Vulnerability Description
CVE-2025-14847 (MongoBleed) is a high-severity (CVSS 7.5) uninitialized memory disclosure vulnerability that allows unauthenticated remote attackers to read uninitialized heap memory from MongoDB Server instances. This vulnerability affects MongoDB Server instances with zlib compression enabled, which is the default configuration. Successful exploitation can lead to sensitive data exposure, including potentially leaked credentials, session tokens, or other sensitive information stored in memory.
The vulnerability exists in MongoDB Server’s zlib message decompression implementation. A flaw in the decompression logic allows attackers to read uninitialized memory regions that may contain sensitive data previously stored in memory, even if that data was not intended to be accessible through normal database operations.
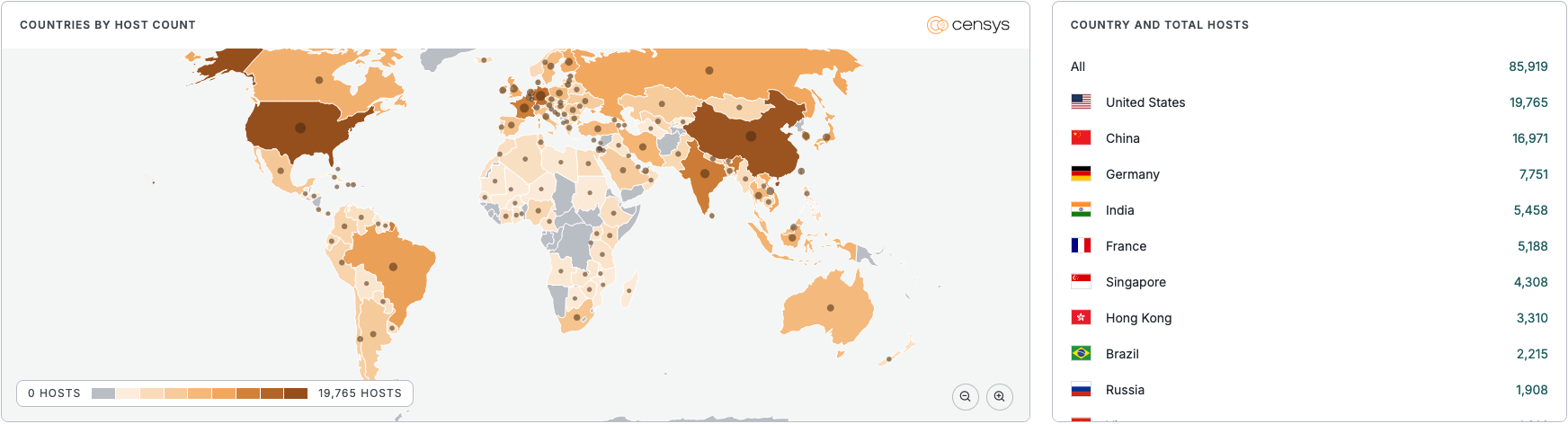
See the full breakdown by country in Censys Platform →
| Field | Description |
| CVE-ID | CVE-2025-14847 — CVSS 7.5 — assigned by MongoDB |
| Vulnerability Description | An uninitialized memory disclosure vulnerability in MongoDB Server’s zlib decompression implementation allows unauthenticated remote attackers to read uninitialized heap memory. This flaw can lead to sensitive data exposure, including potentially leaked credentials, session tokens, or other sensitive information stored in memory. The vulnerability affects MongoDB Server instances with zlib compression enabled (default configuration). |
| Date of Disclosure | December 19, 2025 |
| Affected Assets | MongoDB Server |
| Vulnerable Software Versions | MongoDB Server 8.2: 8.2.0 through 8.2.2MongoDB Server 8.0: 8.0.0 through 8.0.16MongoDB Server 7.0: 7.0.0 through 7.0.27MongoDB Server 6.0: 6.0.0 through 6.0.26MongoDB Server 5.0: 5.0.0 through 5.0.31MongoDB Server 4.4: 4.4.0 through 4.4.29MongoDB Server 4.2: All versionsMongoDB Server 4.0: All versionsMongoDB Server 3.6: All versions |
| PoC Available? | Yes, published by joe-desimone |
| Exploitation Status | No known active exploitation at time of writing. Proof-of-concept code has been published, increasing the risk of exploitation. |
| Patch Status | Fixed in patched versions:MongoDB Server 8.2.3+MongoDB Server 8.0.17+MongoDB Server 7.0.28+MongoDB Server 6.0.27+MongoDB Server 5.0.32+MongoDB Server 4.4.30+Upgrade to patched versions immediately. If upgrading is not immediately possible:Disable zlib compression by starting mongod or mongos with networkMessageCompressors or net.compression.compressors options that explicitly omit zlibRestrict network access to MongoDB instances to trusted IP addresses onlyDeploy MongoDB in a hardened environment with restricted operating system privileges Note: These workarounds do not fully eliminate the risk and should only be used as short-term measures. |
Censys Perspective
At time of writing, Censys observes 87,000+ potentially vulnerable instances, trackable with the following queries:
host.services.software: (product = "mongodb" and ((version >= "3.6.0" and version < "4.4.30") or (version >= "5.0.0" and version < "5.0.32") or (version >= "6.0.0" and version < "6.0.27") or (version >= "7.0.0" and version < "7.0.28") or (version >= "8.0.0" and version < "8.0.17") or (version >= "8.2.0" and version < "8.2.3"))) and not host.services.labels.value: "HONEYPOT"host.services: (service_name = "MONGODB" AND (mongodb.build_info.version: [3.6.0 TO 4.0.0} OR mongodb.build_info.version: [4.0.0 TO 4.4.30} OR mongodb.build_info.version: [5.0.0 TO 5.0.32} OR mongodb.build_info.version: [6.0.0 TO 6.0.27} OR mongodb.build_info.version: [7.0.0 TO 7.0.28} OR mongodb.build_info.version: [8.0.0 TO 8.0.17} OR mongodb.build_info.version: [8.2.0 TO 8.2.3}))risks.name="MongoBleed: Vulnerable MongoDB [CVE-2025-14847]"services: (mongodb.build_info.version: [3.6.0 to 4.4.29] or mongodb.build_info.version: [5.0.0 to 5.0.31] or mongodb.build_info.version: [6.0.0 to 6.0.26] or mongodb.build_info.version: [7.0.0 to 7.0.27] or mongodb.build_info.version: [8.0.0 to 8.0.16] or mongodb.build_info.version: [8.2.0 to 8.2.2])



