On March 4th, 2026, Check Point Security published a blog highlighting an increase in malicious activity targeting IP cameras following the onset of the conflict in Iran. Identifying internet-exposed security cameras is a basic use case for platforms such as Censys. These devices are frequently seen as an Internet hygiene concern for defenders, especially since end-of-life cameras are commonly targeted by malware families such as Mirai and Bashlite. However, this perspective does not capture the full scope of the issue.
Camera hunting is also widely practiced by open-source intelligence researchers who seek to assess the status of physical locations using publicly accessible webcams. In this context, exposed cameras aren’t just vulnerable IoT devices; they can also serve as real-time sources of operational or situational insight, making them relevant to both security research and broader intelligence analysis.
The use of open cameras for situational awareness extends beyond traditional applications. For example, Live Webcams were recently integrated into the widely used World Monitor app, as shown below.

Hunting for Cameras
The process of identifying internet-connected cameras generally begins by detecting characteristics that uniquely distinguish specific devices online. Such indicators may include vendor identifiers, service banners, HTTP response bodies, and exposed configuration files.
Public vulnerability disclosures are also useful in this process. Although the objective is not to exploit devices, vulnerability reports frequently provide technical details that reveal which products are deployed and which service and protocol types should be targeted for identification.
For example, the CISA Known Exploited Vulnerabilities (KEV) catalog, along with two additional CVEs cited in the original Check Point Research blog, provides insight into several camera vendors currently being targeted by attackers:
| Vendor | CVEs |
| Amcrest | CVE-2020-5735 |
| Dahua | CVE-2021-33044, CVE-2021-33045 |
| Edimax | CVE-2025-1316 |
| Hikvision | CVE-2017-7921, CVE-2021-36260, CVE-2023-6895, CVE-2025-34067 |
| PTZOptics | CVE-2019-11001, CVE-2021-40407 |
| Reolink | CVE-2019-11001, CVE-2021-40407 |
The information provided in these reports can be used to craft Censys queries to locate these device types.
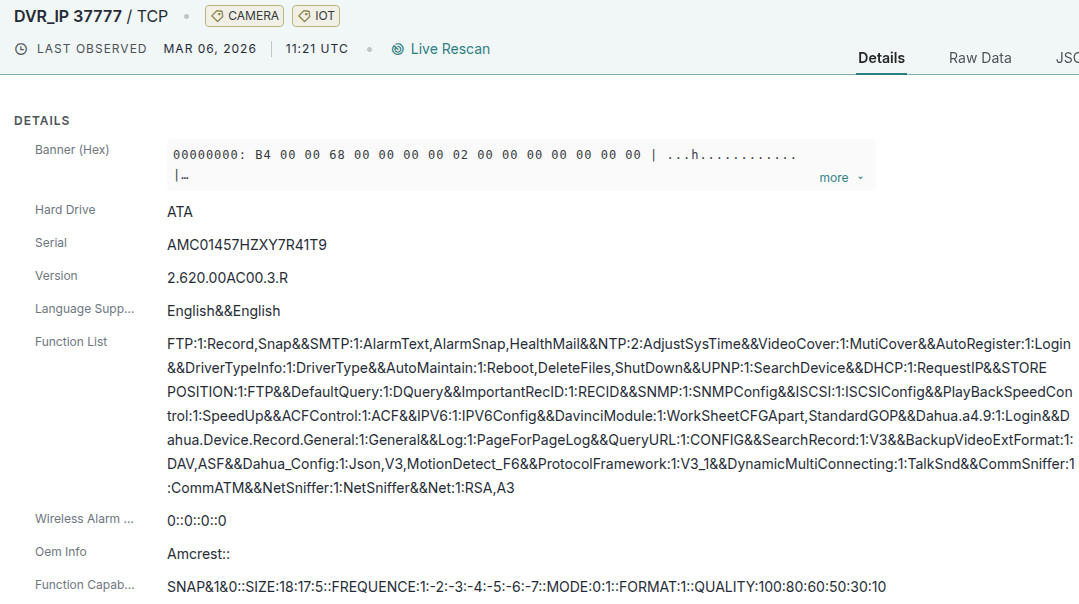
Example: Amcrest
As an example of how the Censys research team approaches discovering these cameras, let’s consider CVE-2020-5735, a vulnerability affecting certain Amcrest cameras and network video recorders (NVRs). The vulnerability allows an authenticated remote attacker to trigger a stack-based buffer overflow on port 37777, potentially crashing the device or executing arbitrary code.
Because the advisory references both a specific vendor and network port, this information can be used to identify potentially affected devices on the internet using Censys. Below, we construct a query to locate hosts that expose port 37777 and whose service banner contains the string “Amcrest”.
host.services: (port=37777 and "Amcrest")
At the time of writing, the above Amcrest query returned 1,393 results, with all but two services listening on port 37777 identified as running the DVR/IP protocol, which is widely used by Amcrest surveillance devices.
