Executive Summary
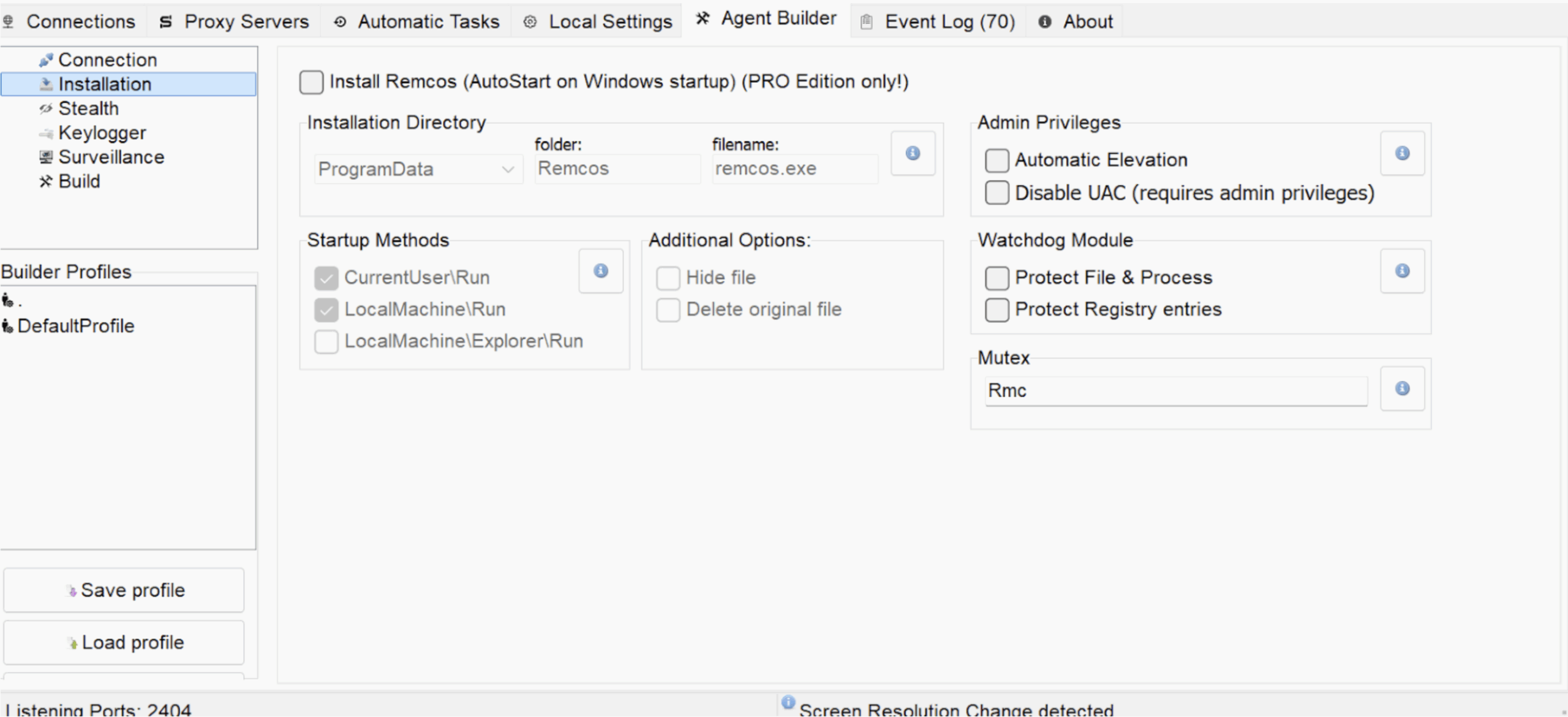
Remcos is a commercial remote access tool distributed by Breaking-Security and marketed as “Remote Administration Software.” It supports remote command execution, file transfer, screen capture, keylogging, and credential collection over an HTTP or HTTPS command-and-control (C2) channel. Public reporting places initial development in the mid-2010s. Recent versions use a modular architecture and use configurable installers that can aid persistence and evasion. The vendor offers a free tier with reduced functionality and a paid Pro edition; cracked Pro copies are observed in the wild. The company also distributes auxiliary tools framed for “security assessments” that can be repurposed in attack chains. Despite administrative positioning, Remcos capabilities are routinely used for unauthorized access and data theft.
