Censys started as a dream.
Ten years ago, Internet-wide scanning was an obviously lucrative tool for research. Tools like ZMap and Masscan made individual scans fast, but building a reliable, ongoing view of the Internet was far harder.
In 2015, we launched Censys to address this challenge and democratize access to scan data. No longer did researchers need to build their own infrastructure, or coordinate with their network admins, to run continuous scans. Instead, they could come to Censys to use the already collected scan data. Censys started as a dream to share data with the people who needed it most.
What first started as an academic project, however, grew into a standalone platform that is used by researchers, industry partners, and government entities alike. Along with this growth has come a complete restructuring of how we scan the Internet. We recently published a ten year retrospective paper exploring how Censys has changed in the last 10 years, how it operates today, and what we learned in the process. This blog is the first of a four-part series breaking down this retrospective — read the full paper here.
How Has Censys Changed?
So how has Censys changed at a bird’s eye view? We rebuilt our scan engine to probe 200+ protocols across all 65K ports from multiple geographic vantage points, combining exhaustive scans with probabilistic models that predict where services are likely to be. We now statefully track Internet entities, pruning stale data and assembling cohesive records that describe hosts, websites, and devices. Instead of organizing results by raw scan outputs, our pipeline extracts durable features such as software versions and manufacturers to present higher-level views of the Internet.
This shift has produced measurable improvements. In 2015, Censys found 275M IPv4 services; at the time of this analysis, it identified nearly 794M — a 188% increase (and that number only continues to grow). We also track IPv6 and name-based web properties, extending visibility beyond traditional IP scans. When compared against ground-truth estimates, we see up to 96% of services on the top 10 ports, 92% across the top 100 ports, and 82% across all ports. In practice, this means Censys surfaces 33–170% more live IPv4 services than other scanning engines and delivers estimated accuracy improvements from 35% – 820%.
While the way we collect and present data has changed dramatically since 2015, the goal has remained the same: to provide the community with the most comprehensive, accurate, and transparent map of the Internet possible.
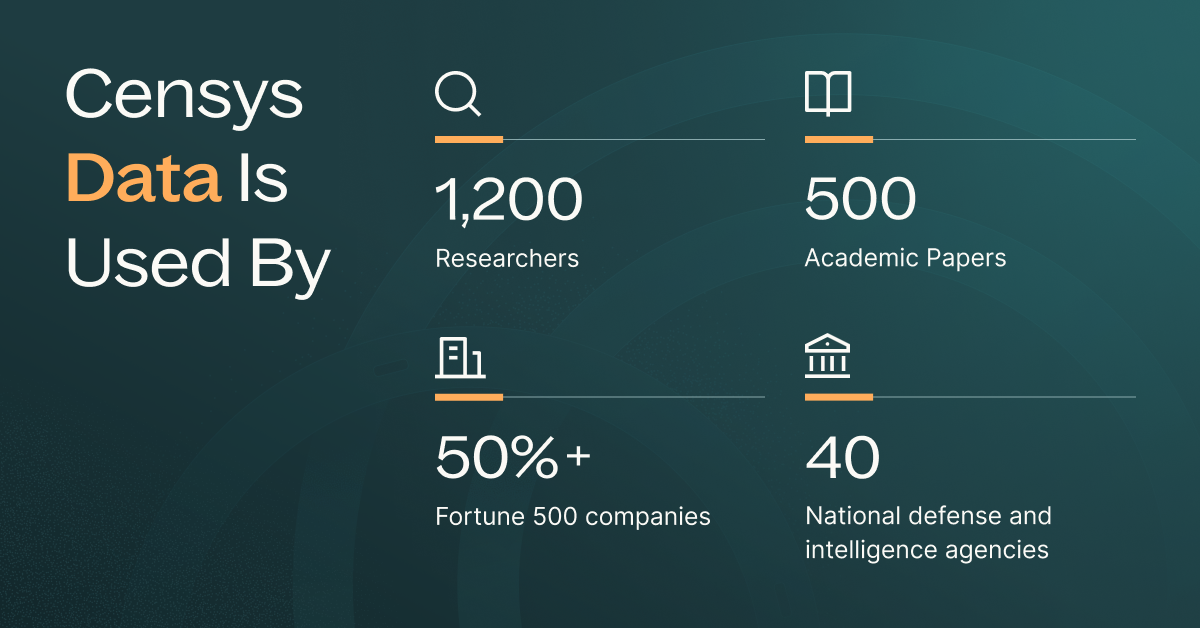
Usage: Industry and Government
While Censys primarily started as a tool for academics, it is now used widely in research, government, and industry. Today, Censys is used by global governments, leading security providers, and over 50% of the Fortune 500. It is also trusted by many of the world’s top financial institutions, telecommunication organizations, healthcare/pharmaceutical leaders, large technological entities, and energy and utility organizations.
