This year I presented at the 2026 SANS CTI Summit on a small, unusual operation from 2022 focused on the Rhadamanthys infostealer. A lot of the cyber operations we talk about publicly are framed around a clean win: infrastructure seized, domains sinkholed, threat actors arrested.
This wasn’t that.
If you’re looking for a disruption success story, Operation Endgame, led by Europol and partners, is a fantastic read. My goal here is different. Using Rhadamanthys as a case study, I want to describe the limits private-sector researchers run into when acting alone or without law enforcement, and what “meaningful action” can look like when the only safe, defensible moves are constrained. In practice, that often means maximizing a narrow opportunity to reduce harm, without crossing the line from observing evidence to changing systems.
Rhadamanthys
Rhadamanthys is an infostealer — a type of malware designed to harvest credentials, cryptocurrency wallets, and other sensitive files from infected computers. At scale, infostealer “logs” become a supply chain for the underground economy: packaged collections of stolen usernames, passwords, browser data, and session artifacts that are bought and resold to enable follow-on activity. Markets like Genesis Market (prior to its 2023 takedown) and Russian Market commonly resell credentials stolen by infostealers.
In late summer 2022, Rhadamanthys was a new player in the infostealer scene. Like many stealers, buyers received a package that let them stand up a web-based control panel on their own infrastructure. Operators used the panel to generate payloads, manage infections, and retrieve stolen data.
