At Censys, we’re always working to expand our visibility into the more obscure corners of the Internet. There are countless protocols that talk away in the background, sometimes serving legitimate purposes, sometimes serving as common vectors for abuse.
Today we’re excited to announce new or improved protocol scanners in our dataset for eight services:
| Protocol | Censys Protocol Name | Query |
| Cisco Network Spectrum Interface (NSI) | CISCO_NSI | 🔎> |
| Adobe Flash Socket Policy Server | FLASH_SOCKET_POLICY | 🔎> |
| Mitsubishi MELSEC PLC Protocol | MELSEC | 🔎> |
| HashiCorp Memberlist Gossip Protocol | MEMBERLIST | 🔎> |
| MikroTik RouterOS Management API | ROUTEROS_API | 🔎> |
| RustDesk Services: Heartbeat service Relay Server ( hbbr)Rendezvous Server ( hbbs) | RUSTDESK_HEARTBEAT RUSTDESK_RELAY RUSTDESK_RENDEZVOUS | 🔎> |
Read on for a breakdown of what each protocol is, why it matters, and how to find it in Censys.
Cisco Network Spectrum Interface
If you’ve ever worked with RF spectrum analysis tools like Spectrum Expert or Chanalyzer, you’ve likely interacted with Cisco Network Spectrum Interface (NSI). It’s a proprietary protocol that allows these tools to communicate with Cisco wireless access points and pull spectrum data.

Cisco Spectrum Expert Interface (Source: Cisco)
While this is a fairly niche protocol, it’s worth tracking since it can reveal information about wireless infrastructure deployments. Hosts running NSI are almost certainly running Cisco Spectrum Expert or a compatible access point, typically intended for high-density wireless environments where RF management would matter, like large enterprise campuses, hospitals, universities, and factories. Since NSI is designed to operate within a controlled management network, finding it exposed on the public internet is also a good indicator of potential gaps in network segmentation.
Censys Platform Query 🔎>:
host.services.protocol="CISCO_NSI"Adobe Flash Socket Policy Server
