Copyright © 2026 Censys | Data Retention Policy | Terms & Conditions | Privacy Policy
Blade Logo Slider
Blade Prefooter
Blade Tab Slider Control Left
Blade Homepage Testimonials
Blade Row – Grid Pattern
Effective cybersecurity begins with visibility. Learn how Censys provides security teams with a high-quality Internet intelligence and context to achieve their objectives.
Blade Beneficts
Identify Exposures
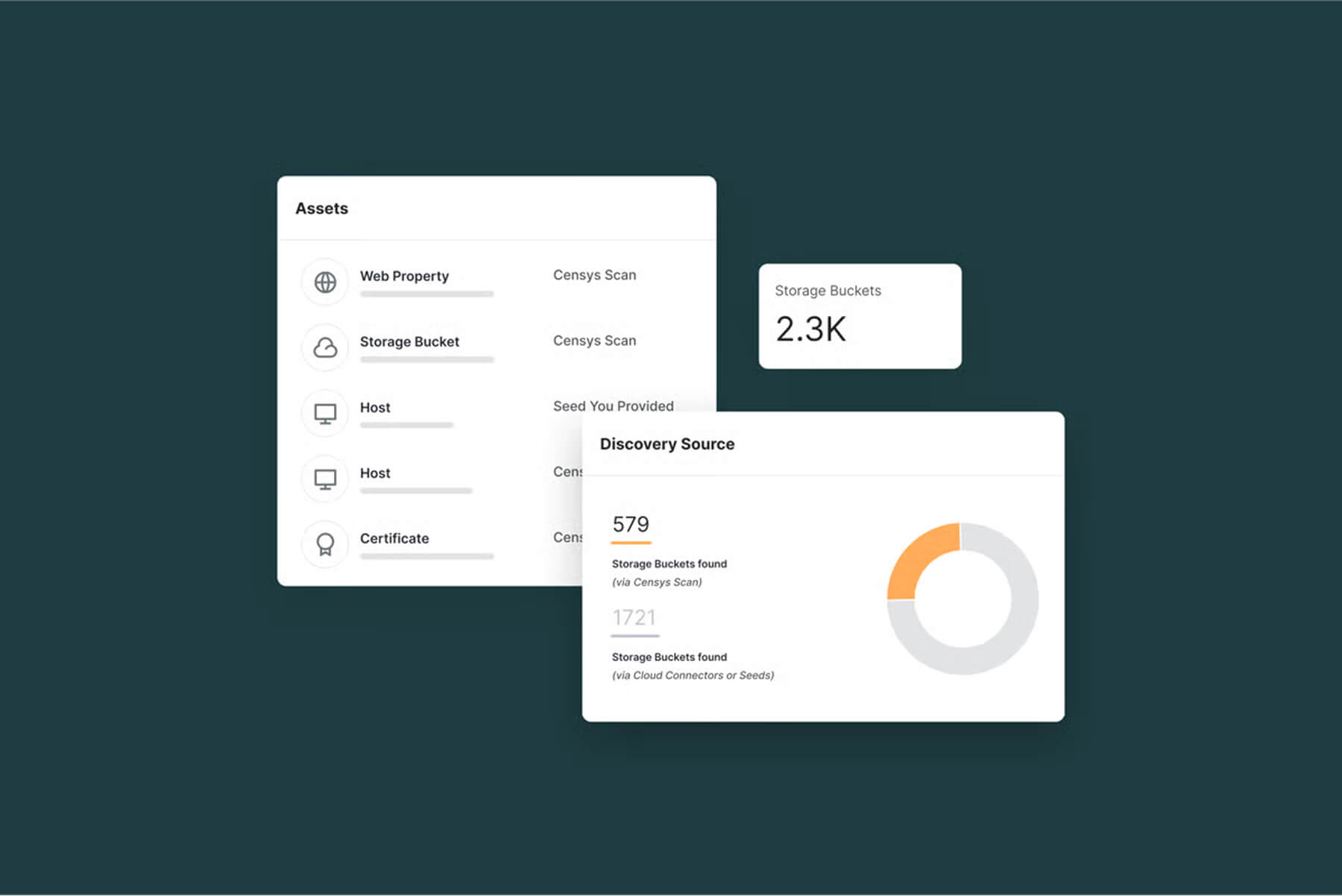
Your security starts with knowing your organization and every asset that’s exposed. Censys continuously maps your internet-facing assets, including cloud environments and unmanaged services, so you can identify risks, eliminate blind spots, and proactively protect your organization from sophisticated attacks.
See Risks
Your security is only as strong as your partners. Censys provides visibility into your third-party vendors and suppliers, helping you uncover vulnerabilities, misconfigurations, or exposures that open your organization to a breach.
