Executive Summary
- Censys ARC examined the Internet footprint of five different password managers and found over 31,000 instances online. Considering the sensitivity of such tooling, this may sound alarming, but each of the tools we studied are designed to be web accessible.
- Germany (22.9%), the U.S. (19.6%), and France (10.8%) are the global leaders in observed instances, and the networks where we observe them mirror this pattern. German cloud provider Hetzner, U.S.-based AWS, and France’s OVH are the top hosting providers, representing nearly a quarter (22.7%) of observations.
- Of the password managers studied, Vaultwarden is the most commonly observed by an order of magnitude, representing 62% of total observations. Just over 1700 Vaultwarden instances (9% of all Vaultwarden instances for which we can obtain a version) appear to be running a server version potentially vulnerable to two critical CVEs from early 2025.
- Contrary to popular sentiment about self-hosted software, Bitwarden and Vaultwarden instances tend to run relatively current releases: 64% of Bitwarden instances appear to be running a version ~6 months old or newer, while 65% of Vaultwarden instances appear to be ~5 months old or newer.
- We identified 20 distinct TLS certificate subject DNs with
*.govdomains on hosts running Internet-accessible password manager interfaces. Though this is a miniscule sample of the larger population studied, we note that Bitwarden is the most common password manager observed across these hosts.
Introduction
At Censys, we often discuss good security hygiene as it relates to keeping sensitive or critical assets off the public Internet. Password managers are a common recommendation for improving security hygiene, both for personal individual use as well as within organizations.
Recommending a tool in theory and deploying it safely in practice are two very different things. Password managers store incredibly sensitive data for individuals and organizations. When they’re accessible via the public Internet, running outdated versions, or not fully configured, these tools can quickly shift from a useful privacy and security tool to a liability.
We examined the Internet exposure of five different password managers to better understand the popularity of different tooling, as well as potential security concerns like outdated versions and misconfigured installations. Before we examine numbers, we should briefly discuss each of these so their exposures are well understood in context.
- Bitwarden is an open source password manager with free and paid tiers for teams and enterprises. The paid version offers single sign-on (SSO), audit logs, and more granular access controls.
- Vaultwarden is a free and open source unofficial Bitwarden server implementation written in Rust. Formerly known as “bitwarden_rs”, it’s a popular self-hosting option as it’s less resource intensive than the official Bitwarden server. It remains compatible with official Bitwarden clients.
- Passbolt is another open source password manager with free and paid tiers built for “security-conscious” teams. Self-hosted and managed cloud options are available.
- Psono is a self-hosted, open source password manager with an inexpensive business licensing scheme that offers cloud hosting.
- Teampass is a free, open source password manager with an emphasis on managing passwords in a collaborative way among team members.
At time of analysis, we observe just over 31,000 total instances of these password manager interfaces online. This may sound alarming, but exposure does not imply compromise. In fact, each of these tools are designed to be accessible via the web.
The actual concern comes, as it often does, further along in the distribution where anomalies and misconfigurations lurk. Before we explore those, let’s look at the big picture.