Unbeknownst to the developer, early versions of these panels had a serious authentication weakness: while users normally needed a username and password to log in, API endpoints used by the frontend could be accessed without authentication. In practice, that meant anyone who could reach a vulnerable panel could potentially enumerate infections and pull data directly from the server. This vulnerability presented a unique operational opportunity to take an active step forward. In practical terms, the most defensible use of that access was also the least glamorous: treat it as a time-limited visibility window, and use it to support harm reduction through established reporting and notification channels.
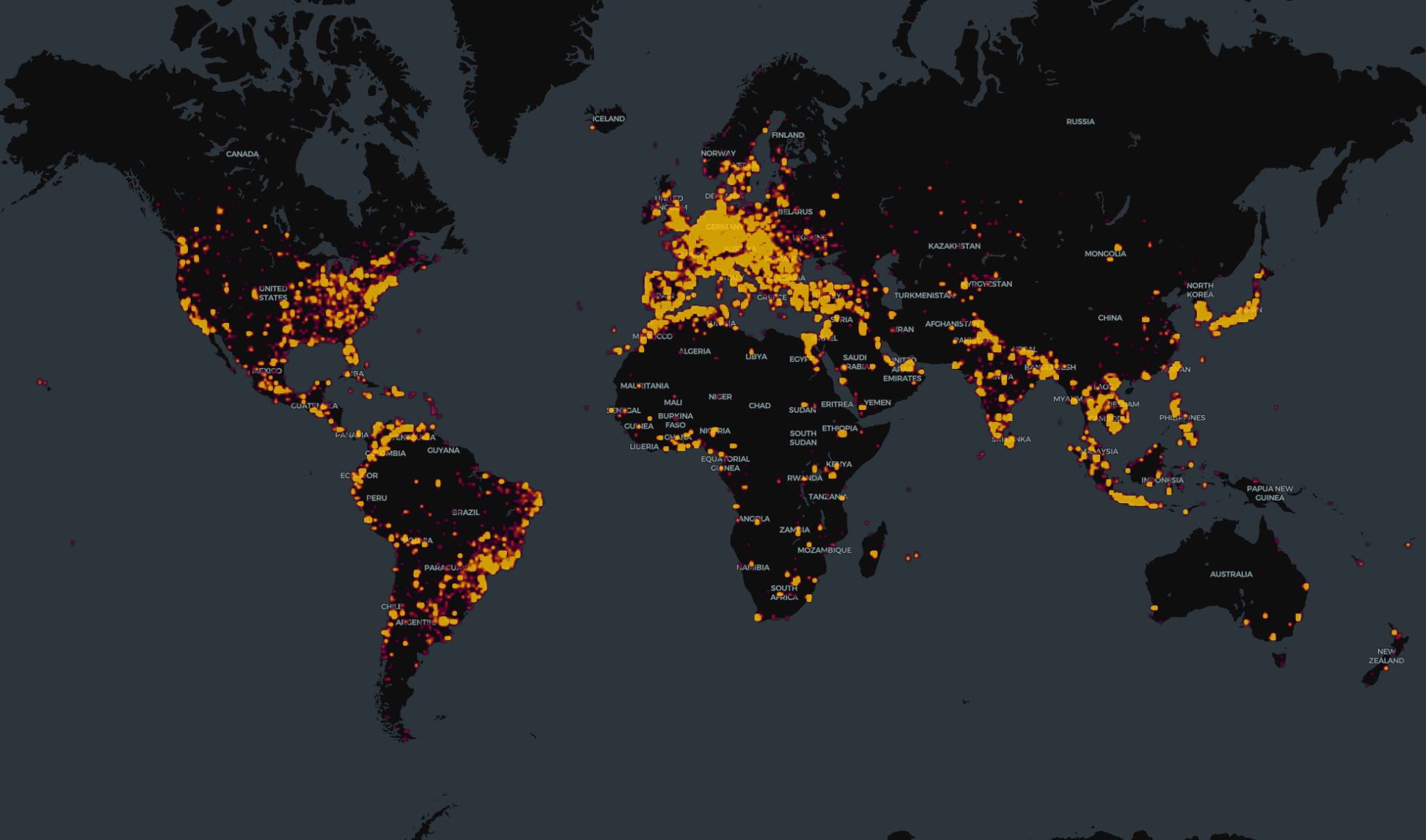
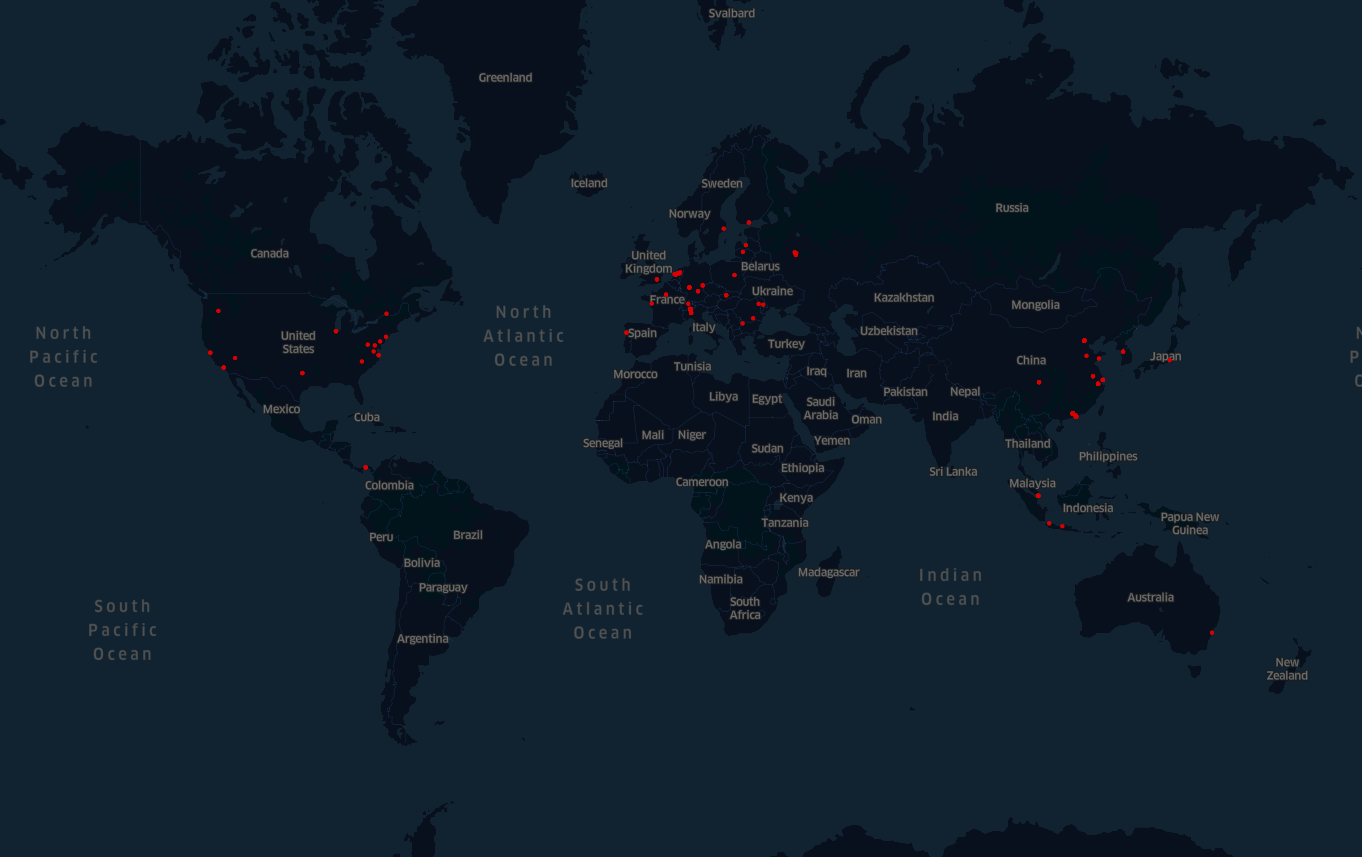
Working with a small group of trusted researchers and partners, the operation focused on collecting newly stolen credentials visible through exposed control panels while the vulnerability was present (from November 2022 through early January 2023), and then reporting stolen credentials through existing mechanisms designed for victim notification and response. At the peak of this activity, the dataset included observations across 303 distinct control servers and 70,000+ infection logs.
This did not “disrupt” Rhadamanthys or materially change the existing attacker infrastructure. The malware continued to operate. Once the flaw was fixed and operators moved to newer versions, our ability to collect this information ended. That constraint is the point: private-sector access to an opportunity is not the same as private-sector authority to act on it.
As Rhadamanthys continued to evolve, it grew in sophistication and resilience to many of the methods we used to identify its infrastructure. Visibility is always fragile.
Retrospective
