Vulnerability Description
CVE-2025-25257 is a critical vulnerability (CVSS 9.6) affecting Fortinet’s FortiWeb Fabric Connector, which is used to connect to and manage other devices in the Fortinet ecosystem. This flaw enables unauthenticated attackers to execute arbitrary SQL commands via crafted HTTP requests, leading to remote code execution (RCE).
Fortinet has confirmed in their security advisory that FortiWeb versions 7.0.0-7.0.10, 7.2.0-7.2.10, 7.4.0-7.4.7, and 7.6.0-7.6.3 are vulnerable. Upgrading to versions 7.0.11, 7.2.11, 7.4.8, or 7.6.4 is strongly recommended. If immediate upgrading is not possible, disable the HTTP/HTTPS administrative interface as a temporary workaround.
Researchers at WatchTowr Labs observed that the get_fabric_user_by_token function does not properly sanitize input. By sending a specially crafted request (to /api/fabric/device/status with their payload in the Authorization header), attackers can exploit the SQL injection vulnerability to write a python (.pth file) into the server’s site-packages directory using the INTO OUTFILE feature of MySQL. This triggers a Python CGI script to execute the injected code, resulting in RCE.
Threat Activity
As of this writing, CVE-2025-25257 is not listed in CISA’s Known Exploited Vulnerabilities Catalog. However, given the availability of public proof of concept exploits, organizations should act quickly to mitigate risk by disabling administrative web access until patched.
| Field | Details |
|---|---|
| CVE-ID | CVE-2025-25257 – CVSS 9.6 (critical) – assigned by Fortinet |
| Vulnerability Description | A SQL injection vulnerability in FortiWeb web application firewall that allows unauthenticated attackers to execute unauthorized SQL code or commands via crafted HTTP or HTTPS requests |