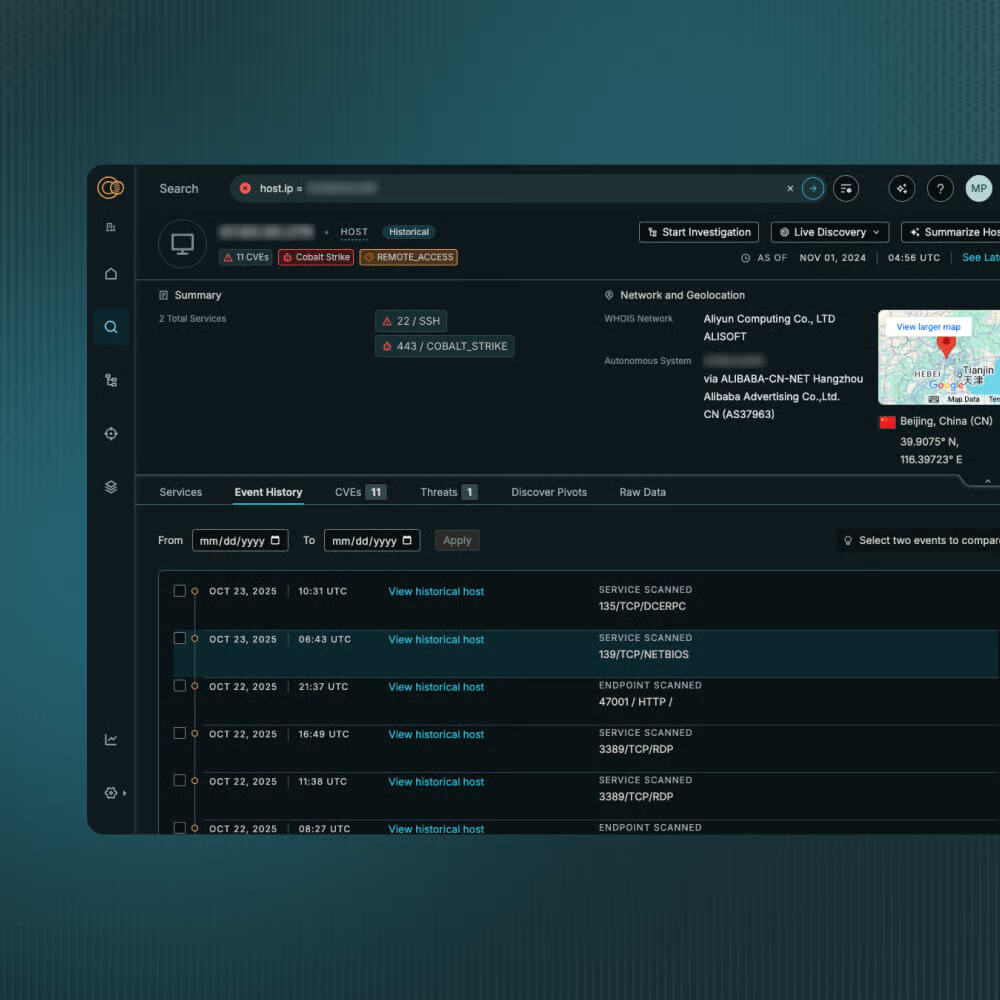
Monitor Threats
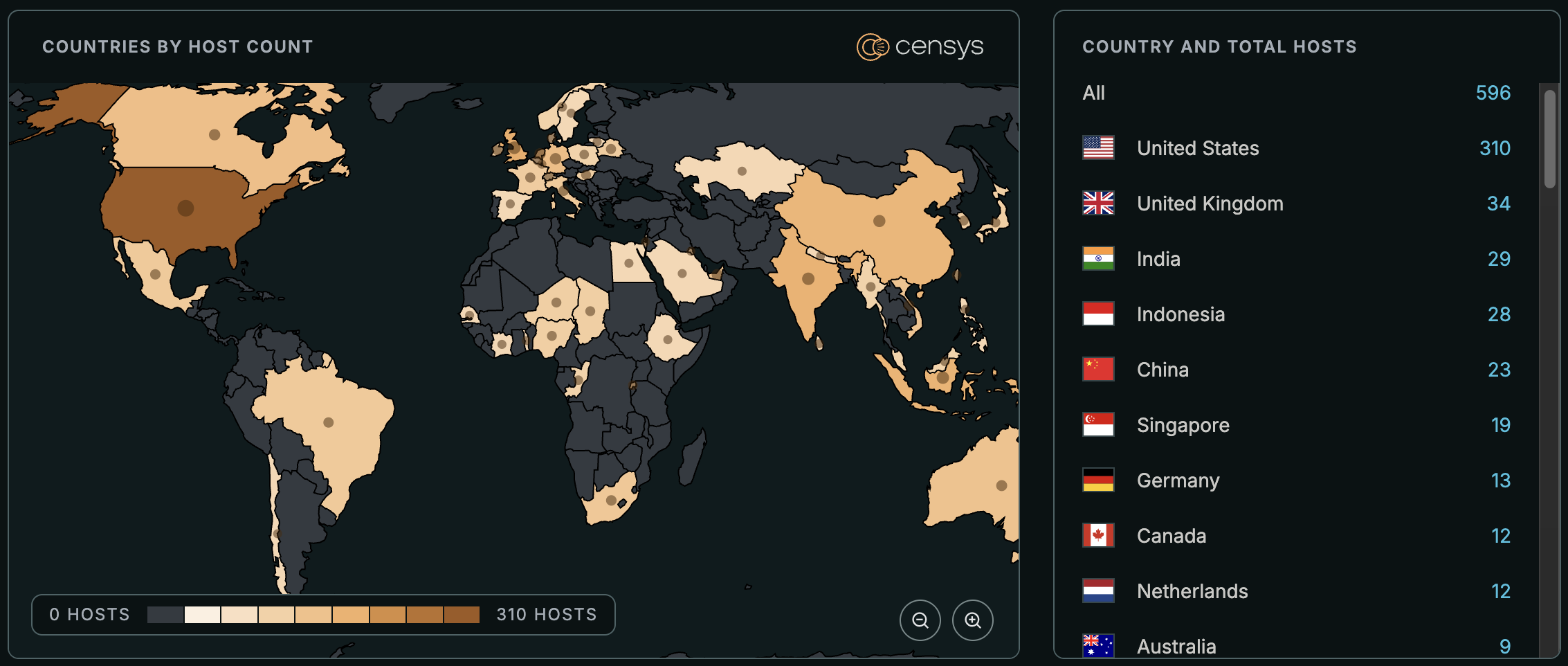
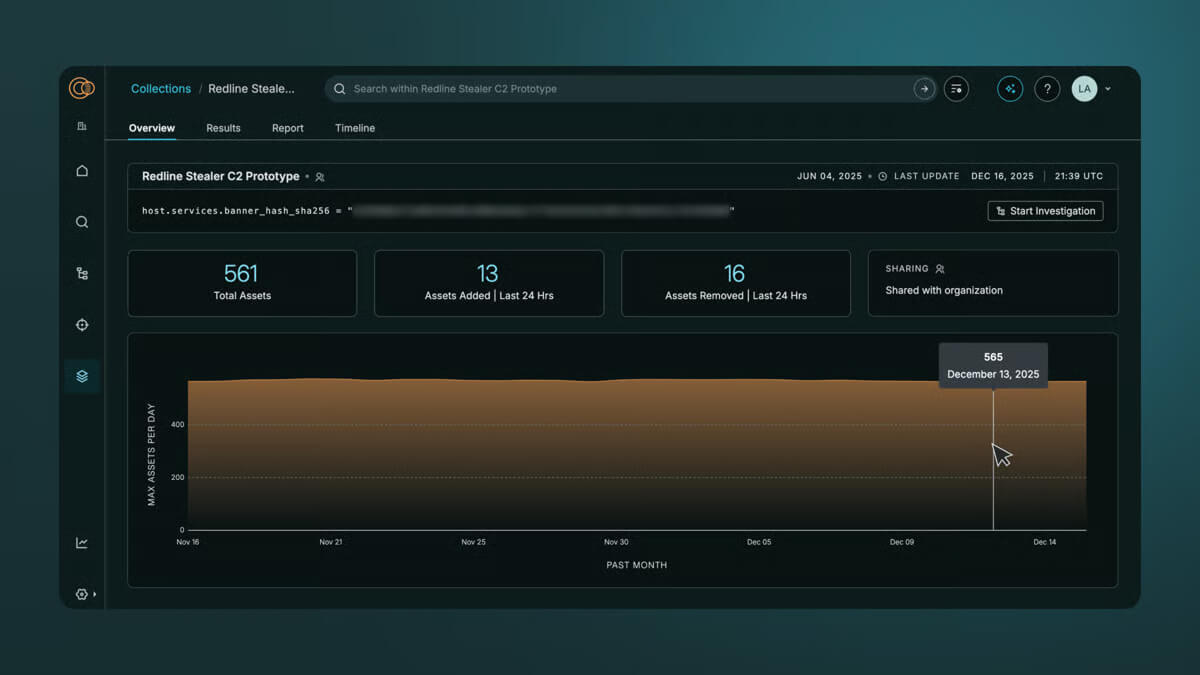
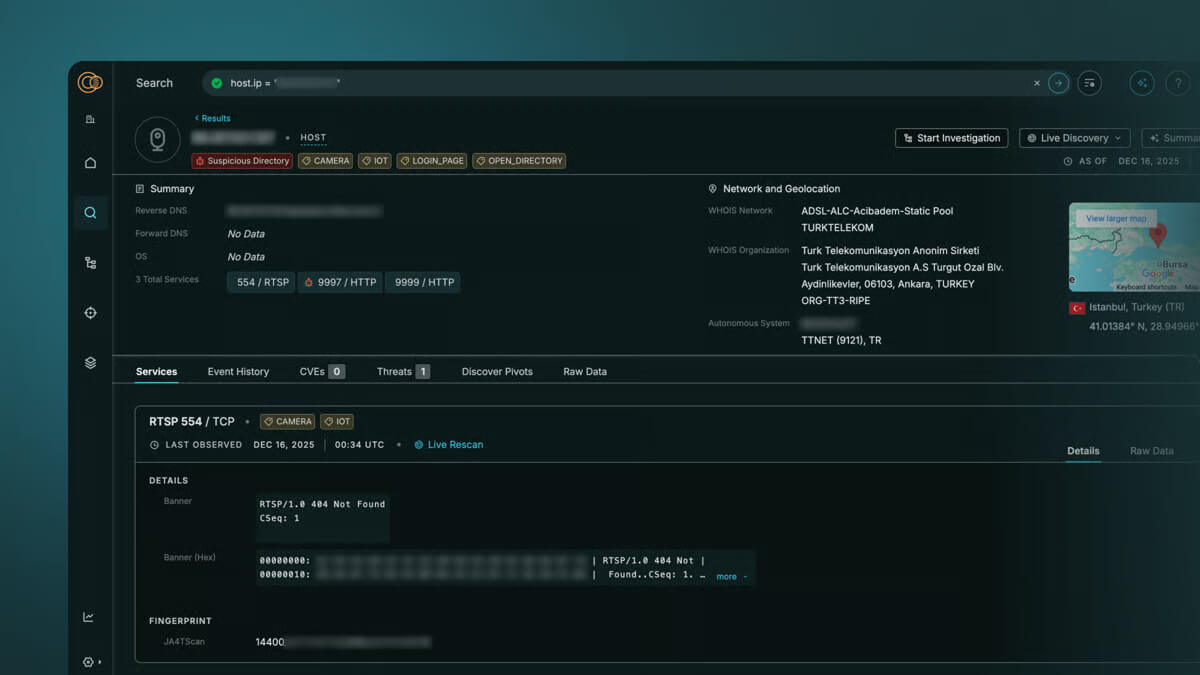
Attackers don’t operate in the dark, and neither should you. We track adversary infrastructure in real time, surfacing malicious domains, phishing infrastructure, and command-and-control (C2) servers, so you can detect threats before they impact your organization.
