Executive Summary
- As tensions between the U.S. and Iran have continued to build, so have opportunistic attacks on industrial control systems (ICS). Throughout March 2026, multiple Iranian actors claimed attacks on various ICS devices throughout the region.
- We revisited Internet exposure of four ICS device types historically targeted or known to be of interest to Iranian threat actors. Devices we studied include Unitronics Vision PLCs, Orpak SiteOmat, Red Lion equipment, and the Tridium Niagara framework.
- Apart from Unitronics devices which are slightly more common in Australia, these devices are most commonly observed in the United States.
- All devices observed experienced at least a minor decrease in global exposure from June 2025 to March 2026, ranging from Orpak SiteOmat’s 30.9% decrease to a 2.8% decrease in Unitronics exposures.
Introduction
In June 2025, as tensions increased between Iran and the U.S., we examined the Internet exposure of four different industrial control systems (ICS) components known to have been targeted by or of interest to Iranian threat actors in the past. We use the term “targeting” carefully here, as the software and devices claimed to have been compromised in these attacks are typically systems exposed directly to the Internet, often with default or weak credentials. While devices in a particular region or from a specific manufacturer may be sought out, the end targets themselves are often targets of opportunity, facilitated by poor security hygiene practices.
Given continued activity between the U.S. and Iran in 2026, we took updated exposure measurements of the same four devices and software studied last June to understand how their Internet footprint–and potential attack surface–has evolved.
Devices of Interest
- Unitronics Vision PLC/HMIs
- Unitronics is an Israel-based manufacturer of PLCs, human-machine interfaces (HMIs), and other tooling often used in industrial environments. Their devices are used across a variety of industries, but those in the water and wastewater (WWS) sector have been commonly targeted. Until late 2023, these systems shipped with a default password of “1111”. Unitronics systems use PCOM, a proprietary protocol, for communications between their devices.
- Unitronics is an Israel-based manufacturer of PLCs, human-machine interfaces (HMIs), and other tooling often used in industrial environments. Their devices are used across a variety of industries, but those in the water and wastewater (WWS) sector have been commonly targeted. Until late 2023, these systems shipped with a default password of “1111”. Unitronics systems use PCOM, a proprietary protocol, for communications between their devices.
- Orpak SiteOmat fuel management systems
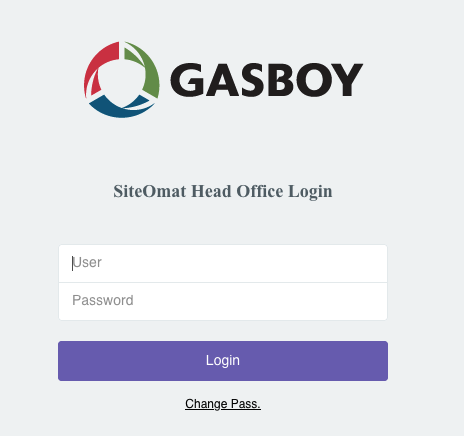
- Orpak, now a subsidiary of Gilbarco Veeder-Root, is an Israel-based provider of fuel station automation, fleet management, and other solutions for oil companies and commercial vehicle fleets. SiteOmat is their fuel station automation software, which ships with a default username and password of “Admin/Admin”.
- Orpak, now a subsidiary of Gilbarco Veeder-Root, is an Israel-based provider of fuel station automation, fleet management, and other solutions for oil companies and commercial vehicle fleets. SiteOmat is their fuel station automation software, which ships with a default username and password of “Admin/Admin”.
- Red Lion
- Red Lion is a U.S.-based company that specializes in HMIs, meters, and controllers for automated or industrial environments. Their products are used across a variety of sectors, including factory and process automation, WWS, oil & gas, and building automation. Crimson is the configuration software for Red Lion’s controllers, HMIs, and meters, which includes a drag-and-drop interface for easier programming.
- Tridium Niagara
- Tridium is a U.S.-based company whose Niagara framework is used to integrate various building automation and control tools into a single interface. This tooling allows building administrators to control lighting, HVAC, and security systems. Tridium systems use FOX, a proprietary protocol, for communications between Niagara devices.
