Vulnerability Description
CVE-2026-41940 is a critical (CVSS 9.8) pre-authentication bypass in the cPanel and WHM login flow, disclosed by cPanel on April 28, 2026. A remote unauthenticated attacker can obtain administrative access to the cPanel/WHM server. cPanel’s changelog attributes the fix to session loading and saving (CPANEL-52908).
| Field | Description |
| CVE-ID | CVE-2026-41940 — CVSS v3 9.8— assigned by VulnCheck |
| Vulnerability Description | A critical pre-authentication bypass in the cPanel and WHM login flow allows a remote unauthenticated attacker to obtain administrative access to the cPanel/WHM server. |
| Date of Disclosure | April 28, 2026 |
| Affected Assets | Vendor: cPanel Product: cPanel and WHM |
| Vulnerable Software Versions | Versions: cPanel and WHM builds prior to 11.110.0.97, 11.118.0.63, 11.126.0.54, 11.130.0.18, 11.132.0.29, 11.134.0.20, and 11.136.0.5. Default ports: 2082 (cPanel HTTP), 2083 (cPanel HTTPS), 2086 (WHM HTTP), 2087 (WHM HTTPS), 2095 (Webmail HTTP), 2096 (Webmail HTTPS) |
| PoC Available | Yes — published by WatchTowr on Paril 29, 2026. |
| Exploitation Status | webhosting.today reports scanning and exploitation attempts against unpatched servers beginning the same day as the advisory. Namecheap and InMotion confirm on their public status pages that they firewalled the cPanel and WHM web ports during the patch window. |
| Patch Status | Patched by cPanel on April 28, 2026. Fixed cPanel and WHM builds: 11.110.0.97, 11.118.0.63, 11.126.0.54, 11.130.0.18, 11.132.0.29, 11.134.0.20, 11.136.0.5. cPanel updated the advisory page on 2026-04-29 14:46 CST with a detection script that server administrators can run to scan local session files for indicators of compromise. |
Censys ARC Perspective
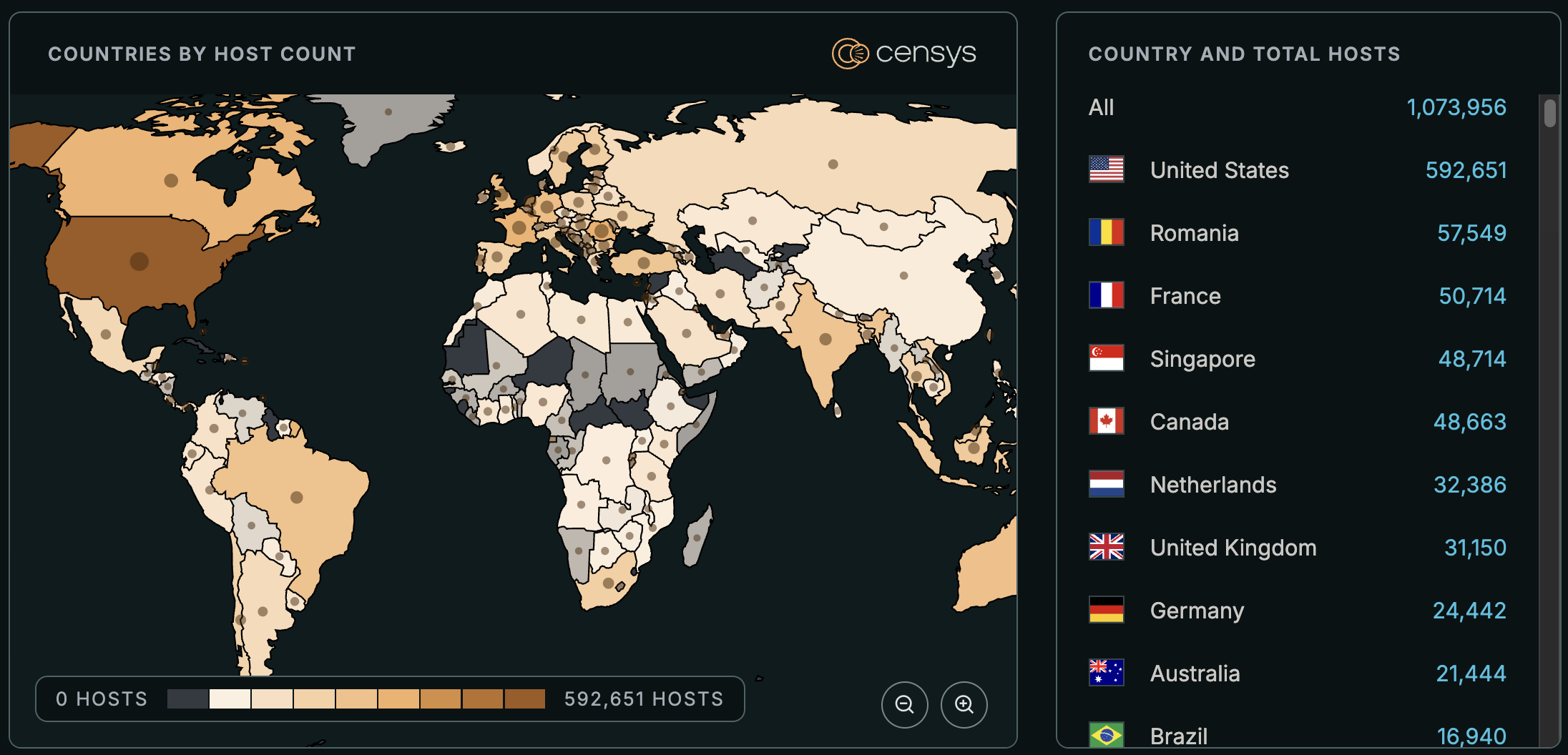
The exposed cPanel/WHM control plane is heavily clustered in a handful of large shared hosting operators: GoDaddy, Bluehost, Oracle Cloud, OVH, Network Solutions, A2 Hosting, Namecheap, Liquid Web, and InMotion together account for nearly half of the cPanel/WHM hosts we see. That concentration means the speed of Internet-wide remediation is largely gated by how quickly a small number of operators patch their fleets.
Another point worth mentioning is that narrowing this population to specifically vulnerable builds from scan data is challenging. The most direct version signal, the Server: cpsrvd/<version> header, is absent on the majority of cPanel/WHM hosts we observe, and the hosts that do return it are mostly running older, end-of-life release branches that cPanel did not publish fixes for. Other body and asset markers we examined cluster installs into release branches but do not reliably distinguish a patched build from an unpatched build within the same branch. Our recommendation to customers is to treat any exposed cPanel or WHM control plane as in-scope until the running build is verified locally.
While these conditions make it difficult to accurately identify the current number of exposures, the following Censys queries return about 1.1 million exposed hosts and 6.7 million exposed web properties.
(host.services.software.product="cpanel" or host.services.software.product="whm" or web.software.product="cpanel" or web.software.product="whm") and not labels="HONEYPOT"host.services.software:(product=`cPanel` or product=`WHM`) or web_entity.instances.software:(product=`cPanel` or product=`WHM`)services.software.product=`cPanel` or services.software.product=`WHM`