Censys ARC Perspective
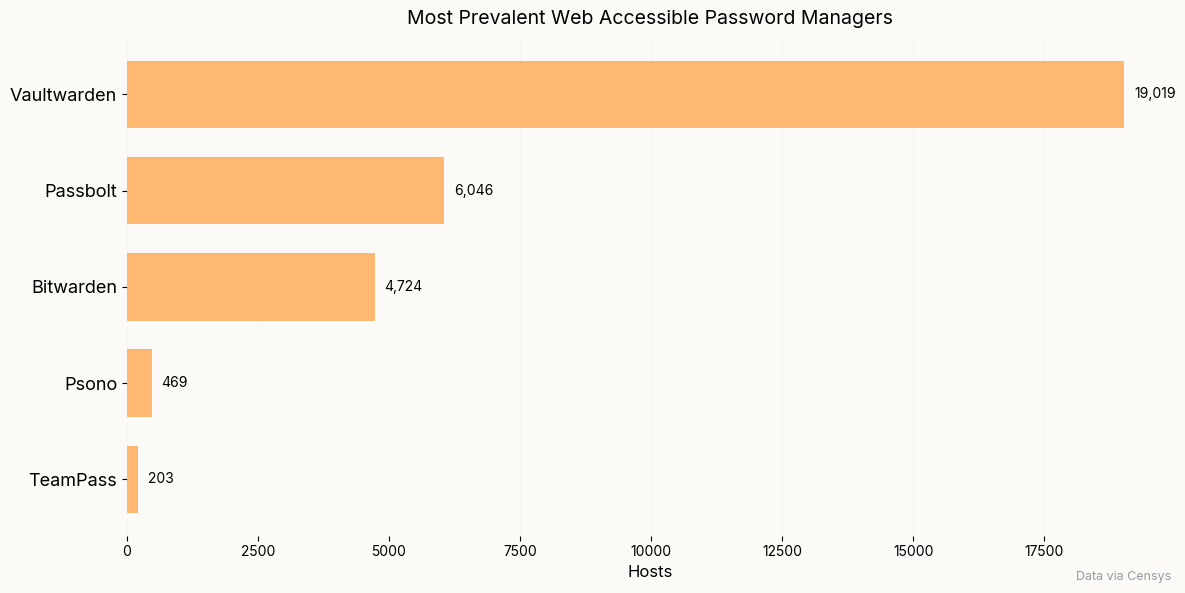
Among password managers we studied, Vaultwarden is the clear leader by an order of magnitude, representing 62% of observed interfaces. It offers many of the same premium features as Bitwarden for free and with fewer computational resource requirements, making it an attractive option for users who want to manage their own password vault.
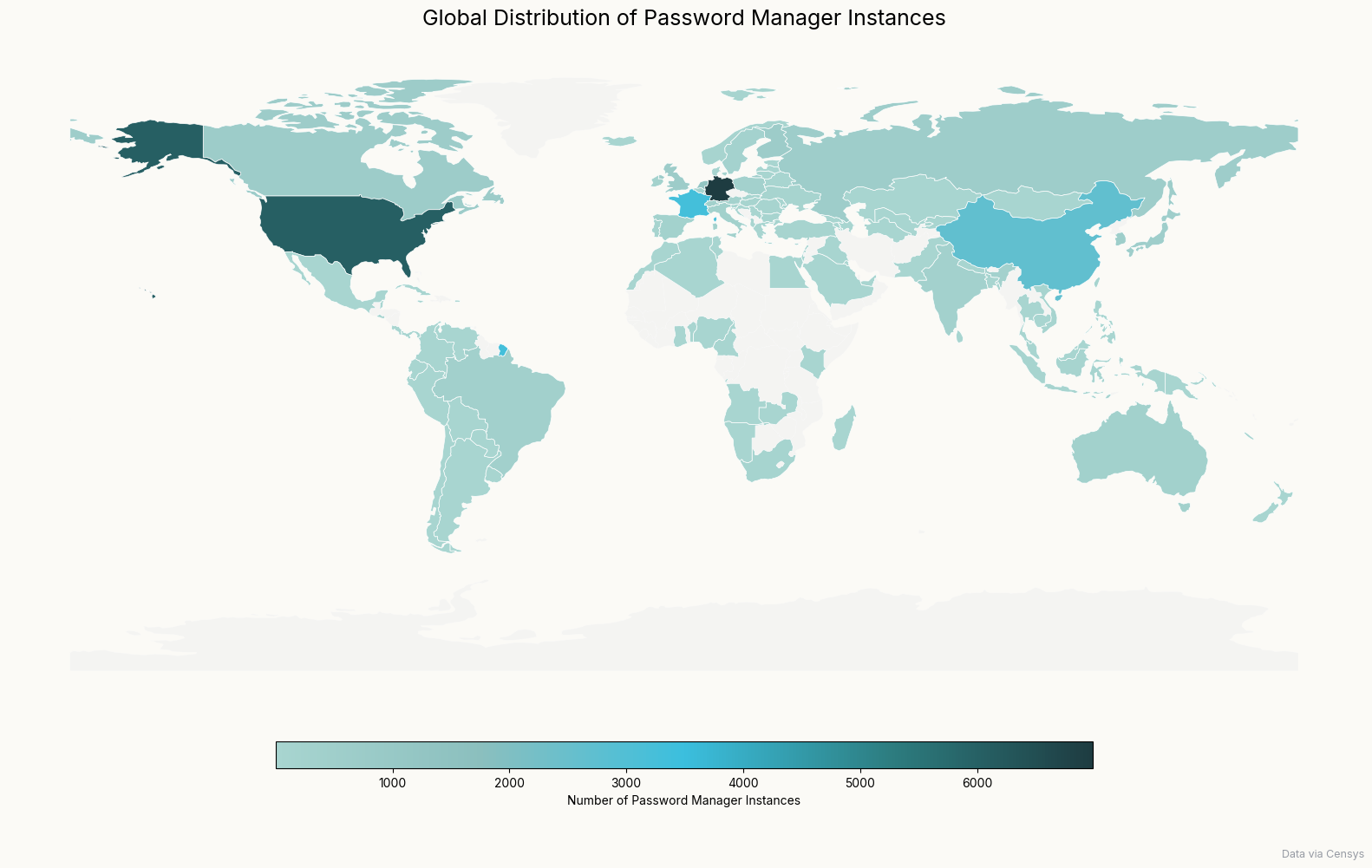
In contrast with other technologies like industrial control systems where we observe a single country dominate the exposure landscape, password manager exposures appear to be a more global phenomenon. Germany leads in observed password managers, with 22.9% of total instances observed, followed by the United States with 19.6%.