During our previous investigation, Unitronics, Red Lion, and Tridium Niagara each saw increases in exposure during the six-month study timeframe biweekly from January 2025 to June 2025. However, in our current biweekly examination of June 2025 through March 2026, we note an overall global decrease in exposure of all four devices studied.
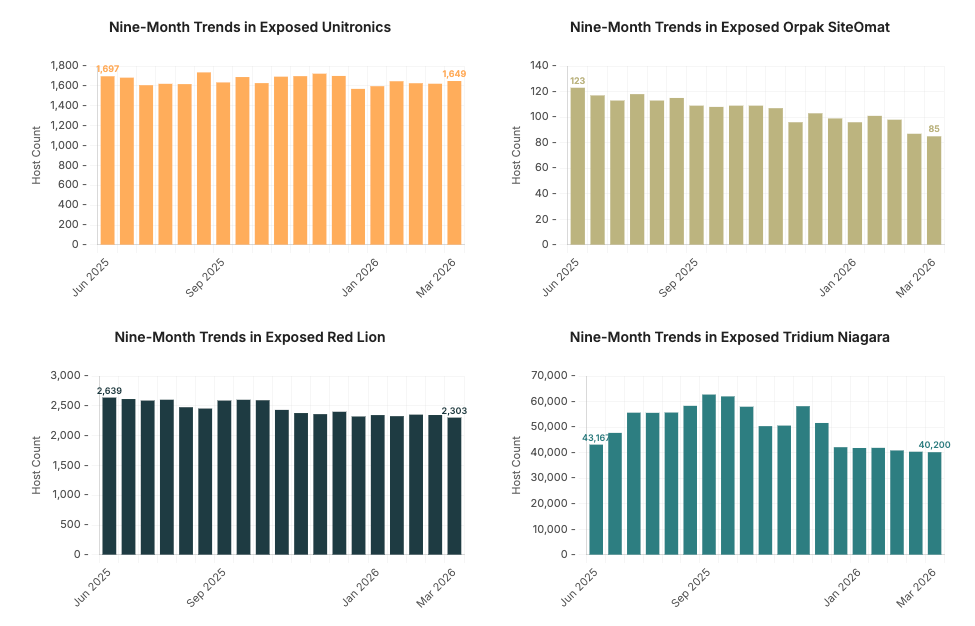
| Device Type | June 2025 Total | March 2026 Total | Delta |
| Unitronics | 1,697 | 1,649 | -48 (-2.8%) |
| Orpak SiteOmat | 123 | 85 | -38 (-30.9%) |
| Red Lion | 2,639 | 2,303 | -336 (-12.7%) |
| Tridium Niagara | 43,167 | 40,200 | -2,967 (-6.9%) |
While we observe decreases in the Internet exposure of each of these systems, the decreases do not all follow the same trajectory. Orpak SiteOmat has the most clear, steady decline across the study timeframe. Unitronics and Red Lion are relatively steady with modest decreases. Tridium Niagara has the most unusual profile of the systems studied, peaking in September 2025 with over 62,000 instances observed before settling back around 40,000 as of our latest look in March 2026. It’s unclear what might have caused this swell in Tridium Niagara, but since early January 2026, exposures have remained relatively stable with minor decreases.
Additionally, the scales of each of these exposures are very different. We began our study in June 2025 with over 43,000 Tridium Niagara systems exposed globally, while we observed 123 Orpak SiteOmat exposures for the same snapshot date. While we discuss changes of exposures over time, it’s important to consider that a hypothetical 10% decrease in Tridium Niagara would look very different from a 10% decrease in Orpak SiteOmat exposures. We must also be mindful of drawing strong conclusions from devices with relatively small online presence.
All data referenced in this report represents device exposure numbers — not all of these devices are necessarily vulnerable to a security issue. However, exposing systems connected to critical infrastructure directly to the Internet is risky and should be avoided.
In the following sections, we compare the last snapshot from the previous report (June 18, 2025) to the most recent snapshot in this analysis (March 11, 2026) for each of the four devices of interest.
