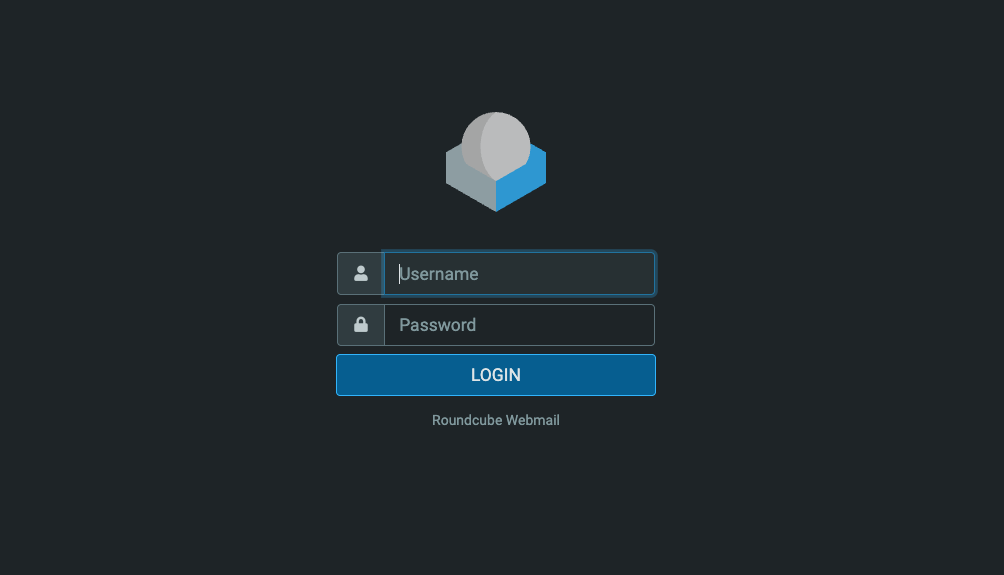
Vulnerability Description
CVE-2025-49113 is a critical vulnerability (CVSS 9.9) affecting Roundcube Webmail versions prior to 1.5.10 and 1.6.x prior to 1.6.11. It allows authenticated attackers to achieve remote code execution (RCE) due to improper input validation of the _from parameter in the program/actions/settings/upload.php endpoint, leading to PHP Object Deserialization.
Threat Activity
While there is no confirmed evidence of CVE-2025-49113 being actively exploited at the time of writing, CERT Polska has observed exploitation attempts targeting a separate Roundcube vulnerability, CVE-2024-42009, in ongoing spearphishing campaigns. Given that a public proof-of-concept (PoC) for CVE-2025-49113 is available, prompt patching is strongly advised.
| Field | Details |
|---|---|
| CVE-ID | CVE-2025-49113 – CVSS 9.9 (Critical) – assigned by MITRE |
| Vulnerability Description | Authenticated RCE due to improper input validation of the _from parameter in program/actions/settings/upload.php |
| Date of Disclosure | June 1, 2025 |
| Date Reported as Actively Exploited | N/A |
| Affected Assets | program/actions/settings/upload.php of Roundcube Webmail fails to validate _from parameter |
