Update 10/27/25
Previous versions of this advisory overestimated the number of affected servers due to only keying off versions, however only recursive resolvers are affected. Numbers have been updated to reflect more accurate counts.
Vulnerability Description:
A flaw in a BIND 9 resolver allows it to accept and cache DNS records that were not requested in the original DNS query. An off-path attacker capable of spoofing or racing responses could inject forged address information into the cache. After the cache is poisoned, users relying on the resolver may be redirected to attacker-controlled systems without new DNS queries being made.
| Field | Description |
| CVE-ID | CVE-2025-40778 — CVSS 8.6 — assigned by Internet Systems Consortium (ISC) |
| Vulnerability Description | A vulnerability in a BIND 9 resolver allows it to accept and cache resource records that weren’t part of the original query. An off-path attacker could inject forged address data into the resolver cache by racing or spoofing responses. This cache poisoning enables the redirection of downstream clients to attacker-controlled infrastructure without triggering fresh lookups. |
| Date of Disclosure | October 22, 2025 |
| Affected Assets | ISC Bind 9 resolver |
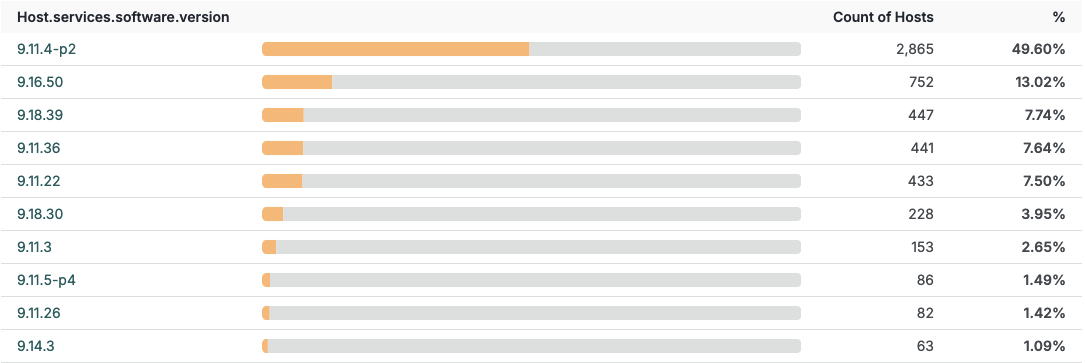
| Vulnerable Software Versions | 9.11.0 – 9.16.509.18.0 – 9.18.399.20.0 – 9.20.139.21.0 – 9.21.12 |
| PoC Available? | A PoC was published on GitHub. |
| Exploitation Status | At time of writing, there has been no known exploitation. |
| Patch Status | Upgrade to patched: 9.18.41, 9.20.15, 9.21.14 (or newer). Restrict recursion to trusted clients; enable DNSSEC validation and monitor caches. |
See the full breakdown in Censys Platform –>
See the breakdown of vulnerable instances by software version –>
Censys Perspective
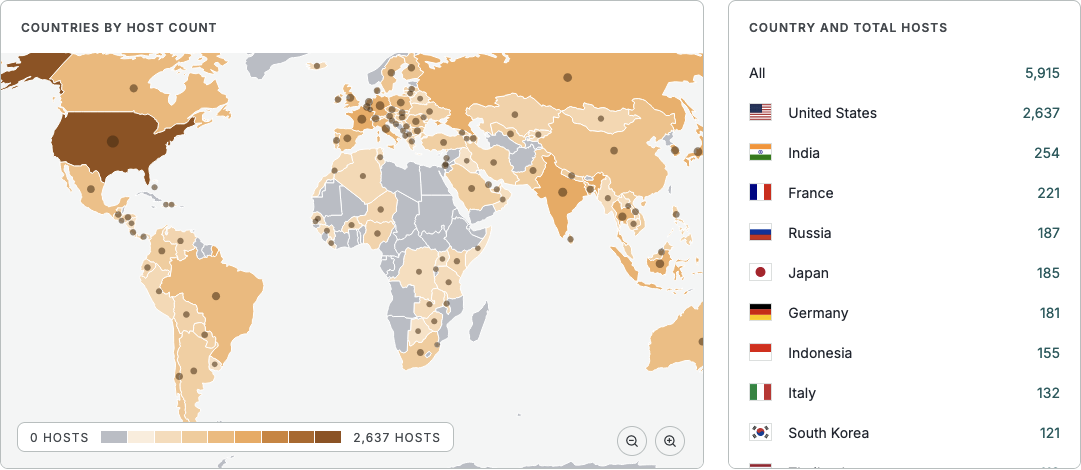
As of the time of writing, Censys sees 5,912 vulnerable instances. Use the following queries to find vulnerable BIND 9 resolvers.
Platform:
Legacy Search:
ASM:





