Vulnerability Description
CVE-2025-4632 is a critical vulnerability in Samsung MagicInfo 9 Server (a digital signage software solution) affecting versions prior to 21.1052 with a CVSS score of 9.8. The issue arises from improper restriction of pathnames to designated directories, allowing attackers to write arbitrary files with system-level privileges.
Threat Activity
This vulnerability is actively being exploited and was added to the CISA Known Exploited Vulnerabilities (KEV) catalog on May 22, 2025.
Following the release of a technical proof-of-concept (PoC) by SSD Disclosure, Arctic Wolf reported suspicious activity targeting Samsung MagicInfo servers. While attribution is unconfirmed, the activity is suspected to be linked to CVE-2025-4632.
Initially, the PoC was believed to demonstrate exploitation of a related vulnerability, CVE-2024-7399, in the same product. However, testing showed that it remained effective even on systems patched against CVE-2024-7399. This indicates that CVE-2025-4632 bypasses the fix previously applied for CVE-2024-7399.
| Field | Details |
|---|---|
| CVE-ID | CVE-2025-4362 – CVSS 9.8 (Critical) – assigned by Samsung TV & Appliance |
| Vulnerability Description | Improper pathname restriction, allowing arbitrary file writes with system-level privileges |
| Date of Disclosure | May 13, 2025 |
| Date Reported as Actively Exploited | May 22, 2025 (CISA KEV listing) |
| Affected Assets | /MagicInfo/servlet/SWUpdateFileUploader implemented by com.samsung.magicinfo.protocol.file.SWUpdateFileUploadServlet |
| Vulnerable Software Versions | Samsung MagicInfo V9 Server versions prior to 21.1052 |
| PoC Available? | A PoC exploit is publicly available here. |
| Exploitation Status | Arctic Wolf observed suspicious activity potentially linked to this exploit and CISA has confirmed active exploitation. |
| Patch Status | Fixed in Samsung MagicInfo Server V9 version 21.1052.0. Available for download on Samsung’s official website |
Censys Perspective
At the time of writing, Censys observed 1,101 exposed Samsung MagicInfo servers online. Note that not all instances observed are vulnerable as we do not always have specific versions available.
We identified a number of exposed Samsung MagicInfo servers referencing the file path src=”/MagicInfo/config[.]js”. When accessed, this resource reveals server metadata, including the installed MagicInfo version.
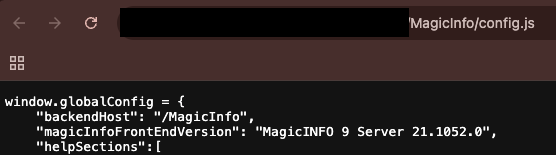
Using this method, we enumerated version data for 116 of the exposed hosts. See the table below for a breakdown of the versions we observed:
| Version | Vulnerability Status | Host Count |
| 21.1052.0 | Not Vulnerable | 57 |
| 21.1050.0 | Vulnerable | 23 |
| 21.1020.0 | Vulnerable | 15 |
| 21.1040.3 | Vulnerable | 8 |
| 21.1040.2 | Vulnerable | 7 |
| 21.1010.4 | Vulnerable | 2 |
| 21.1051.0 | Vulnerable | 2 |
| 21.1010.2 | Vulnerable | 1 |
| 21.1060.0 | Not Vulnerable | 1 |
The queries below can be used to identify exposed instances of Samsung MagicInfo, but they are not necessarily vulnerable to the exploit.
host.services.software: (vendor: "Samsung" and product: "MagicInfo 9 Server") or web.software: (vendor: "Samsung" and product: "MagicInfo 9 Server")
services.software: (vendor="Samsung" and product="MagicInfo 9 Server")
host.services.software: (vendor="Samsung" and product="MagicInfo 9 Server") or web_entity.instances.software: (vendor="Samsung" and product="MagicInfo 9 Server")
Please note that these fingerprints were recently deployed and results may take up to 24 hours to fully propagate.