Introduction
Remcos continues to receive updates and support, which likely contributes to ongoing adoption by a range of actors. It is delivered as an initial payload to stage follow-on tooling or additional malware aligned to campaign goals. Distribution commonly uses malspam with archive or document attachments and lures hosted on compromised sites, often staging binaries in open directories. Remcos is also deployed as a second stage by actor-specific loaders such as GuLoader and Reverse Loader, likely to reduce initial detection (Defense Evasion).
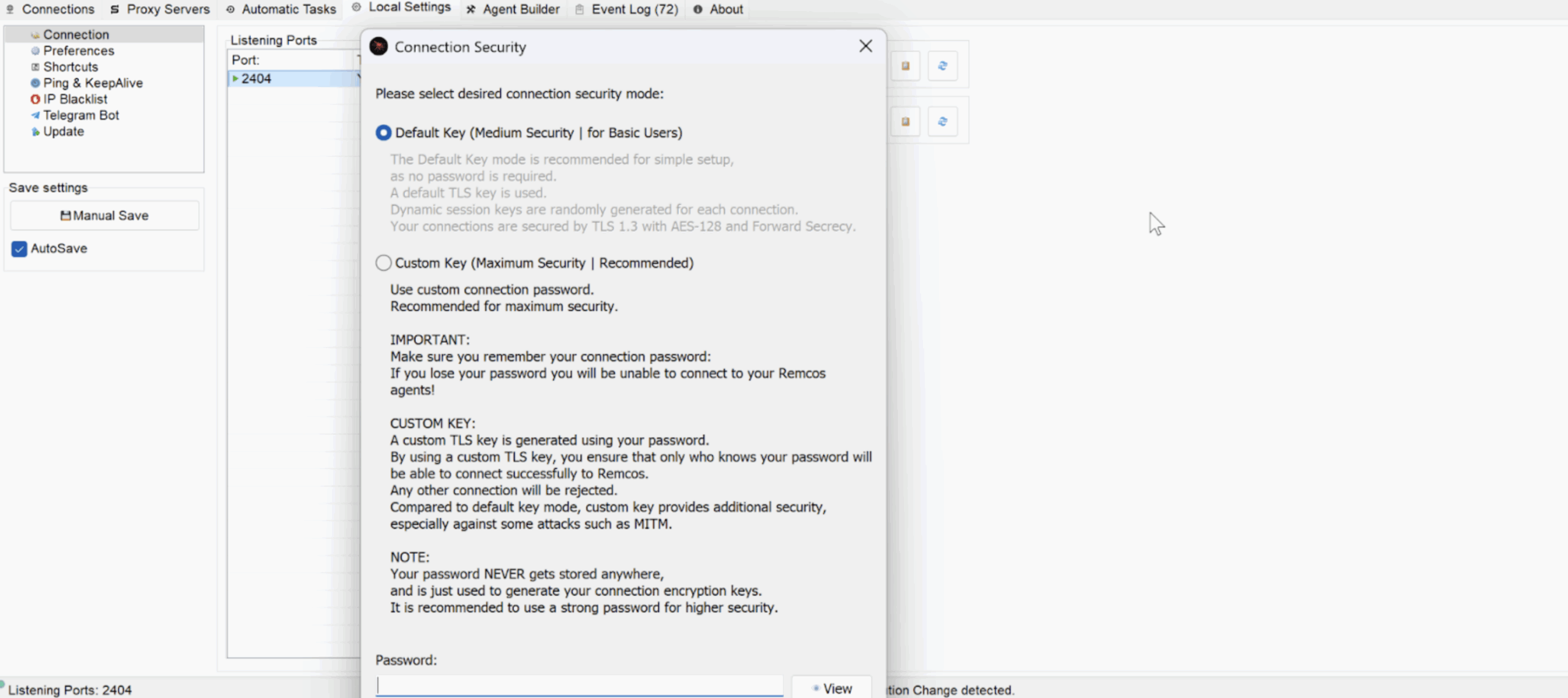
Once active, Remcos often maintains persistence via Scheduled Tasks or Run-key entries and beacons periodically to its C2 over HTTP or HTTPS, typically on ports 2404(default), 80, 443, or 8080. Operators frequently reuse predictable filenames (for example, remcos.exe) or masquerade as system binaries (for example, svchost.exe) while writing under HKCUSoftwareMicrosoftWindowsCurrentVersionRun or similar paths. Network traffic may include encoded POST bodies and atypical TLS settings that yield detectable artifacts for intrusion detection systems.