Unitronics
Unitronics HMIs and PLCs were the subject of a 2023 defacement campaign claimed by the CyberAv3ngers, a hacktivist group with ties to the Islamic Revolutionary Guard Corps (IRGC). The devices were accessible from the public Internet and leveraged default credentials, providing an easy target.

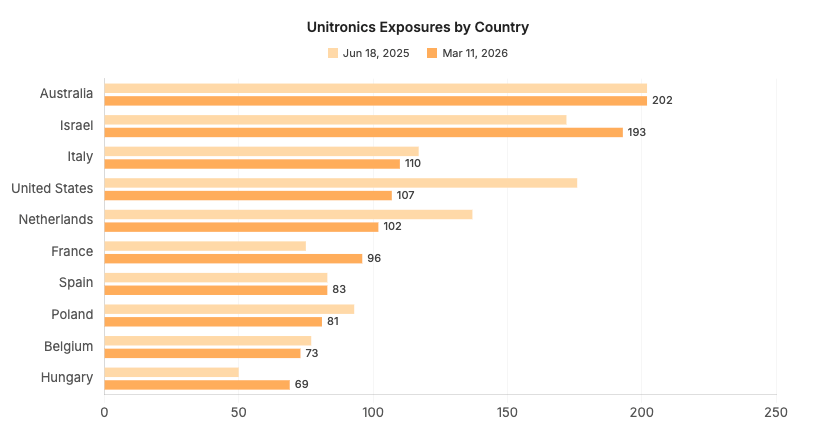
As observed in our previous study, Australia maintains the highest number of Unitronics exposures observed globally. The U.S. and the Netherlands saw sizable decreases (39%, 26% respectively) in exposures from one snapshot date to the next, while Israel’s Unitronics footprint increased by 12%.
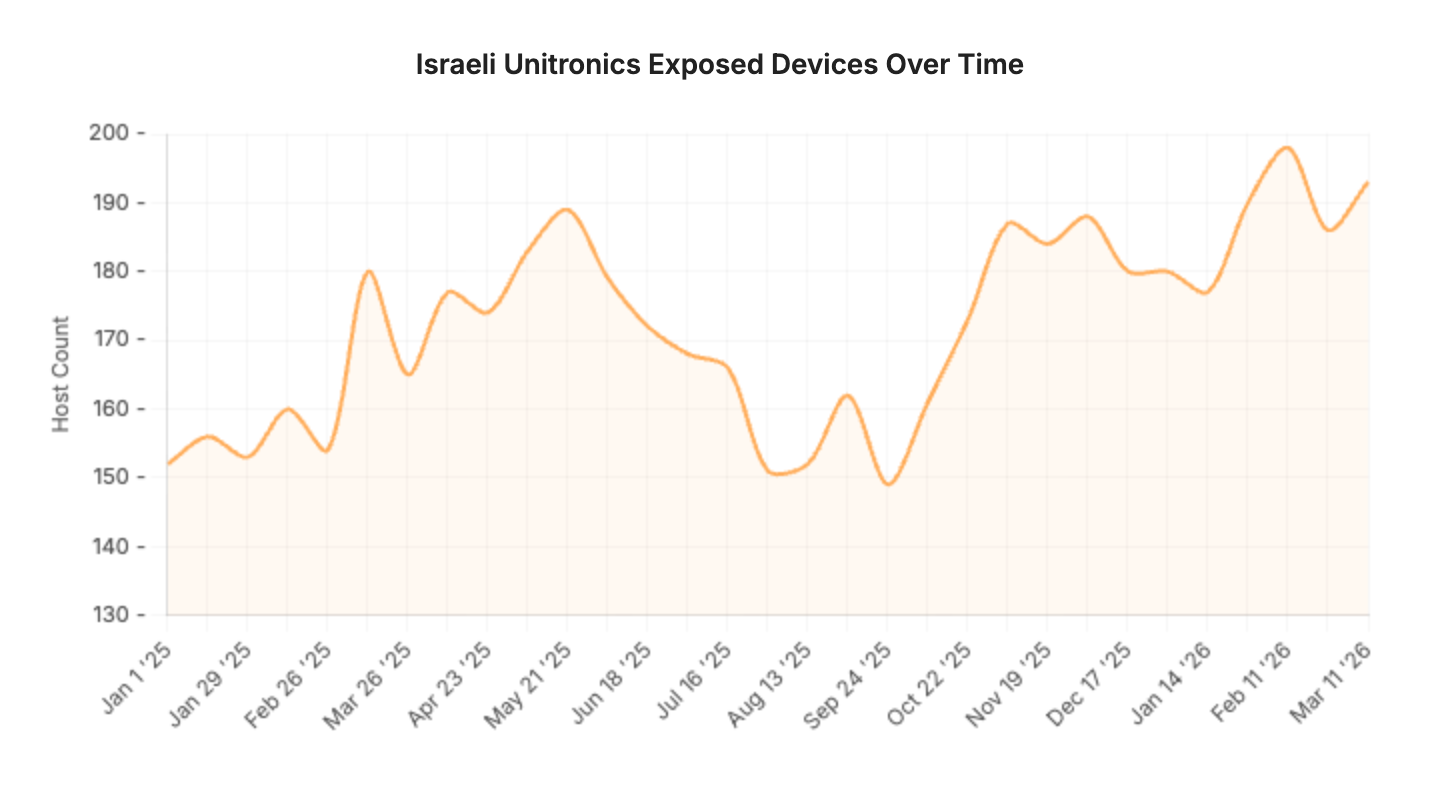
Examining Israel’s Unitronics presence more closely, we observe a clear decrease in exposures beginning in May 2025 that bottoms out throughout