Have you ever prompted an LLM without enough context? You ask for Apple security and end up with fruit storage tips.
It works the same way in the SOC: the output is only as good as the inputs you give it.
That’s why “AI SOC” and SOC modernization efforts stall when the underlying Internet context is thin, stale, or inconsistent. Copilots can summarize alerts, correlate notes, draft incident reports, and suggest next steps. BUT – they can’t conjure ground truth about what’s actually online and how dangerous it is.
Security Operations Centers must be able to bridge those gaps to understand the ground truth of their data. This post is about “AI SOC done responsibly:” modernizing investigations and automation by first establishing a ground-truth Internet iIntelligence layer, so every SOC workflow starts from reality.
The AI SOC Reality Check: Automation Can’t Fix Bad Inputs
Elastic Security Labs recently illustrated how their SIEM’s new AI commands enable detection engineers to build more intelligently and quickly. This leverages, as they call it, the “LLM-as-a-judge” technique, “where LLMs evaluate structured inputs against criteria rather than generate open-ended content.”
“The pattern works well in evaluation pipelines, code review automation, and content moderation,” writes Mika Ayenson, Ph.D, Team Lead at Elastic. “For detection, it lets us tap into the LLM’s knowledge of attack patterns, enterprise tooling, and security context to make triage decisions that would otherwise require analyst judgment or extensive exception lists.”
Their example prompt looks like:
eval instructions = " Analyze if these alerts form an attack chain (TP), are benign/false
positives (FP), or need investigation (SUSPICIOUS). Consider: suspicious domains, encoded
payloads, download-and-execute patterns, recon followed by exploitation, testing frameworks
in parent processes. Do NOT assume benign intent based on keywords such as: test, testing,
dev, admin, sysadmin, debug, lab, poc, example, internal, script, automation. Structure the
utput as follows: verdict=<verdict> confidence=<score> summary=<short reason max 50 words>
without any other response statements on a single line."Then they pass in aggregated telemetry and chains of alerts.
If your SIEM is fed a patchwork of point tools, inconsistent enrichment, and yesterday’s snapshots of “what’s online,” it will confidently produce explanations that are only as good as the underlying data.
SOC modernization efforts succeed when they modernize the boring layer first: reliable, repeatable, evidence-based context that improves every downstream workflow — human and automated.
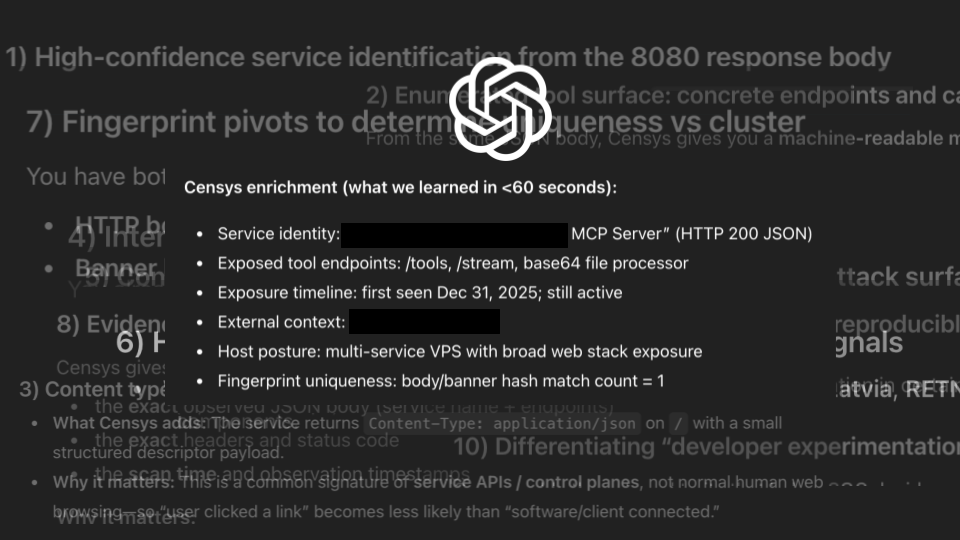
Censys provides that missing layer: reams of first-party Internet intelligence (rich context, history, and metadata across hosts, services, certificates, and domains) paired with Censys ARC-developed enrichment labels (threats, vulnerabilities, and more). And LLMs are excellent at chewing it up: turning dense external reality into clearer summaries, faster triage, tighter incident narratives, and more consistent decisions across analysts and shifts.
If Censys data were part of the Elastic SIEM alert chain above (via enrichment integrations), the LLM-as-a-judge would see improved accuracy. Full stop.

Why SOC Enrichment Breaks Without a Source of Record
Most SOC enrichment today is assembled from:
- A base layer of a SIEM alert with partial context.
- A TI feed with indicators (maybe stale, maybe incomplete).
- A reputation/noise tool to guess whether it’s background activity.
- A few manual pivots across tabs and CLI tools.
- …And a lot of analyst judgment under the gun?
That workflow is survivable (well, arguably), but it doesn’t scale. Especially in distributed SOCs where consistency matters across analysts and shifts.
AI can help reduce the toil of summarizing and stitching, but it can’t reliably compensate for:
- Incomplete outside-in visibility.
- Lack of historical “what changed, when.”
- Raw evidence separated from “what it means.”
- Contradictory results across tools.
SOC modernization needs a ground-truth layer so enrichment is consistent, defensible, and automation-ready.
Censys Brings Ground Truth That Helps Your AI SOC Succeed
Censys Platform is the ground-truth Internet intelligence layer your AI workflows need: first-party Internet visibility with freshness and history, plus Censys ARC-developed context tied directly to hosts, services, certificates, and domains.
1) First-party Internet data: better inputs → better AI outputs (not stitched aggregation)
Censys scans and maintains its own Internet Map. That matters because “stitched” data often comes with uneven coverage, inconsistent identifiers, and hidden caveats that only show up mid-incident — exactly when an AI copilot is most likely to overfit or hallucinate confidence.
2) Freshness AND history: stop narrating “today” when the incident happened last week
This is where AI can either shine or mislead. Without history, copilots produce clean-sounding narratives that accidentally describe the present, not the incident window.
With freshness and history, LLMs can generate timelines that match reality: when a service appeared, when a cert rotated, when a domain relationship changed, and what that means for scoping and containment.

3) Raw signals + Censys ARC enrichment labels: the right level of abstraction for every prompt
Advanced practitioners want raw evidence: services, banners, certificates, domains, infrastructure relationships.
Others need fast answers: threat labels, vulnerability intelligence, campaign/C2 context, and other enrichment signals that speed up triage.
Censys combines both. It provides raw first-party observations plus security-ready, research-developed enrichment — all tied to the exact asset being investigated.
That’s the unlock for AI SOC: your assistant can summarize, correlate, and recommend actions based on evidence that’s already joined, rather than trying to stitch meaning together from scattered sources.
4) Integrations that take AI from “chat” to “workflow”
SOC modernization isn’t “buy a new console.” It’s making your SIEM, SOAR, TIP, EDR, and internal tools produce better outcomes. AI must operate inside those workflows, not alongside them.
Censys is designed to enrich where the SOC already works so context is consistent, playbooks are repeatable, and your copilot can:
- draft enrichment summaries directly in tickets
- standardize analyst handoffs across shifts
- trigger the right next-step automation with fewer false assumptions
Three SOC Playbooks (AI SOC Edition)
Frontline Triage (SOC L1/L2): “What is this alert really telling me?”
Trigger: SIEM alert contains IP/domain/cert hash; the message is thin, noisy, or generic.
Goal: Determine “benign vs suspicious,” confirm what’s actually exposed, and decide whether to escalate.
Censys adds:
- What the host is actually serving right now (services/ports/banners).
- Related certificates and domains (pivot points that reveal adjacent infrastructure).
- Vulnerability context relevant to exposed services.
- Threat labels/detections attached to the entity.
Why it helps your AI: Your LLM copilot can summarize the situation accurately because the evidence is present and consistent, which reduces false confidence.
Incident Response: “Does the timeline change scoping?”
Trigger: “Was this exposed last week?” / “Did the cert rotate after compromise?” / “Is this infrastructure new?”
Goal: Establish a defensible timeline and scope based on real change over time.
Censys adds:
- Historical observations for services, ports, certs, and even threats.
- Timeline views and change over time (appearance/disappearance, rotations, new associations).
Why it helps your AI: AI can draft a coherent incident narrative and action plan when it has time-bounded ground truth instead of just a present-day snapshot.
Threat Hunting / Detection Engineering: “Show me the pattern, not just the IOC.”
Trigger: One clue (patterned hostname, shared cert, exposed admin panel, specific service fingerprint).
Goal: Expand from a single indicator to related infrastructure clusters and build repeatable detections.
Censys adds:
- Pivots across certs, hosts, domains, and services.
- Threat and vulnerability labels curated by Censys ARC to track active patterns and publish findings.
Why it helps your AI: Your assistant can generate better hunting hypotheses and detection logic when infrastructure relationships and enrichment are already joined and queryable.
SOC Modernization Outcome: Make AI Useful by Standardizing the Inputs
AI doesn’t eliminate the hard parts of security operations. It compresses them!
If your Internet context is fragmented across point tools and inconsistent feeds, your copilot will simply generate faster narratives on top of hallucinations. That’s how you end up with confident write-ups, brittle playbooks, and the same escalations you wanted to avoid — just at higher speed.
The fix isn’t “more prompts.” It’s a shared source of record for external reality: what’s online, what it’s connected to, what it means, and how it has changed over time. When that ground truth is consistent and automation-ready, LLMs and agents become genuinely valuable: they can summarize richer evidence, correlate across entities, draft tighter incident timelines, and help analysts converge on decisions with fewer pivots and contradictions.
That’s where Censys fits. Not as your SIEM or EDR, but as the Internet context foundation they can reliably call. The data layer that binds your humans, playbooks, and AI assistants.
Bring AI into your SOC. Just don’t feed it guesswork.
Request a demo to see how Censys strengthens AI SOC workflows with first-party Internet visibility, including our own AI features and integrations.