Censys Perspective
Between October 14 and November 14, 2025, Censys consistently tracked over 150 active Remcos Command and Control (C2) servers, suggesting continued utilization of inexpensive infrastructure. Most servers listened on port 2404, commonly associated with Remcos, with additional use of ports 5000, 5060, 5061, 8268, and 8808, showing deployment flexibility. A subset of hosts exposed Server Message Block (SMB) and Remote Desktop Protocol (RDP), suggesting some operators also use native Windows services for administration. Hosting concentrated in the United States, the Netherlands, and Germany, with smaller clusters in France, the United Kingdom, Turkey, and Vietnam. Providers such as COLOCROSSING, RAILNET, and CONTABO accounted for a significant share, consistent with inexpensive and lightly vetted networks.
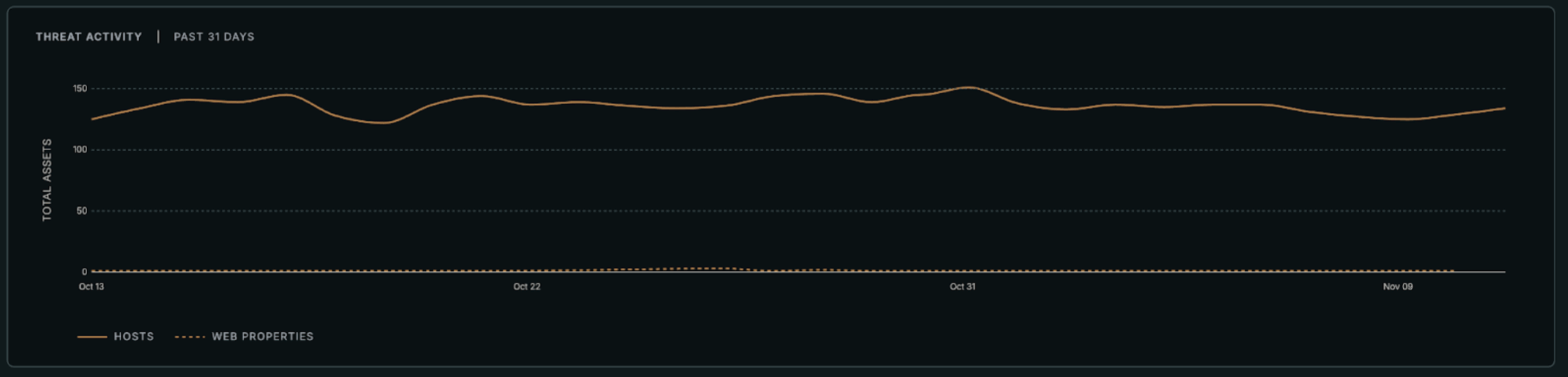

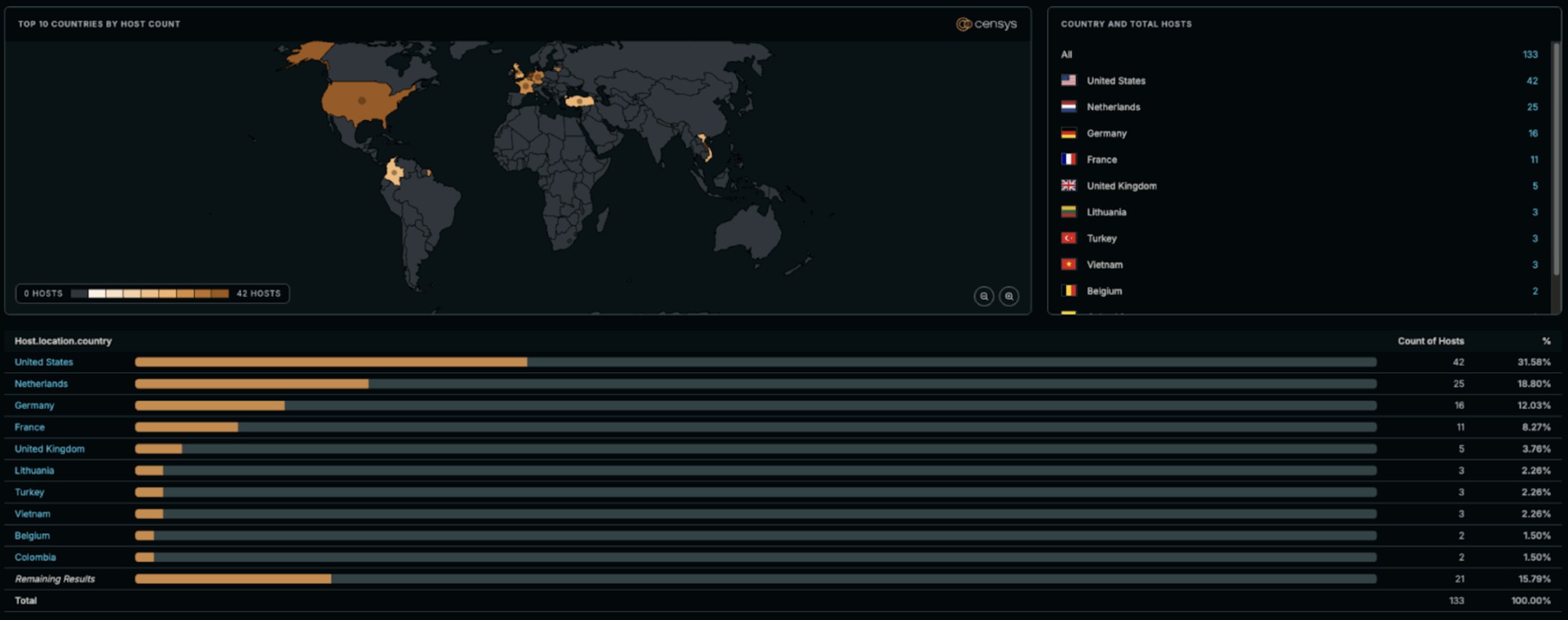

Certificate use points to simple, repeatable setups. SSL/TLS certificates are sometimes reused across multiple IPs, which implies template-based configuration and minimal obfuscation and enables cluster linkage. The consistent presence of RDP and SMB further suggests a portion of operators maintain direct control rather than fully automated deployment.
Infrastructure turnover appears mixed. Certificate and IP reuse indicates some servers persist for weeks or months, while others rotate quickly, typical for commodity remote access trojans. Growth during this window was most visible in autonomous systems linked to virtual private server resellers, indicating continued reliance on disposable infrastructure. Overall visibility looks stable with modest expansion in European hosting and gradual diversification among smaller providers.
Conclusion
Credential theft and persistent access make Remcos a priority target for network monitoring and endpoint detection. The tool’s mix of remote command execution, file transfer, and keylogging enables rapid data loss. Scheduled task and Run-key persistence keep access stable after initial compromise. HTTP and HTTPS beacons on predictable ports create repeatable points of visibility. Together these traits raise the likelihood of impact if basic controls are weak.
Leverage the Censys Threat Hunting Platform to identify and disrupt infrastructure linked to Remcos. Explore the threat regularly and alert on any outbound communications matching the resulting hosts.