[UPDATE]: August 4, 2025
On July 31, 2025, Unit 42 identified a failed exploitation attempt targeting CVE-2025-53770, prompting an investigation that uncovered the deployment of 4L4MD4R ransomware, a variant of the open-source Mauri870 ransomware. In their writeup, Unit 42 noted the following:
- The loader downloads and executes the ransomware from hxxps://ice.theinnovationfactory[.]it/static/4l4md4r.exe (145.239.97[.]206)
- The ransomware encrypts files and demands 0.005 BTC, providing a contact email and Bitcoin wallet address for payment.
- The ransomware generates two files: DECRYPTION_INSTRUCTIONS.html (ransom note) and ENCRYPTED_LIST.html (a list of encrypted files).
On July 23, 2025, Microsoft updated the Indicators of Compromise (IoCs), Attribution, Mitigation & Protection Guidance, Detections, and Hunting sections of their blog. This update followed the discovery of Warlock ransomware deployment, observed through continued monitoring of exploitation activity by Storm-2603, a group Microsoft tracks and assesses, with moderate confidence, to be a China-based threat actor.
As of August 3, 2025, we observed 9,665 on-premises Microsoft SharePoint devices exposed to the internet. While these devices are exposed, we cannot confirm their vulnerability status because version information is unavailable. Notably, nearly half (~47%) of these exposures are associated with network infrastructure owned by Microsoft.
Vulnerability Description
CVE-2025-53770 (CVSS 9.8), part of an exploit chain dubbed “ToolShell”, enables unauthenticated remote code execution on vulnerable on-premises Microsoft SharePoint servers. The chain leverages two critical steps: a vulnerability in the /_layouts/15/ToolPane.aspx endpoint allows threat actors to write malicious files directly to the server, then extract sensitive cryptographic keys from SharePoint configuration files. With those keys, they can generate legitimate-looking, signed payloads to gain full control of the server.
This CVE, along with CVE-2025-53771, are considered variants on the earlier vulnerabilities CVE-2025-49704 and CVE-2025-49706, which were demonstrated during Pwn2Own Berlin in May 2025 as part of a working unauthenticated exploit chain.
Threat Activity
On July 18, 2025, a few days after a PoC of this exploit was posted on X, researchers at Eye Security, noticed a malicious .aspx payload linked to a suspicious process chain flagged in an endpoint alert on a legacy on-premises SharePoint server. ToolShell activity was subsequently confirmed by multiple security researchers. CVE-2025-53770 was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog on July 20, 2025, further confirming the active exploitation of this issue.
Attackers have been observed using ToolShell to gain unauthenticated access to internet-facing, on-premises SharePoint instances, upload web shells, and deploy PowerShell payloads. These attacks are fully network-based and require no user interaction – just a request to the /_layouts/15/ToolPane.aspx endpoint. Note that this only affects on-premises SharePoint servers – SharePoint Online in Microsoft 365 is not impacted.
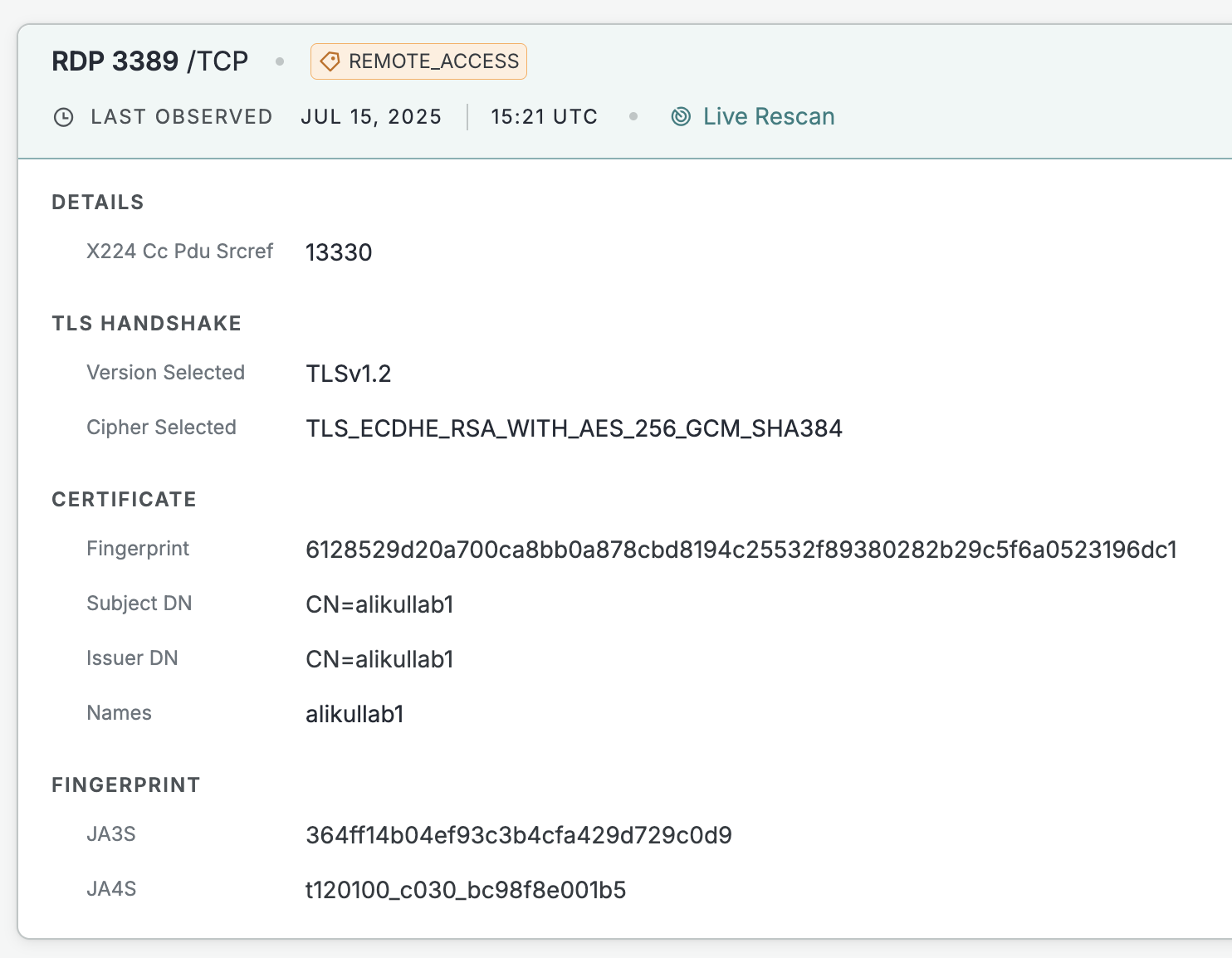
