Vulnerability Description
CVE-2025-3935 affects ConnectWise ScreenConnect, formerly known as ConnectWise Control but rebranded in May 2023, versions 25.2.3 and earlier and carries a CVSS score of 7.2. The issue stems from the way ASP.NET Web Forms utilize ViewState to maintain page and control state. This state data is Base64-encoded and protected using machine keys.
If an attacker gains privileged system-level access, they can retrieve these machine keys and craft a malicious ViewState payload, potentially resulting in remote code execution (RCE) on the server.
Notably, this is a platform-level issue, not a flaw introduced directly by ScreenConnect. In other words, while the underlying issue stems from ASP.NET platform behavior, exploitation is possible within ScreenConnect’s implementation when machine keys are compromised.
Threat Activity
This vulnerability is actively being exploited and was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog on June 2, 2025.
On May 28, 2025, ConnectWise reported suspicious activity tied to a suspected nation-state actor. The activity affected a small subset of connected ScreenConnect customers. ConnectWise initiated an investigation with Mandiant, implemented enhanced hardening measures, and has reported no further suspicious activity since.
| Field | Details |
|---|---|
| CVE-ID | CVE-2025-3935 – CVSS 7.2 (High) – assigned by NVD |
| Vulnerability Description | ViewState data in ASP.NET Web Forms is Base64-encoded and secured by machine keys. Attackers with privileged system access can extract these keys and send crafted ViewStates to trigger RCE. |
| Date of Disclosure | April 24, 2025 |
| Date Reported as Actively Exploited | June 2, 2025 (CISA KEV listing) |
| Affected Assets | ConnectWise ScreenConnect servers running versions 25.2.3 and earlier, which rely on ASP.NET Web Forms and expose ViewState functionality. |
| Vulnerable Software Versions | ConnectWise ScreenConnect Versions 25.2.3 and earlier. |
