Vulnerability Description
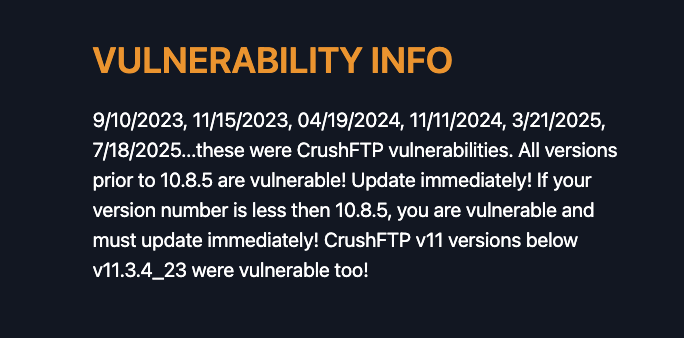
CVE-2025-54309 (CVSS 9.8) is a critical vulnerability affecting CrushFTP10 (prior to version 10.8.5) and CrushFTP11 (prior to version 11.3.4_23). When the DMZ proxy feature is not enabled, improper AS2 validation allows remote attackers to gain administrative access via HTTPS.
Threat Activity
This vulnerability is actively exploited and was added to CISA’s Known Exploited Vulnerabilities (KEV) Catalog on July 22, 2025. Other critical CrushFTP vulnerabilities, such as CVE-2025-31161 and CVE-2024-4040, have also been added to the CISA KEV in recent years, making it apparent that CrushFTP is a frequent target for attackers.
CrushFTP has acknowledged the exploitation and released an advisory with remediation steps. They noted the bug likely existed in builds before July 1st, 2025, and that attackers adapted their methods after a related AS2 fix was published. If exploitation is suspected, the developers recommend restoring a previous default user from backup, with detailed instructions available in their advisory.
Additionally, they included the following Indicators of Compromise (IoCs) in their advisory:
- The presence of “last_logins” in MainUsers/default/user.XML
- A recent modification date on default user.XML
- The default user having administrative access
- Recently created usernames with administrative privileges
- Disappearance of buttons in the end-user WebInterface, or a regular user now seeing an Admin button
- Unrecognized, long, random user IDs (e.g., 7a0d26089ac528941bf8cb998d97f408m)
| Field | Details |
|---|---|
| CVE-ID | CVE-2025-54309 – CVSS 9.8 (Critical) – Assigned by Microsoft |
| Vulnerability Description | CrushFTP 10 (before 10.8.5) and 11 (before 11.3.4_23) when DMZ proxy is not used. Improper AS2 validation allows remote attackers to gain admin access via HTTPS. |
| Date of Disclosure | July 18, 2025 |
| Date Reported Actively Exploited | July 22, 2025 (Added to CISA KEV) |