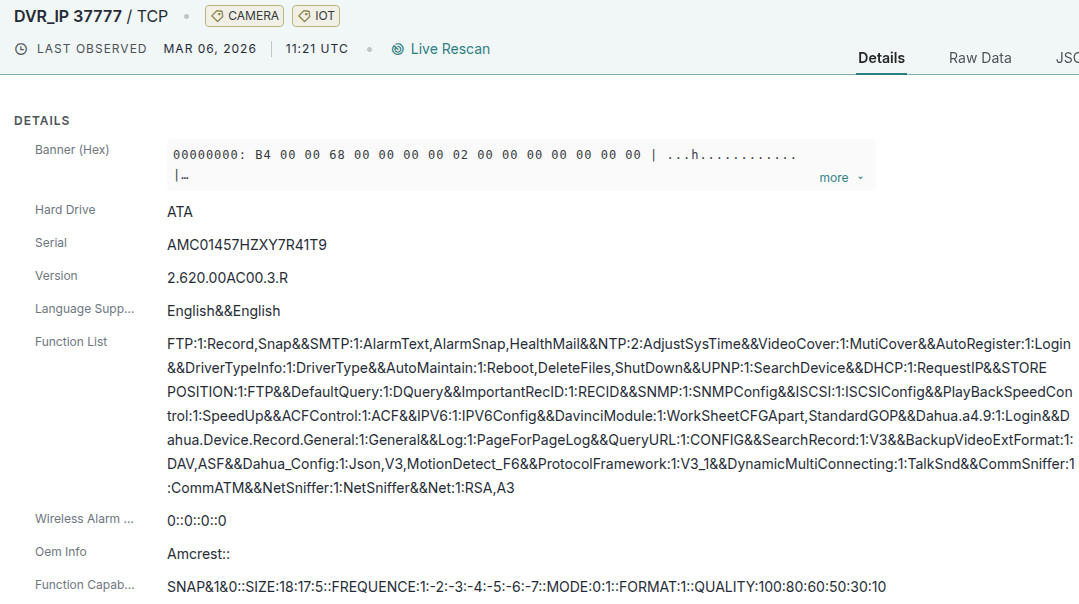
Although this vulnerability requires authentication, obtaining credentials may not be as difficult as it sounds. A simple web search for “Amcrest default username and password” quickly leads to the official Amcrest documentation for accessing the device’s web interface, which states:
“If this is the first time accessing the device, the username and password will both be admin”
Therefore, when default credentials remain unchanged, which is frequently the case, the barrier to entry for attackers seeking to compromise or exploit the camera is significantly reduced.
Example: Dahua
Alternatively, rather than targeting devices for exploitation, researchers may seek to identify cameras that already expose publicly accessible video feeds.
Using Censys, we can locate Dahua devices where anonymous access is enabled by examining configuration data collected during a scan.
When Censys detects that a service is a Dahua camera, it automatically retrieves the contents of the /web_caps/webCapsConfig endpoint. This endpoint exposes runtime configuration information used by many of the scripts loaded by the device’s web interface to render its UI.
Within this configuration is a boolean variable named Anonymous. When set to true, authentication for viewing video feeds is disabled.
So, if a researcher wanted to locate Dahua cameras with unauthenticated video feeds operating in the state of Pennsylvania, we could construct a Censys query that looks something like this:
host.services: (hardware.cpe: "cpe:2.3:h:dahuasecurity:camera" and `"Anonymous" : true`) and host.location.province = "Pennsylvania"
This query identifies services that self-report as Dahua cameras with configurations indicating that anonymous access is enabled, and filters results to hosts geolocated in Pennsylvania.
At the time of writing, more than 680 unauthenticated Dahua camera feeds were exposed to the internet globally.
Example: All the Cameras
Censys attempts to identify and label known camera-related services discovered during scans. These services can be searched using the CAMERA label:
host.services.labels.value=CAMERA
It should be noted that this label is not limited to web interfaces for cameras. It also encompasses camera-adjacent services, including video streaming protocols such as RTSP, and other software used to manage or relay camera feeds.
Censys also supports geographic filtering. For example, if we wanted to locate hosts with the CAMERA label within 1,800 km of the city of Buraydah, we could construct a query using the geo_distance function like this:
geo_distance(host.location.coordinates, "27.12", "43.29", "1800km") and host.services.labels.value="CAMERA"
This query returns hosts that Censys has identified as camera-related services within the specified geographic radius.
This query can be further refined by targeting specific software known to provide anonymous or unauthenticated video feeds. For instance, the go2rtc streaming server is frequently used to relay RTSP camera feeds and may expose them publicly if misconfigured:
geo_distance(host.location.coordinates, "27.12", "43.29", "1800km") and host.services: (labels.value="CAMERA") and host.services.software.product: "go2rtc"
At the time of writing, there were five go2rtc cameras within the defined area.
Conclusion
After the onset of the 2026 Iran conflict, WIRED highlighted a growing trend in modern warfare: the use of internet-connected consumer cameras for strategic visibility. In the initial days of the conflict, two separate reports documented the use of cameras for suspected military or intelligence purposes. Check Point Research indicated that Iranian cyber operators targeted IP cameras across Israel and neighboring states, while the Financial Times reported that actors attributed to Israel maintained long-term access to Tehran’s traffic cameras. These cases illustrate a significant use case for exposed cameras beyond tactical network access; when operational, these devices can deliver valuable real-time situational awareness.
A 2025 joint advisory from U.S. and allied agencies said GRU Unit 26165 / APT28 likely used access to private cameras from 2022 near border crossings and rail stations to monitor aid shipments into Ukraine.
It is important to note that camera targeting remains an ambiguous indicator. Since these devices are routinely scanned and exploited by a diverse range of actors, such activity alone does not necessarily imply military intent. This ambiguity contributes to the tactical value of cameras; the same access that facilitates opportunistic cybercrime can also enable reconnaissance, surveillance, and operational planning during conflict.
For defenders, this means internet-exposed cameras deserve attention not only because they may be compromised, but because, when left accessible, they can provide outsiders with persistent operational visibility. Tools like Censys make it possible to understand the scale of that exposure, helping organizations identify vulnerable or openly accessible devices before others do.