Flash Socket Policy servers were part of Adobe Flash’s cross-domain security model. Before a Flash application embedded in a browser could open a socket connection to a remote server, it first needed to retrieve a policy file from that server. That policy file defined which origins were allowed to establish connections, acting as a kind of firewall rule set for Flash-based socket communication.
Adobe Flash Player was officially discontinued at the end of 2020, and browsers have long since stopped supporting it. So why does this matter now? Because Flash Socket Policy servers are still out there, quietly listening on nearly 100,000 hosts. The vast amount of exposure we see is geolocated in China.
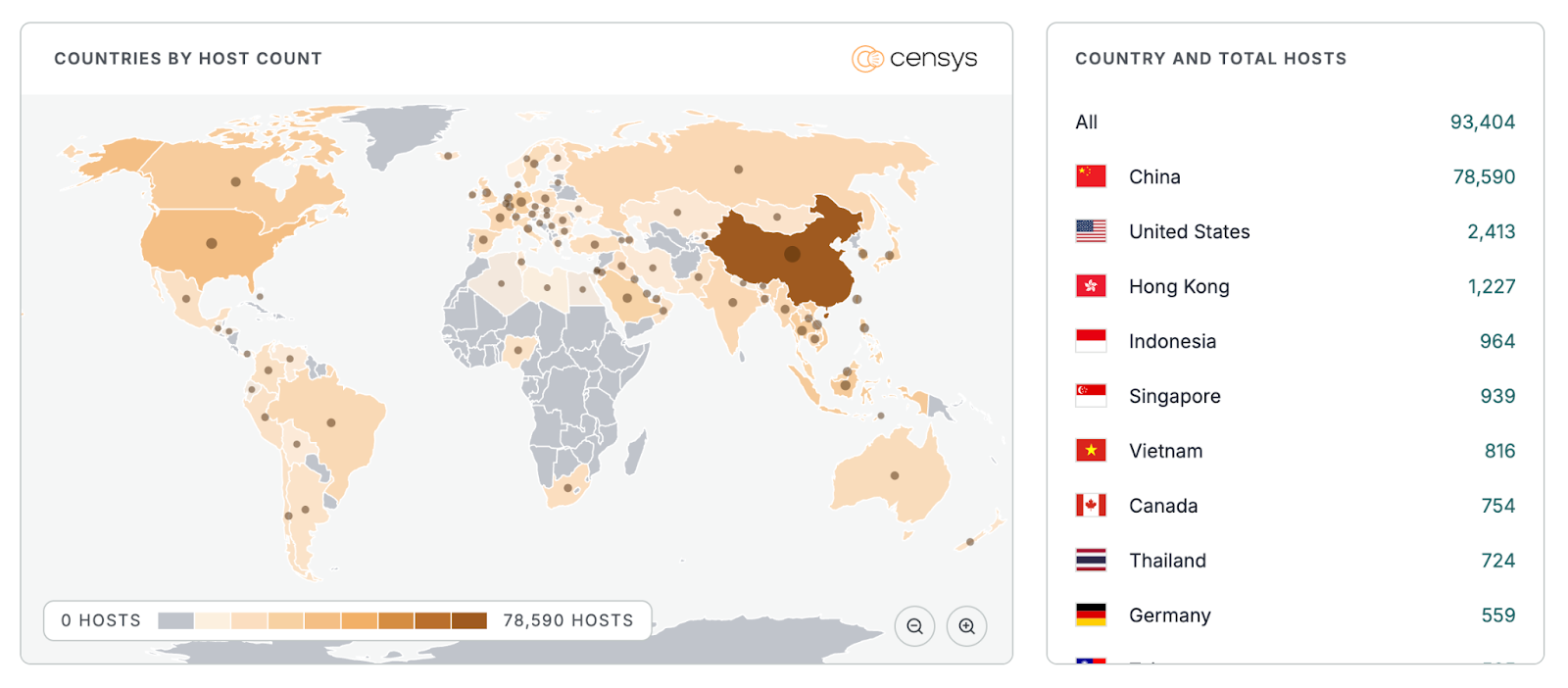
Their presence is a useful signal for identifying aging or abandoned infrastructure. Hosts still running these services could likely be running other legacy software as well, which makes them interesting targets for attackers and important ones for defenders to find.
Censys Platform Query 🔎>:
host.services.protocol="FLASH_SOCKET_POLICY"Mitsubishi MELSEC PLC Protocol
MELSEC refers to Mitsubishi Electric’s line of programmable logic controllers (PLCs) that are widely used in industrial automation environments. This scanner is an improved replacement for our legacy melsecq scanner, with broader and more reliable detection across the MELSEC protocol family.
MELSEC PLCs are found across a wide range of industries, particularly the automotive and manufacturing sectors, and handle everything from small-scale machine control to large, complex factory automation systems.
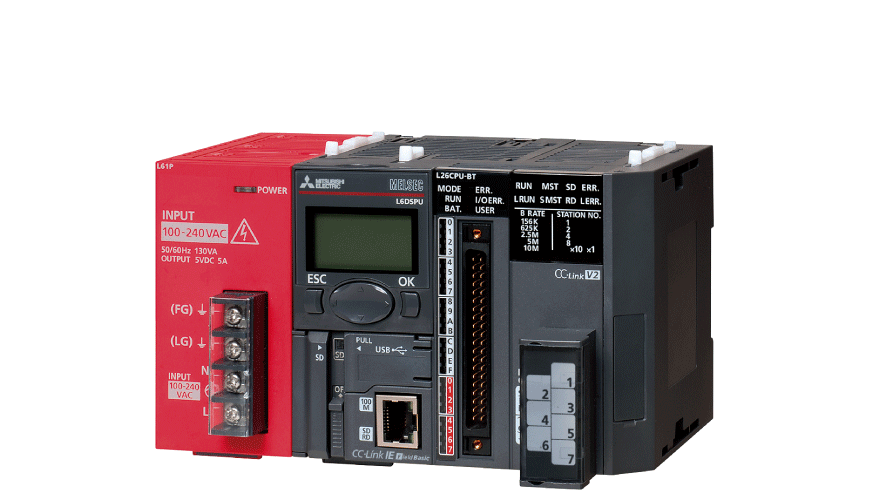
Exposing any kind of industrial PLC interface to the public internet can potentially give malicious actors the ability to remotely enumerate, and in some cases interact with, industrial control systems. This is the kind of exposure that has real-world physical consequences if exploited. Identifying internet-facing MELSEC devices is a critical step in ICS/OT asset discovery and risk reduction.
