[UPDATE]: August 12, 2025
CVE-2025-32433 was added to CISA’s Known Exploited Vulnerabilities catalog on June 9, 2025.
Vulnerability Description
CVE-2025-32433 is a critical vulnerability in the Erlang/OTP framework SSH implementation affecting versions prior to OTP-27.3.3, OTP-26.2.5.11, and OTP-25.3.2.20 with a CVSS score of 9.8. If successfully exploited, it allows for unauthenticated remote code execution on the SSH server.
Erlang is a programming language designed for building scalable, high-availability systems and OTP (Open Telecom Platform) is a set of Erlang libraries that provide middleware for developing these systems. Erlang/OTP includes a built-in SSH server, and this vulnerability stems from improper parsing of incoming protocol messages—allowing attackers to execute arbitrary commands without authentication.
Threat Activity
As of June 9, 2025, this vulnerability has been added to CISA KEV and is being actively exploited. The Horizon3 Attack Team demonstrated the exploit and noted the ease of exploitation.
Multiple commits have been pushed to patch this vulnerability in OTP-27.3.3, OTP-26.2.5.11, and OTP-25.3.2.20. The Erlang/OTP team noted the following in their security advisory:
- Until upgrading to a fixed version, it is recommended that users disable the SSH server or prevent access via firewall rules.
- All users running the Erlang/OTP SSH server are impacted by this vulnerability, regardless of the underlying Erlang/OTP version. If your application provides SSH access using the Erlang/OTP SSH library, assume you are affected.
Censys Perspective
At the time of writing, Censys observed 253 exposed Erlang SSH Servers. The majority of these exposures displayed the SSH application version in the banner, not the OTP version.
However, the SSH version displayed in the banner (e.g., SSH-2.0-Erlang/4.9.1.3) corresponds to specific OTP releases. Based on Erlang’s OTP Versions Tree, SSH version 4.9.1.3 was included in OTP 22.3.4.17.
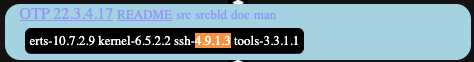
Following the mappings from that tree, we can infer the following OTP versions running on these SSH servers:
This mapping may help identify potentially vulnerable servers, though banner versions do not guarantee vulnerability even if they match a vulnerable OTP version due to potential patch backports or custom builds.

The queries below can be used to identify exposed Erlang SSH servers, but they are not necessarily vulnerable to the exploit.
host.services.software: (vendor:”Erlang” and product:”SSH”)
services.software: (vendor=”Erlang” and product=”SSH”)
host.services.software: (vendor=”Erlang” and product=”SSH”)
Note that these fingerprints were recently deployed and results may take up to 24 hours to fully propagate.





