Vulnerability Description
CVE-2025-68613 is a critical (CVSS 9.9) remote code execution (RCE) vulnerability that allows an authenticated attacker to execute arbitrary code with the privileges of the n8n process. Successful exploitation may lead to full compromise of the affected instance, including unauthorized access to sensitive data, modification of workflows, and execution of system-level operations.
The vulnerability exists in n8n’s workflow expression evaluation system. Under certain conditions, expressions supplied by authenticated users during workflow configuration may be evaluated in an execution context that is not sufficiently isolated from the underlying runtime. This allows authenticated attackers to execute arbitrary code.
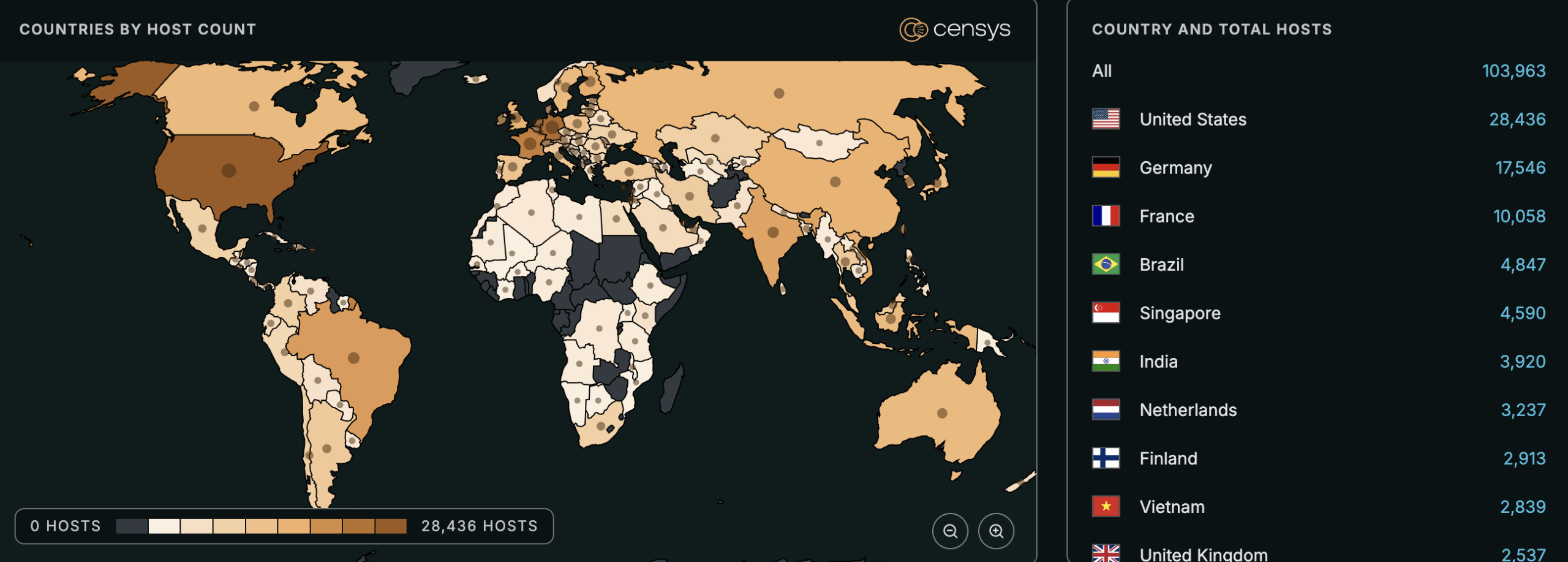
See the full breakdown by country in Censys Platform →
| Field | Description |
| CVE-ID | CVE-2025-68613 — CVSS 9.9 — assigned by GitHub |
| Vulnerability Description | A critical RCE vulnerability in n8n allows authenticated attackers to execute arbitrary code with the privileges of the n8n process. Successful exploitation may lead to full compromise of the affected instance, including unauthorized access to sensitive data, modification of workflows, and execution of system-level operations. |
| Date of Disclosure | December 19, 2025 |
| Affected Assets | n8n |
| Vulnerable Software Versions | Starting with 0.211.0 and prior to 1.120.4Starting with 0.211.0 and prior to 1.121.1Starting with 0.211.0 and prior to 1.122.0 |
| PoC Available? | Yes, published by SecureLayer7 |
| Exploitation Status | No known exploitation at time of writing. |
| Patch Status | Fixed in patched versions: 1.120.41.121.11.122.0Upgrade to patched versions immediately. If upgrading is not immediately possible:Limit workflow creation and editing permissions to fully trusted users only.Deploy n8n in a hardened environment with restricted operating system privileges and network accessNote: These workarounds do not fully eliminate the risk and should only be used as short-term measures. |
Censys Perspective
At time of writing, Censys observes 103,476 potentially vulnerable instances, trackable with the following queries:
host.services.software.product: "n8n"risks.name="Vulnerable n8n [CVE-2025-68613]" or host.services.software.product: "n8n" or web_entity.instances.software.product: "n8n"services.software.product: "n8n"