Censys Platform Query 🔎>:
host.services.protocol="MELSEC"HashiCorp Memberlist Gossip Protocol
Memberlist is an open-source Go library from HashiCorp used for cluster management and failure detection in distributed systems. It uses a gossip protocol, or a peer-to-peer communication model where nodes in a cluster periodically share state with one another, to keep all members in sync about who’s in the cluster and who’s gone dark. You’ll find Memberlist embedded in a number of well-known projects, including Consul, Serf, and various other distributed systems that need to manage cluster topology.
When Memberlist discovery ports are exposed to the internet, they can leak information about internal cluster structure, such as node addresses and membership states. For organizations running distributed infrastructure, this is the kind of quiet exposure that’s easy to miss and worth knowing about.
Censys Platform Query 🔎>:
host.services.protocol="MEMBERLIST"MikroTik RouterOS Management API
MikroTik’s RouterOS is a popular network operating system found on MikroTik routers and other networking hardware worldwide. The RouterOS API is a proprietary interface for programmatically managing these devices, including querying their configurations, modifying settings, and automating network operations. If you’re hunting for MikroTik exposure, this pairs well with two other MikroTik admin protocols already in our dataset: MIKROTIK_BW (Bandwidth tester) and MIKROTIK_WINBOX (WinBox utility).
MikroTik devices are extremely common in small-to-medium business environments, ISPs, and home labs, and their management interfaces have historically been attractive targets for threat actors trying to gain an initial access foothold into a network.
Exposed RouterOS API ports are a meaningful signal of internet-facing network device management, and in cases where default credentials are in use or authentication is weak, they create a significant attack surface. MikroTik vulnerabilities and misconfigurations have been exploited in a number of high-profile campaigns over the years, making visibility into these exposures particularly valuable.
Censys Platform Query 🔎>:
host.services.protocol="ROUTEROS_API"RustDesk: Three New Scanners for a High-Risk Tool
RustDesk is an open-source, self-hosted remote desktop application that’s essentially a self-managed alternative to tools like TeamViewer or AnyDesk. Because it’s open source and free to self-host, it’s grown a significant user base. However, like any remote access tool, it has also become a frequent target for abuse.
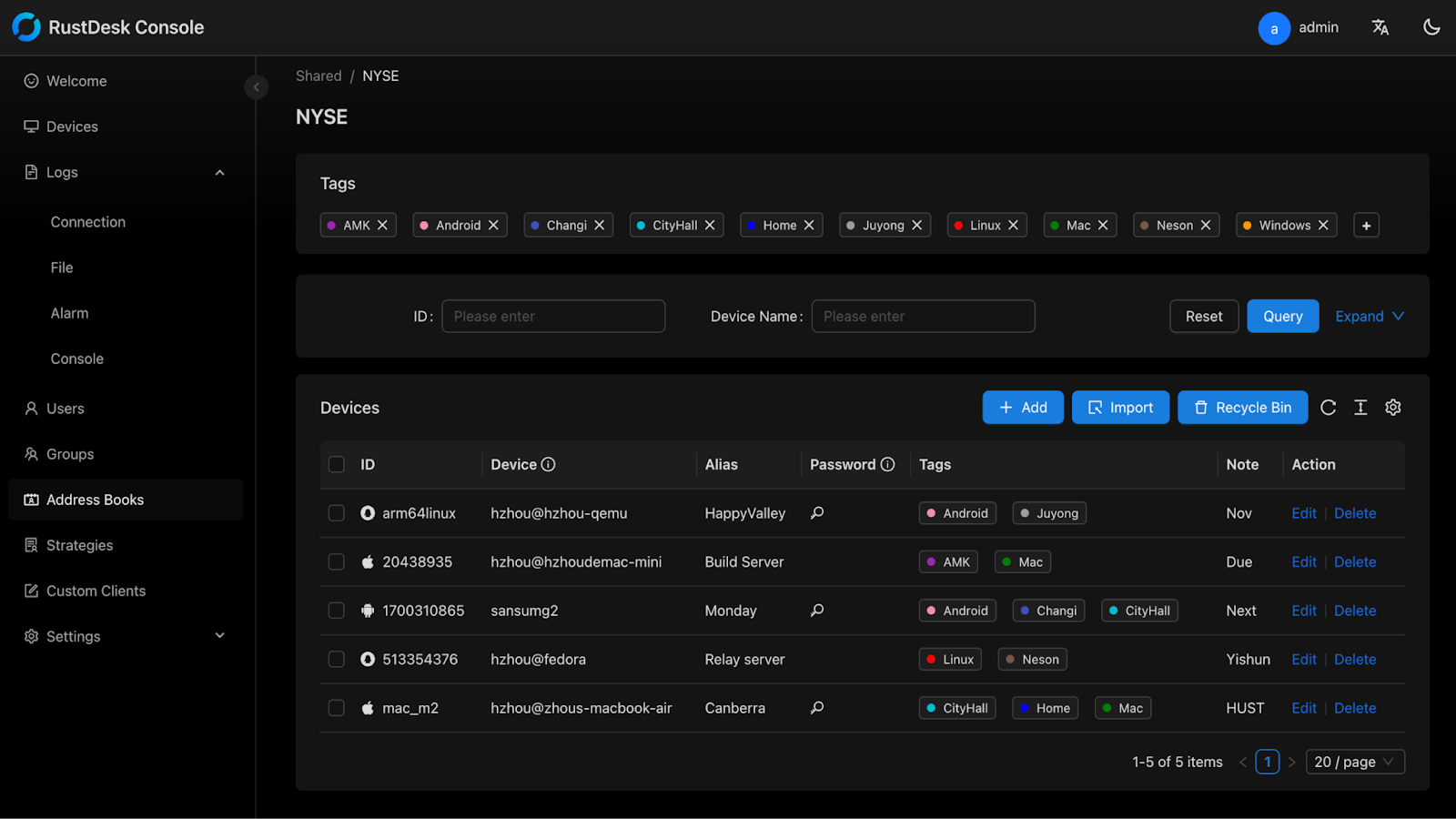
We’ve updated our RustDesk detection with a more precise and comprehensive set of detections of various service components:
RUSTDESK_HEARTBEAT covers the UDP heartbeat and ID registration service used by the hbbs (rendezvous) server to maintain connections with registered clients.
RUSTDESK_RENDEZVOUS covers the TCP rendezvous and registration service, where clients initiate key exchange and NAT traversal with the hbbs server.
RUSTDESK_RELAY covers the hbbr (relay) server, which proxies traffic between clients when a direct peer-to-peer connection can’t be established.
When RustDesk servers are misconfigured, they expose all of these ports to the public internet and function as open relays, meaning anyone can route traffic through them, not just the intended users.
Remote access tools are consistently abused by threat actors, and RustDesk is no exception. A few notable recent examples include:
North Korean IT Worker Campaigns: Mandiant has reported that North Korean actors posing as foreign IT professionals have used RustDesk as part of their operational toolkit. These individuals infiltrate remote work positions at companies around the world, using remote access tools to maintain persistence and exfiltrate data. RustDesk’s open-source and self-hosted nature makes it particularly useful for actors who want to avoid commercial tools that typically have built-in logging and abuse reporting.
Customer Service Scams: In 2023, RustDesk was used in a wave of tech support and customer service scams where victims were tricked into installing it, granting attackers remote access to their systems and enabling theft of credentials and sensitive data.
Tracking internet-facing RustDesk infrastructure is an important capability for threat intelligence teams, incident responders, and anyone trying to understand the remote access tool landscape on the internet.
Censys Platform Query 🔎>:
host.services.protocol={"RUSTDESK_HEARTBEAT","RUSTDESK_RELAY", "RUSTDESK_RENDEZVOUS"}User Access
All the aforementioned protocols are accessible to Free and Starter users at a minimum, with visibility into whether these services are present on a given host. Core and Enterprise users get full visibility and search capabilities across most protocols, with the exception of MELSEC, which requires the ICS add-on for complete access. The three RustDesk services are fully viewable and searchable across all subscription tiers.
References
- https://www.cisco.com/c/en/us/support/docs/wireless/5500-series-wireless-controllers/113344-cuwn-ppm.html
- https://airsdk.dev/reference/actionscript/3.0/flash/net/Socket.html
- https://whatportis.com/ports/843_adobe-flash-socket-policy-server
- https://www.mitsubishielectric.com/fa/products/cnt/plc/pmerit/
- https://github.com/hashicorp/memberlist
- https://help.mikrotik.com/docs/spaces/ROS/pages/47579160/API
- https://github.com/rustdesk/rustdesk
- https://rustdesk.com/docs/en/self-host/rustdesk-server-pro/relay/