Blade Box with Text and Image
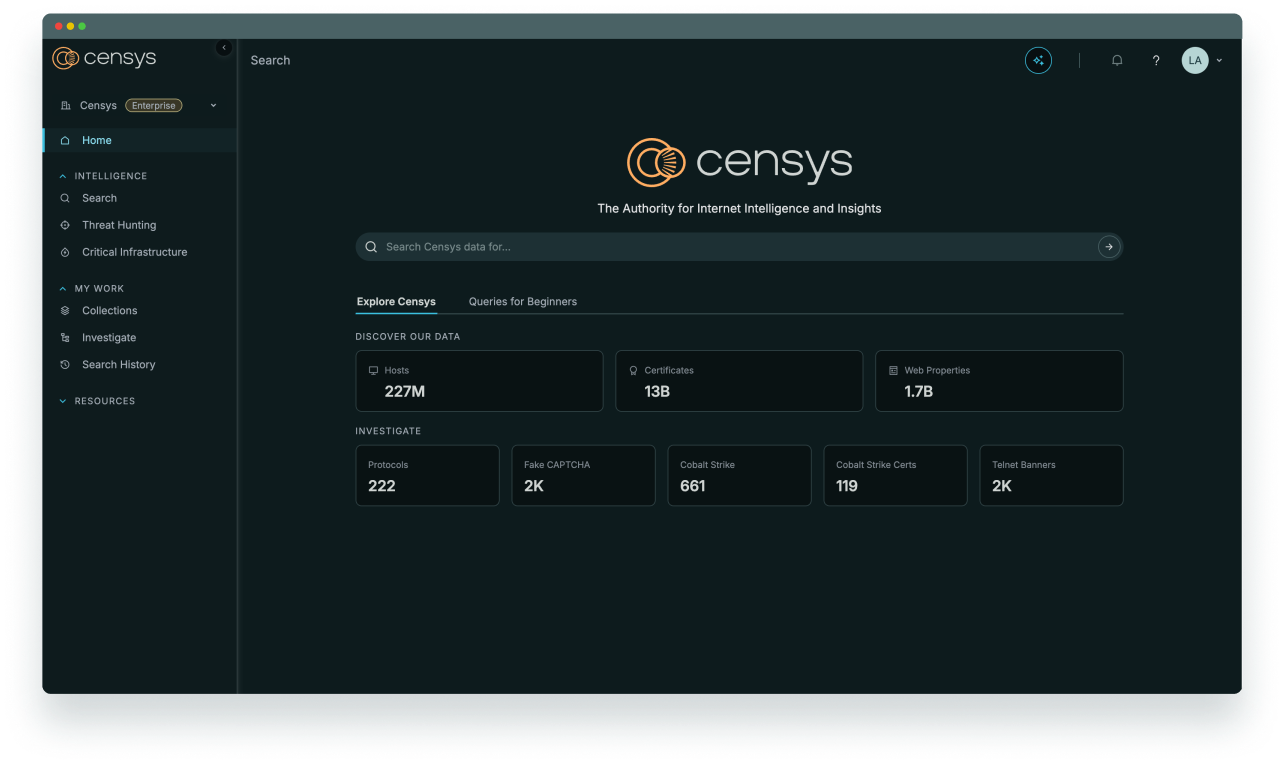
The Censys Internet Map is the industry’s most comprehensive, up-to-date dataset of global Internet infrastructure and the foundation for our security solutions. Censys’ ML-driven scanning infrastructure continually learns the complex deployment patterns of Internet infrastructure, which it uses to track every IP, host, service, and website on the Internet in close to real time.
We enhance our data with external context, WHOIS, CVEs, and threat actor fingerprints — enabling security teams and researchers to uncover threats, track changes, and defend their Internet presence with precision.
Blade Core Capability
The Censys Internet Map isn’t just a collection of raw scan data; it’s a continuously evolving, real-time representation of everything that exists on the Internet. Our technology doesn’t just find assets — it understands them, enriching each entity with context, ownership, risk profiles, relationships, and changes over time. This is how we build and maintain our Map of the Internet.
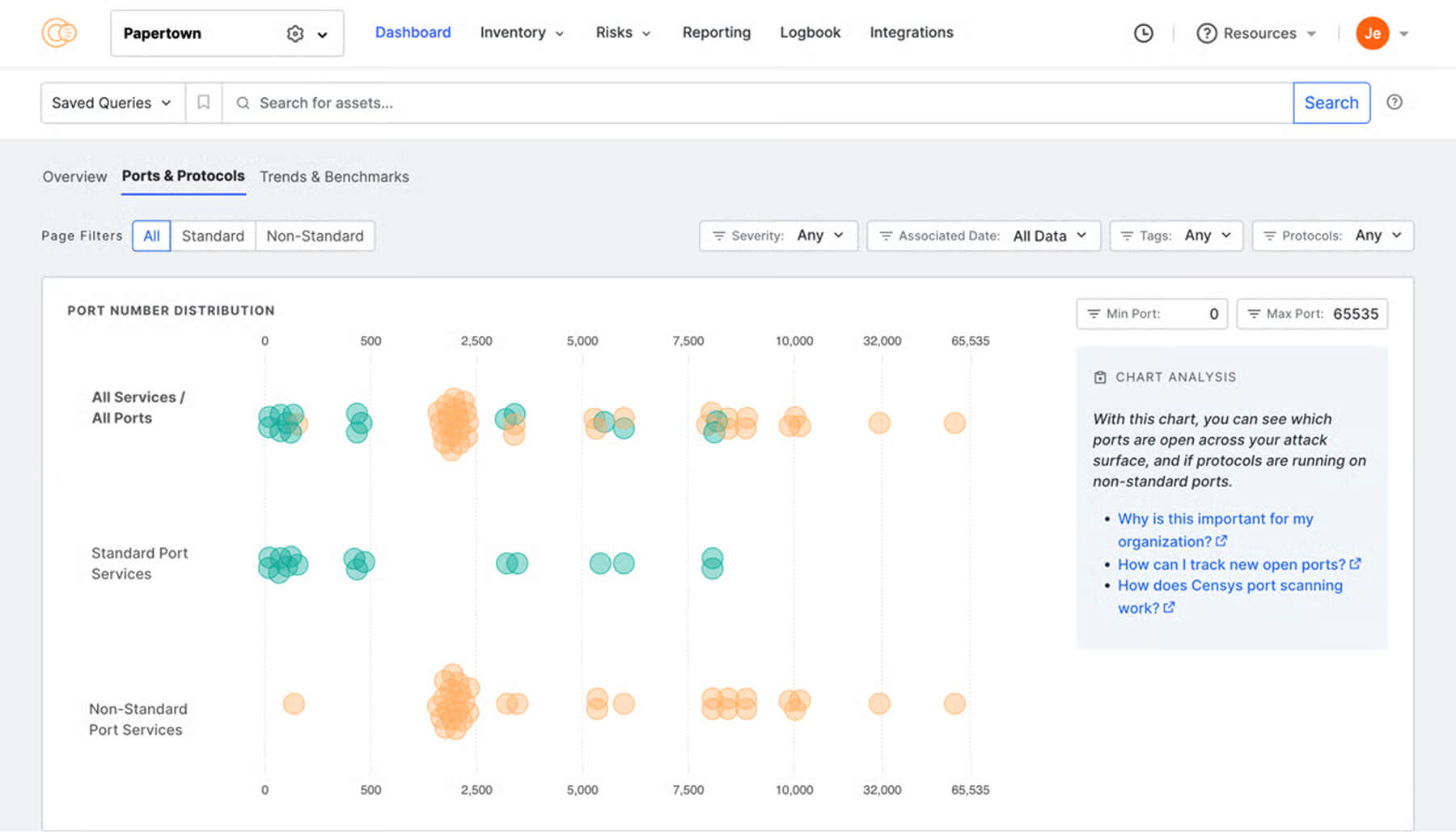
Predictive AI-driven internet scanning
Discovers services on non-standard ports, uncovering Internet services that would otherwise go uncovered.
