Vulnerability Description
On December 3, React disclosed CVE-2025-55182, dubbed “React2Shell,” a critical unauthenticated remote code execution flaw in React Server Components (RSC) with a maximum CVSS severity score of 10. It’s caused by an insecure deserialization within the “Flight” protocol used by RSC. It allows an unauthenticated, remote attacker to execute arbitrary code on the server by sending a specially crafted HTTP request to a Server Function endpoint.
This flaw is actively exploited in the wild: AWS researchers reported that China-nexus threat actors began exploiting this within 24 hours of public disclosure, targeting vulnerable cloud-hosted applications using RSC and often deploying web shells and backdoors shortly after initial access. As of December 5, it’s been added to CISA’s Known Exploited Vulnerabilities Catalog.
The broad adoption of frameworks like Next.js and the ease with which the vulnerability can be triggered make this a high-impact, high-likelihood issue.
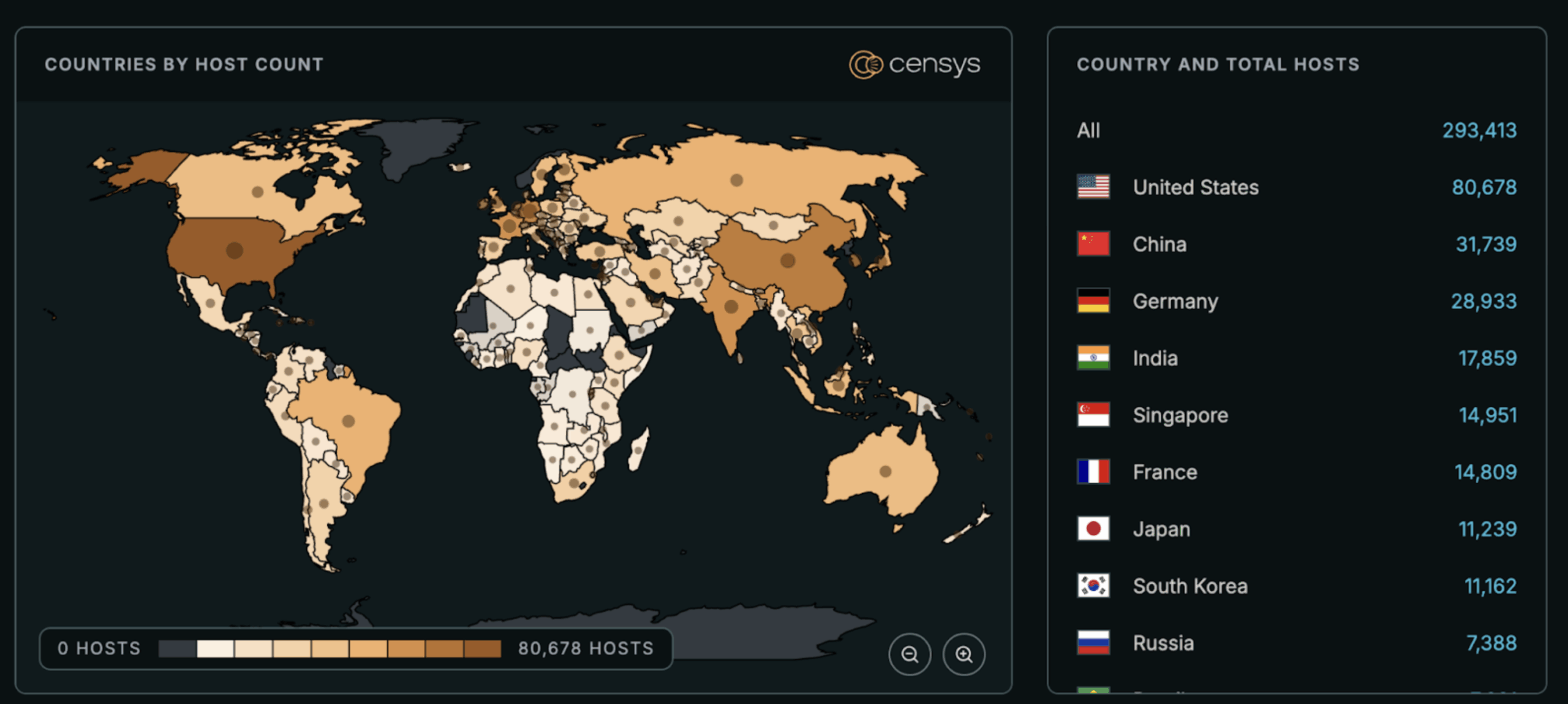
See the full breakdown by country →
Vulnerable React Packages:
The following versions are affected: 19.0.0, 19.1.0, 19.1.1, and 19.2.0 of:
- react-server-dom-webpack
- react-server-dom-parcel
- react-server-dom-turbopack
Affected Frameworks and Bundlers:
Several frameworks and tools either directly depend on or bundle the vulnerable packages:
- Next.js (next)
- React Router RSC preview (react-router)
- Waku
- Parcel RSC Plugin (@parcel/rsc)
- Vite RSC Plugin (@vitejs/plugin-rsc)
- RedwoodSDK (rwsdk)
Note that there are some conditions to consider when evaluating the impact to your environment:
- Multiple WAF providers, including Cloudflare and AWS, have added rulesets that they claim will automatically protect applications behind them from this CVE. However, some PoCs report WAF-bypass techniques. They’re not a magic bullet, so patching is still the safer and more reliable approach.
- According to React, apps that do not implement React Server Function endpoints may still be vulnerable if they support React Server Components (RSC).
- Pure Client-Side React Apps Are Safe: If your React app does not run on a server, or if you’re not using a framework or bundler that supports RSC, your app is not affected.
| Field | Description |
| CVE-ID | CVE-2025-55182 — CVSS 10 — Assigned by Facebook. |