late August and September. While we can’t make causal statements, this timeframe aligns with increased concerns about offensive Iranian cyber activity. Since late September 2025, Unitronics exposures have steadily increased, with nearly 200 online in Israel as of mid-March 2026.
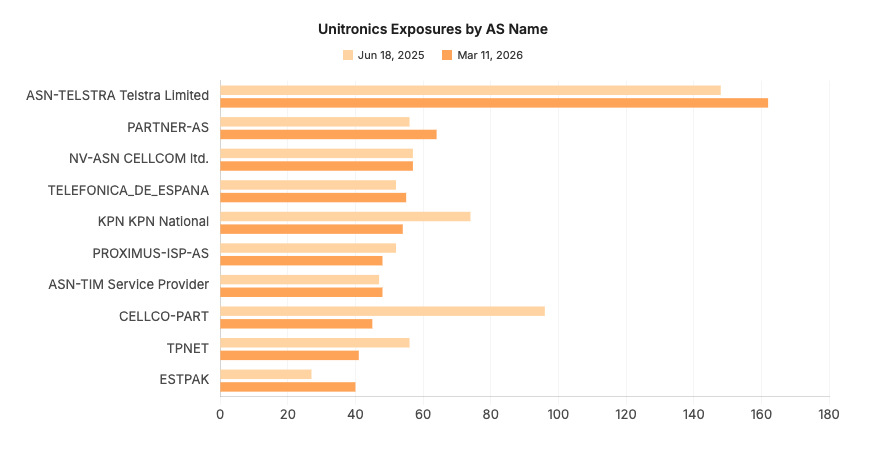
The most dramatic decrease observed is a 53% drop in exposures on CELLCO-PART, a Verizon network where we’ve previously observed large numbers of ICS devices. That decrease in particular is driven by the drop in U.S.-based Unitronics devices, while the 27% decrease on KPN corresponds to the drop in exposures observed in the Netherlands.
Orpak SiteOmat
The CyberAv3ngers also claimed to have compromised multiple SiteOmat instances in 2023, possibly gaining access by leveraging default credentials.