This operation is best understood as a case study in “bounded action.” It did not directly disrupt infrastructure offline or remove actors from play. Instead, it provided a short-lived opportunity to reduce harm through reporting and coordination, an outcome that is often the realistic ceiling for private-sector efforts without law enforcement involvement. In contrast, Operations like Endgame, Cronos, and Tovar demonstrate what becomes possible when law enforcement, infrastructure providers, and private-sector responders can operate together under a coherent plan and legal authority.
If there is a single lesson from this Rhadamanthys operation, it is that “meaningful action” is often less about dramatic technical intervention and more about disciplined execution under constraints:
- Coordinate early so action aligns with partners who can actually move infrastructure, notify victims at scale, or preserve evidence.
- Have a theory of impact that matches how these ecosystems adapt (many threats can reconstitute infrastructure quickly after purely technical disruption).
- Align incentives so participation is sustainable—time, approvals, data-sharing constraints, and reputational risk all shape what organizations can realistically do.
The end state is not a universal prescription. It’s a more realistic mental model: private-sector responders can create leverage, but lasting disruption typically requires public-private collaboration and lawful authority.
If the Rhadamanthys story has a “win,” it’s that it clarifies the shape of the problem, and why the industry needs stronger institutions for responsible collaboration when rare opportunities like this appear.
Further Reading
Public-private partnership success story: In 2024, Censys identified nearly 400 U.S. water facilities exposed online. Through a successful partnership with the U.S. Environmental Protection Agency, over 90% of them were secured.