Automatic protocol detection
Identifies services and protocols regardless of their port, revealing misconfigurations, unauthorized services, and backdoors.
Name-addressed web entities
Goes beyond IP addresses to detect technologies like WordPress, Kubernetes, ElasticSearch, and exposed APIs on web entities.
AI-driven context and relationships
Enriches data with deep intelligence on ownership, risk, and ties to threat actors.
Blade Pattern Background
Censys Search is the industry’s most powerful and comprehensive search engine for discovering and analyzing every system, service, IoT device, and asset on the Internet.
Blade Blogs
Blade Box With Video
Get an inside look at how the Censys Threat Hunting Module gives you unmatched visibility into attacker infrastructure. Powered by the industry-leading Censys Internet Map, this demo shows how you can proactively detect threats, accelerate investigations, and stay ahead of evolving cyber risks with precision and confidence.
Blade Leadership
Censys ARC is a team of experienced security and threat researchers with diverse backgrounds in specialized security analysis, engineering, research publication, and more. Meet the faces behind the research.
Blade Flip Cards
Prefer to develop your own integration with Censys? Check out our API documentation for Search and Attack Surface Management.
Blade Glossary
Curious about the difference between ASM and VM? Wondering what cloud connectors are, and how they could enhance your security efforts? We’ve got you covered. Find definitions and resources for key terms related to exposure management, threat hunting, and the broader cybersecurity landscape in our Censys Glossary.
Blade Pricing
Asset Discovery
The process of identifying internet assets that are part of an attack surface. Connections between the assets and the attack surface should be determined in an automated fashion, prioritizing only high-confidence findings to reduce false positives. Asset discovery is a foundational capability of Attack Surface Management, and should be conducted as frequently as possible.
Attack Surface
See more related to this term:
The set of internet assets relevant to an organization’s cybersecurity posture that an attacker can attempt to gain access to or compromise. Both internal and external assets make up an attack surface and can live on-premises, in the cloud, with shared hosting providers, and other third-party dependencies. An attack surface includes all assets, whether they are known or unknown, and whether they are protected by an IT/security team or left unguarded.
Attack Surface Management (ASM)
See more related to this term:
A proactive approach to exposure management involving the continuous discovery, inventory, and monitoring of an organization’s IT infrastructure, both known and unknown. Attack Surface Management (ASM) is a continuous process involving both inside-out and outside-in visibility of assets. ASM gives security programs the ability to understand and share context across teams to become proactive in building secure solutions and protecting the business. External Attack Surface Management (EASM) is a function within the larger Attack Surface Management process focused specifically on the external attack surface.
Censys Attack Surface Management is a best-in-class ASM solution which empowers security teams to gain full visibility into their attack surfaces. An outside-in view, or attacker’s perspective, of every asset and exposure is refreshed daily, hourly, or on-demand, giving your organization near-real time visibility and context so you can manage and communicate your cybersecurity posture. Your external attack surface is also assessed for risks and each is prioritized by what is important to you.
Automatic Protocol Detection
A method during port scanning of analyzing every server response to identify its underlying service, even if the service is non-standard for the port number (i.e. SSH on port 1234). This accounts for the fact that any service can be running on any port. Around 60% of all services observed on the internet are found on a non-standard port.
Censys Internet Map
See more related to this term:
The foundation of the Censys Platform is our data. Founded by the creators of zMap, Censys’ proprietary map of the internet offers the most coverage, fastest discovery, and the deepest insights available. The Censys Internet Map is the most comprehensive, up-to-date collection of global internet infrastructure enriched with critical context to empower your security and intelligence teams.
The Censys Internet Map by the numbers:
- 10B certificates
- 137 Top Ports
- 1,440 cloud ports daily
- 3,502 ports weekly
- >200M IPv4 Hosts
- >80M IPv6 Hosts
- >580M name-based hosts
- Daily refreshes on all (>2B) services
- 7 years historical data
Censys Platform
See more related to this term:
The leading Internet Intelligence Platform for Threat Hunting and Exposure Management, founded on the most comprehensive, accurate, and up-to-date map of the internet available. To ensure security teams have visibility into the threat landscape, they need access to a comprehensive and highly contextualized dataset for both proactive and reactive security analysis at scale. With the Censys Platform, organizations can get the most accurate data available, enabling teams to take down threats as close to real-time as possible, with no deployment or configuration required.