| Date of Disclosure | July 8, 2025 |
| Date Reported Actively Exploited | N/A |
| Affected Assets | get_fabric_user_by_token function of Fortinet FortiWeb does not properly sanitize input. |
| Vulnerable Software Versions | 7.0.0-7.0.107.2.0-7.2.10 7.4.0-7.4.77.6.0-7.6.3 |
| PoC Available? | WatchTowr Labs published a detailed proof of concept writeup. |
| Exploitation Status | We did not observe this vulnerability on CISA’s list of known exploited vulnerabilities or in GreyNoise at the time of writing. |
| Patch Status | This vulnerability has been patched in versions 7.0.11, 7.2.11, 7.4.8, and 7.6.4 of FortiWeb. |
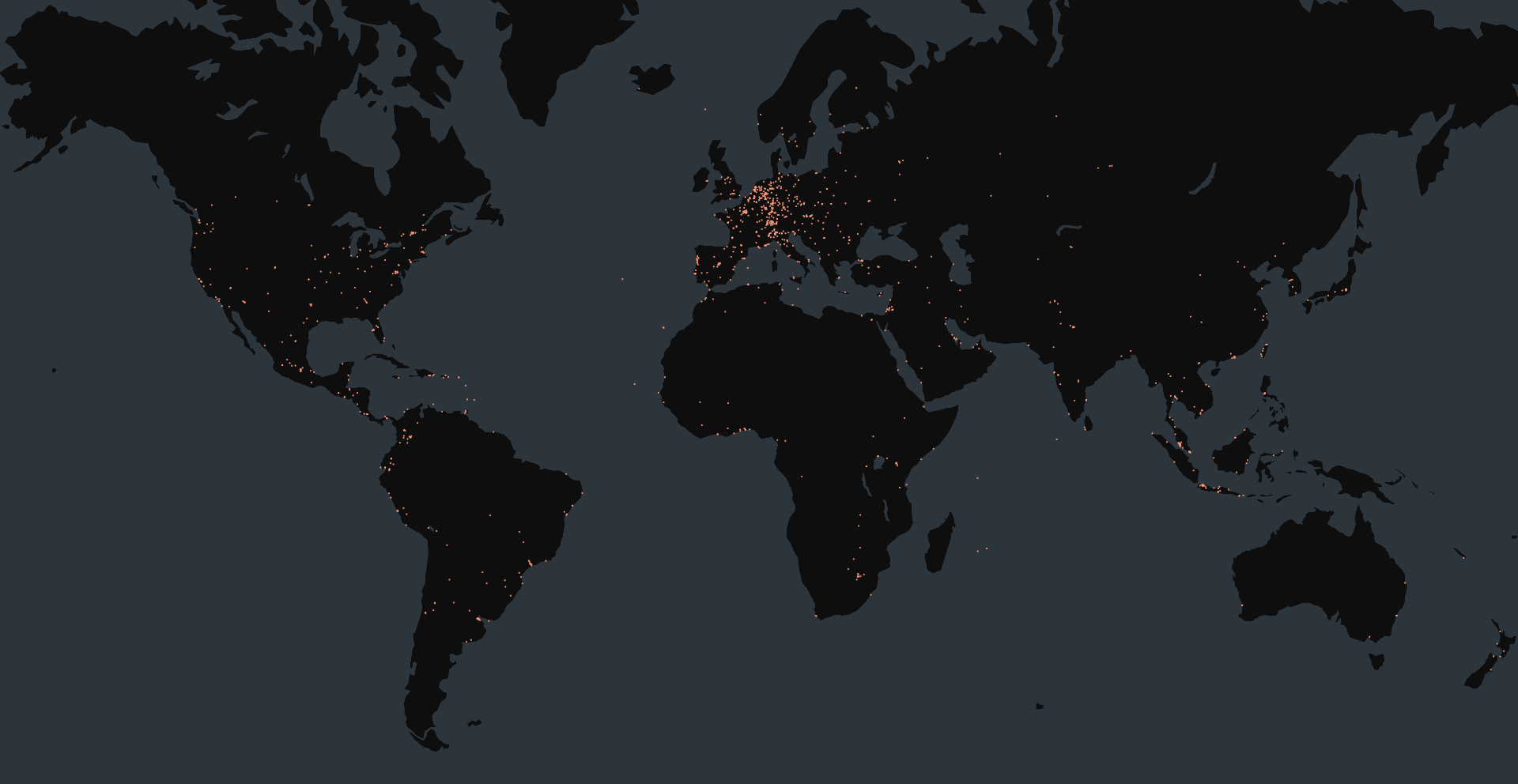
Censys Perspective
At the time of writing, Censys observed 20,098 Fortinet FortiWeb appliances online (honeypots excluded), though many did not appear to be directly exposed. A large number of hosts returned error codes (500/503), possibly due to filtering, but this does not guarantee they are fully protected. Note that we cannot identify version information for any of these hosts, so inferring vulnerability status is not possible.
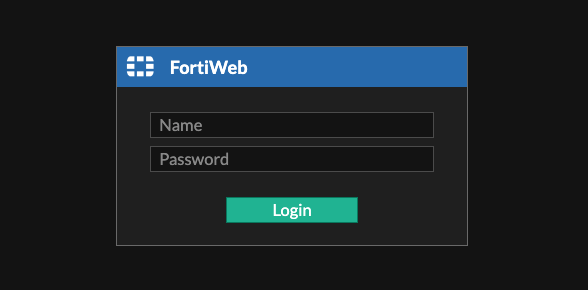
This Censys Platform query can be used to identify FortiWeb devices that did not filter out requests.
web.software: (vendor="fortinet" and product="fortiweb") and web.endpoints.http.status_code=200 and not web.endpoints.http.html_title = "Endpoint Security Required" and not web.labels.value = "HONEYPOT"
The queries below can help identify any FortiWeb devices, regardless of administrative interface exposure.
web.software: (vendor="fortinet" and product="fortiweb")host.services.software: (vendor="Fortinet" and product="Fortiweb") or web_entity.instances.software: (vendor="Fortinet" and product="Fortiweb")services.software: (vendor="Fortinet" and product="Fortiweb")