| Country | Percent of Global Password Managers |
| Germany | 22.9% |
| United States | 19.6% |
| France | 10.8% |
| China | 8.7% |
| Netherlands | 4.2% |
| Singapore | 2.3% |
| Canada | 2.3% |
| United Kingdom | 2.2% |
| Finland | 2.2% |
| Russia | 2.1% |
Top 10 countries by password manager exposure
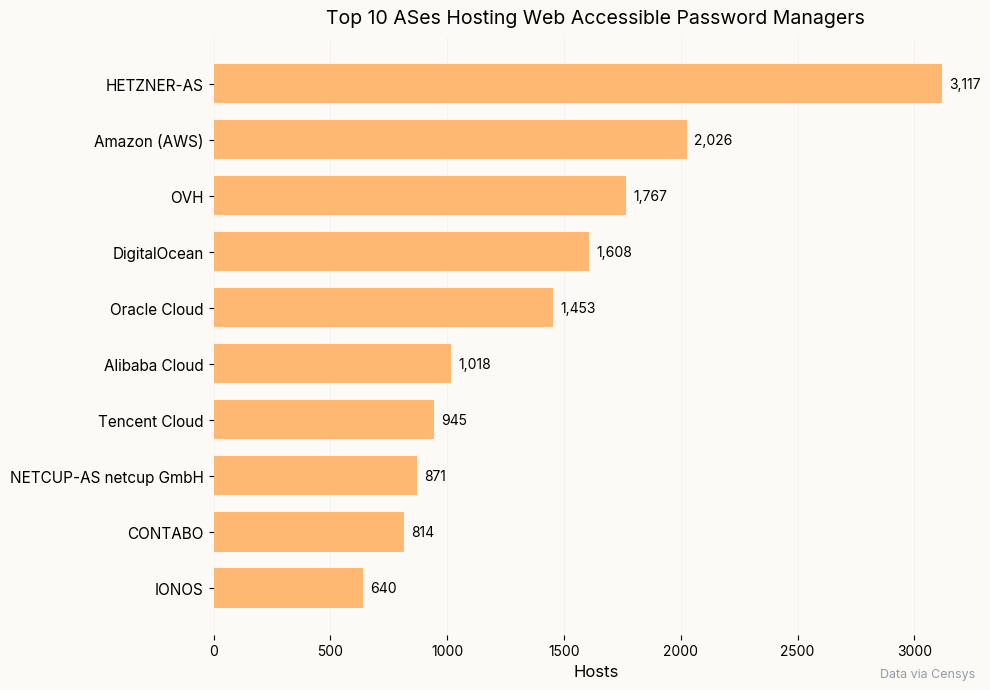
Mirroring the top three countries where we observe password manager interfaces, Germany’s Hetzner (10.2%), U.S.-based AWS (6.7%), and France’s OVH (5.8%) top the list of providers where we most commonly find these interfaces. Collectively, they represent 22.7% of where we observe password manager interfaces.