| Vulnerability Description | React Server Components (RSC) and related packages (react-server-dom-webpack, react-server-dom-parcel, react-server-dom-turbopack) improperly deserialize JSON payloads sent to Server Function endpoints. An attacker can supply a crafted payload via HTTP request — without authentication — that causes the server to execute arbitrary JavaScript code, leading to full RCE. |
| Date of Disclosure | December 3, 2025 |
| Affected Assets | Server‑side applications using React 19.x (RSC):react-server-dom-webpackreact-server-dom-parcelreact-server-dom-turbopackAs well as any frameworks, bundlers, or libraries that embed the vulnerable react-server packages: Next.js using App RouterReact Router RSC previewWakuVite RSC pluginParcel RSC pluginRedwoodSDK |
| Vulnerable Software Versions | react-server-dom-webpack, react-server-dom-parcel, react-server-dom-turbopack versions 19.0.0, 19.1.0, 19.1.1, and 19.2.0For Next.js, versions ≥ 14.3.0-canary.77, all 15.x, and all 16.x (when using App Router) are impacted. |
| PoC Available? | Multiple public PoCs have been published. Note that there are several PoCs circulating on GitHub that have proven to be fake, incomplete, or are distributing malware. |
| Exploitation Status | Actively exploited – Amazon threat intelligence teams observed exploitation attempts by China-aligned state-sponsored groups including Earth Lamia and Jackpot Panda. As of December 5, it’s been added to CISA’s Known Exploited Vulnerabilities Catalog. Additionally, GreyNoise has published an analysis of the exploitation traffic they’ve observed against their honeypots. |
| Patch Status | Fixed versions released: React patched to 19.0.1, 19.1.2, 19.2.1; Next.js patched to 15.0.5, 15.1.9, 15.2.6, 15.3.6, 15.4.8, 15.5.7, 16.0.7. |
Censys Perspective
Given the popularity of React and Next.js, many public and private web applications are likely affected. Any internet‑accessible server running affected React Server Components code should be assumed vulnerable until updated as a precaution.
At the time of writing, Censys observes just over 2.15 million instances of internet facing services that may be affected by this vulnerability, including exposed web services using React Server Components and exposed instances of frameworks such as Next.js, Waku, React Router, and RedwoodSDK. Note that this number reflects exposures of affected software but does not filter for vulnerable versions; as such, not all of these are necessarily vulnerable.
