Vulnerability Description
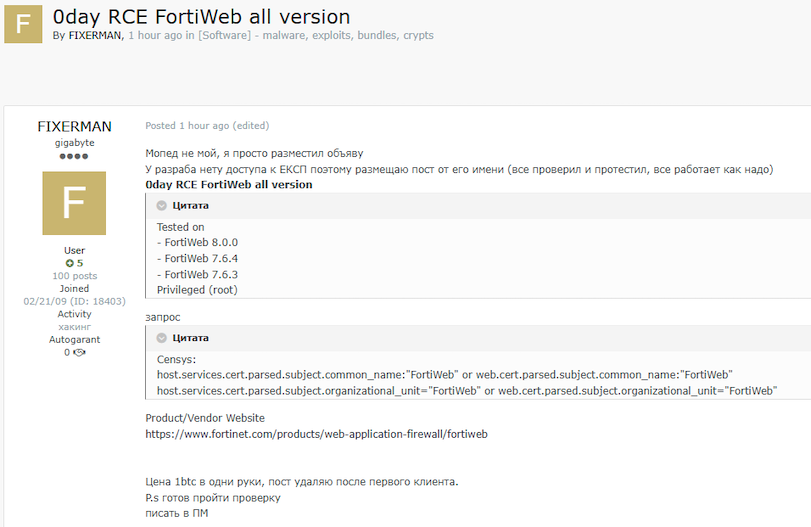
A vulnerability in Fortinet’s FortiWeb WAF allows unauthenticated attackers to create administrator accounts and gain full control of the device. Active exploitation has been observed in the wild by multiple sources since early October 2025, with attackers abusing the flaw to access both the web management interface and WebSocket CLI to make configuration changes and achieve remote command execution. Widespread scanning of exposed FortiWeb systems has been detected, and attackers have been seen creating rogue accounts such as “hax0r” on affected instances.
Timeline
- October 6, 2025 – Security firm Defused published a PoC and noted exploitation attempts on their honeypots. No CVE was assigned at this time, and there was no response from Fortinet.
- November 13, 2025 – Rapid7 published more exploitation attempts that they observed. Still no CVE and no official vendor guidance.
- November 14 – Fortinet publishes some official vendor guidance and assigns CVE-2025-64446 to this issue.
| Field | Description |
| CVE-ID | CVE-2025-64446 — CVSS 9.1 — assigned by Fortinet |
| Vulnerability Description | An unauthenticated access vulnerability in Fortinet’s FortiWeb Web Application Firewall (WAF) allows remote attackers to create administrator accounts and execute arbitrary commands.Enables full administrative control over the web management panel and WebSocket CLI without prior authentication. |
| Date of Disclosure | October 6, 2025 |
| Affected Assets | FortiWeb |
| Vulnerable Software Versions | FortiWeb ≤ 8.0.1 confirmed vulnerableFortiWeb 8.0.2 (released October 2025) appears to mitigate the issue; exploitation attempts return 403 Forbidden, but it’s not clear if this is just a coincidence or an effective silent patch. |
| PoC Available? | Yes, first published by Defused on X on October 6, 2025 |
| Exploitation Status | Actively Exploited – this vulnerability has been observed to be exploited in the wild since at least early October 2025 according to honeypot data by Defused and Rapid7 and according to the vendor advisory from Fortinet. |
| Patch Status | Seemingly, version 8.0.2 is not susceptible to this (the public PoC fails against it), though this may be a coincidence instead of evidence of a full patch. WatchTowr Labs has published a tool for checking whether a FortiWeb instance is vulnerable. |
Censys Perspective
The following queries can be used to identify exposed instances of Fortinet FortiWeb. Note that not all of these are necessarily vulnerable, as specific version information is not available.
((web.cert.parsed.subject.common_name: “FortiWeb” or web.cert.parsed.subject.organizational_unit: “FortiWeb”) and (web.software.vendor: “fortinet”)) and not web.labels.value: “HONEYPOT”
web_entity.instances.software.vendor:”fortinet” and (web_entity.instances.tls.certificate.parsed.issuer.common_name: “FortiWeb” or web_entity.instances.tls.certificate.parsed.issuer.organizational_unit: “FortiWeb”) and not web_entity.instances.labels={`honeypot`, `tarpit`}
services.software.vendor:”fortinet” and services: (tls.certificate.parsed.subject.common_name: “FortiWeb” or tls.certificate.parsed.subject.organizational_unit: “FortiWeb”) and not labels={`honeypot`, `tarpit`}
References
- https://x.com/DefusedCyber/status/1975242250373517373?s=20
- https://cybersecuritynews.com/fortinet-fortiweb-vulnerability/
- https://www.rapid7.com/blog/post/etr-critical-vulnerability-in-fortinet-fortiweb-exploited-in-the-wild/
- https://labs.watchtowr.com/when-the-impersonation-function-gets-used-to-impersonate-users-fortinet-fortiweb-auth-bypass/