Cloud Connector
See more related to this term:
An integration with cloud accounts that is used for shadow cloud discovery, exposure monitoring, and cloud asset inventory. Information from all internet-facing assets in a given cloud account (Amazon S3, Azure Blob, Google Cloud Storage, virtual instances, databases, etc.) is continuously fed into an ASM platform, ideally as frequently as possible, enriching the asset discovery process and providing total cloud visibility. Cloud connectors are available within the Censys Attack Surface Management platform and empower users to gain total cross-cloud visibility.
Command and Control (C2) Infrastructure
See more related to this term:
Software that is used to control the servers on which they appear over the internet. Like any software, they have uniquely identifiable default settings and configurations. This can provide security professionals with tools to test their defenses, but they can also be leveraged for malicious actions.
Continuous Threat Exposure Management (CTEM)
A term coined by the analyst firm Gartner that refers to the “set of processes and capabilities that allow enterprises to continually and consistently evaluate the accessibility, exposure, and exploitability of an enterprise’s digital and physical assets.” Exposure management solutions, like Censys Attack Surface Management, that uncover unknown assets and continuously monitor an attack surface can be part of a CTEM strategy.
Critical Infrastructure
See more related to this term:
The assets, systems, and networks (both physical and virtual) that are essential to a functioning economy and national security. Critical infrastructure is an attractive target for hacker groups and nation-state threat actors; the 2021 Colonial Pipeline Attack is one example of a recent attack on critical infrastructure. Countries like the United States have made defending critical infrastructure from cyber attacks a key priority. In their 2023 national cybersecurity strategy, the Biden Administration stated that, “defending critical infrastructure against adversarial activity and other threats requires a model of cyber defense that emulates the distributed structure of the internet. Combining organizational collaboration and technology-enabled connectivity will create a trust-based ‘network of networks’ that builds situational awareness and drives collective action”.
Exposure
All potential ingress points on a given asset that can be seen from an outside-in perspective (internet-facing). Exposures in themselves do not determine the overall risk to an organization, but present opportunities that can be exploited by attackers and should be monitored or addressed.
Exposure Management
A proactive cybersecurity strategy that seeks to identify and manage all assets that are exposed on the public-facing internet. Exposure management helps organizations better identify risks across their attack surface to prevent a cyber attack. An exposure management strategy can be carried out with the support of Attack Surface Management solutions.
External Asset
An Internet-facing entity that an organization controls in order to conduct business on the Internet, including IP addresses, netblocks (CIDRs), autonomous systems (ASNs), certificates, domains and subdomains, websites, and storage objects. A collection of External Assets represents an organization’s external attack surface.
External Attack Surface
The set of external assets relevant to an organization’s cybersecurity posture. The external attack surface includes both known and unknown assets and has become the number one entry point of security incidents and breaches.
False Positive
When a cybersecurity solution or cybersecurity team incorrectly classifies activity on an attack surface as a risk. The frequent occurrence of false positives can lead security teams to waste unnecessary time and resources investigating benign activity, and can result in “risk fatigue”. A study from Forrester Research finds that on average, Censys ASM customers experience 70% fewer false positives.
Historical Lookup
The ability to retrieve details about an asset on the internet, like a host or a certificate, from an earlier point in time. Censys users can leverage historical data collected from our internet map to better understand the behavior of internet devices over time and to inform their threat hunting efforts. Users can observe changes to a specific asset or group of assets on any given day within the past two years.
Misconfiguration
The presence of security configurations and protocols that are not implemented or that are implemented incorrectly, resulting in gaps to an organization’s security posture. Examples of misconfigurations include unencrypted services, weak or missing security controls, and self-signed certificates. Research from Censys finds that misconfigurations are the most prevalent type of risk observed on the internet, accounting for four of the five most commonly observed risks.
Query
A command entered into an internet search tool that is used to retrieve information about an asset or group of assets. A query, or “search query,” can return a wide range of information about assets on the internet, including details about a host’s geographic location, software, and operating systems. The Censys Research Team frequently shares queries that users can run to inform their own investigations into unusual internet assets and threats.
Ransomware
A type of malware attack that uses encryption to lock out users from their systems until a sum of money is paid to the threat actors(s) deploying the attack. Some ransomware attacks threaten to expose data if victims do not pay within a requested time period. Ransomware can be spread through malicious attachments in emails, software apps, and websites, among other sources embedded with malware code.
Remediation
The process of mitigating or eliminating a vulnerability or threat to an organization’s network. Remediation can occur before malicious activity impacts an organization, such as at first discovery of a phishing attempt, or it may occur in response to the activity to limit damage, such as after a breach.
Rescan On-Demand
Triggering a port scan of any host within an attack surface to rescan all known services, refreshing host data with its most current configuration from an outside-in perspective. This is often used as a “trust, but verify mechanism as the final step of any exposure remediation efforts.
Risk
The potential for an exposure to negatively impact an organization if exploited or acted upon by an attacker. The overall severity of a risk is determined by a combination of the exposure itself and the underlying data, business context, or importance to an IT ecosystem. Risk severity may be different on a case by case basis.
Shadow Cloud
Cloud-hosted, internet-facing assets that live outside of any environments protected by an organization’s security program. Shadow cloud is the result of managed and unmanaged cloud adoption within an organization, and most commonly occurs as parts of the organization outside of IT create cloud services, often circumventing any formal IT process.
Shadow IT
Internet-facing assets that are not cohesively maintained, managed, and protected by an organization. Shadow IT presents easy-to-exploit attack vectors due to these assets being outside the scope of security tooling and often have minimal protection in place. Common sources of Shadow IT are legacy infrastructure, newly inherited assets through a merger or acquisition, non IT-managed assets being created by other parts of the organization, and the adoption of cloud services.
Threat Hunting
A proactive approach to cybersecurity in which skilled analysts use internet intelligence and other cybersecurity tools to seek out and identify risks, vulnerabilities, and other potentially malicious threats to the organization. Threat hunting is a form of vigilant defense that helps organizations stay ahead of threat actors. It involves threat hunters developing hypotheses based on the known behaviors of threat actors and validating or disproving these hypotheses through investigations.