| PoC Available? | There is no evidence that a public proof-of-concept exists at the time of writing. |
| Exploitation Status | ConnectWise reported suspicious activity suspected to be tied to a sophisticated nation state actor on May 28, 2025. This vulnerability was added to CISA KEV on June 2, 2025. |
| Patch Status | No action is required from cloud customers to apply the patch as updates were automatically deployed. On-premises customers are urged to follow these instructions from ConnectWise to apply the 25.2.4 patch. |
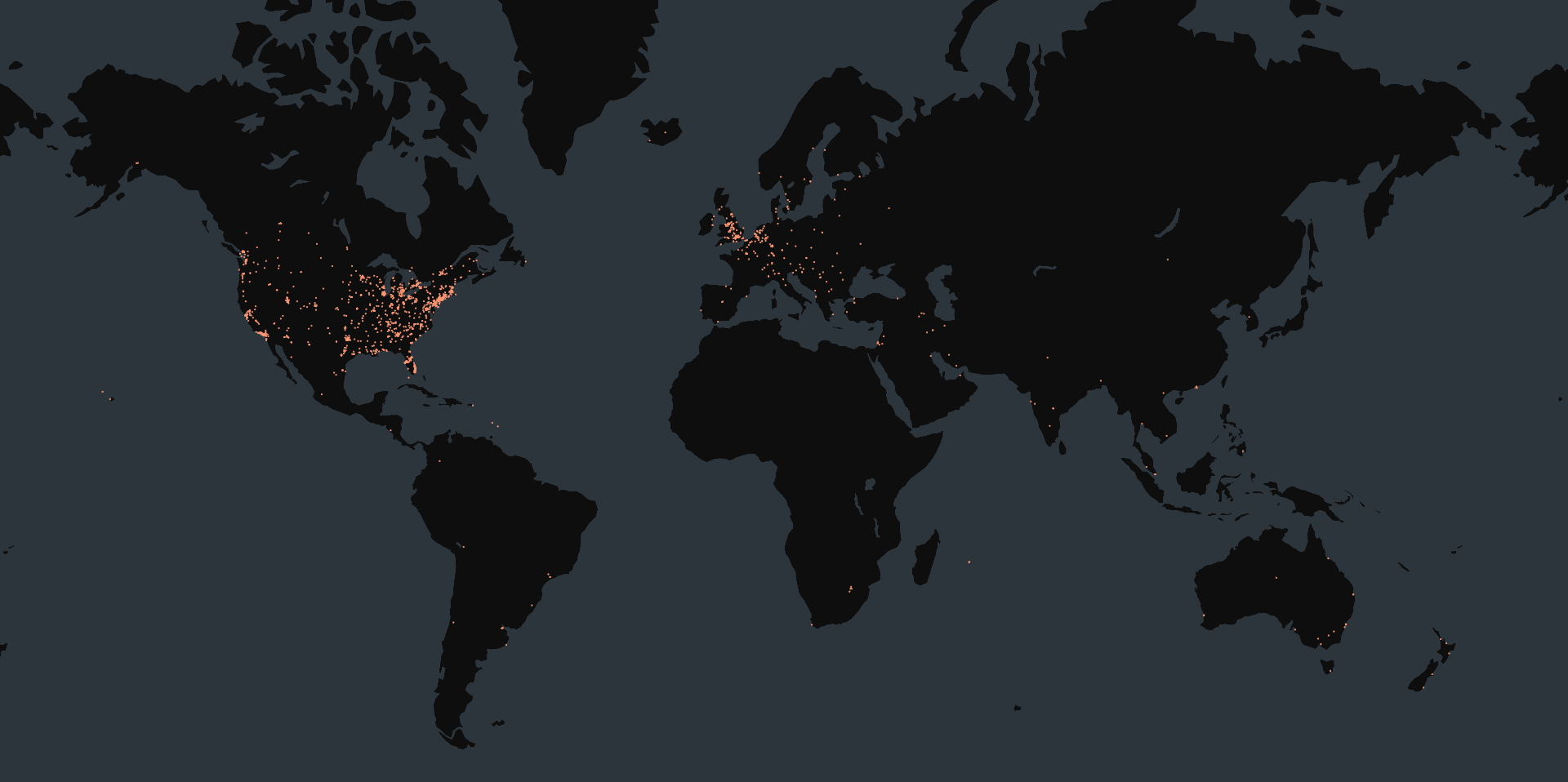
Censys Perspective
At the time of writing, Censys observed 4,338 exposed ConnectWise ScreenConnect servers online, all of which were exposing version information. The versions in the table below were observed most frequently:
| Version | Vulnerability Status | Host Count |
| 23.9.10.8817 | Vulnerable | 486 |
| 23.9.8.8811 | Vulnerable | 429 |
| 22.4.20001.8817 | Vulnerable | 336 |
| 23.2.9.8466 | Vulnerable | 181 |
| 24.1.9.8915 | Vulnerable | 174 |
| 24.2.10.8991 | Vulnerable | 144 |
| 23.9.13.9244 | Vulnerable | 144 |
| 6.3.13446.6374 | Vulnerable | 90 |
| 24.1.7.8892 | Vulnerable | 63 |
| 24.3.4.9026 | Vulnerable | 486 |
The queries below can be used to identify exposed instances of ConnectWise ScreenConnect, but they are not necessarily vulnerable to the exploit. Please note that these fingerprints were recently modified and results may take up to 24 hours to fully propagate.
host.services.software: (vendor: "ConnectWise" and product: "ScreenConnect") or web.software: (vendor: "ConnectWise" and product: "ScreenConnect")services.software: (vendor="ConnectWise" and product="ScreenConnect")host.services.software: (vendor="ConnectWise" and product="ScreenConnect") or web_entity.instances.software: (vendor="ConnectWise" and product="ScreenConnect")Please note that this risk was recently deployed and results may take up to 24 hours to fully propagate.
risks.name = "Vulnerable ConnectWise ScreenConnect [CVE-2025-3935]"