GreyNoise first observed a request to this endpoint on one of its sensors on July 16 from the IP 172.174.82[.]132, part of Azure’s cloud ranges, which it labeled as “suspicious”. The user-agent strings don’t match any known malicious indicators and it’s unclear whether this activity was benign or related to the broader exploitation that began on July 18. Our scans show that the same host briefly exposed an RDP service on TCP/3389 using an untrusted certificate named “alikullab1”. The service appeared on July 15 around 15:21 UTC and disappeared on July 18. As of the time of writing, the host is no longer exposing any services and there are no other hosts presenting that certificate.
In addition to the activity observed in GreyNoise, Eye Security and Palo Alto’s Unit42 have observed malicious activity originating from the following IPs:
- “107.191.58[.]76 – first succesful exploit wave US-based source IP responsible for active exploitation on 18th of July around 18:06 UTC deploying spinstall0.aspx
- 104.238.159[.]149 – second exploit wave US-based source IP responsible for active exploitation on 19th of July around 07:28 UTC
- 96.9.125[.]147 – shared by PaloAlto Unit42, initial (testing) exploit wave US-based source IP responsible for active exploitation (probably) on 17th of July around 12:51 UTC, but it not succeeded at our customer for some reason
- 45.77.155[.]170 – third exploit wave US-based source IP responsible for active exploitation on 21th of July around 19:03 UTC”
Source: Eye Security https://research.eye.security/sharepoint-under-siege/
Organizations should monitor for suspicious POST requests to /_layouts/15/ToolPane.aspx, unexpected .aspx files on disk, and activity originating from the known malicious IPs listed above. It’s also recommended to rotate your ASP.NET MachineKeys ASAP as a precaution. For the most up-to-date information on IoCs and remediation, refer to published guidance from both Microsoft and CISA.
| Field | Details |
|---|---|
| CVE-ID | CVE-2025-53770 – CVSS 9.8 (Critical) – Assigned by Microsoft |
| Vulnerability Description | An unauthenticated attacker can achieve remote code execution (RCE) on SharePoint Servers due to deserialization of untrusted data. |
| Date of Disclosure | July 18, 2025 |
| Date Reported Actively Exploited | July 18, 2025 |
| Affected Assets | On-premises SharePoint Servers |
| Vulnerable Software Versions | SharePoint Server Subscription Edition < 16.0.18526.20508SharePoint Server 2019 < 16.0.10417.20037SharePoint Enterprise Server 2016 (All versions) |
| PoC Available? | A PoC has been published on GitHub |
| Exploitation Status | Multiple sources have reported observing mass exploitation of this issue targeting on-premises SharePoint servers. It was added to CISA KEV on July 20, 2025. Earliest signs of successful exploitation activity date to July 18, 2025 when researchers at Eye Security identified the malicious .aspx payload in a customer environment. |
| Patch Status | Microsoft has released security updates for customers using SharePoint Subscription Edition and SharePoint 2019. |
Censys Perspective
At the time of writing, Censys observed 9,762 on-premises SharePoint servers online. While we do observe version information for these devices, we cannot determine from our data whether the necessary patches have been successfully applied to these instances and therefore cannot infer vulnerability status. The queries below can help identify any SharePoint devices, regardless of vulnerability status.
