Executive Summary
ResidentBat is an Android spyware implant used by the Belarusian KGB for surveillance operations against journalists and civil society. Once installed (via physical access and ADB sideloading, not via the C2), it provides operators with access to call logs, microphone recordings, SMS, encrypted messenger traffic, screen captures, and locally stored files. The malware was discovered by Reporters Without Borders (RSF) and RESIDENT.NGO in December 2025; code analysis suggests development dates back to at least 2021.
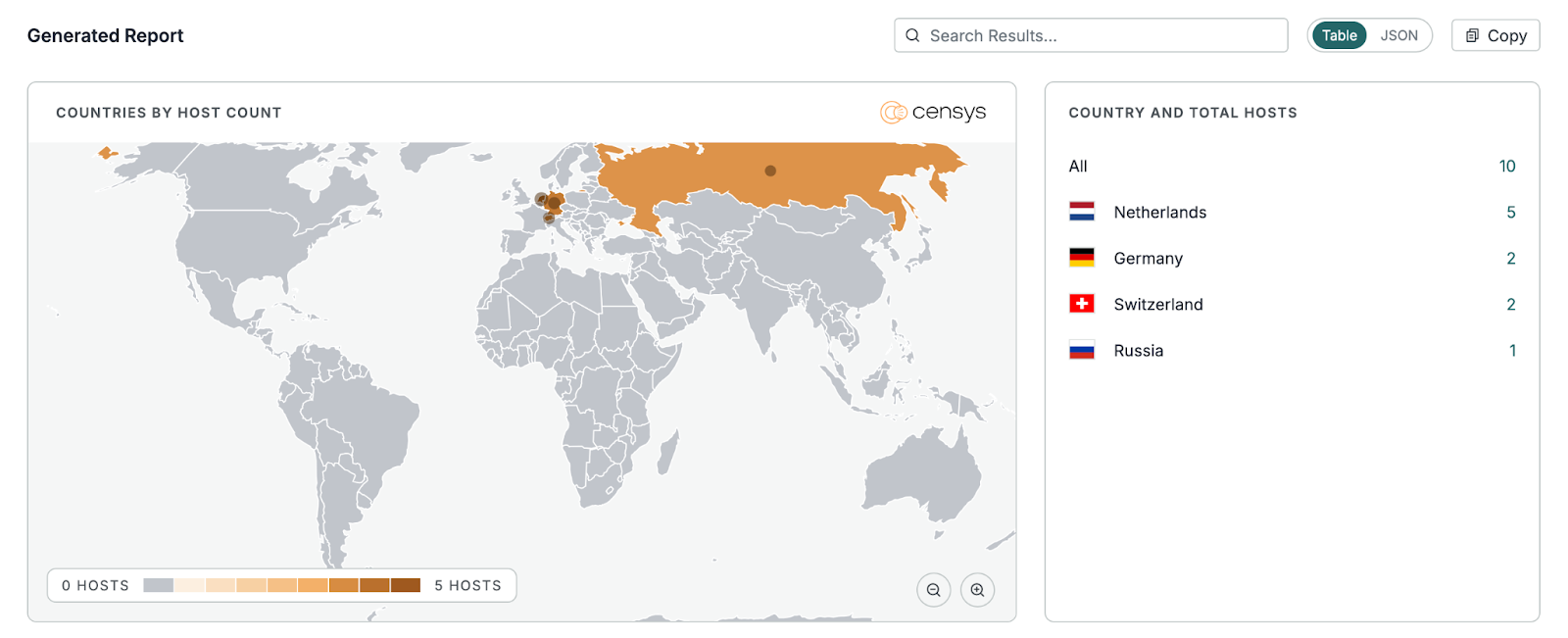
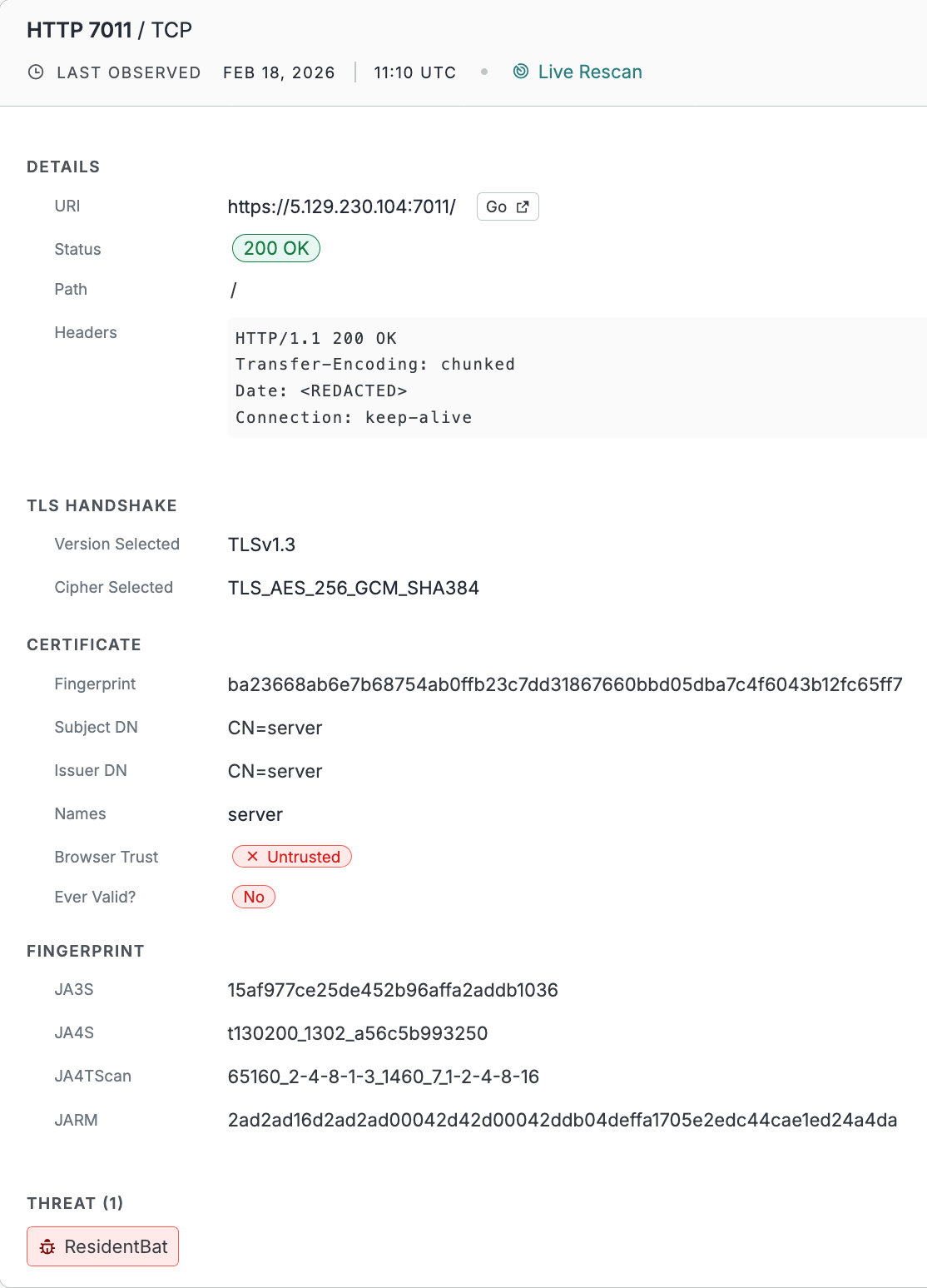
C2 servers communicate over HTTPS with a distinctive fingerprint: self-signed certificates with CN=server and a consistent TLS/HTTP banner hash. The Censys Threat Module (Threat ID: THREAT-240) identifies these hosts automatically; as of February 2026, ResidentBat-associated infrastructure is concentrated in Europe and Russia: Netherlands (5), Germany (2), Switzerland (2), and Russia (1) in a recent Platform view, using a narrow port range (7000-7257) for control traffic.
ResidentBat gives operators long-lived surveillance and remote device control, including remote wipe via DevicePolicyManager.wipeData. That makes it a serious threat for journalists and others at risk from Belarus-related targeting.

Background