Potentially contributing to Hetzner’s popularity, they offer a step-by-step tutorial for setting up Vaultwarden via Docker image. Similarly, AWS offers multiple machine images with installs for Vaultwarden on Ubuntu, Vaultwarden on nginx and CoreOS, Vaultwarden via Hossted CLI, Vaultarden hardened via Lynxroute, Bitwarden, and Passbolt.
Vaultwarden and Bitwarden
As we began cleaning the data and performing exploratory analysis, we noted two variants of the HTML title associated with Bitwarden: “Bitwarden Web Vault” and “Bitwarden Web vault”. We identified a similar phenomenon with Vaultwarden: most titled “Vaultwarden Web” while others were “Vaultwarden Web Vault”.
While this presented a trivially annoying data cleaning task of normalization, it also raised the question of why the difference exists. One change appears to be intentional while the other (upper case “Vault” to lower case “vault”) appears less so, but regardless, we can use these changes to develop a rough estimate of the age of some of these installs.
Vaultwarden
Vaultwarden initially announced that they’d be changing their name from “bitwarden_rs” to “Vaultwarden” in April 2021, and the web interface title was eventually updated to read “Vaultwarden Web Vault” in December 2022. In early 2024, the HTML title was updated again to read “Vaultwarden Web”.
As of this analysis, we observe 540 hosts with the title “Vaultwarden Web Vault” for the web interface, suggesting that these vaults may have been instantiated prior to 2024, or used an earlier patch version when being deployed. A far larger population of “Vaultwarden Web” instances currently exist; we observe over 18,000 of these instances.
The HTML titles are a useful bellwether for when these instances might’ve been set up, and thus how outdated they might be, but determining version isn’t as straightforward as it may seem when looking at the “Vaultwarden Web Version” string in the footer of the web interface.
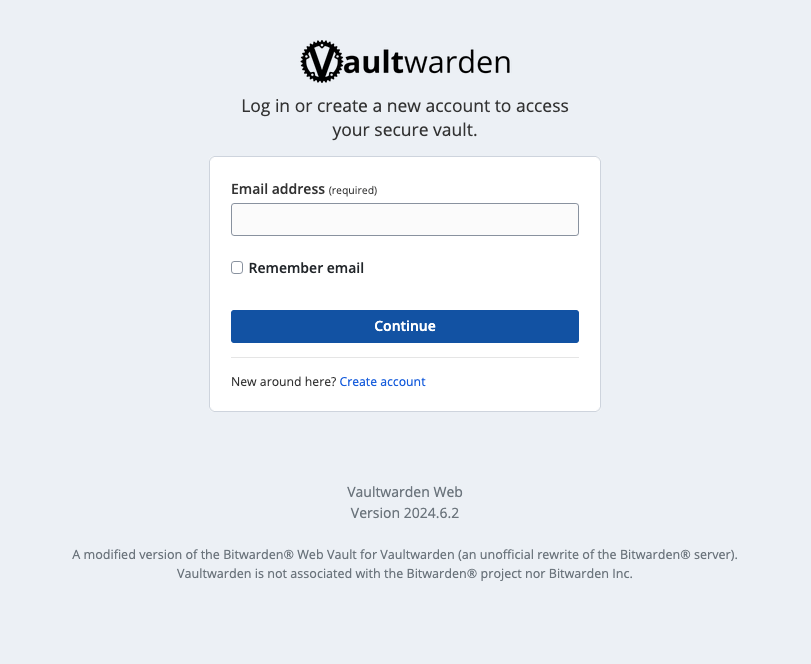
Vaultwarden web interfaces expose a version number in the page footer, at /api/config, /vw-version.json, and /version.json, and they don’t always match. Vaultwarden users have reported confusion about this, and it’s suggested to remove /vw-version.json and use /version.json as the source of truth.