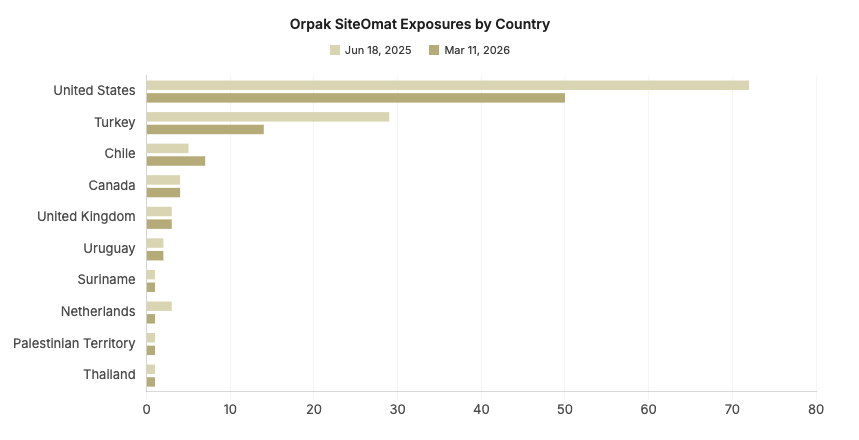
Despite a 30% decrease from the previous snapshot, the U.S. remains the leader in Orpak SiteOmat exposures. Alongside the U.S., Turkey has also substantially reduced their exposure, dropping 51% from 29 instances to 14. In contrast to other countries where SiteOmat is observed, Chile saw a slight increase, from 5 to 7 instances.
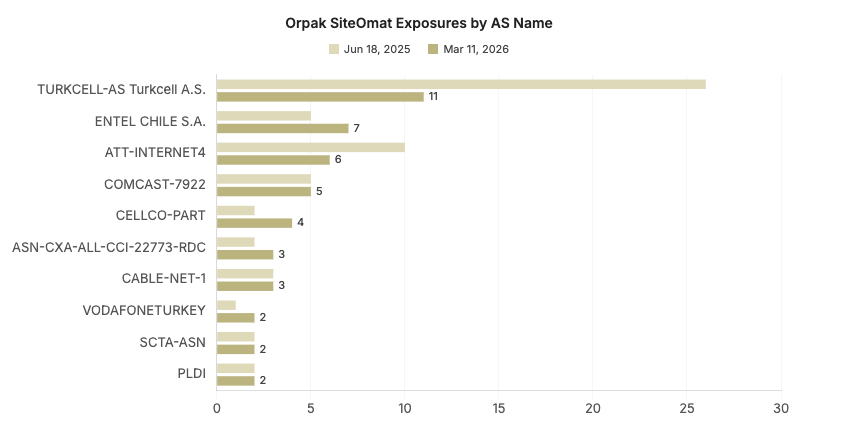
TURKCELL, a Turkish mobile provider, experienced a 57.7% drop in exposures during our study timeframe, and it closely mirrors the drop in SiteOmat instances in Turkey. The slight increase in Chile’s SiteOmat instances is reflected in the additional representation on ENTEL CHILE, a major Chilean telecom.
Red Lion
In 2024, Claroty published findings about IOCONTROL, a custom IOT/ICS malware leveraged by Iran to target Israeli and U.S.-based IOT and ICS devices. Red Lion is among the vendors reported to be affected by this malware.
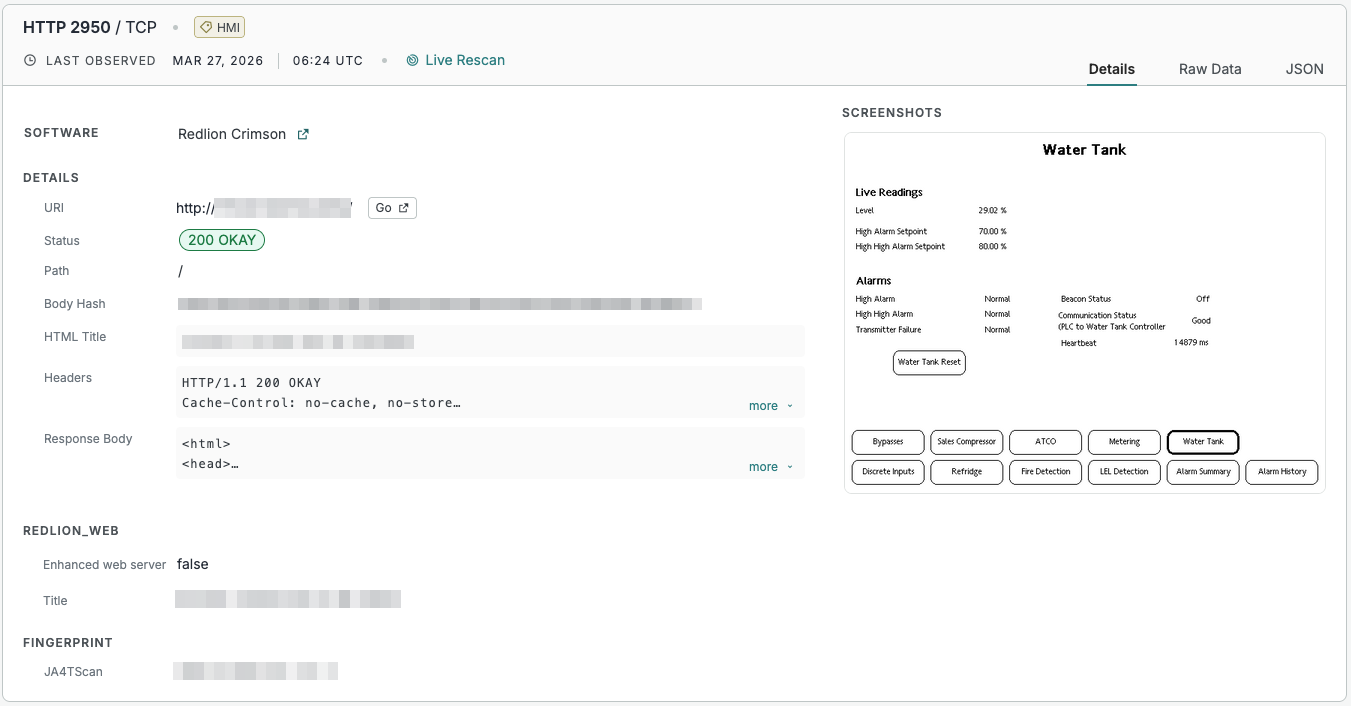
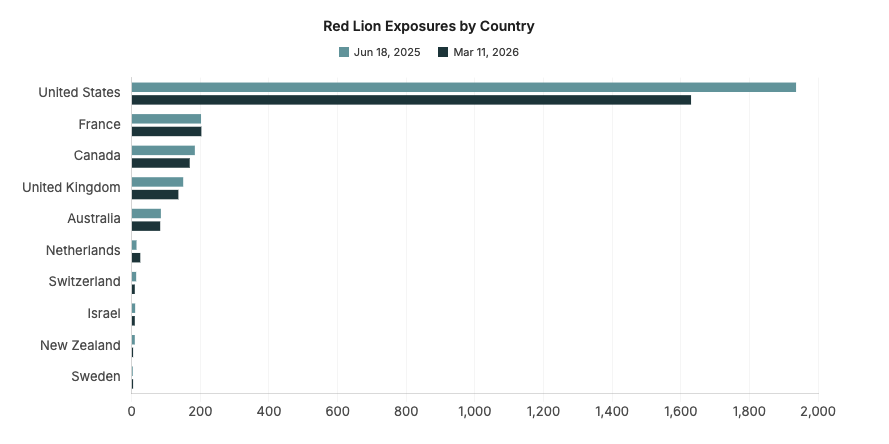
The U.S. continues to lead in Red Lion exposures despite a 15.8% decrease over the studied snapshots, with the next largest geographic footprints in France, Canada, and the U.K. an order of magnitude smaller.
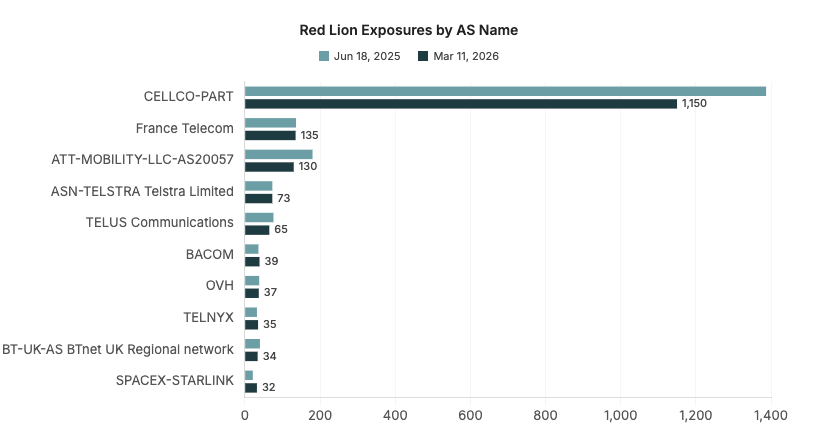
CELLCO-PART and ATT-MOBILITY decreases (17.1% and 27.8%, respectively) reflect decreases in Red Lion’s U.S. footprint, while STARLINK hosts several more instances of Red Lion, primarily in the U.S. Similar to observations of other ICS devices and systems, most instances of Red Lion are found on mobile or consumer ISP networks.
Tridium Niagara
Though Tridium Niagara systems have had their share of vulnerabilities and CVEs in the recent past, we are currently unaware of any Iranian attacks against these systems. We included these systems in our initial analysis based on findings in OpenAI’s 2024 Influence and cyber operations report which details queries allegedly made by CyberAv3ngers, including one for default credentials to Tridium Niagara devices.
We include them again here not only for the purposes of comparison, but because more recent attacks claimed by the Cyber Islamic Resistance have targeted building management systems (BMS) in Israel.
In this message and accompanying video, they claim attacks on several targets in Israel, including a hotel in Tel Aviv where “…the doors were locked, and electricity and water were cut off to all rooms of the hotel and the surrounding areas.” They also claim to have targeted “the entire lighting network” at a university in Haifa.
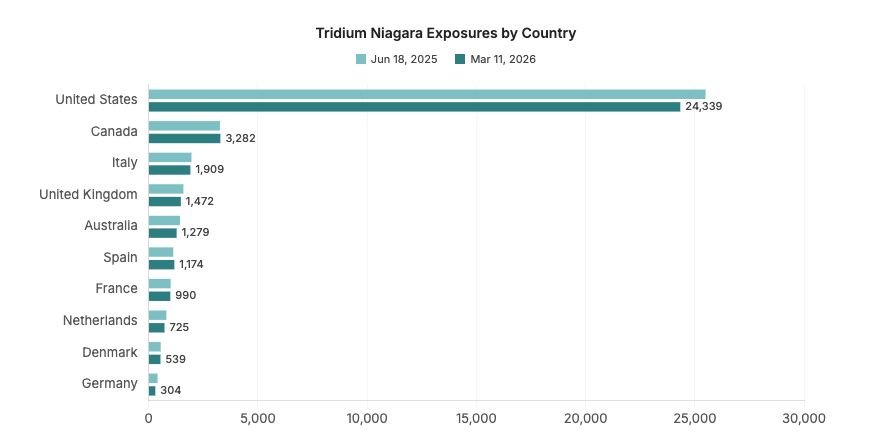
The geographic distribution of Tridium Niagara systems remains largely stable, with the majority still found in the U.S. Canada, Italy, and the U.K are a distant second, third, and fourth in global Niagara exposures.