| Vulnerable Software Versions | Roundcube Webmail versions prior to 1.5.10 and 1.6.x prior to 1.6.11. |
| PoC Available? | Public exploit code has been published on GitHub. |
| Exploitation Status | There is no evidence that this vulnerability is being actively exploited at the time of writing. |
| Patch Status | This vulnerability has been patched in versions 1.5.10 and 1.6.11 of Roundcube Webmail. |
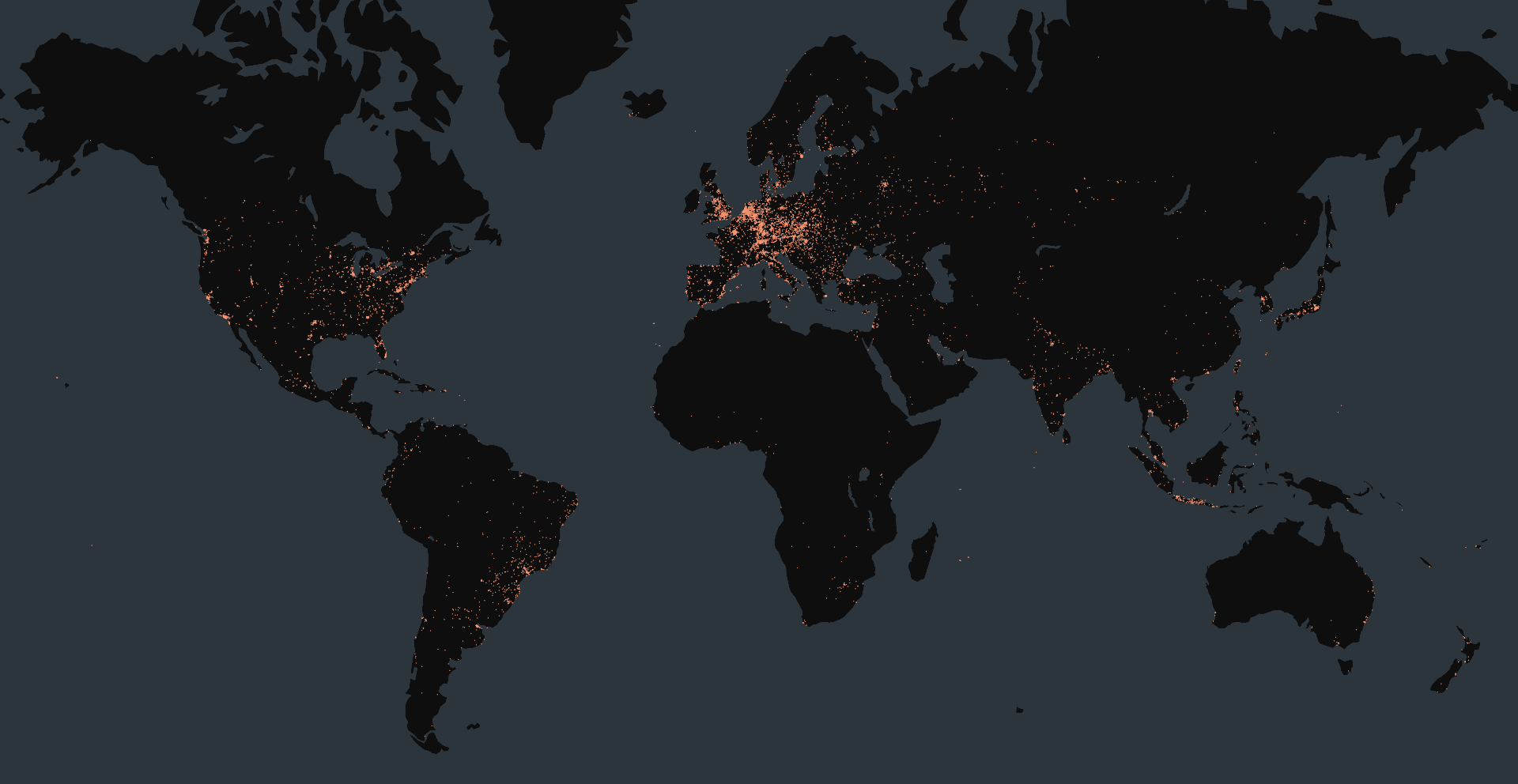
Censys Perspective
At the time of writing, Censys observed 2,473,116 exposed Roundcube Webmail instances online, nearly all of which are exposing version information. The versions in the table below were observed most frequently:
The queries below can be used to identify exposed instances of Roundcube Webmail, but they are not necessarily vulnerable to the exploit.
web.software: (vendor: "roundcube" and product: "webmail")services.software: (vendor="Roundcube" and product="Webmail")host.services.software: (vendor="Roundcube" and product="Webmail") or web_entity.instances.software: (vendor="Roundcube" and product="Webmail")The query below can be used to find instances of Roundcube Webmail that are vulnerable to the exploit. Please note that this risk was recently deployed and results may take up to 24 hours to fully propagate.
risks.name = "Vulnerable Roundcube [CVE-2025-49113]"