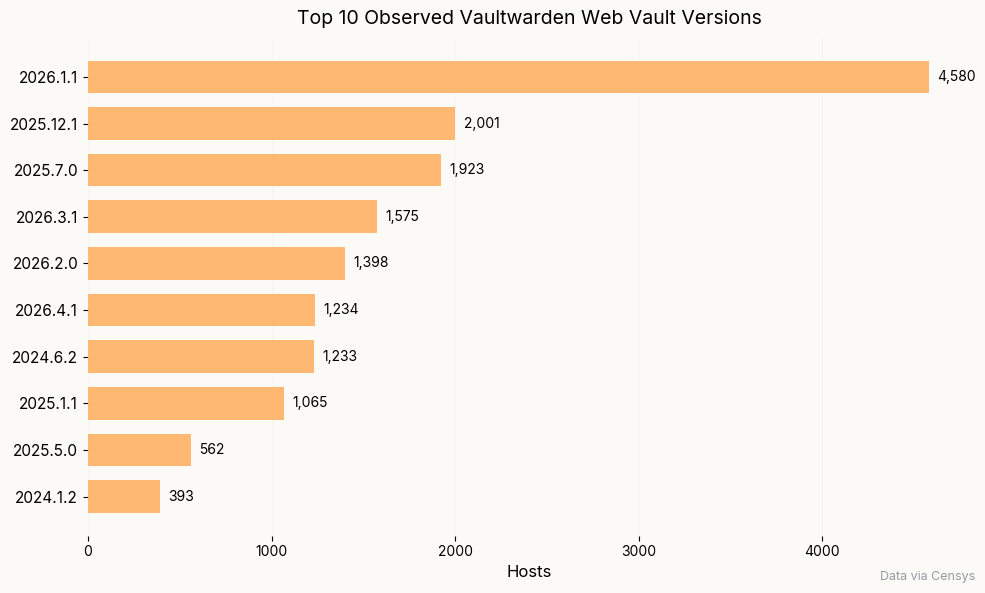
In polling the /version.json endpoint for all the web interfaces we identified, we found that 27% are running 2026.1.1, released on February 11, 2026. The oldest version in the top 10 is version 2024.1.2, which was released January 30, 2024.
There’s a chance that currently undocumented web application vulnerabilities exist in the interfaces, but to truly understand the potential security risk, we must examine the server versions as well.
Fortunately, we can enumerate server versions with data from the /api/version endpoint.
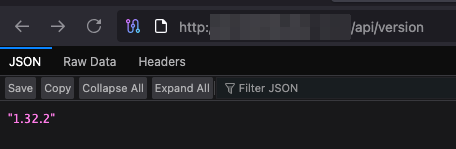
/api/versionendpoint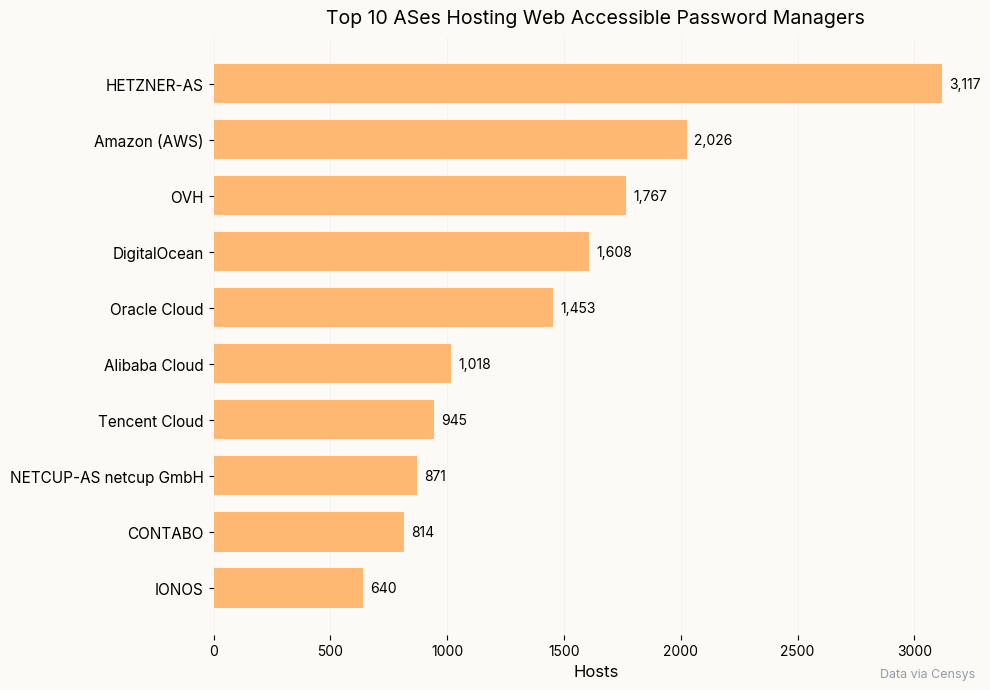
NVD currently lists 14 CVEs for Vaultwarden, only two of which are deemed critical severity:
- CVE 2024-55224 is an HTML injection vulnerability which “allows attackers to execute arbitrary code via injecting a crafted payload into the username field of an e-mail message.”
- CVE-2024-55225, is an incorrect default permissions issue which “allows attackers to impersonate users, including Administrators, via a crafted authorization request.”
In more practical terms, CVE-2024-55225 allows a threat actor to access a Vaultwarden instance without the master password. Personal vault data is encrypted with said master password, so an actor cannot decrypt the vault by accessing it in this way. The more concerning implication involves organization instances. In an organization with multiple account privilege tiers, a lower-privileged actor could login as an administrator and retrieve that user’s key material, enabling them to decrypt the organization’s secrets.
CVE-2024-55224 is an entirely separate issue that allows an actor with a Vaultwarden account to set a malicious username and trigger an emergency email invitation to a target. In this case, a malicious username would, for example, add an HTML “body separator with a custom HTML body” that could inject whatever HTML the actor wishes to deliver–spoofed login pages or other pointers to actor-controlled infrastructure.
CVE 2024-55225 is arguably the more severe of the two, but one could imagine chaining these together to target an organization’s Vaultwarden instance.
Detailed analysis of these vulnerabilities can be found here. Each of these affect Vaultwarden server versions up to 1.32.5, which comprise just over 1700 hosts at time of analysis, or roughly 9% of deployments. The oldest version in the top 10 is 1.32.7, which was released on December 20, 2024.
Surprisingly, 65% are running a release that’s no older than ~5 months (1.35.0, released December 27, 2025). We often lament about the perils of out of date and end of life software, and it appears that Vaultwarden users are cautious and mindful of their deployments.
Bitwarden
Given the similarities between Vaultwarden and Bitwarden, we can also check Bitwarden server versions using the /version.json endpoint we discovered previously.