While none of these commercial use cases were planned when we first built Censys, its widespread adoption across a broad range of use cases demonstrate how ubiquitous Censys has become.
Some of the top ways industry and government organizations use Censys include:
- Attack Surface Management: Internet-facing systems remain a common entry point for attackers, and companies rely on Censys to discover and monitor their public facing exposure. For large organizations with sprawling cloud footprints, tracking exposure is surprisingly hard. New assets appear constantly, and it can take time to figure out who owns them and whether they’re secure. Censys helps make that process faster and more complete with attack surface management.
- Supply Chain & Cyberinsurance: Organizations also track the security posture of their supplier, and as such insurers use Censys to assess risk, set premiums, and help customers strengthen their defenses.
- Critical Infrastructure: Governments use Censys to protect critical services like water, energy, and healthcare. Instead of mapping one company’s perimeter, they look for classes of vulnerabilities across whole sectors. For example, in 2024 we helped the EPA identify insecure water system interfaces in 268 U.S. towns; within months, over 97% were remediated. That effort has since grown into an ongoing partnership.
- Threat Hunting: Security teams use Censys to track attacker infrastructure, from C2 servers to compromised IoT devices. Since we continuously scan, our data can reveal malicious systems earlier than traditional intel sources, supporting both incident response and proactive defense.
- Fraud & Impersonation: Finally, companies use web and certificate data to find fraudulent sites impersonating their brands, whether through lookalike domains, favicons, or hijacked certificates, and take them down before they cause harm.
Usage: Research Community
However much we have changed, we remain true to our roots and provide access to verified researchers. As of early 2025, we have found Censys used in over 500 papers to study everything from spyware abuse and IoT security to censorship, RSA key recovery, and even reverse engineering NSO Group operations. Work citing Censys has appeared at 160 venues — most often IMC, USENIX Security, CCS, and NDSS — and has fueled nearly 100 theses and a growing number of security courses at universities like Georgia Tech, UCLA, and Stanford. We’ve also seen Censys data used in unexpected ways, such as stress-testing new systems or illustrating concepts in the classroom.
When Censys first launched, all data was freely available for non-commercial use. But after misuse by companies and concerns about malicious actors, we introduced an application-based research program in 2018. Since then, we’ve reviewed nearly a thousand requests and granted access to over 1,200 researchers at 239 organizations.
Running the program hasn’t been simple. Senior academics are easy to verify, but most requests come from students or independent researchers with little track record. To keep access fair, we require a clear research plan, intent to publish, and academic or non-profit affiliation. Still, challenges remain, from vague proposals and language barriers to universities acting as fronts for government operations. To reduce risk, we created access tiers.
Most researchers engage positively, but we’ve also seen frustration and even hostility. Despite the challenges, we remain committed to supporting the research community, while making the tough tradeoffs needed to balance openness with safety.
Stay tuned for the following three blogs that dive into system architecture, data quality assurances, and looking forward. In the meantime, read the full retrospective paper.