| Affected Assets | CrushFTP Web Interface when the DMZ proxy feature is not in use. |
| Vulnerable Software Versions | CrushFTP10 before version 10.8.5CrushFTP11 before version 11.3.4_23 |
| PoC Available? | There is no evidence that a public proof-of-concept exists. |
| Exploitation Status | Added to CISA KEV on July 22, 2025. |
| Patch Status | This vulnerability has been patched in CrushFTP 10.8.5 and CrushFTP 11.3.4_23 |
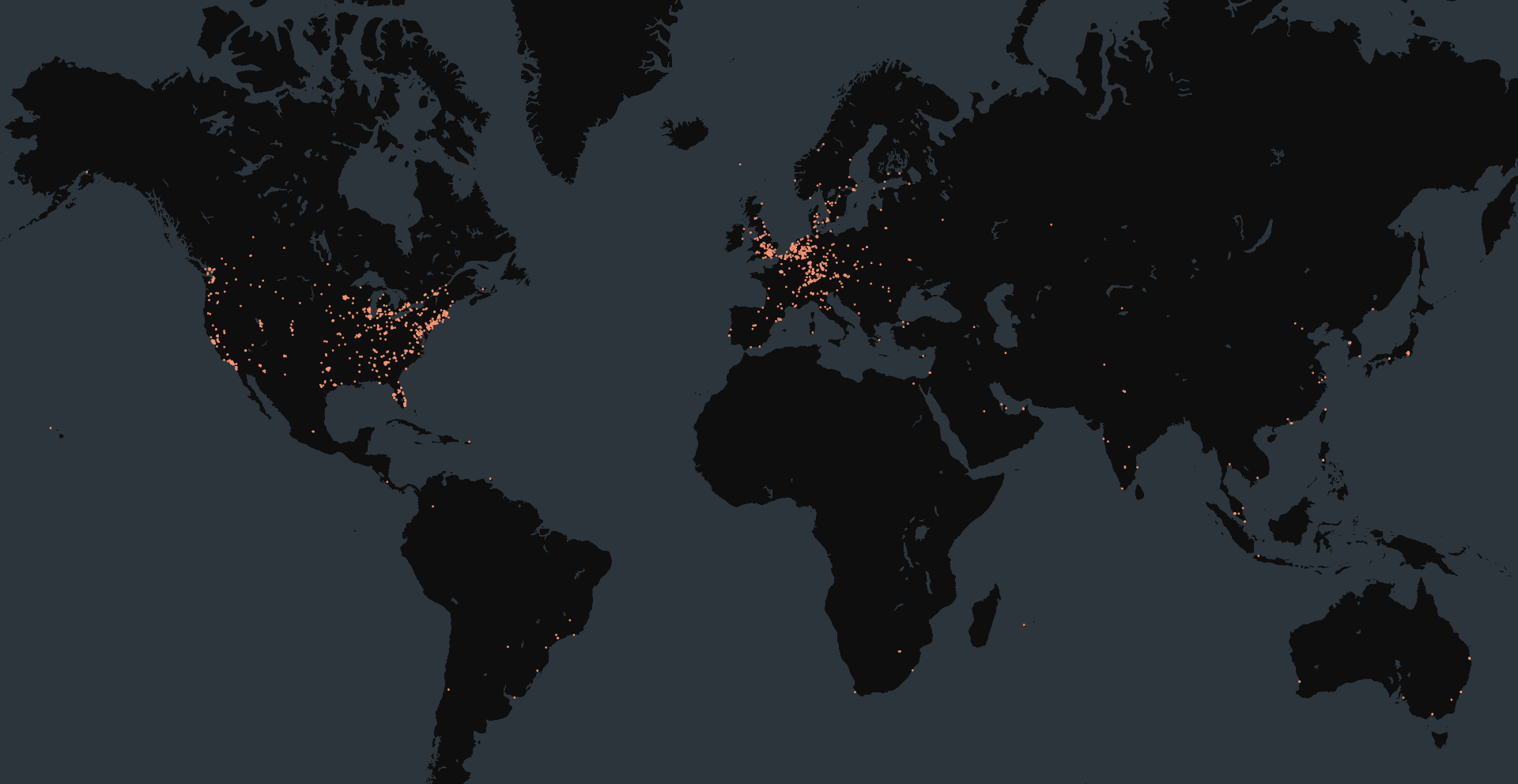
At the time of writing, Censys observed 55,683 devices exposing the CrushFTP web interface. While version information is available, it is typically limited to the major version. This means we can infer potential vulnerability for CrushFTP11 instances, but not for CrushFTP10.
The HTTP body of CrushFTP pages often contains a version string in the format:
11.W.XXX-YYYY_MM_DD_HH_MM
We believe the date in this string corresponds to the update date. When a new CrushFTP release follows a vulnerability disclosure, the date and update number can be mapped to the patched version. For example, if update 756 corresponds to the patched CrushFTP11 version, then instances with major version 11 and update numbers below 756 are potentially vulnerable. This inference is made with medium to low confidence, as it cannot be directly verified.
Examples of version strings seen in the HTML body:
src="/WebInterface/custom.js?v=11.W.756-2025_07_18_15_27"
src="/WebInterface/custom.js?v=11.W.664-2025_03_21_11_44"The queries below can help identify any devices running CrushFTP software, but they are not necessarily vulnerable.
web.software: (vendor:"CrushFTP" and product:"CrushFTP Web Interface") and not web.labels.value="HONEYPOT"host.services.software: (vendor="CrushFTP" and product="CrushFTP Web Interface") or web_entity.instances.software: (vendor="CrushFTP" and product="CrushFTP Web Interface")risks.name = "Vulnerable CrushFTP [CVE-2025-54309]"services.software: (vendor="CrushFTP" and product="CrushFTP Web Interface")