Vulnerability Description
CVE-2025-12762 is a critical remote code execution (RCE) vulnerability in pgAdmin4 server mode when restoring PLAIN-format dump files allows an attacker to inject and execute arbitrary commands on the host. Exploitation of this flaw has the potential to cause full system compromise of the pgAdmin host and downstream database environment, including database management systems and underlying data integrity.
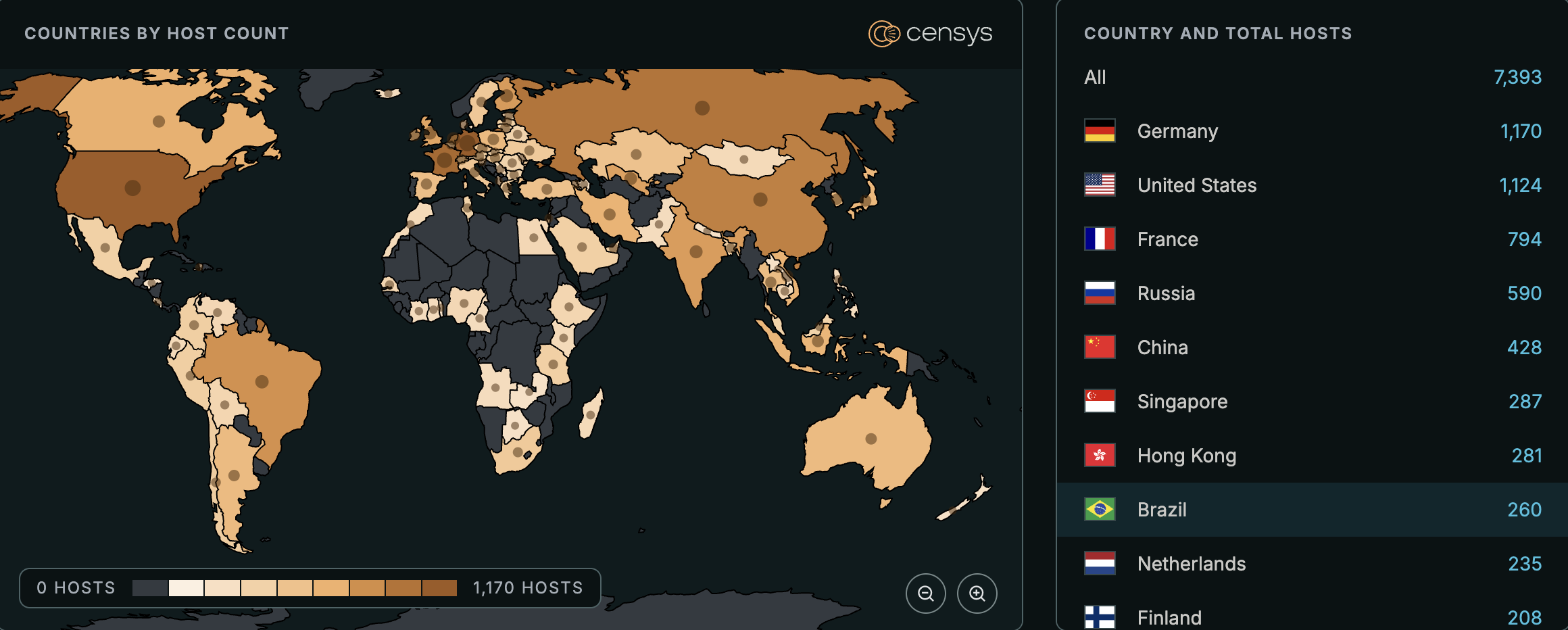
See the full breakdown by country in Censys Platform –>
| Field | Description |
| CVE-ID | CVE-2025-12762 — CVSS 9.8 — assigned by PostgreSQL |
| Vulnerability Description | A remote code execution (RCE) vulnerability in pgAdmin4 server mode when restoring PLAIN-format dump files allows an attacker to inject and execute arbitrary commands on the host.Risk impact is database management systems and underlying data integrity.Full system compromise of pgAdmin host and downstream database environment is possible through this flaw. |
| Date of Disclosure | November 13, 2025 |
| Affected Assets | pgAdmin4 server |
| Vulnerable Software Versions | pgAdmin4 server mode version 9.9 or earlier.Requires the dump restore functionality using PLAIN-format files. |
| PoC Available? | No public PoC is currently available. |
| Exploitation Status | No known exploitation at this time |
| Patch Status | Upgrade to pgAdmin4 version 9.10 (or later) |
Censys Perspective
At the time of writing, Censys observes 7,393 instances of potentially exposed hosts, trackable with the following queries:
host.services.software: (product: "pgadmin_4" and version<"9.10") and not host.services.labels.value: "HONEYPOT"risks.name: "Vulnerable pgAdmin 4 [CVE-2025-12762]"services.software: (product: "pgAdmin 4" and version: {* to 9.10.0}) and not labels: {honeypot, tarpit}