The following queries can be used to track these exposures:
Exposed Web Services using React Server Components or an affected framework:
web.endpoints.http.headers: (key: "Content-Type" and value: "text/x-component")
or web.endpoints.http.headers: (key: "Vary" and value: "RSC")
or web.software.product: "next.js"
or web.endpoints.http.body: {"react-router-dom.js","__WAKU_CLIENT_IMPORT__", "__WAKU_ROUTER_PREFETCH__", "__WAKU_HYDRATE__", "__WAKU_PREFETCHED__","import.meta.viteRsc", "__vite_rsc", "__RWSDK_CONTEXT"
}
or web.endpoints.http.html_tags = "<meta name="generator" content="Waku"/>"
or web.endpoints.http.favicons.hash_sha256 = "4ec926d579c8540e4eb8e4eff3d0fc9060410ce5218293ddebd9ddb36e76b7e6"ASM — Broad Exposure Fingerprint:
host.services.http.response.headers: (key: "Content-Type" and value.headers: "text/x-component")
or host.services.http.response.headers: (key: "Vary" and value.headers: "RSC")
or (web_entity.instances.http.response.headers.key: "Content-Type" and web_entity.instances.http.response.headers.value.headers: "text/x-component")
or (web_entity.instances.http.response.headers.key: "Vary" and web_entity.instances.http.response.headers.value.headers: "RSC")
or host.services.software.product: "next.js"
or web_entity.instances.software.product: "next.js"
or host.services.http.response.body: "react-router-dom.js"
or web_entity.instances.http.response.body: "react-router-dom.js"
or host.services.http.response.body: {"WAKU_CLIENT_IMPORT", "WAKU_ROUTER_PREFETCH", "WAKU_HYDRATE", "WAKU_PREFETCHED", "import.meta.viteRsc", "__vite_rsc", "__RWSDK_CONTEXT"}
or web_entity.instances.http.response.body: {"WAKU_CLIENT_IMPORT", "WAKU_ROUTER_PREFETCH", "WAKU_HYDRATE", "WAKU_PREFETCHED", "import.meta.viteRsc", "__vite_rsc", "__RWSDK_CONTEXT"}
or host.services.http.response.html_tags = "<meta name="generator" content="Waku"/>"
or web_entity.instances.http.response.html_tags = "<meta name="generator" content="Waku"/>"
or host.services.http.response.favicons.md5_hash="3efbaca4b784bc49455565d443232c72"
or web_entity.instances.http.response.favicons.md5_hash="3efbaca4b784bc49455565d443232c72"ASM — Risk Fingerprint for Exposed RSC:
risks.name="React2Shell: Unauthenticated RCE in React Server Components [CVE-2025-55182]"services.http.response.headers: (key: "Content-Type" and value.headers: "text/x-component")
or services.http.response.headers: (key: "Vary" and value.headers: "RSC")
or services.software.product: "next.js"
or services.http.response.body: {"react-router-dom.js","__WAKU_CLIENT_IMPORT__" ,"__WAKU_ROUTER_PREFETCH__","__WAKU_HYDRATE__","__WAKU_PREFETCHED__","import.meta.viteRsc", "__vite_rsc", "__RWSDK_CONTEXT"}
or services.http.response.html_tags: "<meta name="generator" content="Waku"/>"
or services.http.response.favicons.hashes: "4ec926d579c8540e4eb8e4eff3d0fc9060410ce5218293ddebd9ddb36e76b7e6"Inventory, patching, and verifying package versions is strongly recommended.
References
- https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components
- https://nvd.nist.gov/vuln/detail/CVE-2025-55182
- https://aws.amazon.com/security/security-bulletins/rss/aws-2025-030/
- https://digital.nhs.uk/cyber-alerts/2025/cc-4723
- https://blog.cloudflare.com/waf-rules-react-vulnerability/
- https://www.greynoise.io/blog/cve-2025-55182-react2shell-opportunistic-exploitation-in-the-wild-what-the-greynoise-observation-grid-is-seeing-so-far




