Vulnerability Description
CVE-2025-66516 is a critical (CVSS 10.0) XML External Entity (XXE) injection vulnerability in Apache Tika that allows an attacker to carry out XXE injection via a crafted XFA file inside of a PDF. The vulnerability can allow remote attackers to read sensitive data, exhaust server resources (DoS), or perform Server-Side Request Forgery (SSRF).
This vulnerability affects tika-core versions 1.13.0 through 3.2.1 (fixed in >= 3.2.2).
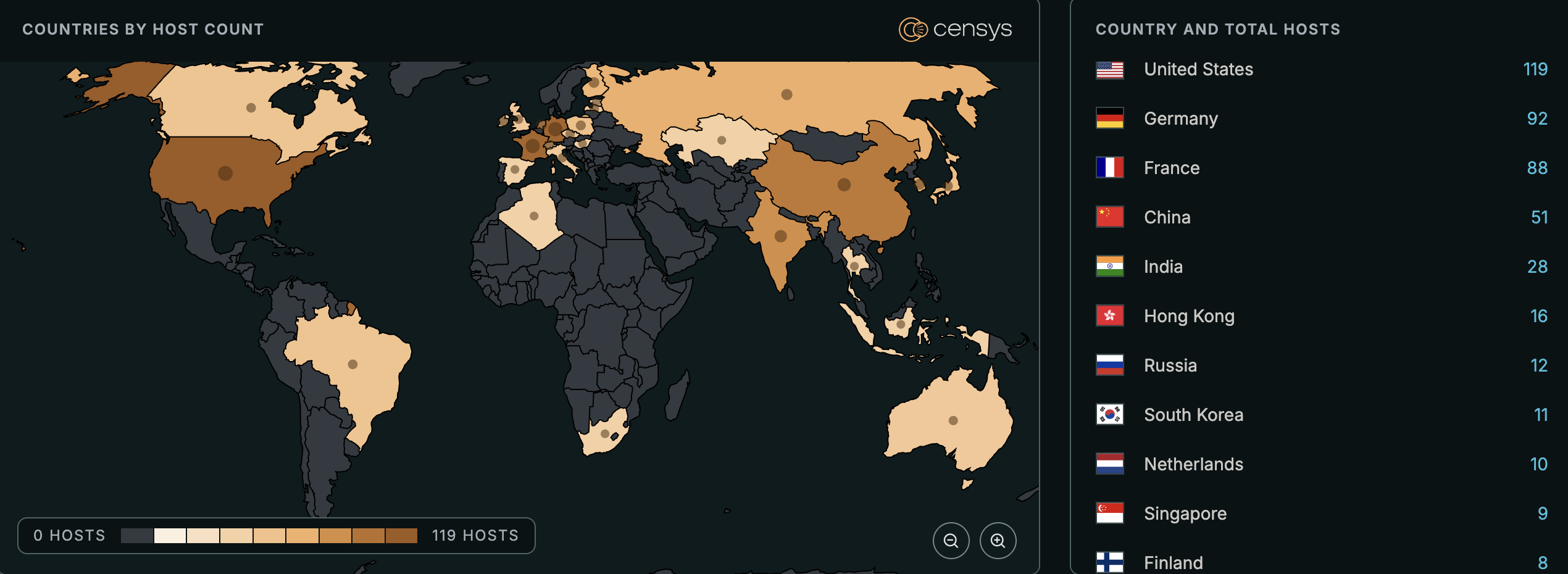
See the full breakdown by country in Censys Platform →
| Field | Description |
| CVE-ID | CVE-2025-66516 — CVSS 10 — assigned by Apache Software Foundation |
| Vulnerability Description | A critical XXE injection vulnerability in Apache Tika allows an attacker to carry out XXE injection via a crafted XFA file inside of a PDF. The vulnerability can allow remote attackers to read sensitive data, exhaust server resources (DoS), or perform Server-Side Request Forgery (SSRF). |
| Date of Disclosure | December 4, 2025 |
| Affected Assets | Apache Tika Server instances running tika-core. |
| Vulnerable Software Versions | Apache Tika Server instances running tika-core versions 1.13.0-3.2.1. Note: This detection only identifies Tika Server instances (which use tika-core). We cannot detect Maven dependencies (tika-parsers, tika-pdf-module) in user applications, so those may still be vulnerable even if this risk is not detected. |
| PoC Available? | At time of writing, there is no PoC available. |
| Exploitation Status | No known exploitation at time of writing. |
| Patch Status | Fixed in tika-core >= 3.2.2Fix Version: Upgrade Apache Tika Server (tika-core) to version 3.2.2 or later. For applications using Apache Tika as a Maven dependency (tika-parsers or tika-pdf-module), ensure those dependencies are also updated to safe versions (tika-parsers >= 1.28.6 or tika-pdf-module >= 3.2.2). |
Censys Perspective
At time of writing, Censys observes 565 potentially vulnerable instances, trackable with the following queries:
web.endpoints.http.html_title=~"Welcome to the Apache Tika ([0-9].[0-9]+(.[0-9]+)?)(-SNAPSHOT)? Server" or web.endpoints.http.body=~"^Apache Tika ([0-9].[0-9]+(?:.[0-9]+)?)nFor endpoints, please see https://wiki.apache.org/tika/TikaJAXRS"ASM:
risks.name="Vulnerable Apache Tika [CVE-2025-66516]"services.http.response.html_title=/Welcome to the Apache Tika [0-9.]+ Server/ 




