Vulnerability Description
FortiClient EMS 7.4.5 through 7.4.6 is affected by an improper access control vulnerability, and Fortinet has assigned a CVSS v3.1 score of 9.1. NVD has added this to their database as well, but with a higher score of 9.8. According to Fortinet PSIRT FG-IR-26-099, an unauthenticated remote attacker may send crafted requests that bypass API authentication and authorization, resulting in unauthorized code or command execution. Fortinet states the issue has been exploited in the wild, and CISA added this to their Known Exploited Vulnerabilities Catalog (KEV). If you are running these devices, treat your Internet-exposed EMS management surfaces as high risk until patched and consider restricting access to trusted networks where possible.
| Field | Description |
| CVE-ID | CVE-2026-35616 — CVSS v3 9.1— assigned by Fortinet |
| Vulnerability Description | FortiClient EMS 7.4.5 through 7.4.6 is affected by an improper access control vulnerability that allows an unauthenticated remote attacker to send crafted requests that bypass API authentication and authorization, resulting in unauthorized code or command execution. |
| Date of Disclosure | April 3, 2026 |
| Affected Assets | Fortinet FortiClient EMS |
| Vulnerable Software Versions | 7.4.5 through 7.4.6 |
| PoC Available | No public PoCs have been observed at this time. |
| Exploitation Status | Fortinet has observed exploitation in the wild, and this was added to CISA KEV on April 6th, 2026. |
| Patch Status | Fortinet has published version-specific hotfix instructions for 7.4.5 and 7.4.6, which are linked in their advisory. FortiClientEMS 7.4.7 will also include a fix. The 7.2 EMS branch is listed as not affected. |
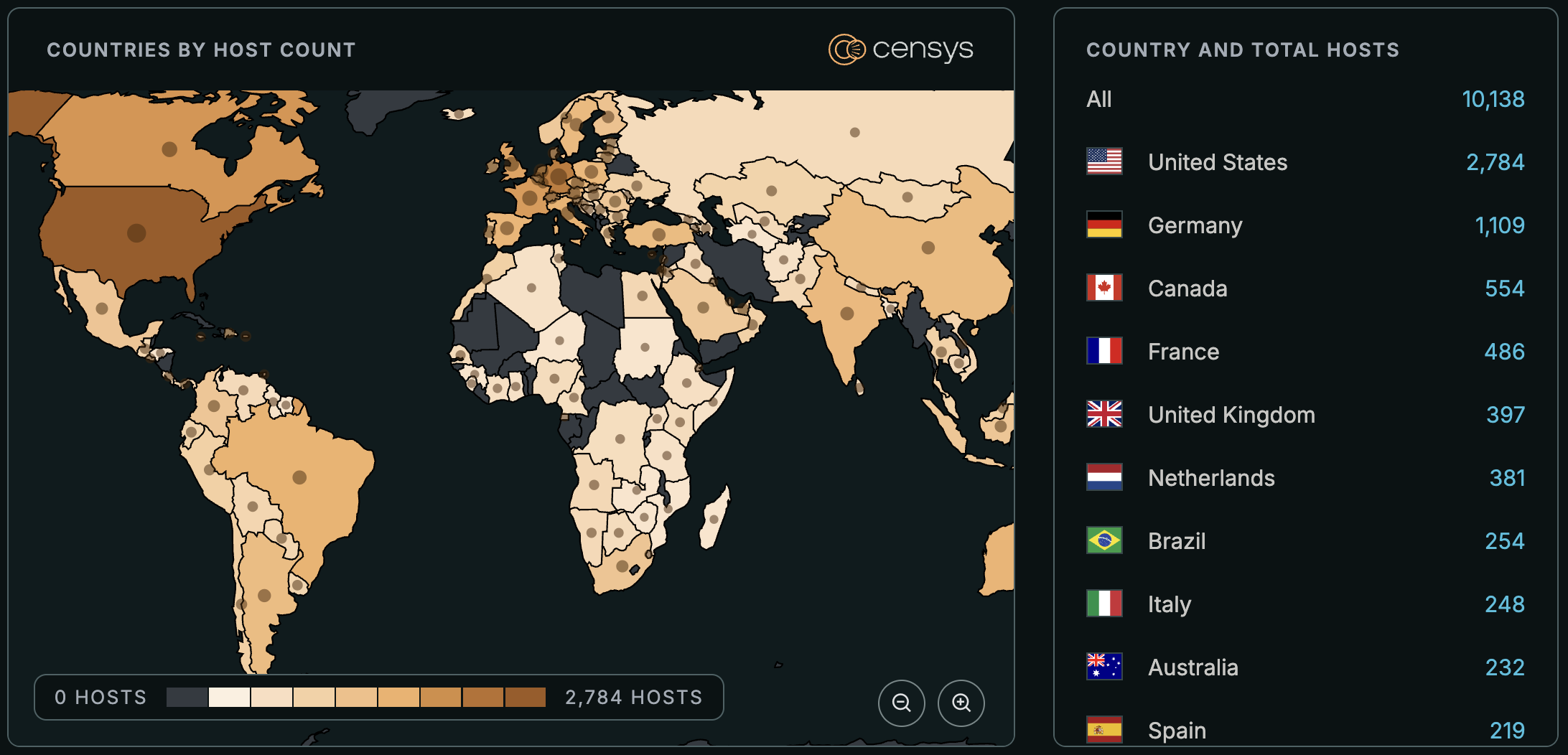
Censys ARC Perspective
Censys observes around 10K exposed hosts serving FortiClient EMS. Of these, 3,835 hosts are potentially vulnerable given that they serve banners that match affected versions.
(host.services.endpoints.http.html_title: "FortiClient Endpoint Management Server" or host.services.cert.parsed.subject_dn: "CN=FortiClient Enterprise Management Server" or host.services.endpoints.http.favicons.hash_md5: "fb9c168a99561a9672f6dce2144ad7e7" or host.services.protocol: "FORTINET_FCM" or web.endpoints.http.html_title: "FortiClient Endpoint Management Server" or web.cert.parsed.subject_dn: "CN=FortiClient Enterprise Management Server" or web.endpoints.http.favicons.hash_md5: "fb9c168a99561a9672f6dce2144ad7e7") and not labels: "HONEYPOT"
host.services.http.response.html_title: "FortiClient Endpoint Management Server" or host.services.tls.certificates.leaf_data.subject_dn: "CN=FortiClient Enterprise Management Server" or host.services.http.response.favicons.md5_hash: "fb9c168a99561a9672f6dce2144ad7e7" or host.services.service_name: "FORTINET_FCM" or web_entity.instances.http.response.html_title: "FortiClient Endpoint Management Server" or web_entity.instances.tls.certificates.leaf_data.subject_dn: "CN=FortiClient Enterprise Management Server" or web_entity.instances.http.response.favicons.md5_hash: "fb9c168a99561a9672f6dce2144ad7e7"
(services.http.response.html_title: "FortiClient Endpoint Management Server" or services.tls.certificates.leaf_data.subject_dn: "CN=FortiClient Enterprise Management Server" or services.http.response.favicons.md5_hash = "fb9c168a99561a9672f6dce2144ad7e7" or services.service_name: "FORTINET_FCM") and not labels: {honeypot, tarpit}