host.services.software: (vendor: "microsoft" and product: "sharepoint")host.services.software: (vendor="Microsoft" and product="SharePoint")services.software: (vendor="Microsoft" and product="SharePoint")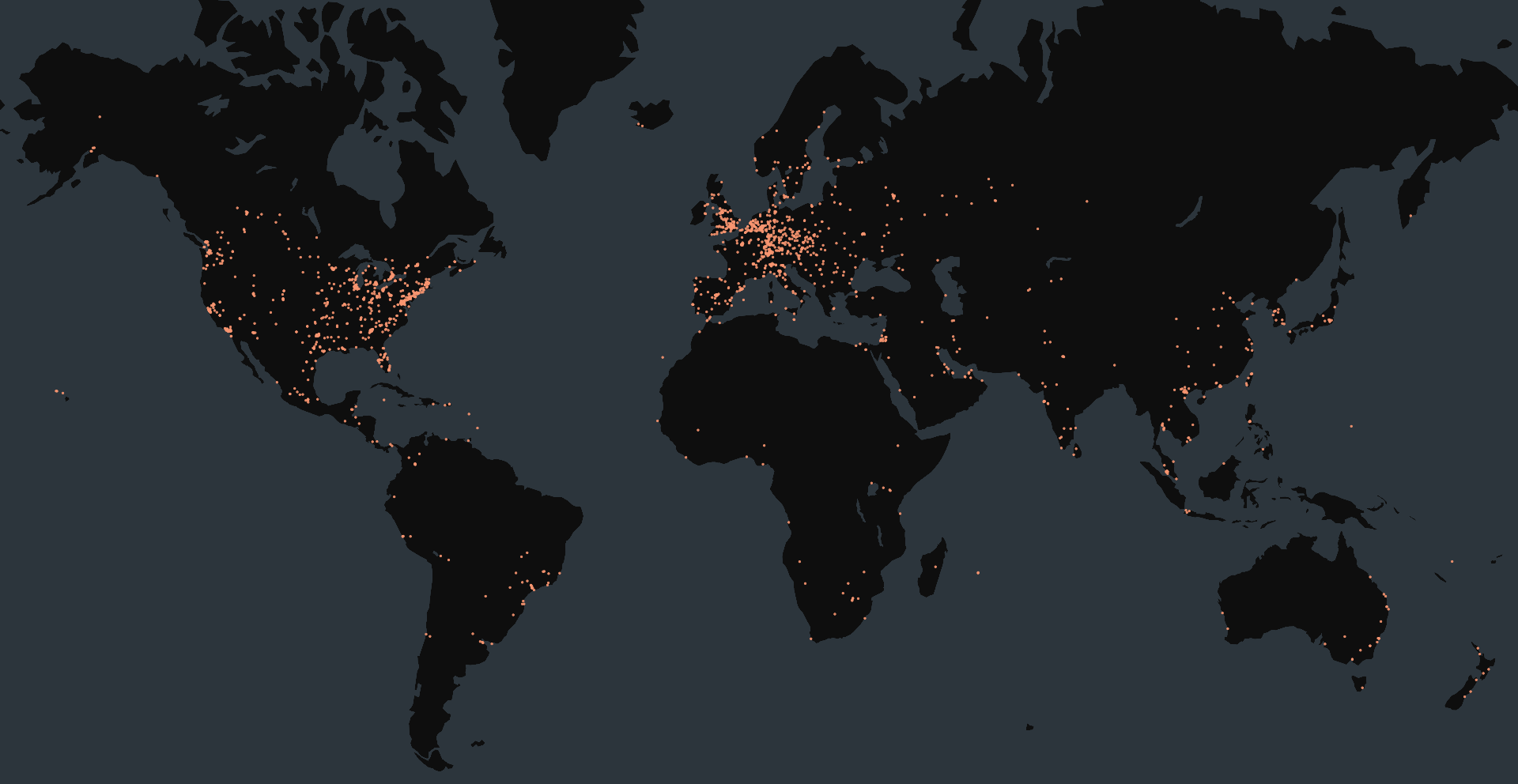
References
- CVE-2025-53770 NVD Advisory
- CVE-2025-53771 NVD Advisory
- CVE-2025-49704 NVD Advisory
- CVE-2025-49706 NVD Advisory
- Microsoft SharePoint Server Remote Code Execution Vulnerability
- CVE-2025-53770 PoC
- Microsoft Releases Guidance on Exploitation of SharePoint Vulnerability (CVE-2025-53770)
- SharePoint 0-day uncovered (CVE-2025-53770)
- Active Exploitation of Microsoft SharePoint Vulnerabilities: Threat Brief (Updated July 31)