Vulnerability Management (VM)
A cybersecurity strategy that continuously identifies and evaluates security vulnerabilities in systems so that organizations can prioritize threats and better protect their assets. Vulnerability management solutions begin with scanning to evaluate known assets; if vulnerabilities on those assets are discovered, a VM solution will then assess and prioritize the vulnerabilities. Unlike ASM, which identifies both known and unknown assets, VM only looks at the assets which are already known to an organization. Security teams can enrich their VM efforts with ASM by adding newly discovered assets to their inventory for ongoing monitoring and management.
Web Entities
All named HTTP(S) services such as websites, elasticsearch instances, kubernetes clusters, and prometheus endpoints. Users of Censys Attack Surface Management can use our Web Entities feature to gain visibility into their websites and other name-based HTTP content. These assets can be discovered, monitored, assessed for risks, and triaged so that teams can better defend against places where attacks happen. The Web Entities feature has been modeled to better reflect the cloud infrastructure that most teams use to deploy their websites and name-based HTTP services.
X.509 Certificates
Also known as SSL certificates, X.509 certificates help mitigate risk on the internet by enabling encryption for web traffic and acting as identity verification. Because certificates are useful for verifying an entity’s identity, they can provide helpful pivots in threat hunts and other investigations. Censys has the largest X.509 certificate repository in existence, which users can explore with advanced, granular searching capabilities to quickly retrieve the information they need.
Zero Trust
A security principle or architecture framework that is applied to an organization’s IT systems. Zero trust is used to secure infrastructure, and it requires that all individuals attempting to access that infrastructure be continuously authenticated and validated. As the name suggests, a zero trust model does not give an attempted user, even those within the organization, implicit trust without verification. There are three principles of zero trust as defined by the NIST: 1.) Enhanced identity government and policy based controls 2.) Micro-segmentation 3.) Overlay networks and software-defined perimeters.
| Compare plans | Individual Contact Sales | Security Operations Contact Sales | Threat Hunting Contact Sales |
|---|---|---|---|
| Platform | |||
| Users | 1 | Customizable | Customizable |
| API Access | ✓ | ✓ | ✓ |
| Search Query TypesEntity performs single lookups. Standard search leverages Censys query. Advanced are queries that include regex. | Entity, Standard, & Advanced | Entity, Standard, & Advanced | Entity, Standard, & Advanced |
| RBAC SupportRole based access controls. | ✗ | Enterprise | Enterprise |
| SSO and SAML SupportSupports the use of 3rd Party identity provide to provide SSO & authentication services. | ✗ | ✓ | ✓ |
| Available SupportGold Support Add-On Available for Enterprise and Threat Hunting customers. Additional Threat Hunting Gold Support also available. | Community | Community | Community |
| Data Visibility | |||
| Platform Data Access | Expanded Protocols, Services & Certificates | All Protocols, Services & Certificates (excluding ICS protocols) | All Protocols, Services & Certificates (excluding ICS protocols) |
| Host Data History | 1 week | 1 month | 1 month |
| Results per QueryViewable results for each query (up to 100 per page). | Up to 500 | Unlimited | Unlimited |
| View and Download Raw/JSON DataEnables the ability to download detailed information about this asset in JSON or Raw format. | ✓ | ✓ | ✓ |
| Matched FieldsHelps pinpoint relevant fields on a host from a Censys query result. | ✓ | ✓ | ✓ |
| Search CPE-based context fieldsAbility to search across Common Platform Enumeration name of a host. | Limited Set | ✓ | ✓ |
| Application Scanner DataProvides full protocol data access and advanced insights provided by Censys deep application scanners. | ✗ | ✓ | ✓ |
| Censys CollectionsAutomates the tracking & monitoring of the results from a Censys query over time. | 2 | 15 | 15 |
| Security Operations & Threat Hunting | |||
| Vulnerability InsightsCommon Vulnerability Exposures + VulnCheck Exploit Intelligence. | ✗ | ✓ | ✓ |
| Censys Threat DatasetCurated threat insights into C2 Infrastructure used by 155+ Malware Families. | ✗ | ✗ | ✓ |
| CensEyeEnables hunters to quickly identify malicious infrastructure and find new infrastructure with similar characteristics. | ✗ | ✗ | ✓ |
| On-Demand ScanningEnables the ability to initiate a scan request against specific hosts, returning the freshest data. | ✗ | ✗ | ✓ |
| Certificate & Host Visualization | ✗ | ✓ | ✓ |
| Advanced Pivoting & Contextual Hashes | ✗ | ✗ | ✓ |
| Exploration Dashboards | ✗ | ✓ | ✓ |
For Government Agencies Worldwide
Censys provides purpose-built internet intelligence with specialized datasets to support government specific investigations and exposure management requirements.
What you’ll achieve:
- Complete internet visibility with government-grade controls
- Detect and neutralize advanced persistent threats with datasets specialized for government agencies
- Enable cross-agency collaboration with mission-critical security controls
Features:
- Search all protocols and services
- Perform standard and advanced queries
- Unlimited pages of results
- Web property data from deep application scanners
- 1 months of host history, or more
- Raw/JSON data
- API access
- SSO and SAML login options
- Gold support available
- 10 users per account (add-on packs available)
Blade Icon Cards
Authoritative internet intelligence from continuous measurement of the global internet, giving security teams visibility into infrastructure and adversaries at internet scale.
The Censys Platform
Built on the industry’s authoritative Internet Map, Censys empowers security teams with the insights and investigative tools that they need.
Blade Leadership
Censys is guided by a seasoned group of board members with decades of experience leading and investing in tech.

Karim Faris
General Partner, Google Ventures
Karim Faris is a General Partner at GV, where he invests in visionary entrepreneurs building the future of cybersecurity, enterprise software, and AI. With a background in engineering and business, he brings a strategic approach to scaling high-growth startups. Before joining GV, Karim held leadership roles in venture capital and product management, helping companies navigate complex technology landscapes. His passion for cybersecurity innovation drives his support for transformative companies that redefine digital security and resilience.

