 < 12.1.7 PAN-OS 11.2: < 11.2.4-h17 < 11.2.7-h13 < 11.2.10-h6 < 11.2.12 PAN-OS 11.1: < 11.1.4-h33 < 11.1.6-h32 < 11.1.7-h6 < 11.1.10-h25 < 11.1.13-h5 < 11.1.15 PAN-OS 10.2: < 10.2.7-h34 < 10.2.10-h36 < 10.2.13-h21 < 10.2.16-h7 < 10.2.18-h6 |
| PoC Available | No third-party source we have reviewed publishes exploit code at the time of writing this. |
| Exploitation Status | CISA added CVE-2026-0300 to the KEV catalog with an FCEB remediation deadline, and several national CERTs have issued matching advisories. Per Palo Alto Unit 42, exploitation has been observed since April 9, 2026, with successful remote code execution achieved by April 16, 2026. Observed post-exploitation activity includes shellcode injection into the nginx worker process on the firewall, Active Directory enumeration using credentials extracted from the firewall, anti-forensic log cleanup, and deployment of network tunneling tools (EarthWorm, ReverseSocks5) for outbound command and control. Customers whose Authentication Portal was Internet-reachable during the pre-disclosure window should review the IOCs and artifact paths published by Unit 42 to assess whether their device may have been targeted. |
| Patch Status | Palo Alto Networks has published fixed-version targets across the 12.1, 11.2, 11.1, and 10.2 branches, and the advisory lists individual ETAs per version. Roughly half of the fixed builds are scheduled for May 13, 2026 and the remaining builds for May 28, 2026. Until the fixed build for a given maintenance line is applied, the vendor’s published workarounds are to either restrict Authentication Portal access to trusted internal networks or disable the feature entirely if it is not required. Refer to the vendor advisory for the full configuration steps. |
Censys ARC Perspective
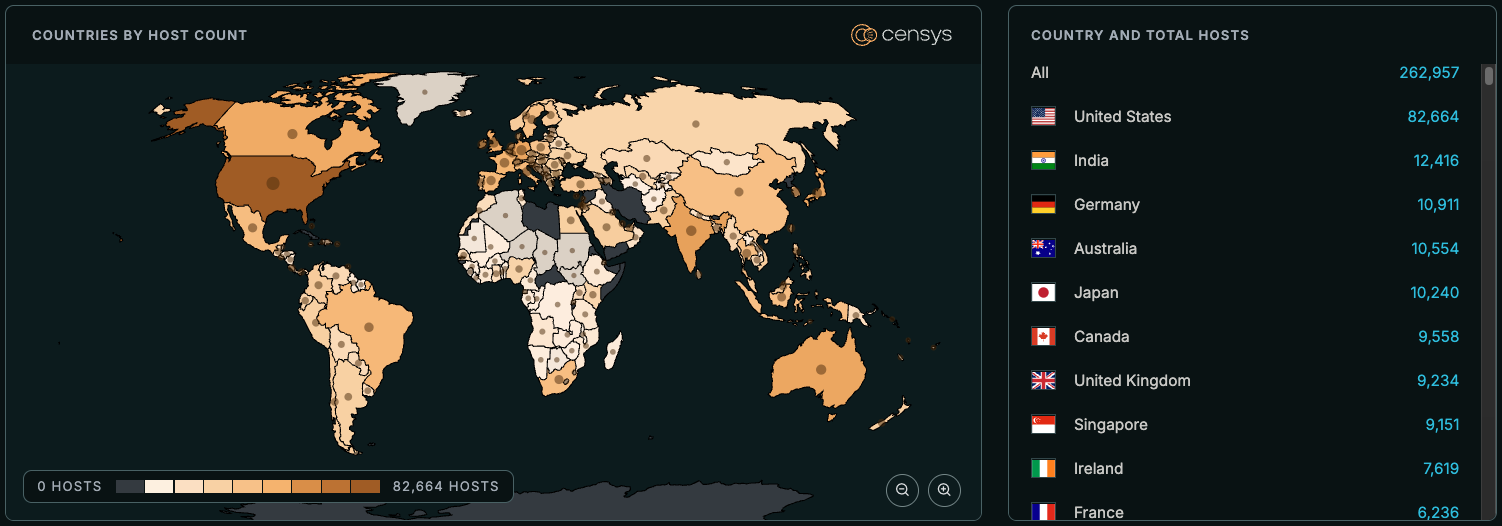
Censys observes a global footprint of roughly 263,000 Internet-exposed hosts running PAN-OS. CVE-2026-0300 affects only PA and VM-Series firewalls, and only when the User-ID Authentication Portal feature is reachable from untrusted networks. Most Internet-exposed PAN-OS instances do not appear to publish the Authentication Portal externally, and the potentially vulnerable subset we can identify from scan data is much smaller than the overall PAN-OS population.
While exploitation is active and patches are still rolling out, we are not publishing the narrowing query for the exploitable subset. Customers should identify their PAN-OS exposure using the broad query below and verify Authentication Portal configuration directly on each device.
vendor: "PaloAltoNetworks" and product: "PAN-OS" and not labels="HONEYPOT"
((host.operating_system.vendor: "Palo Alto Networks" and host.operating_system.product: "PAN-OS") or host.services.software: (vendor: "Palo Alto Networks" and product: "PAN-OS") or web_entity.instances.software: (vendor: "Palo Alto Networks" and product: "PAN-OS"))
((operating_system.vendor: "Palo Alto Networks" and operating_system.product: "PAN-OS") or services.software: (vendor: "Palo Alto Networks" and product: "PAN-OS")) and not labels: {"honeypot", "tarpit"}