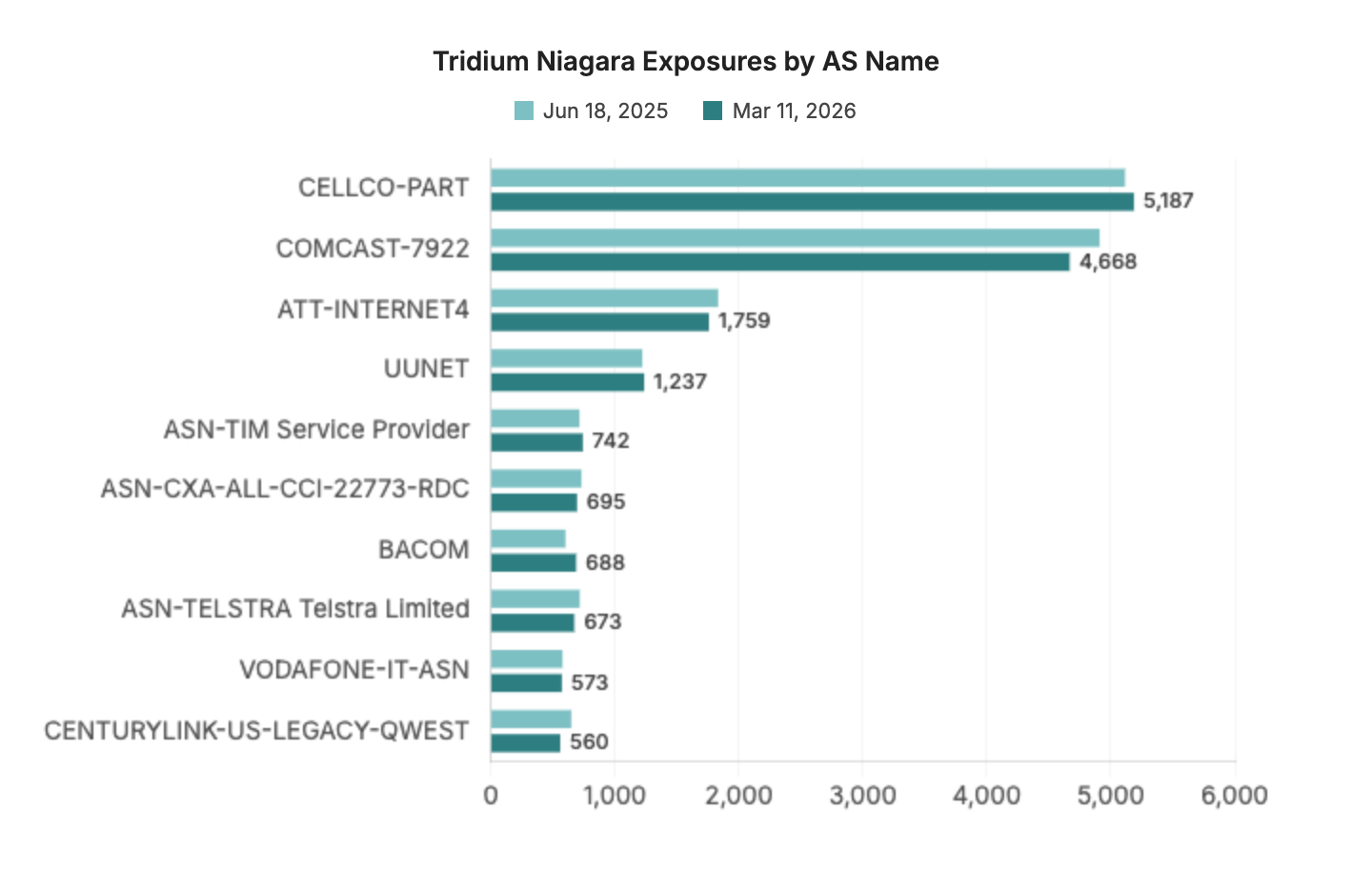
As observed across other ICS devices, we observe the majority of Tridium Niagara systems on cellular or consumer ISPs, including U.S.-based providers CELLCO-PART, COMCAST, and ATT-INTERNET.
Conclusion
“Overall global exposure decreases” for these devices makes for a positive headline, and it is indeed encouraging to see general declines in these systems exposed to the Internet. These slow, steady decreases could point to trends of better hygiene around these devices.
We continue to observe these devices primarily deployed on cellular or consumer ISPs, as well as satellite carriers (e.g., Starlink). This is in line with previous research on the broader ICS landscape, but can present security concerns, as these devices are often difficult to attribute to a specific owner or organization for remediation.
We close with our often repeated reminder that exposed ICS devices are never ideal, and we always encourage operators to remove these interfaces from the public Internet.
Next up: Check out the Censys ARC exposure brief for the Iranian-linked wiper attack on global medtech firm Stryker.