Dug Song
Board Member
Dug Song is a visionary entrepreneur and cybersecurity leader, best known as the founder of Duo Security, which achieved the largest tech exit in Michigan’s history. A champion of Ann Arbor’s tech ecosystem, Dug has helped establish the city as a hub for cybersecurity innovation. Beyond tech, he is deeply committed to philanthropy through the Song Foundation, which supports equity, entrepreneurship, and community development. His lasting impact spans security, startups, and social good, shaping the future of both industry and community.

Jon Sakoda
Founder & Managing Partner, Decibel
Jon Sakoda is the Founding Partner of Decibel and a seasoned investor dedicated to backing bold entrepreneurs in cybersecurity, cloud, and AI. A former founder himself, Jon embraces a “founder-first” philosophy, helping startups find their unique advantage and scale into market leaders. Before Decibel, he was a General Partner at NEA, leading investments in category-defining companies. His deep expertise and commitment to innovation continue to drive the success of the next generation of enterprise technology pioneers.
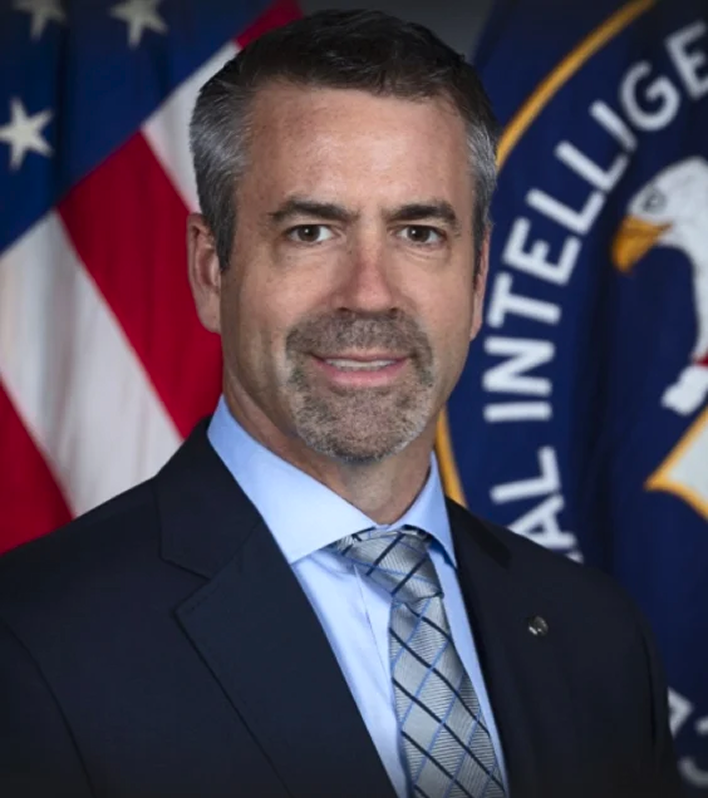
Andrew Boyd
Former Director of the CIA’s Center for Cyber Intelligence
Andrew Boyd is a cybersecurity and intelligence expert with decades of experience in national security. He served in senior leadership roles at the CIA, where he helped advance cyber operations and intelligence capabilities to protect against emerging threats. Now advising top security organizations, he brings deep expertise in threat intelligence and digital defense. His background in intelligence and commitment to cybersecurity innovation continue to shape the tools and strategies used to defend critical infrastructure and national interests.

Zakir Durumeric
CEO and Founder
Zakir Durumeric is the Founder and CEO of Censys. A leading expert in internet security, his research has earned a Sloan Research Fellowship, a USENIX Security “Test of Time” award, multiple IETF Applied Networking Research Prizes, and Best Paper honors. In 2015, MIT Technology Review named him one of its “35 Innovators Under 35” for his work on fast Internet scanning. Zakir holds a Ph.D. in Computer Science and Engineering from the University of Michigan. He is an Assistant Professor of Computer Science at Stanford University.
Blade Tab Slider – Vertical Scroll
Use Censys to power fast, consistent enrichment and internet-aware decisions across SIEM, SOAR, and internal workflows.
Case Study
Blade Testimonials – Case Study
Highlights
- Lorem ipsum dolor sit amet
- Lorem ipsum dolor sit amet
- Lorem ipsum dolor sit amet
- Lorem ipsum dolor sit amet
Our Story
Blade Timeline
Since day one, Censys has pushed the boundaries of what’s possible in cybersecurity. From first introducing fast Internet-wide scanning to developing the most sophisticated scan engine on earth, we are continually improving how we collect data and derive insights about Internet infrastructure.
2013
Zakir Durumeric invents ZMap
We created fast Internet scanning at the University of Michigan, released the ZMap open source scanner, and showed that it’s possible to measurably improve the security of the whole Internet by getting the right insights into the right hands.
2015
Censys Search
Launches
We introduce Censys Search and data downloads, initially scanning 16 popular Internet protocols.
2017
Censys Inc. Founded
Censys evolves from a research project into a free-standing company, bringing its best in class Internet visibility to security teams worldwide.
2019
New Scanning
Technology Built
Censys architected a brand new scan engine with proprietary scanning technology.
2020
Censys ASM
Launched
Censys introduces its industry-leading Attack Surface Management platform to provide security organizations the insights they need to protect their internet-facing infrastructure.
2023
Community Users
Censys surpasses 350,000 total community users … and growing.
2024
Global Expansion
Censys goes to market in Nordics, France, Australia, Singapore, Japan, and more.
2025
Censys Platform
Launched
Providing real-time, high-fidelity intelligence that security teams can trust to detect threats faster, prioritize risks with confidence, and accelerate investigations.
Today
We empower private and public sector security teams with high-fidelity insights that drive proactive defense and operational resilience.