Vulnerability Description:
Cisco Catalyst SD-WAN Controller (formerly vSmart) and SD-WAN Manager (formerly vManage) are vulnerable to an authentication bypass that lets a remote, unauthenticated attacker join the SD-WAN management plane as a rogue peer. Once joined, the attacker operates as a trusted component within the network management system, gaining access to NETCONF and the ability to read and modify SD-WAN fabric configuration across the organization. The attack requires network access to port 22 (SSH) or port 830 (NETCONF) on a controller or manager instance. Patches are available, and CISA issued Emergency Directive 26-03 on 02/25/2026 with a two-day remediation deadline for federal agencies.
According to the ACSC-led Hunt Guide, this vulnerability has been exploited in the wild since at least 2023 by a threat actor who chains it with CVE-2022-20775, a known local privilege escalation from 2022, to achieve root access. It is worth noting that Cisco did not introduce restrictions on port 830 to known system IPs until Release 20.18.1 in 2025.
| Field | Description |
| CVE-ID | CVE-2026-20127 — CVSS 10 — assigned by Cisco |
| Vulnerability Description | Cisco Catalyst SD-WAN Controller (formerly vSmart) and SD-WAN Manager (formerly vManage) are vulnerable to a remote authentication bypass that allows an attacker to gain access to NETCONF with the ability to read and modify SD-WAN fabric configuration across the organization. |
| Date of Disclosure | February 25, 2026 |
| Affected Assets | Cisco Catalyst SD-WAN Controller (vSmart), Cisco Catalyst SD-WAN Manager (vManage) |
| Vulnerable Software Versions | All Cisco Catalyst SD-WAN releases prior to 20.9.8.2, 20.12.5.3, 20.12.6.1, 20.15.4.2, and 20.18.2.1, regardless of deployment type or device configuration. Note that 20.9.8.2 is not yet available (estimated February 27, 2026 per Cisco). See Cisco advisory for the full fixed release matrix. |
| PoC Available | No public PoCs are available at time of writing |
| Exploitation Status | Actively exploited in the wild since at least 2023, per the ACSC-led Hunt Guide. The threat actor chains CVE-2026-20127 (initial access via rogue peer) with CVE-2022-20775 (local privilege escalation to root, enabled by deliberate system image downgrade to a vulnerable version). CISA KEV listed. CISA, NSA, ASD’s ACSC, Canadian Cyber Centre, NCSC-NZ, and NCSC-UK issued a joint advisory on 02/25/2026. |
| Patch Status | Fixed software releases are documented in the Cisco advisory. Mitigation is to restrict traffic to port 22 and port 830 to only known controller IPs using ACLs, firewall rules, or security group rules per Cisco Catalyst SD-WAN firewall ports guidance. |
Censys Perspective
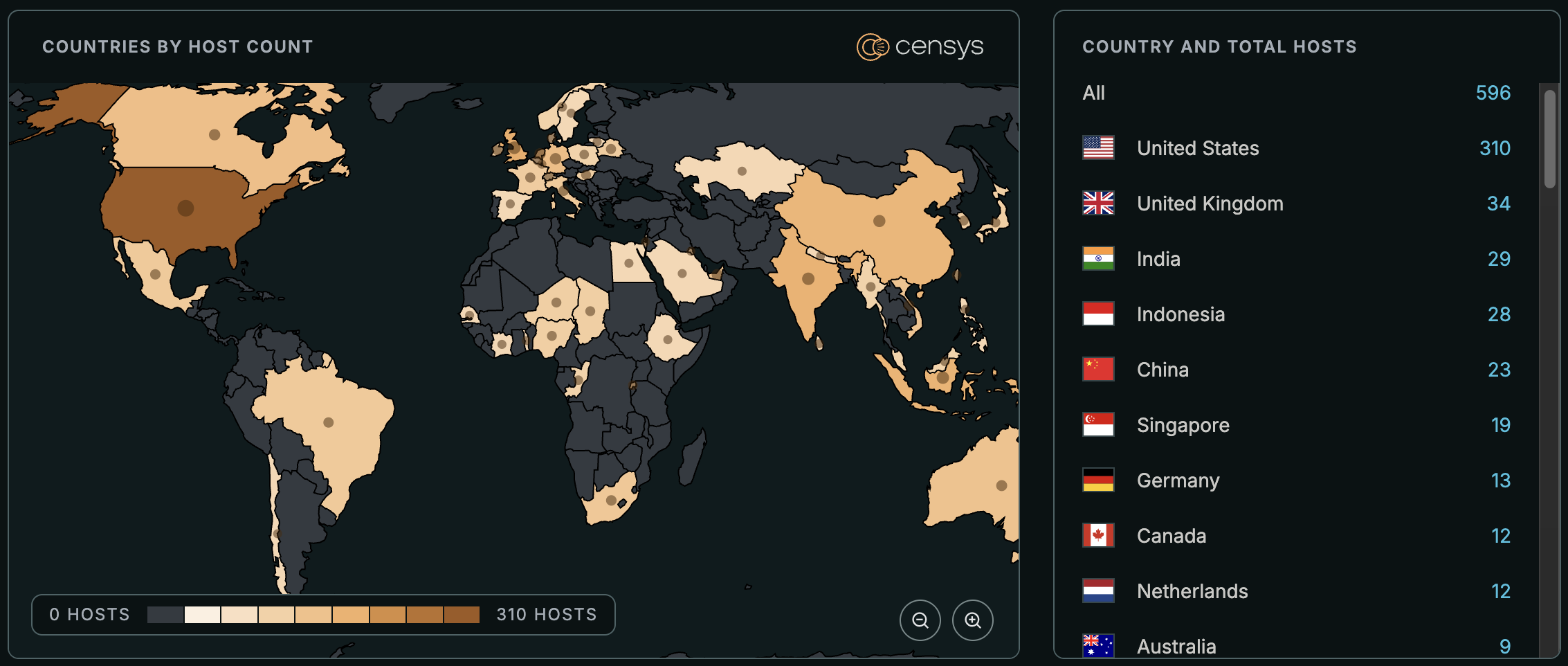