ResidentBat was first publicly documented in December 2025 in a joint report by Reporters Without Borders (RSF) and RESIDENT.NGO (report PDF). The report attributes the tool to the Belarusian KGB (State Security Committee) and describes its use against journalists and civil society. Analysis of the malware’s codebase indicates development likely began at least as early as 2021.
Distribution model: ResidentBat is not distributed via the C2. Installation requires:
- Physical access to the target device
- ADB (Android Debug Bridge) sideloading of the APK
- Manual granting of permissions by the attacker
- Google Play Protect disabled by the attacker
The C2 is used only for receiving exfiltrated data, sending commands and updates, and configuration management. This “hands-on” deployment model limits scale but enables highly targeted, persistent surveillance.
Capabilities
Once installed, ResidentBat provides operators with:
- Exfiltration of communications: SMS, call logs, and access to encrypted messenger data
- Microphone and screen capture: Real-time or on-demand recording and screenshots
- File access: Exfiltration of files stored on the device
- Remote commands: Tasking and configuration pushed from the C2
- Remote wipe: Ability to trigger DevicePolicyManager.wipeData to erase the device
- Device status queries: Checking device state and compliance with operator-defined policies
Configuration is delivered via JSON and includes parameters such as server address (sars), upload period (spd), and an “upload data ASAP” flag (asp).
Technical Characteristics
ResidentBat C2 servers show consistent traits you can use for detection at internet scale:
| Characteristic | Detail |
| Protocol | HTTPS (TLS) |
| Port range | 7000-7257 (control ports); some endpoints also use 4022 |
| Certificate | Self-signed, CN=server, typically 3-year validity |
| Banner fingerprint | banner_hash_sha256: 6f6676d369e99d61ce152e1e2b2eb6f5e26a4331f4008b5d6fe567edefdbeaca |
C2 server hardening: Active probing of exposed C2s shows a catch-all 200 response pattern: all HTTP paths return 200 OK with an empty body, and various auth headers and POST bodies produce no visible change. A static or fake Date header (e.g. Tue, 06 Jan 2026 01:00:00 GMT) has been observed, suggesting anti-forensics and minimal fingerprintability beyond TLS. The C2 likely relies on client certificate authentication (embedded in the APK), a proprietary or non-REST protocol, and server-side device allowlisting.
Certificate clustering: Multiple endpoints can share the same certificate; across probed infrastructure, 5 distinct certificate SHA-256 fingerprints were observed, with some certs reused across two or more IP:port endpoints. This supports both detection (consistent CN=server, self-signed) and clustering of related infrastructure.
Operational Context
ResidentBat targets journalists and activists, not mass compromise. Physical access and ADB mean devices have to be taken briefly (at borders, during arrests, or via supply-chain interference). Infrastructure sits in European and Russian hosting (AS29182 RU-JSCIOT, TWC-EU, and other VPS providers). Censys lets you map and track this infrastructure without malware samples.
Censys’s Perspective
The Censys Platform and Threat Module let you discover and track ResidentBat C2 infrastructure. Threat Hunting customers can query by threat name or by the fingerprint:
Threat Module (recommended):
host.services.threats.name = "ResidentBat"The Threat Module tags hosts and services that match ResidentBat, so you can explore by country, ASN, and port without building the fingerprint yourself. Explore ResidentBat (THREAT-240) in the Platform.
Manual fingerprint (Search):
For custom alerts or historical analysis, the same logic can be expressed as:
host.services: (
cert.parsed.subject_dn = "CN=server" and
banner_hash_sha256 = "6f6676d369e99d61ce152e1e2b2eb6f5e26a4331f4008b5d6fe567edefdbeaca"
)Scale and infrastructure (February 2026):
- Host count: A recent Platform view shows 10 ResidentBat hosts by country (see figure below). Host count may vary by scan time; the Threat Module keeps results updated as Censys rescans the internet.
- Geography: Infrastructure is concentrated in the Netherlands (5 hosts), Germany (2), Switzerland (2), and Russia (1) in the mapped view. Full export data shows additional concentration in Russian ASNs (e.g. AS29182 RU-JSCIOT), with Netherlands, Switzerland, and Germany also represented, consistent with VPS/datacenter locations.
- ASN: AS29182 (RU-JSCIOT) is a dominant autonomous system; AS210976 (TWC-EU), AS44812, AS51395, AS44051, and others also appear.
- Ports: C2 services cluster in the 7000-7257 range (e.g. 7001, 7005, 7011, 7015, 7025, 7251-7257), with some endpoints on 4022; SSH (port 22) is commonly co-hosted on the same IPs.
Open any host in the Platform to see service details: TLS version, certificate (e.g. CN=server, untrusted), JA3S/JA4S/JARM fingerprints, and the ResidentBat threat label, as in the host example below.
Notable Findings
- C2 hardening reduces HTTP-level fingerprinting: Catch-all 200 responses and empty bodies mean TLS certificate and banner hashes are the main identifiers for discovery and tracking, not HTTP paths or response content.
- Certificate reuse helps clustering: The same certificate often appears on multiple ports or IPs, so you can pivot from one known endpoint to related infrastructure.
- APK hashes for sample correlation: The RSF report publishes SHA-256 hashes of ResidentBat APK samples; these can be used in VirusTotal, MalwareBazaar, or with researchers (e.g. RSF Digital Security Lab, Amnesty Security Lab) to correlate new samples with known C2s.
Conclusion (Implications for Defense)
ResidentBat combines communications and device takeover (SMS, calls, messengers, screen, files, remote wipe). That makes it a serious threat for journalists and others at risk. Installation needs physical access and ADB, so device handling and supply-chain security matter. Disable USB debugging, avoid sideloading from untrusted sources, and consider enabling Android Advanced Protection Mode (AAPM), which blocks sideloading entirely and adds other hardening for at-risk users.
Detection strategies:
- Network-based:
- TLS connections to servers presenting CN=server (self-signed) on ports 7000-7257 (and 4022 where observed).
- Certificate fingerprint and banner hash as above for blocking or alerting.
- Use the Censys Threat Hunting Platform to find ResidentBat hosts and add them to blocklists or monitoring.
- Device-based:
- Monitor for ADB usage and sideloaded packages on managed devices.
- Awareness of Google Play Protect being disabled and of sensitive permissions granted to unfamiliar or system-looking apps.
Blocking and hunting:
Use the Censys Threat Hunting Platform to find and block ResidentBat infrastructure. Run the provided queries regularly and alert on outbound HTTPS to the identified IP:port combinations or certificate fingerprints.
References
- RSF exclusive: RSF uncovers new spyware in Belarus
- RSF report (PDF): report1.pdf
- Censys Threat: ResidentBat (THREAT-240)
- Android Advanced Protection Mode: developer.android.com