Vulnerability Description
CVE-2026-22557 is a critical unauthenticated path traversal vulnerability (CVSS 10.0) in the Ubiquiti UniFi Network Application. An attacker with network access can exploit this to access and manipulate files on the underlying system, leading to account compromise. No authentication or user interaction is required.
The UniFi Network Application is Ubiquiti’s centralized management platform for UniFi networking equipment. It is deployed both as a self-hosted controller on Linux/Windows and as a bundled application on UniFi OS hardware. Self-hosted controllers expose the Network Application directly and are clearly affected. UniFi OS devices also run the Network Application behind the OS portal.
| Field | Description |
| CVE-ID | CVE-2026-22557 — CVSS 10 — assigned by HackerOne |
| Vulnerability Description | CVE-2026-22557 is a critical unauthenticated path traversal vulnerability (CVSS 10.0) in the Ubiquiti UniFi Network Application. An attacker with network access can exploit this to access and manipulate files on the underlying system, leading to account compromise. No authentication or user interaction is required. |
| Date of Disclosure | March 18, 2026 |
| Affected Assets | Ubiquiti UniFi Network Application |
| Vulnerable Software Versions | Official Release: Version 10.1.85 and earlier (fixed in 10.1.89) Release Candidate: Version 10.2.93 and earlier (fixed in 10.2.97) UniFi Express (UX): Version 9.0.114 and earlier (fixed in firmware 4.0.13, which includes Network Application 9.0.118) |
| PoC Available | No public PoCs are available at time of writing |
| Exploitation Status | No in-the-wild exploitation has been reported. |
| Patch Status | Patches are available. Ubiquiti released fixed versions on March 18, 2026. Users should update to version 10.1.89 or later (Official Release), 10.2.97 or later (Release Candidate), or UniFi Express firmware 4.0.13 or later. This patch also addresses another vulnerability disclosed in the same advisory bulletin from Ubiquiti, CVE-2026-22558, which is an authenticated NoSQL injection that allows for privilege escalation within the application. |
Censys ARC Perspective
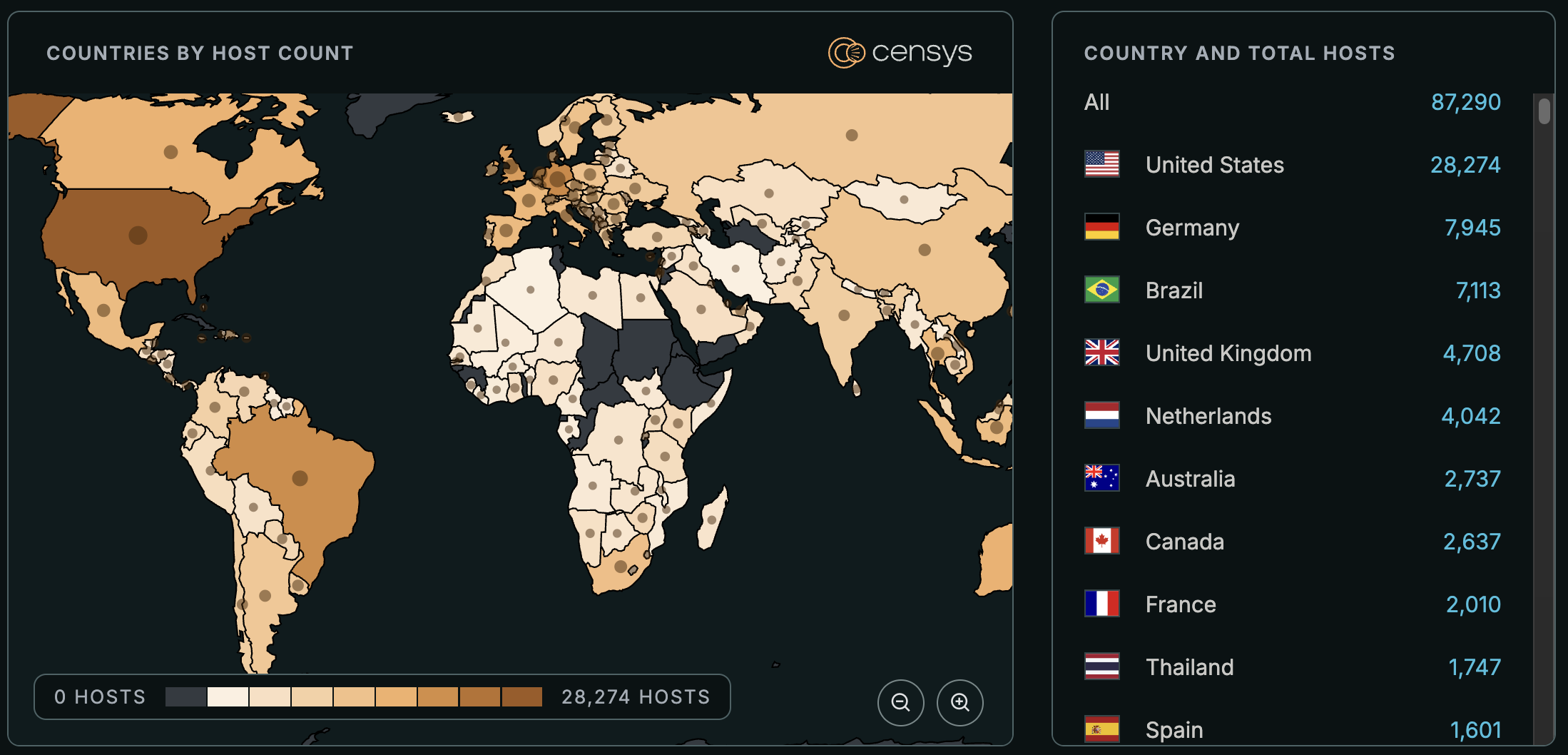
At the time of writing, Censys observes 87,196 exposed hosts with the UniFi Network Application HTML title, trackable with the queries below. This includes both self-hosted controllers and UniFi OS devices that expose the Network Application directly. An additional population of UniFi OS devices shows only the OS portal (HTML title “UniFi OS”) and is not included in that count.
The UniFi Network Application does not expose its version externally. Build hashes in static asset paths vary per version and no public mapping is readily available, so Censys cannot distinguish between vulnerable and patched instances.
(host.services.endpoints.http.html_title: "UniFi Network" or web.endpoints.http.html_title: "UniFi Network") and not labels: "HONEYPOT"
host.services.http.response.html_title: "UniFi Network" or web_entity.instances.http.response.html_title: "UniFi Network"services.http.response.html_title: "UniFi Network" and not labels: {honeypot, tarpit}