Both the ACSC Hunt Guide and Cisco’s own Hardening Guide state that SD-WAN management interfaces should not be exposed to the internet. Censys data shows that around 600 Cisco SD-WAN Manager instances are currently internet-facing, with the majority concentrated in the United States.
Exploitation of CVE-2026-20127 requires access to port 22 (SSH) or port 830 (NETCONF) on the management plane. Of the exposed SD-WAN Manager hosts, nearly 25% also expose one or both of these ports to the internet.
The observed attack chain pairs this zero-day with CVE-2022-20775, a local privilege escalation from 2022. After initial access, the actor deliberately downgrades the system to a version vulnerable to CVE-2022-20775, exploits it for root access, then restores the original version. This means even fully patched systems are at risk once the initial authentication bypass is achieved.
At time of writing, Censys sees around 600 exposed hosts, trackable with the following queries:
host.services.endpoints.http.html_title={"Cisco Catalyst SD-WAN", "Cisco SD-WAN", "Cisco vManage"} or host.services.cert.parsed.issuer_dn="CN=cisco.com, C=US, ST=CA, L=Milpitas, O=Cisco Systems, OU=Cisco SD-WAN" or host.services.endpoints.http.favicons.hash_sha256="ac75a9591065d48e5f236265a7ce1ff801e65ac73c0f17605dbe80b1c07f019e" or web.endpoints.http.html_title={"Cisco Catalyst SD-WAN", "Cisco SD-WAN", "Cisco vManage"} or web.endpoints.http.favicons.hash_sha256="ac75a9591065d48e5f236265a7ce1ff801e65ac73c0f17605dbe80b1c07f019e"host.services.http.response.html_title={"Cisco Catalyst SD-WAN", "Cisco SD-WAN", "Cisco vManage"} or host.services.tls.certificates.leaf_data.issuer_dn="CN=cisco.com, C=US, ST=CA, L=Milpitas, O=Cisco Systems, OU=Cisco SD-WAN" or host.services.http.response.favicons.md5_hash="f5a68db40594839cfc2696197608e2a3" or web_entity.instances.http.response.html_title={"Cisco Catalyst SD-WAN", "Cisco SD-WAN", "Cisco vManage"} or web_entity.instances.http.response.favicons.md5_hash="f5a68db40594839cfc2696197608e2a3"services.http.response.html_title={"Cisco Catalyst SD-WAN", "Cisco SD-WAN", "Cisco vManage"} or services.tls.certificates.leaf_data.issuer_dn="CN=cisco.com, C=US, ST=CA, L=Milpitas, O=Cisco Systems, OU=Cisco SD-WAN" or services.http.response.favicons.md5_hash="f5a68db40594839cfc2696197608e2a3"References:
- Cisco Security Advisory cisco-sa-sdwan-rpa-EHchtZk
- ED 26-03: Mitigate Vulnerabilities in Cisco SD-WAN Systems
- CISA Alert: Ongoing Global Exploitation of Cisco SD-WAN Systems
- CISA Emergency Directive 26-03
- CISA Supplemental Direction ED 26-03: Hunt and Hardening Guidance
- ACSC-led Cisco SD-WAN Threat Hunt Guide
- Cisco Catalyst SD-WAN Hardening Guide
- CISA KEV – CVE-2026-20127
- NVD – CVE-2026-20127
- Firewall Ports for Cisco Catalyst SD-WAN Deployments