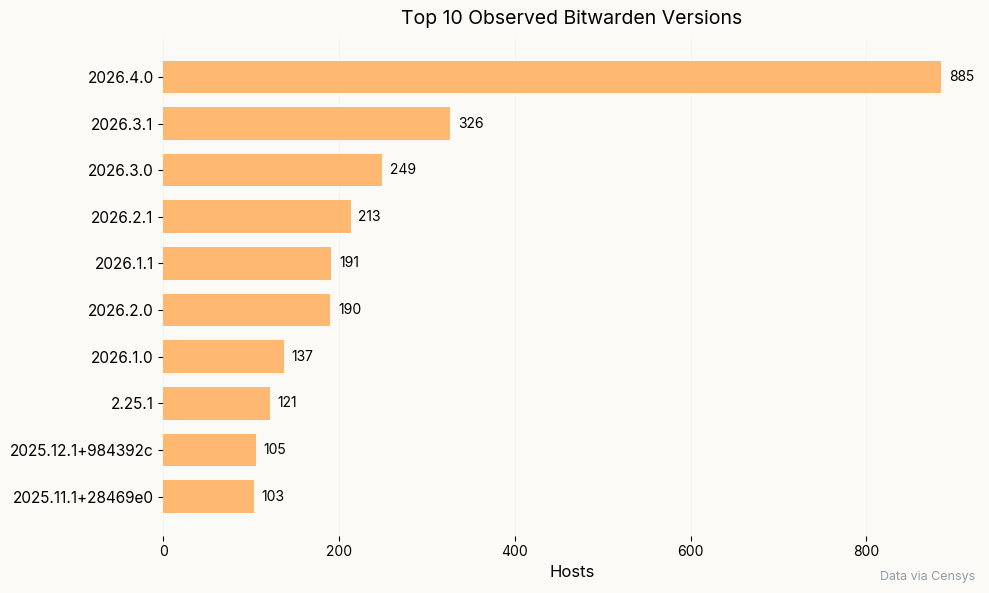
The similarities between the two password managers aren’t limited to their architecture. 64% of all Bitwarden hosts for which we were able to obtain a version appear to be running a release from no earlier than ~6 months ago (version 2025.10.2 released November 3, 2025). However, one obsolete version–2.25.1–still makes it into the top 10 most common versions we observe. Bitwarden’s documentation states that:
Prior to May 2022, clients and server each had different versioning systems. If you’re using a client or server with a version
1.xx.xor2.xx.x, you’re using an old version. When Bitwarden drops support of a version, the entire release and all previous versions will also no longer be supported.
While the above graph shows the top 10 versions we observe, as of our analysis, we find that just under 10% of all instances for which we could obtain versions are of the 1.xx.x or 2.xx.x format and are no longer supported.
Additional Findings
- 55 instances of Passbolt installer ready to be configured. Some of these appear to be personal/home deployments that were perhaps abandoned. This isn’t especially alarming, but it could point to other misconfigurations or abandoned infrastructure that could easily be usurped.
- 35 instances of Psono Admin Panel, which is an optional client separate from the Psono general web client that allows privileged users to access a “different set of APIs that are part of the Psono server and allow “promoted users” (e.g. your admins) to fulfil some tasks (e.g. reset a second factors of other users)”.
- 20 distinct certificate subject DNs containing *.gov domains, including some that appear to be from cities in the U.S., Australia, and Brazil. This is a very small subset of the greater password manager population, but Bitwarden is the most commonly observed password manager on these hosts, followed by Passbolt and Vaultwarden.
Conclusion
Self-hosted Internet accessible password vaults offer convenience that comes with several important considerations:
- Every web vault directly accessible from the Internet is one critical CVE away from disaster. That may sound dramatic, but for users who wish to host their own vault infrastructure, they must be prepared to patch at any time to protect their assets.
- Multifactor authentication (MFA) cannot be viewed as optional for web vaults that are on the public Internet. MFA provides an additional layer of security against brute forcing and credential stuffing attacks, offering protection in the worst case scenario of a master password compromise. While some password managers offer integrated TOTP functionality, the most security-conscious users may consider keeping their second factor separate from their password vault.
Conventional wisdom around self-hosted software is that convenience often wins out over maintenance: users gain full control of their data, but they are solely responsible for keeping things updated and monitoring for signs of nefarious activity like brute forcing. Cloud deployments invert this tradeoff, outsourcing both data storage and software maintenance.
Fortunately, our findings offer some nuance to this picture. Among observed Vaultwarden instances, 65% are running a release no older than 5 months, suggesting that users who take on the effort of running their own instance tend to keep it reasonably current. Bitwarden tells a similar story: 64% of observed instances appear to be running a version no older than 6 months.
Outdated and misconfigured instances exist across all the software examined here. However, the Vaultwarden and Bitwarden findings suggest that, at least in some cases, self-hosted software patching behavior may be less dire than commonly thought–particularly when that software holds the keys to one’s kingdom.